Tracking TTP Changes Of SocGhoulish - Chris Morgan
Show transcript [en]
um thank you all for joining today's presentation which is going to be on so goulish which is a really common malware loader that we we're seeing quite frequency uh on customer incidents um so my name is Chris Morgan I work for a company called relay Quest if youve not had a chance to speak to our guys downstairs absolutely go and do so U we're a market leader in xdr you know really helping our customers improve their visibility threats but also manage those threats as well so thank you very much for for joining this presentation um just a show of hands who's actually heard of s gulish here oh quite a few of you then okay well good stuff so that's
off to a good start then um so this is the agenda of what we'll be covering today uh we'll be quickly discussing you know what is a malware loader introducing so ghoulish um which is also known as fake updates um we'll be talking through an typical kill chain and also some new behaviors that we've seen associated with this malware loader and then we'll talk about the association with ransomware activity as well so obviously I'm in quite a learned uh group here so I'm not going to Harbor on this point too long um but it's in short a malware loader is a piece of software that's designed to act as a conduit and dropping other malicious uh
artifacts other malicious software on your estate then execute it um it does this a number of different ways but it primarily acts in is the the main way in a multi-stage um attack um mostly to facilitate initial access but also persistence un compromised devices um and employing sophisticated techniques to actually avoid your inent responders as well so avoiding what we're doing um that might be a number of different ways from like obfuscation techniques or kind of living off the land using native tools but in short malware loaders are are there to try and deliver other whatever that might be onto a Target system in terms of um so goulish which as you can see also known as fake
Updates this has been around since 2019 um so it's not a new thing it's actually quite a quite an old bit of Kit to be honest with you um this is a JavaScript based initial access um remote access Trojan U that essentially stands out because it mimics legitimate software updates through compromis websites um so it might be a browser update it might be you know if you've ever been on to one of those dodgy torren insights or a streaming service not that I would ever do that of course you know I wouldn't recommend that you do that but if you ever go to one of those and it pop ups with um you know update your JavaScript
here or update your Adobe Flash whatever it might be um that's the kind of thing that that it propagates through um so goulish is often referred to as an attack framework because it's a technique that can be easily customized and changed by whatever cyber criminal is actually trying to use it um we've seen so goulish associated with pretty much a who's who of ransomware activity um from if we go back in time mazee egregor um the the reval group which obviously many of you will probably have heard of all of the subsequent Ral groups you know many of these have actually been using St live attacks uh many of the more recent rans way groups
as well um so it's really an interesting piece of Kit um and kind of crucial to understand because we think it represents a really significant change in the way that threat actors are actually gaining initial access um very very highly successful because it's employing these social engineering techniques that many of you will have heard in the other presentations today so I sat in the presentation with um Ian foron Trump and he was talking about 74% of incidents that they're observing come through social engineering that's very much this this kind of thing it's spreading through targeting the user targeting the Curiosity of the human um that's that's ultimately the the big thing to take away um bottom line up
front so this is something I took from a previous career you might have come across this one actually BL um it's essentially an executive summary so what are the three things that you need to take away from this presentation you know if you can remember three things from every presentation you've had today you're probably doing quite well so the first thing is that again it's it's sophisticated social engineering you know it stands out through its ability to propagate um leveraging these really interesting tricks uh to force a user or coera user into actually um accepting this fake browser update and that starts the whole process right for the get-go um it's modular and stealthy in design
so really designed to be easily customizable um allowing your cyber criminals whoever's using it to adapt it to whatever their motivation might be so it might be to uh drop spyware a key logger you know data exfiltration tools you know obviously data extortion is a really common thing that we're observing the last few years you know a lot of these extortion groups are kind of pivoting away from ransomware you know just stealing your data and then using that to extort you you know the salt Gish can can achieve this it can assist the threat actor in achieving this so very modular and kind of stealthy in what it can do and then also it's why WID spread
distribution and collaboration through different cybercriminal groups so again we've seen this spread on dark web forums um on marketplaces you know actors sharing how to use it changing its behavior and that's probably why it's been around you know since 2019 so really has that Effectiveness and that prevalence within the the Cyber threat landscape um in terms of a typical kill chain it pretty much looks like this um so you'll start with the initial compromise of a legitimate website so that might be through the theft of a web administrators credentials it might be injecting third party scripts onto a website it might be just exploiting a vulnerability that's that's is exposed but whatever way it happens you know the
website is compromised the user is then directed to this website you know potentially through like a Speer fishing mail or something of that nature um and then they will be um given this fake update prompt so the compromised websites will display a popup message or a banner that basically mimics a legitimate software take and post it down um but it pops up with this um browser update it might be Chrome Firefox you know whatever it might be uh and then believing that the update is legitimate the user then clicks on that prompt to download the supposed update and then the actual attack cycle starts um the user then executes the downloaded file believing it's to be legitimate uh and then this
executed file installs initial payload onto the user system um and it's it's pretty much as simple as that you know there might be persistence mechanisms that are built into this um you know potentially modifying system settings um using other techniques to make sure that it runs on system reboot um but it's a pretty pretty simple kill chain but again you know the social engineering is what makes it tip um so this is just an example of of one of the typical fake updates you'll see you know it might be Chrome it might be Firefox saari um you know whatever it might be you know this is the kind of thing that they're using and obviously
if the user thinks it's a legitimate website there's no reason that they would go okay well I don't need to install this I'll just you know go ahead with it but this is what so goulish is is leveraging it's the user error so in terms of um a new infection chain in the first quarter of this year so February uh we observed um several suspicious incidents that we attributed to S goulish and when reviewing the um the execution of the first a stage payload we saw this behavioral change essentially using python as a method uh for consistence so once the initial file is dropped and installed on a a victim's computer you know much in the same way
that we observed in the last fi chain um the execution is made via um W script and then we see these new behaviors KCK in so the first one is the process begins with downloading um the latest version of python from the official python repository and after confirming this and listing the download directory the contents of the zip file uh are then extracted to a specific folder um this original zip file is then deleted uh and the contents of the extracted folder are listed to make sure everything's in place um we then see the renaming of a temporary file that contains malicious code so milous python codes and then a scheduled task is created um essentially to run hidden
Python scripts every five minutes and that then connects out to one of the attack controlled IP addresses so essentially what they're doing they're downloading and extracting python um that named it here 3.1.2 I guess that's the most up toate one uh renaming a temporary code that contains malicious script uh and then they're connecting to a suspicious IP address um and this new finding is you know further evidence of that kind of cat and mouse game between Defenders and attackers also they're changing their behaviors based upon what we're doing so this just another kind of Behavioral change that we observed um so we've released quite a few reports on so goulish uh so on the left hand side I think that was from the
end of last year that was the first one we did uh and on the right hand side is this new infection chain that I just went over um highly recommend going and checking these out uh we have new blogs on the on the site every day so definitely go and check these out at rei.com and in terms of malware loader activity in general um this graph basically represents um the total observations of malware loaders from the 1st of January this year to the 9th so you can see so goulish was representing over 70% of the mway loader activity that we'd observe between this time period and one of the really interesting things I want to
point out on this is um we released a report last year right before the takedown of the quack bot infrastructure or qbot that you might have heard of um and at that time s Gish was around 33% of the total activity and once quack bot was taken down you had this void you know this void happens quite often in the aftermath of these law enforcement operations you know we have um a period in which some of the other groups or in case this in this time a malware loader actually steps up to the plate and fills that void and we can just see that with s gulish you know you have the other malware loaders on there so go loader
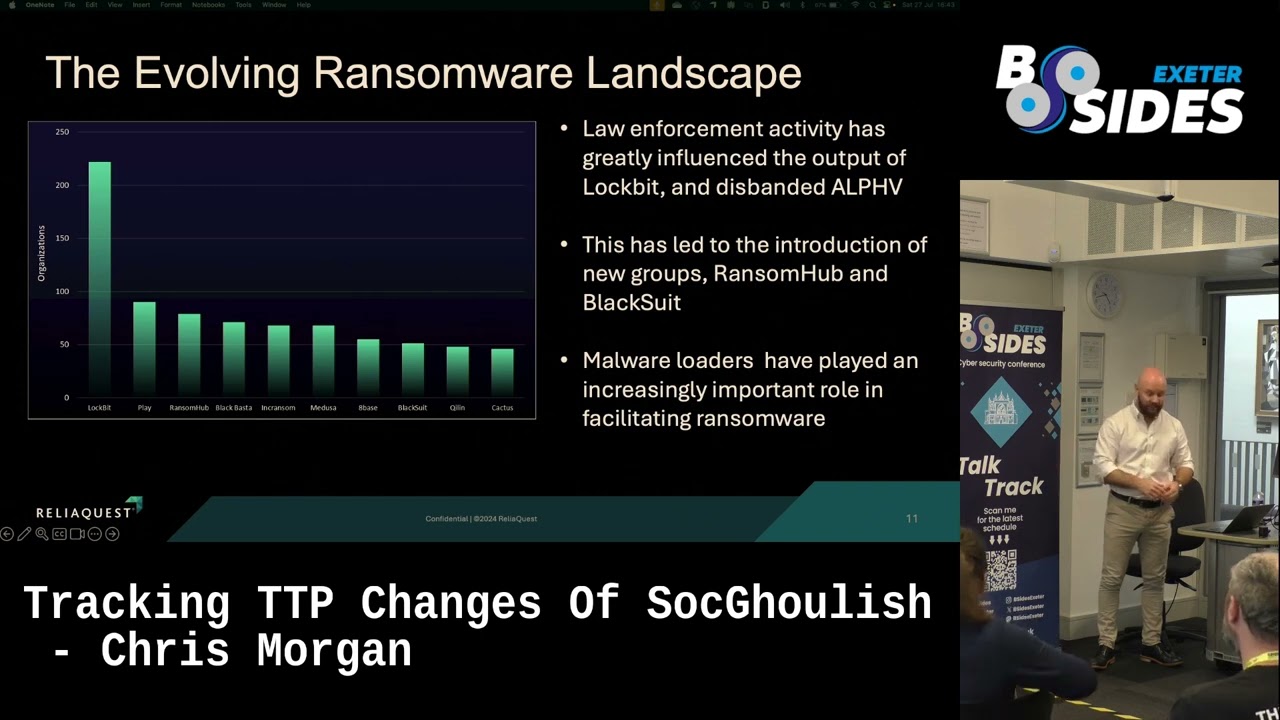
raspberry Robin G loader you know they all represent a significant threat as well but we can just see that the overwhelming majority of what we're seeing from a malware loader perspective is coming from sof Rish um so interesting point and then this is just a slide um so I took this graphic off of our Q2 ransomware report um so basically demonstrates the total numbers of organizations posted onto distinct r W groups data leak sites uh obviously that doesn't account for every victim because a lot of them will pay the ransom you know huge percentage will pay Ransom uh and then not get posted and named and shamed um but it's been a bit of a tumultuous time for ransom
activity because we have seen a greater tempo of law enforcement activity so we had I think it was Hive last year tail end of last year we had Alie which were kind of like the the runners up if you like in ransomware activity and then obviously lock bit um lock bit they're an interesting one they have shown resilience and even though they're they're by and far the still the market leader their output is actually significantly reduced um so we we do see a really good effect from these law enforcement operations but again it's kind of like wacka Mall when we take these groups down they're just going to resurface in a new rebranded or um
renamed effort you know the Affiliates will move to a new program it's just very very difficult to take down with any real um longevity and the key point at the bottom there again is just Mal loaders are really playing an increasing role within this this activity you know they're they're significantly turning to the likes of sish um to enable initial access so recommendations you know realistically I could put up like so much here but I kind of thought you know enhancing visibility is the key point you know you can't protect what you don't know exists um so just making sure you've got adequate visibility of all end points you know events like you know process execution you know registry
modification um you know these are these are a good place to start you know these logs you need to be collecting um you know you need to have really good Network elemetry um I put gopo in there as well so configuring notepad to be the default application that JavaScript files open in you know that can be a really useful way of of stopping many of these JavaScript based malw from actually going places and doing bad things and then the last thing on there is is really just training staff like that sounds like such a high level kind of cliche answer but your staff need to know what social engineering can do they need to understand what are the common
ways in which threat actors are actually you know masquerading and which are tricking users um and also having a culture in which you're your users have the confidence to report something they need to have the confidence to report something they need to know that they're not going to be condemned um that they're not going to be um I guess reprimanded if they've done something wrong like have the confidence to actually report something if they've landed on a website that has you know something like this and it appears suspicious don't just click off it make sure it gets reported you know if you receive a fishing email don't just delete it make sure it goes to your
security team you know these are the basic things that can make all the difference and then the last thing I just want to mention um so this is something I took off of our annual threat report so this is reli Quest version of the Verizon dbir if you've ever read that you know fantastic report um we found that organizations who opted to leverage some level of AI and automation within the incident response uh they saw a reduction in their meantime to resolve to 58 minutes which was a 98% decrease which is just a a staggering statistic absolutely staggering um so this could be I it could be anything really but things that crop up for me are
like if you have a user who finds out their um their credentials been compromised like automatically rotating them there doesn't need to be any delay in that automatically rotating them if you have a session in which you detect two or more users all actively logged into it making sure that gets terminated you know these are the real things that can make such a difference from a Time lers perspective and can really stop a lot of these commodity threats in the tracks um so automation is something I'll I'll definitely Bang more you need you just have to get on board with this because you'll get Left Behind the Walls um that brings me to the end um I know
I'm quite quick on the time today but it has been quite a long afternoon right so um maybe not the worst thing in the world but if anybody has any questions I'm I'm more than happy to answer them sure um the prrams as what the challenges
it's because of those alisation techniques that they're using so it's the methods that they get around your sort of typical end points elemetry and security devices so the um the use of python you know that was a really interesting one because you just wouldn't assume that that would be malicious you would think that that would be just like regular routine behavior and obviously they're going on to what appear to be legitimate websites that would just wouldn't flag up that it's malicious in the first place so there's a lot of different techniques are used but it's those kind of combination of social engineering which is difficult to detect and behaviors that they use to kind of s skirt your
typical endpoint detection really so it's combination of those factors joh how is python used for systems python so obviously when they're reaching out when they have that command and control that's that's the um that's essentially how they're using it so when they're stepping outside um and using python I need to come back to you on this I need to come back to a better answer on that yeah let me come back to you on that one George [Music] it's the choice to
what would driver behind that to do with being able to do more stuff well I mean obviously python is is your your most commonly used um so I would imagine it's it's probably enabling them to do more based upon those facts and again it probably comes back to the fact that they're less likely to be detected as as malicious um there's there's lots of different changes I've only represented one on here but this is a really modular and customizable attack framework so there there's lots of different ways in which they can kind of Sid skirt around your your usual detection so it's it's probably that that factor really that they can do more as you alluded to I
will come back to you on that question though you mentioned lock there um and obviously they were hit over the back of the head by yes large law enforcement um have you seen some of the other industry reports that say that l b are not as dead as they as the operation May succeed and the statistics say that there's been like a 600% increasing outbreaks of lock bit itself so clearly it's not quite as did do you know if lock bit are using sorry I finally get resemblance Point um do you know if blck bit is or some instances of blit using poolish themselves that's a good question uh I know that they have been
associated with malware loader activity in general I'm not sure if we detected them with soft ghoulish specifically um your original point was on the the activity levels yeah so we're still we're still seeing that they're the the market leader we're still seeing that they're the most active group but it is still a massive step back from where they were last year there's clearly been an impact on their confidence of the Affiliates like the lock bit brand has taken a massive kicking because a lot of these Affiliates will be thinking they're now compromising by law enforcement and security researchers um obviously they had the post regarding the US Federal Reserve recently yeah which turned out to be bogus and we saw
a lot of posts on like cyber criminal Forum saying you need to stop with these speculative things because you're losing confidence or you're going to lose more members if you make ridiculous claims like this um so I think their their reputation was taken a bit of a kicking I think from my perspective they they gave out like a snar because they'd been they'd been crept up on and someone had hit them over the back of their head with a Crying Pan when your first instinct is to Bear your teeth at everyone around you it was reactionary wasn't it yeah yeah they all do this these ransomware groups they'll they'll post things that are Fantastical speculative great is great is great
bedtime reading it's absolutely hysterical but yeah we have to try to find line in here because we all find it ing but we also need to recognize these groups are horrible and they're doing like genuinely terrible things and a lot of these organizations that are targeted by rans they don't recover you know I'd love to get a percentage on how many don't recover you know because it just highlights the the scale of the threat really any other questions um one of my friend called me to uh remove my work from their laptop I connected remotely to see if any mother on laptop and I didn't find any but what I found was um push notifications with all this oh you have
virus from different websites yeah and when you visit such malicious website they just ask you yes no if you allow this push notifications and they just every week like it's almost like alert fatigue yeah yeah yeah so so it almost becomes a a something you see all the time so you just don't actually see the real threat that is surfacing interesting okay it's another way of yeah getting around it I suppose alert team any other questions does lo requ elevation run elevation or it runs as
so once the initial infection has happen that can Target a a regular user but their end goal is to get to an elevated account yeah AB rights can run back and it it becomes a part of the typical attack chain so it will initial access happens and then obviously their end goal is to elevate Privileges and then move on to a more privileged account yeah so M utilize this privilege escalation that used by uh some legitimate software like Adobe some other stuff and they just somehow I don't know exploit or utilize this breaching systemy to get ini sure sure one final one for me yeah and is it always a explicit download and execution for so foolish or is it sometimes
driveby download where the JS is loaded into files and that same surprise you've got say the question one more time um is it always explicit download of a compromised file based on social engineering or is it also posted on some kind of content delivery Network and then by download it can depends the most common delivery method that that we do see is your driveby download and those fake updates that's probably why it's more commonly known as that but there are additional ways they can do it like this your standard Speer fishing emails things like that so there's lots of different ways in which you can kind of propagate nice cool well not nice but I know what
you're saying yeah got you awesome um well thank you everybody for joining um really appreciate your time um look forward to catching up with you in the drinks later but thanks very much oh