Out Go The Lights: An Enlightening Discussion Of IoT Automation Security

Show transcript [en]
outstanding outstanding those really nice-size audience here kind of impressed with that I've done a lot of b-sides and seeing turnouts like this aren't always always there I've been in rooms where I had five people show up so nice turnout really appreciate it so a couple quick questions just to gauge the audience so how many people here are IT security management people so we have a few so and I guess the rest of you are practitioners do we have any pin testers here a couple pen testers good so it gives me an idea of the audience well today's presentation is called out go the lights and an enlightening you like that play words enlightening discussion of automated technology or automated
security so this talk is going to be around IOT technology so let's go ahead and start with me my name is Darryl Hyland I work for rapid7 I hope you don't mind if I walk around I really really hate standing behind podiums I find that horribly boring so I work for rapid7 I'm the research lead and my job is to research IOT based technology so this has been really challenging a real challenge when I was given this job one of the first things they asked me was you know so now that you're in charge of research in IOT what is IOT and also you don't have a budget so so I've been doing that for about
I've been an IT for about 25 years I've been in security for about 15 and I was working as a pen tester for last 8 or 9 years before taking the role as the research lead for rapid7 so let's kind of move on so our agenda today is give you an idea or understanding of IOT at least from my view my vision of IOT may not be everyone's vision of IOT but it's mine and we're to talk about IOT migration into the enterprise we're also going to be talking about lighting automation exploitation I did some research recently on Io T based lighting so you know you can say hey I seen a guy today with a light bulb in his pocket
and we can also talk about securing IOT best best practices how do you approach IOT within the workplace how do you take care of it how do you manage the security risk implications associated with IOT within the workplace so let's start with the Internet of Things there's a couple couple interesting things here when talking about IOT how do we define IOT so there's a couple key areas interrelated devices IOT technology has interrelated devices they collect and share data between them they do this over a network this typically can involve Ethernet Wi-Fi ZigBee z-wave some kind of communication they're going to communicate and then also we get into a bed electronics they all contain bed electronics so this is the base of all
definitions when trying to define what IOT is so this is what I was challenged with doing defining what IOT is so me as a research lead can figure out what kind of research we're going to do in the area of IOT and the only way to do that is to properly define what IOT is but see this wasn't sufficient enough in my opinion what we needed to do is look at it from a bigger picture kind of an ecosystem so in an ecosystem of course we have the network communications but when we're dealing with IOT technology there's three other core pieces that make this up this actually includes mobile applications and includes the embedded technology and it also includes
the web api's and within each one of these we actually have code running on each one of these that make up the overall IOT structure and we also have data that's actually exchanged over the network communications the east of each of these three pieces so why are we looking at it from this ecosystem type concept the ultimate goal is is is to understand the potential risks of security vulnerabilities that could apply within the IOT environment or ecosystem and the only way to do that is look at each segment of that the mobile the Web API and the embedded part of this and how all of them affect each other because we're the security breakdown on any one of
these pieces is obviously going to lead to a failure of the overall system the biggest problem I've seen with most IOT research that I've encountered it all seems to focus on the actual embedded technology so everyone's going oh I'm looking at a hardware device I'm looking at an appliance you know they look at this this happens to be a light a five for a home this is a home automation for lighting systems so they look at this and they go this is IOT the fact is this is not a OT this is one piece of IOT this device here is control with the mobile applications on your phone that's part of IOT to do that it
communicates to cloud applications cloud API is out on the Internet this will communicate to those cloud EP is the mobile app communicate to those cloud EP is and that's used to control this device another piece of IOT and all of those pieces make up the ecosystem so the failure at any one of these pieces could somebody compromise a light bulb that could lead to actually compromise in your home network can someone compromise this that could lead to compromising the cloud a api's could someone compromise the cloud API is the effect could compromise your phone to gain access to your network the answer is yes unless we look at that whole ecosystem there's no way we could
effectively secure IOT technology so we have to look at it from that standpoint does that make sense to everyone says we're going through this I think we got enough time if anyone has any questions while we're moving through this please ask don't hesitate to ask that so make this much more fun and exciting if we have some good questions that come out of this whole presentation so moving from there let's talk about each one of these pieces in the potential risk or attack vectors that need to be considered so when we're looking at mobile mobile applications obviously we have the application we also have the communication that's associated with it that's going to communicate to the
cloud they may communicate across your network through your Wi-Fi network directly to the device so we need to look at that type of structure we got to look at actually what's being stored on your phone what kind of information relate it to the IOT ecosystem is being stored on that phone that creates a security issue a security vulnerability and last we got to think about authentication how do we attend ik eight to that application on your phone is it strong is it we can it be compromised moving from there we have the cloud aspect this is very much similar when we talk about the cloud EAP is most of the time this is actually going to be web a
web service it's available on the Internet and again we have the similar type of stuff we have to deal with authentication how is the thin ocation so you can buy IOT based technology you could deploy it in your home in your workplace but if the authentication mechanism is totally flawed within the cloud API what's the impact of that for your home security or your enterprise security it could be quite significant if I can compromise that cloud API I assume that I can gain access to PII information critical information about you your business or potentially tunnel through that application into your internal network and that has to be considered we also have to think about encryption is the data flowing from your
phone to the cloud API or from the embedded device to the cloud API properly encrypted is it passing confidential information passwords information PII information if it's not encrypted what's the potential risk there I just finished up a research project I wish I could share you the details about it but we're waiting for the vendors to actually fix the problem and this turned out that the mobile application that we were looking at when it communicated to the to the cloud it wasn't properly authenticated in a cloud there was really no good indication at a cloud so all I had to do was be able to capture a piece of data any piece of data about that communication and was
able to use that data to access all the information about this device you the person the PII information from the cloud because of poor authentication mechanism and then of course we got to deal with I'm sorry poor encryption then we got to deal with data storage how is your data actually being stored in the cloud is it being stored properly securely those need to be considered and last don't but not least web attacks within the cloud API since they are typically web applications are they vulnerable to the common web attacks can you do cross-site scripting cross-site request forgery sequel injection or a number of other type of attacks that are available door to web stuff and then we want to get into
network communication all these three pieces the the cloud the mobile app and the actual embedded device all communicate via network so from a research standpoint ecosystem standpoint we need to consider all the communication that happens to go over the network what about the protocols I mean like I said this is the number of different protocols we're all used to Ethernet that's pretty common or Wi-Fi but now we're seeing communication protocols between devices or you know the example would be like the light bulb on the network that are using other protocols this particular light bulb uses a ZigBee protocol we need to look at all of those communication protocols between the sensors the embedded devices the clouds the other embedded devices on
your network and all these pieces in the mobile applications and that communication is it proper is it secure is it encrypted and can we attack that I mean we have a number attacks like the home automation there's attack against the ZigBee protocol the home automation version of the protocol because it never raqi's plus someone cracked the key and it's available on the Internet so even though the authentication between this light bulb and that device there is encrypted it can be replayed because it uses the same key or it could be decrypted because everyone knows what key is because it's easily available on the Internet and you go oh my gosh it's a light bulb who cares well the truth is
that's fine if it's in your home if your neighbor just wants to torment the daylights out of you by turning your lights on and off all day that's perfectly fine no harm done but if you were actually sitting in this room and this whole room is controlled via this technology which is now hitting hitting the market and being implemented what's the impact of lights in this room going off we're going on off I mean it you say oh I would just leave well that's fine but what about the business what's the impact of the business what if you're in a retail business and you can't keep your lights on what if you happen to be
in your place of work trying to do your job and you can't keep the lights on I mean most of us are probably like sitting there hovered over a computer wearing a black hoodie anyways but in Jenna and Jenna in general the truth is you can't function without lights okay so if you're security your lights are bad at a bare minimum you got a denial service that needs to be considered so it's kind of fascinating area to think about was that yes could you say that again adhere oh wow I never even thought about that so he's basically said that that there was a scam where they would actually call in a bomb scare well
they're elite riding on coats or whatever in the bomb scared everyone run out the door and they stole all the coats in this case they just turned off all the lights walked out the door so yeah that's that's the reality it's there's a bunch I never even thought about that but yeah I guess that's a scam we don't necessarily see in the u.s. they just walk out the door they don't bother to care yes sir yes
so hit what he was saying there if you didn't hear it was basically by turning lights on and off at ten Hertz it affects epileptics and I know there's been a number of attacks like that the horrible thing someone did that to the epileptic website and made it flash at that frequency so yeah I have so yeah you've done it is that from experience and what was your name excellent thank you very much thank you very much so yeah you you have replay attacks spoofing attacks against a number of these protocols and even though it's something simple the lights there's a number of possible risk and vulnerabilities that exist there and again this is a piece of the overall
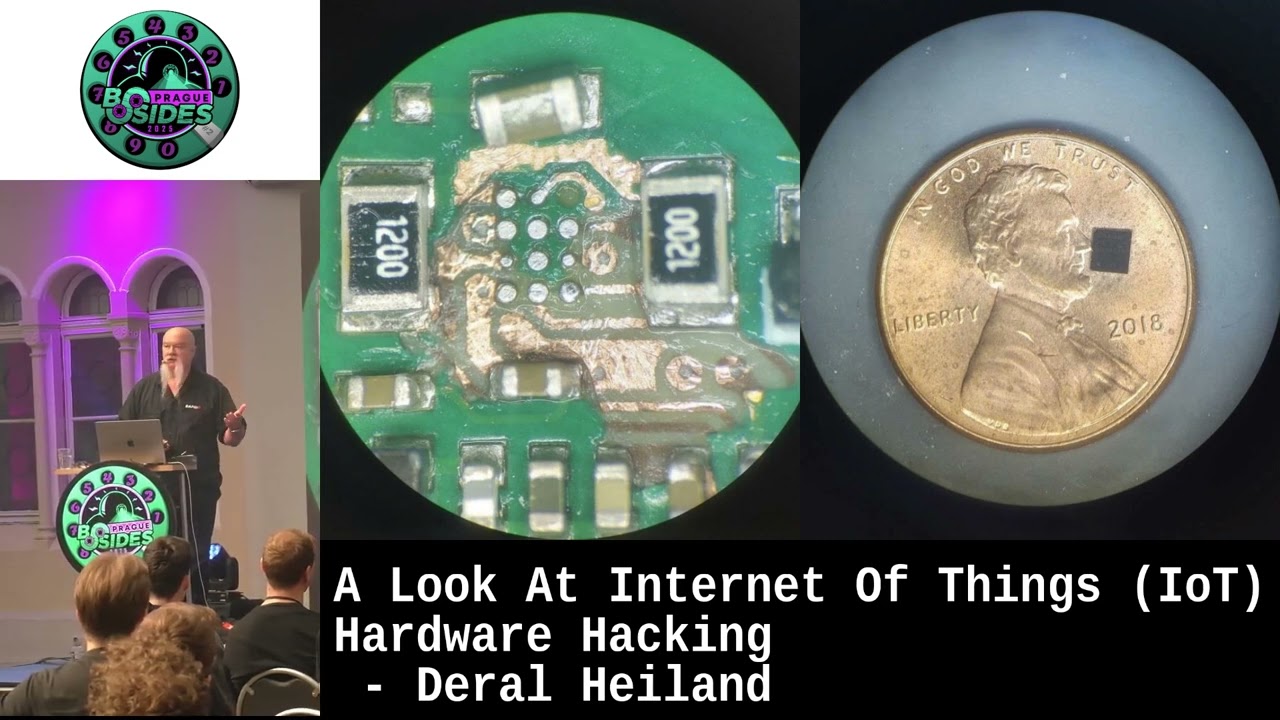
ecosystem that we need to think about when we're examining IOT technology that we're not just examining a small piece of it and the last one is the hardware this is the part everyone kind finds fascinating so you want you want to be able to look at the detail of the actual devices so the circuit board you see up there I actually cut that out of one of these light bulbs so that's actually a picture of it and just so you can get a closer look I ask that you return it here's here and pass it around so pass it around the National circuit board it was cut out of one of these light bulbs so we like to
examine things at this level here and look at the possible security implications we want to download the firmware code off these devices this one here the actual firmware code was actually brought down encrypted and was actually stored encrypted too which was kind of crazy on there technology all this company's technology on this case here it's actually a ZigBee processor that's on the device and the interesting thing if you look close at that board you actually see where the I think the three black wires that I have on there those actually connect to your UART a serial connection so you can actually hook that up to a computer and watch the device boot up so so it gives you a different
perspective of what a lightbulb is very different than what we're used to seeing in the past it's a piece of technology it's a computer it has code on it that code can be manipulated there was a talk at blackhat that I missed but I was told that it based on mostly on theoretical concept in the theoretic attacks against lights and actually being able to create a worm that could spread through like light bulbs I think it's doable it would only take someone a little bit of time to figure out a piece of code that they could put on one of these light bulbs screw it in when it's incorporated into the ecosystem of that technology spread
through all the lights potentially doing some of these other nasty attacks that we heard here at will or at random so it's something to consider so let's move on IOT migration into the enterprise don't have a lot of slides here but I have a lot to say about it so let's start off with yes they are here I don't know if people remember the movie apparently not okay so so IOT technology is in our workplace I talked to you professionals all the time I go to a lot of conferences and I ask the question do you have IOT in your workplace and most of the time is two things I don't know or no the answer is more likely you do
so let's think about this remember we're looking at it as a as an ecosystem so we're not looking at it as just some small piece of Technology we're looking at the whole ecosystem and how it connects up so example your employee has a Fitbit strapped on to his arm or some other type of wearable technology okay that wearable technology connects the Bluetooth Low Energy typically to his cell phone okay and his cell phone has applications on it mobile apps it's part of the ecosystem those mobile apps and a lot of times will also connect out to cloud technology okay so it ties into the cloud so we have those three people pieces we have the embedded technology
we have the mobile technology and then we have the cloud api's then he walks into your workplace and he attaches to your internal Wi-Fi because you have the whole bring your own device policy okay so now even though you don't believe it or not that Fitbit or that wearable technology is part of your network because he has it on this wrist hooked to your phone connected to your internal Wi-Fi network connected to the cloud now all those three pieces are now part of your network what's the security implications of that the scary thing is we don't know yet we're still so young in this field of understanding what the security implications is such things are
of wearable technology and how somebody could abuse those two compromised you so then we get into lighting now think about this okay you you're in a business your company your managers decide they're gonna cut costs and they're gonna put in lighting automation solutions to make the lighting all better okay say hired contractor and they put the Lighting's in they hook everything up they connect it into your network you know what I bet you it's probably about a 75% chance they never bothered to tell the IT department that they were actually going to tap into their network I've come across as more times than not that IT is often the last people to know with some of these core
based technologies such as lighting implementations coming into the network the other ones heating ventilation and air conditioning so when you implement heating ventilation air conditioning automation the IOT based stuff within your environment a lot of times this is used to manage power consumption within the organization to keep cost down this may tie back to a corporate quarters it made a it's more likely going to do this to the cloud more likely you're going to have mobile based technology involved in this I've seen these like iPad type things mounted at various locations in a building that are used to control this type of technology within your environment and that's what gets implemented into your environment but yet they don't necessarily tell your
IT department that's not part of the process IT department does computers right they do servers they do laptops they do desktops they do router switches in firewalls they don't necessarily get involved in the process around lighting or heating ventilation and air conditioning systems am I correct am I wrong does anyone go to challenge me such silence in here so how many people have IOT in your workplace now now would you raise your hand before I mention some of those things okay good some of you some of you said yes and that's perfectly good so we need to be thinking about these things within your environment this technology is coming in every day now me when it comes
to the definition of IOT I do not consider router switches and firewalls part of IOT I know you'll run into a number of definitions of IOT that involve anything it touches the internet it is the Internet of Things so if it touches the Internet it must be IOT if that's the case we've been at using IOT since the 90s at least now and I don't necessarily agree with that I think it's part of that ecosystem that I mentioned that actually makes up the IOT based technology so power management is another thing that's another one of those things that I'm just recently getting involved in I had I had a company I did some work for had just
implemented this type of technology power management to actually attract empower in their organization in their case the IT department vet at the entire technology before it's plugged into the network which is really good you don't often see that that's what I challenge most organizations to do get your security people and your IT people involved in some of these type of technologies to make sure it's done right they actually tested all of the products that they implemented with an organization and I was up there doing some work for him had a big discussion about this and they go yeah we implemented a company a B and C's technology it's in all of our store locations all over the United States
what it does is it manages power what it tells us how much power consumption is being used it communicates this to the cloud we could use various applications or mobile applications to interact with it to get this type of information and we add yes we did consider all the security things they actually with an Ethernet version of it which was kind of neat and then instead of the Wi-Fi because the Wi-Fi gives you the remote attack capability and you will actually talk about that in a few minutes on some products so they went with the Ethernet and then they also isolated it into a subnet which toured in we're gonna talk about some of these best practices the
nice thing was they go yeah Darrell and we actually have a whole spare unit that you can have and they gave it to me so that's sitting at my lab at home actually busted open with a bunch of probes connected to the circuit board as I'm analyzing the technology but again that's one another one of those technologies that may not be incorporated or me I team may not be involved in the thinking process around deploying that type of technology and we need to do that now this is the one that always gets me audio/video system so you go in an organization you go do you have i oh t technology in your environment and they're like no we don't I pull my
cell phone up I turn on my bluetooth low energy sniffer and it lights up like a Christmas tree and everything says Samsung Samsung Samsung go into every one of the conference rooms they got these big TVs on the wall there and I I imagine a lot of you have those in your home too right big the big Smart TVs they're kind of neat my wife actually forbids me from putting one in the house she doesn't even like going into my office cuz it's kind of there's so much IOT stuff plugged in she doesn't trust anything that goes on in that room she's not putting one of those in her house and I'm like why she goes well I don't
want the thing watching us so you know and all these TVs actually have our cameras built into them they actually watch you and send this stuff off to people not all of them but a lot of them do if you connect it to the internet they definitely listen to your audio okay and that's also transferred off onto the Internet if you have the TV connected to the Internet I know a number of people had these TVs that have turned that technology off I know other people that the technology on certain TVs they couldn't turn off and it would continue alerting on the screen that they couldn't connect until they plug the thing into the Ethernet so connected
to the Internet so I'm not sure what TVs you have or what TVs you have in your organization but let's think about that so you have a TV it's sitting in a conference room where you have confidential talks and discussions okay is that TV connected to the Internet if it is connected to your network it's connected to the Internet because I'm sure it will find its way there unless you've set it up specifically not be able to route but I know I've been into offices where they go yeah they fire up their laptop and they connect to this Wi-Fi service and in the how and the building and they're connected to the TV and they display anything they want on
that TV because it's on their network so it's on their network it's on the Internet now it's communicating audio/video out to the Internet actually one of the vendors and I think it was Samsung actually came out with a statement it says don't do anything in front of our TV you wouldn't do in public so think about that when you're when you're at home from your TV it's watching you or it could potentially be watching you says something to think about but it's nothing to be scared about it's a thing to understand okay you don't want to panic over stuff like that but if I assure you I'm getting ready to buy TV if it has a camera on it there's gonna
be a little piece of tape probably over the camera because I don't want I won't go buy one those little slide things I'll just put black tape or something over it so I look weird but it's something to consider and something to consider in your corporation so if you implement these technologies look to see if they are communicating out to the Internet because if they are the last thing you want to be going out the Internet are potentially going out over the internet is all the conversation that takes place inside your conference rooms obviously that's typically important meetings confidential information now these TV manufacturers are not using that data for anything unscrupulous they're not doing anything
illegal they're not harvesting your data and selling it to people they're not doing none of this type of stuff it's all part of this move to be able to market to you better so they can consume your communications and deliver you commercials seriously in the future that are based on your conversations that you had in front of the TV I don't like that but that's kind of one of the goals I see them moving forward to but the reality is is if somebody wants to compromise your network or somebody wants to eavesdrop on you somebody wants to break in and steal your corporate secrets how are we gonna do that I know what I would do I would probably tap
into all these TVs you have setting into conference rooms if they happen to have video capability to happen have audio capability why can't I record that information and excellent rate it off the network out to wherever I'm at and watch you and record you with what you're doing I think that would probably be the most interesting attack vector I can think of if I was just wanting to monitor to you does that make sense so is everyone gonna go home and everyone's gonna get out the black tape and I cut the wires the audio on their TV and do crazy things don't do that don't don't do anything crazy the whole idea is awareness if you're aware of something
you can make the right decisions for yourself personally and for your company and that's what it's all about it's one of the reasons why I do IOT research it's never about fear and certainty and despair it's about knowledge if we have the right knowledge we can make the right decisions so they're going to get into lighting automation exploits how much time we got okay good you got 10 more minutes okay so let's kind of move through this so automated exploits we're gonna talk about mobile applications embedded web communication protocols local Direct Connect services so we're talk about some of the attacks that I was doing so let's start with this one mobile applications where I had mentioned that
you need to look at the data stored on your mobile applications when you're looking at the ecosystem here's a prime example here happens to be a iPad and the plist file actually contains my password and my SSID for my home network so if I lost my phone and I go get a new phone truthfully this data is compromised another example and this is fairly straightforward and simple but it turns out like with an iPad you know when you hit the one button shut the application down it takes a screenshot of that page and you know how it shrinks you see the page the way they simulate that is by taking a screenshot and shrinking the screenshot and that's
actually stored on your machine so if you happen to be on the configuration page setting a password and you're done you hit that button you just made a screenshot now the screenshots will overwrite each other over time but I mean if you're on doing banking I'm doing banking on my iPad putting all the stuff critical information I shut it down and then I lose my iPad I leave in a cab hey the person all I have to do is pull up this screenshot folder and actually can see what the last page is you looked at before you shut down and actually could leak information prime examples the password they're embedded web attacks cross-site scripting let's just
do a demo it's a lot much much more fun but we're dealing with in embedded technology and you're dealing with and you're dealing with IOT technology most corporate enterprise IOT technologies just like most corporate enterprise devices on your network have web servers they all have web servers well we haven't have a lighting system here this is a this is a lie defy enterprise level lighting system this one hasn't been patched yet so what I'm going to show you has actually been patched
so let's go ahead and log on to this device I'm not sure how well this will you'll be able to see this this is a configuration page for AWS roms lighting system like I said they've patched this do not consider this any kind of negative against asraam they actually patch this stuff I work directly with them helping them behind these issues so these are actually good things this is a good company they do things right they take their security right they create patches quickly automatically update the patches on the system I just prevent it this one from doing updates that's the only reason why it's still vulnerable so we come down here under management and
we look at security logs in this case you can see where you've logged on and I logged off that's how the security logs are it's kind of small but this is a page of security logs okay this case here see if it's words
let's come over here real quick here's the actually pricing this any better this is the Oswald configuration page you look over here when you go the security logs we can view the security logs here see them a little better you see is really nothing there simple security logs what we'd expect well what we're going to do is we're going to actually log on but we're gonna pay a log on so we're gonna send it a failed log on this failed log on is actually going to contain HTML source code this case here which is basically a cross-site scripting so we log on and it fails so then if we come over here refresh this so now his logs are a
little more unique we're actually able to plant stuff in there so there's a number of attacks that can be carried out this way you can carry out cross-site request forgeries it caused them to reconfigure the device so this happens to be one vector that we found which is not necessarily an uncommon vector it's easy enough to inject cross-site scripting via logs very common method but we have another one I have a video for this one here is an attack vector very similar it's a video it's easier to do with the video but in this case here instead of a failed logon attempt we're actually going to start up our own Wi-Fi hotspot and for the SSID
we're actually going to put attack code into it in this case it's just going to be a flash file we're not going to do any real attacks with it but we're gonna show how it's delivered and it's a similar attack as the other one we carry out cross-site scripting so any device that actually displays SSID structure we could actually potentially inject cross-site scripting cross-site request forgery in so again we go to the Lyta Phi system here we're going to come down to the Wi-Fi configuration we're going to go to the wireless client mode it's going to come up here in a second and we can see we have 2 SS IDs that one happens to be
going home that one's my neighbors but what we're gonna do is we're gonna fire up our own SSID in this case we're actually going to call a flash file and we can call JavaScript files from a third third party site to do attacks but this is what we're gonna do so when this product actually enumerates the wireless spots nearby we'll scan it again so it shows up this case something different happens and again again it's it's a fun entertaining way of actually demonstrated in a potential vulnerability in a product but the reality this type of attack thing never gonna quit there we go so this is just one way to demonstrate the attack but the reality is this
attack vector is pretty serious I did a get blackhat you're up here three years ago on this exact topic where we demoed enterprise level products and one of the examples we actually use this attack to create a administrative ID on a enterprise level wireless control and controller with root level privileges used in this attack and also had the device offload all of its configurations to us to a third party website so these same attacks can be carried out any other way so if you happen to be implementing a technology or using a an embedded IOT based technology where it can see Wi-Fi around you and it's monitored via that anytime someone would see those SS IDs the potential for an
attack vector existing there does exist and again this is kind of an entertaining way of demonstrating that attack vector but it's a quite serious attack vector so let's jump back to slides real quick
so on the last one I'd mentioned is communication protocols ZigBee Ethernet z-wave Wi-Fi the whole list goes on and on and on but the truth is and and we mentioned it earlier these type of protocols can be used to do replay attacks and various things like that and they exist across the number of these different protocols that needs to be considered on the the Wi-Fi communication on these devices and some other ones we've been finding a lot of the WPA pre-shared keys that exist on these technologies by default and you know they give them wpa2 out of the box setup they seem to be complex but they're not complex it turns out that we typically are able to crack most of
these keys in two to six hours so if you using these technologies and use them their defaults that come with their products you need to reconsider that because we're found in the key spaces are using to generate those keys are insufficient and they're brutal and we can easily crack them and like I said two to five hours and if you happen to have one of these devices connected to your network via ethernet and Wi-Fi and I'm sitting in a parking lot and I can crack your WPA pre-shared keys on these devices I am now on your network it turns it into an access point so we can easily pivot into your internal network so that's something to consider
also local connect one things I found out with most iot technologies especially the home stuff is when the cloud goes down does your whole product quit working no it does not quit working it goes into what we refer to as local mode so your mobile app will connect straight to the device but typically the whole thin occation mechanism was your device with indicating to the cloud to get information down your mobile app connecting to the cloud to get stuff down but when the cloud fails that communication drops the local mode and instantly there's no longer any authentication and it happened to be the case with this particular device right here so the code you see up there I mean
it's a simple piece of code snippet and what we're doing there is literally we can pass an SSID and our own pre-shared key directly to the device without Afeni keishon and it will do from your network andrey off to ours without any authentication and this is not this is not common or uncommon it's quite common i've seen a lot of technologies that are built that way so instantly i mean your home networks typically going to be secure it's probably not going to be a problem but as you see more of these technologies and move into the enterprise environment those need to be considered your network becomes a lot bigger a lot more people in it you could have people unfriendlies
on it people break into your network if i can compromise your network and find some technology that i can set up a permanent backdoor by routing your system out through my system I'm going to do it it creates a way for us to move data back and forth without properly not getting detected so an attacker is definitely going to do that now we want to get into security IOT best practices and we've kind of covered a couple of these so stopping right here the stuff I've showed you guys do we have any questions yes sir
although we haven't looked into it so the question the question was have you seen any lighting systems used to exfiltrate data often network was that we were saying basically so and no I have not seen anything in the wild but we were talking about that with my manager just recently but because when I was at Def Con I was in an IOT village talk and they were talking about lighting specifically and in that case there they it actually took a building a lighting control system and turned the whole front of a building into a video game by using the office Lighting's so it actually played out like a video game using all the office Lighting's so so
that brought up the subject with my manager going hey you know someone could use that to actually send data out of a company Network you know that 40 storey building and you have a light on you know the 40th floor that goes on and off at a certain rate is anyone going to notice maybe maybe not or have lights come on in various places at different times to actually communicate data out through a building and so yeah it is possible I'm not sure I'm sure someone will eventually try it let's be real you know so that is a possible attack vector yeah okay let's kind of move on to this right here best practices and this is
this these are real simple this is not rocket science identification you want to go through make methods to identify IOT technology it's currently in your workplace how do you do that this is something I'm currently challenged with trying to figure out from for rapid7 is how how can we help our customers identify IOT if we don't know what they got if you don't know anything about what's there is there ways for us to identify IOT it's something you need to do because you can't protect it if you can't identify it business needs you always need to make business decisions that's what everything's about it's not about security it's about business decisions the business has to make those decisions
are we gonna embrace IOT and do it correctly or are we going to wait until we wake up one day and something happens and we go huh I didn't know I had I owe t technology in the workplace which is basically what happened the phones I mean did cell phones sneak up on us and sort of most companies would don't have any cell phone policies until they find out that half their employees cell phones are connected to their network and then they go oh my gosh maybe we should have a policy so let's think ahead of that from an IOT perspective and think about what's acceptable what isn't acceptable from a standpoint of IOT within your corporate environment
isolate segmentation the best thing you can do if you're implementing heating ventilation air conditioning power management lighting systems don't put those on the core network put those on some kind of backbone network so that if it is compromised they do not compromise your internal network to me that's the best way to go keep it isolated patch management anytime you go to purchase an IOT technology the first thing you need to ask them how do i patch it what's the method for patching it how easy it does it patch the truth is if I have a technology and and the asraam was probably one of the best examples that homelite if I system every time a patch
comes out I fire up my cell phone or my mobile app to look at my lights to turn them on and off it alerts me that there's a patch all I have to do is go patch a minute later everything's patched it does it over the wire does it over the protocols it patches all my lightbulbs does it all that's the type of technology we want if a vendor goes oh yeah yeah you'll have to have an outage and you'll have to take the device and you have to do a B or C to get it patched in but we never patch anyway so it shouldn't be a problem you don't want that product you want a company takes
patching serious and they're patching method around upgrading the devices firmware is simple and not complex if not it's not the case you don't want the product and any questions yes sir right yeah with with IOT the IOT technologies I see that I've just started working with myself for like Bluetooth Low Energy so there is still number tools that are coming out for monitoring Bluetooth Low Energy there's some hardware like Adafruit puts out a sniffer that you can actually get within the middle of a Bluetooth low-energy communication there's the uber tooth device for sniffing Bluetooth technology those are some of the tools for sniffing there's also RZ USB device which killer B which is basically attack tools but it
gives you the ability to sniff ZigBee and capture though protocols just recently there's been stuff come out with z-wave but I've not looked into it typically z-wave you're gonna use some kind of RF RF hacker tool or something like that to catch those RF communications but yeah unfortunately unfortunately there's not a lot of tools readily available typically the technologies are with us longer than I've liked before people start producing valid tools for capturing that data but from Bluetooth Bluetooth Low Energy there's some good tools out there the ZigBee like I said the R and I have one of the devices here if you want to actually see it devices for the ZigBee stuff that you can use to capture replay
dump do peak apps and stuff like that so you can actually analyze the data available and most of these you can also input the data into Wireshark the Bluetooth Adafruit sniffer will actually output all the data into Wireshark for further analysis also in same way with the uber tooth any other questions what's that the work that no that's not necessarily long with vulnerability you want it you want things to update but you want them to be signed also so packets firmware package should be signed that means you just can't drop a firmware on the device automatically that's important but the automatic updates they don't automatically update what happens is is your mobile application plays the pivot
point and when you say update it pulls those firmware packages down and then serves them up to the actual Gateway and then the Gateway deploys them to the light bulbs can you hack the phone in this kit and this in this case here all of the packets were encrypted all the firmware packets were encrypted I did not know the decryption form so you would you would have to know their encryption mechanism their signing mechanism to be able to create a packet to do that but you got a good point there just because the device is automatically update just mean it's secure you can easily update it with your own firmware then it's not secure a
company has to have good encrypted firmware and the packets need to be signed if they don't meet those qualifications they should not be able to be deployed onto the device so a good point yes sir no no I mean I mean let's think about that you think the application community operating system community have a problem with bugs I mean Microsoft has a crapload it comes out every month bugs aren't gonna go away so so how did how did Microsoft solve the problem they solved the problem by putting a good program in to patch so and I think that's the case now I agree with some of the bugs are just like you got to be kidding me did you
even try and you're gonna run into that in some cases and it's kind of a new field and you got to remember a number of these companies aren't software companies they've never done software before so they don't understand security they've always produced some kind of product and now they're in they decided we're in IOT so yeah they're a little bit behind the eight ball but there's something companies out there build it secure secure securely build it securely which is the website if you look that up that is a company or that's an open sore a non-profit basically focus on helping vendors build security models around the creating and deploying their products so think about time