When SSL Fails: Tracing the SSL vuln to the most shocking real world impacts

Show transcript [en]
[Applause] thank you Karen thank you so much all for coming to see my talk today so um I'll get cracken because um I need the time so hopefully I won't run over uh so my talk this is it when SSL fails tracing the SSL vulnerability to the most shocking real world impacts so why am I talking to you about weak ciphers um as you all know I'm involved in bite I'm also a seasoned pentester had of pentesting for vertical structure with a background in risk and software engineering this kind of all started for me when I was about 11 years old um I loved puzzles and my uncle had bought a or had sold a briefcase to a customer
and it was locked so he brought it to me and I proceeded to do Brute Force attack against it to get it unlocked little did I know at 11 years old that this would be a career for me um in University and my software engineering degree I loved cryptography mod so much that I went on to do a a security Masters as part of my masters my thesis I did on security protocols and implementation of theor theoretical secure multi-party computation protocol this was for blind Fair bidding and it was fairly mathematical um and a long time ago so might not be able to ask answer questions on it but maybe someday um so crypto is kind of tricky but I like it
uh and this when I said about doing this talk uh it reminded me how much I enjoy it and not a lot of uh people in pest pen testing dive into it in much depth there's not as many YouTube demo videos like with everything else in security as mentioned in my abstract almost every pentest report delivered has a bunch of SSL issues um at the very least weak ciphers and there's a reason for that I'll come to later I've been questioned on these by colleagues and clients and started digging my Google Fu and other researchers come come up quite lacking so a combin so this was back before the cfp combination of the upcoming call for papers for bsides and
I also had the absolute pleasure of interviewing Jeff White for his new book rinsed I was inspired so I set out on my mission investigate why should we care about weak ciphers or should we uh and do it let's have some demo fun so uh first week in my job uh like 18 years ago so I had to put my hand up earlier for Holly um my one of the directors said what can go wrong will go wrong so hopefully we get through this without too much hassle first of all I want to show you some encryption ciphers so this is what we're looking at when we're testing encryption um for websites anyway um so
just to explain a little bit about week ciphers when I talk about it what do I mean so every website that uses encryption and this should be all of them now that certificates are free but unfortunately it's not um all of these websites have configured which encryption ciphers they can use to connect to the people can use to connect to the site when you're connecting to a site the browser is also configured to use certain encryption ciphers so when the browser on the website connect they establish which uh encryption Cipher they're going to connect over they're going to the all Communications will pass back and forth through ideally this would be completely protected from anyone who can see the
traffic so this is a a short list of there's many many many ciphers out there um the ones that are highlighted in red are considered weak and the others are not currently considered weak so just to give you a very quick breakdown and I'm not going to get into this too much because I don't want to get too Technical and because that loses people especially in crypto so when you see the TLs this is a very um this is a protocol in use older ones were SSL uh DH DHE or EC DHE is denotes the key exchange algorithm being used and RSA is the authentication mechanism AES is the session Cipher 128 or 256 is the
encryption key length in bits that's important uh CBC or G GSM is the type of encryption and sha is the hash function 256 384 is the digest size of the message so we'll come back to these a little bit later we'll see them later on um but for your information if you see the CBC ones so the bottom two red ones these for TLS version 1.2 these are considered to be weak ciphers but they're probably the strongest of all the weak ciphers uh this is due to the CBC uh Cipher blockchaining mechanism or Cipher and that is inherently insecure with lots of issues but we'll come back to that later see if this works so I want to give a quick well
relatively quick brief history of SSL and TLS So for anybody who doesn't know slsl secure sockets layer TLS transport layer security this is the protocol that we use for encryption two different names but it's the same thing um so we started started before this SSL version one was never released then in March 1995 SSL version 2 was was shipped in Netscape browsers very quickly there were vulnerabilities discovered so immediately SSL vulnerabilities coming out same year in December SSL version 3 was submitted a year later in 1996 the development Begins for SSL version 3.1 Microsoft I believe applied some pressure and got the name changed to TLS version version 1.0 so this is it's the same it's the same thing new name
development began '96 it was released in 99 um so it took three years and it was released then in April 2006 we got TLS version 1.1 in August 2008 we got TLS 1.2 um and then we saw in March 2011 SSL version 2 was deprecated then we started to see a lot of kind of high-profile attacks the Beast attack attack in June 2011 exploited predictable initialization vectors in the encryption uh the crime attack in September 2012 exploit exploited TLS compression and then we can see in November 2012 the industry started to try and bring in some mechanisms and measures to help protect uh the encryption and they brought in the hsts HTP um I know
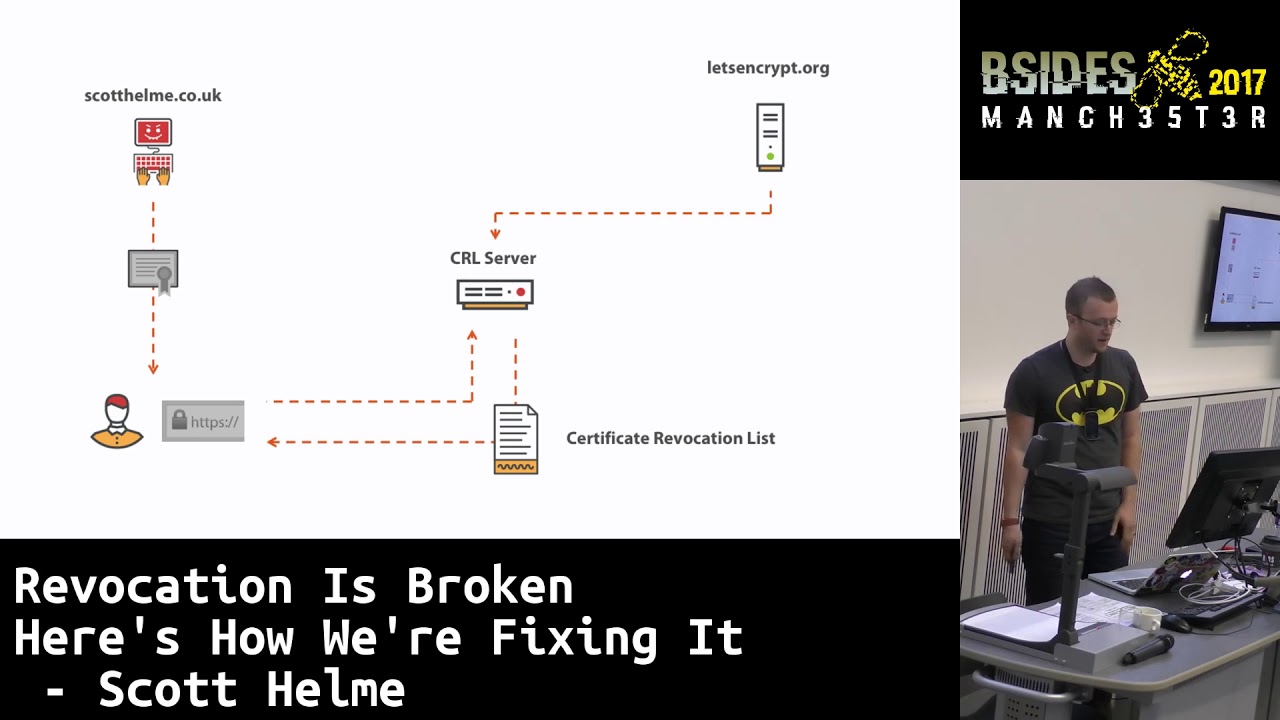
this I knew it blank on um anyway hus yes and the content security policy CSP um as measures that people could use to help protect and then very quickly in 2013 uh we saw Lucky Lucky 13 attacks issues with rc4 rc4 um ciphers were now considered dead broken and the breach attack so in August the same year then TLS version 1.3 development began TLS version 1.3 is our current version current strongest version of TLS um April 2 2014 harple attack came out I'll I'll show this later on um September 2014 cloud flare began to release free certificates and in October 2014 the poodle attack hit SSL version 3 at this point very few people were using SSL
version 3 so it was quite easy for companies to disable and not as big an impact as it could have been however then in December 2014 the TLs poodle attack was released um and discovered that it was not just affecting SSL so in February 2015 then rc4 was prohibited from use because it's that broken um in May 2015 The Log Jam attack was released in June 2015 SSL version 3 was deprecated in November less encrypt started issuing free certificates with automated issuance so that was more progress in terms of getting all of the sites encrypted and and using better security in March 2016 then we had the drown attack August 2016 sweet 32 there are there are many other
attacks as well that I haven't listed here just for brevity but these are kind of the big ones that I thought were important to include um in January 2017 then sha one was deprecated seemingly before it had been exploited but one month later sha finally failed and shattered was released that broke it so March 2018 then TLS version 1.3 standard was proposed we're still not there yet um and TLS in 2018 TLS version 1.0 was deprecated in August 2018 TLS version 1.3 was finally released this was 10 years following the previous TLS version 1.2 and then in June 2020 Chrome and Firefox browsers stopped supporting TLS version 1.0 and TLS 1.1 because of issues and in September IE followed very
quickly so we're left with TLS version 1.2 and TLS version 1.3 currently there are no known issues with any of the TLs version 1.3 ciphers but there are some weak ciphers in TS 1.2 however um we do still see them a lot hence all of the findings and reports for pen testing um and there's some good reasons for that they're required to support older browsers so if people are using an old phone uh an Android 10 phone or something like that they need to connect to a website they can't connect unless the website supports some of these older ciphers because the browser just configured to use those and not updated um so that's an issue for all
organizations you know they depending on their customer base depending on what devices they're trying to connect with computers they're trying try to connect with they if they need to support it they need to support it so there is an element of risk but we'll move on there I've referenced at the bottom here and I can share these afterwards and share the links but um Ian ristic wrote a book even yeah um SSL um bulletproof SSL and TLS and he has on online a really really detailed timeline that I used as a reference but he's got loads of stuff in it that's really cool and definitely worth a look um a lot of information about certificate Authority compromises
um that I was thinking oh that would be a really good talk but that's for another day so um okay so what I really wanted to do inspired by Jeff's book um and he tells some really really cool stories about high-profile hacks and crimes and I really wanted to link you know could I find a link somewhere along the chain of of what happened in those attacks to weak encryption ciphers to make it real to bring it home for my for my clients um unfortunately I wasn't able to with the information that I had access to interviews that I did with people it's it's possible that there are links um and I just wasn't able to get
into that that depth of those attack those attacks at the time um they're really interesting and I'm plug in the book cuz I really loved it but um I'm not going to talk about them here so uh I didn't I didn't find that however some high-profile hacks for example the TJX company's breach um the attackers were able to crack rc4 based weapon encryption allowing them to steal over 45 million credit and debit card numbers and the breach went undetected for nearly a year causing significant financial damage um I know we know rc4 is really broken and prohibited from use we're not there yet with some of the later ciphers but maybe it's only a matter of time similarly South uh Tempa
South Florida University had weak rc4 ciphers enabled uh that enabled attackers to access sensitive data and student information most heinous crimes there's a lot of stuff Jeff talks about in his book uh about moneya laundering not really related to encryption so we'll move on from that um so overwhelmingly from all of my research my interviews um I you know speaking to people talking about crimes and walking through them it's the path of least resistance for criminals we all know that you know the house with the alarm is uh less of a Target than the one without um so business email compromise is overwhelmingly the first route of entry for to an organization with most attacks
and fishing for websites we're think we're thinking about outdated software with no inv vulnerabilities or authentication weaknesses so at this point in my research I was like oh great well is that is that it is that the end and I started thinking well maybe when all the other doors are closed there's nothing left the attackers are forced to look at something a bit harder like the encryption uh so we're talking about high value targets something that's worth the effort that's required to decrypt uh a chunk of data nation state hackers I have it on good authority uh but wasn't able to get any information unfortunately that this is happening with nation state levels um Banks
governments that that's kind of who would care a little bit more about this I believe so should we care it's really hard to do there's no PR iCal attacks except for the older ones uh there's usually easier methods and probably not worth the effort for a lot of systems but it's not a problem until it is like we saw with all of the other attacks so to quote cryptopals cryptopals is a fantastic resource online cryptopop pals.com is referenc below uh where you can go in and do a bunch of crypto challenges and step through them it it requires a little bit of coding but it's it's really fun H as with a lot of people in the industry
will say the systems that we're relying on today aren't known to be fatally broken but they're in a state of just waiting to be fatally broken so it is only a matter of time we could see in the timeline that the Sha one was deprecated before it was officially broken um the likes of CBC or with the lik of poodle for example H initially it was just SSL that was vulnerable then it was TLS the attacks evolve and it is only a matter of time so let's have a look and see how easy heart bed was to exploit just for example um I would have liked to have done more of them but I ran out of time so we're going to have
to stick with this I'm also going to attempt a live demo here so bear with me uh I don't know if I can get this up on that screen
[Music] okay this is going to be tricky can't see it on my screen whoa okay so for this example I'm using this is so awkward I maybe not do this bwap uh which is an oasp project for a vulnerable web application that also has the server configured with weak SSL so I'll just if I can do this backwards oh my gosh uh right so the first step that I want to do is run a testing tool called test SSL Dosh um to see if the site is vulnerable so show me show you
and forgive me tab is not working properly for me on this laptop 8443 that is going to take a little bit of time to run so I'm going to show you the output first here so you get all the of the output in the terminal but also the flag away outputs in multiple formats why is that not working oh yeah come back other screen right so this is the output here this is really really good tool and it's really helpful for um pentesters so CU it shows everything so clearly it's color coded how easy is that uh SSL version 2 not offered that's okay SSL version three offered not okay SSL version one offered deprecated not
okay SSL 1.1 offered not okay uh TLS version 1.2 offered okay TLS version 1.3 so for all of these the output that you get it runs through each of the protocols these are the protocols that we've got and checks which ones are supported by the website then below here we look at the types of ciphers offered not the actual ciphers the types so here we can see these triple Dez ciphers are offered and that's not good and obsolete CBC ciphers we were talking about Cipher blockchaining earlier offered not okay then below here we've got the testing servers Cipher preference Okay so we've got each of the protocols again uh where's my each of the protocols um sslv2
nothing else supported sslv3 these are the specific ciphers that are supported no server order so the server can be configured to have a preference order this is not and that's not great TLS version one ciphers that are listed here 1.1 1.2 and 1.3 is not supported okay bunch of other really useful information down here that you can flick through different issues with the algorithms offered you did basically look for the red sha one signature is used which is not good issues with the certificate chain of trust certificate is expired not okay not okay uh down here we look at specific call specific vulnerabilities are called out so the heart bed it's vulnerable to Heart blade
so we're going to demo that it's vulnerable to CCS that's um change Cipher spec messaging injection I'm not going to be showing you that today um secure insecure renegotiation is okay poodle is vulnerable to and a bunch of other issues Log Jam based Etc okay so that's kind of nice output that you get from this am I where am I here okay so that still hasn't run yet not sure why there's such a delay with that but I'm going to move on so the next thing that we're going to do is uh run n map so nmap is another pen testing tool that we use this is to confirm the vulnerability in a different way so this
is if we find heart blade is listed then we can use this to check that it actually is SSL heart blade SV P 8443 I'm going to regret this 2168
40130 so that's running I'm not sure how long that's going to take so I'm just going to kill this off because we've looked at the results we don't need it
uh that's going to spit out the results too in the interest of time I'm just going to move on we'll come back to it so the next thing I want to show you is actually running um the exploit script so spoiler alert it is vulnerable um can't spell can't type backwards python 2 heart BL so what this exploit script does is it sends a malformed request to the server that specifies a length feeli larger than the actual payload and causes the server to return additional memory so we're pulling memory from the server before I run this I need to just jump into the server to log in so that there's something in memory okay so refresh that we're going
to log in B bug okay we're in right so let's run this script Port 8443 1 92168
40130 let's have a look fail try again here we go so this is the memory laked uh just have to scroll up to the top to show you what we've got hopefully we've got some information we can use in here yeah pull that screen out a bit ah come
on yeah okay um can I not resize this hold [Music] on stupid computer okay so anyway here we've got you can kind of half see it um apologies for the screen cut off here but here is the URL for the website here is the PHP session to token uh and down here we've got the login username and password can't really see it there we'll probably see it in the next demo so it's that easy right um so then the next thing I want to do is clear that and we'll run um Metasploit so this is another tool we can use to attack it and we'll go back and check this here uh so here we can see the results
from the nmap scan shows on Port 8443 it is vulnerable to the heart blade vulnerability so we we go back in here madis flit is up and running almost there we go so we're going to search heart blade and we're going to use this op SSL heart blade so use auxilary
scanner C SSL SSL open SSL heart GL okay right show
options okay so we scroll up this is socky to right so here we've got to just set the remote hosts to our Target and remote Port so set our hosts to 192.168 30 uh 40130 40130 set Port or Port to uh what was it 8443 okay and show actions so on scan so
run come on okay so then I'm going to set action to dump front
okay and this gives us a bin file so we'll copy this uh copy and paste that in here okay we're going to use strings because it's a bin file we want to get some useful information out of it strings um paste hold onast selection uh that's not what I meant to do it's not what I meant to copy copy backwards
right section strings past selection and this pulls out you can see really clearly this time the oh the URL is from the referral header the cookie is the session cookie there and the login B and Bug username and password so that was so easy right um so let's move on um get my screen back where's my there we
go okay so that was easy right um that's my video move on uh so I also promised some practical takeaways so you have seen me run SSL Labs no you haven't seen me run so there's a couple of different things we can do here we can run SSL Labs that it's available online for everybody I'll show you that quickly um run test SSL which is my preferred tool as pentester and we can run open SSL commands manually to to verify things um and check the certificate manually so very quickly SSL Labs you browse to SSL labs.com I'll not do this demo because we don't have time um put in your website don't forget to take do not show
the results on the boards so I've put in vertical structure.com we get this kind of a result um a nice A+ rating uh I can't run SSL Labs on the vulnerable server that I have because it's not accessible to the Internet so um then my screenshot didn't paste there sorry about that uh so here on the left ignore the text on the right um test SSL Dosh we run the command at the top and we get that kind of output but you've seen that already and you've seen what was supposed to be on the right was supposed to be the output from um the vulnerable app with the different colors so um then manually verifying we look at
the website if we browse to the website directly we'll get a certificate error how many people get certificate errors and just ignore them um most of the browsers won't let you ignore them so easily anymore but here we can see we can open up the certificate and get all the information about it in there we can also use open SSL commands open SSL sore client connect to see if we can connect and then we can run the these commands the head and or is for the testing the insecure renegotiation so basically you connect then you enter the head string there followed by or hit return and it it sometimes well if it's configured correctly it will just kill the
connection sometimes it will let you do it multiple times if it lets you do it more than five times it's insecure renegotiation um so then below there's some commands there to show um running open SSL connect to see if the first one is to see if null ciphers could be supported and that it failed I think can't see that properly um and then the next one was tripled as ciphers so that connected and showed the results below um so first of all I just want to say how do we protect against it so disabling weak ciphers is the best way to to not have that issue however as I mentioned earlier to support Legacy ciphers we can't always disable week
ciphers um so many companies are hamstrung by the use of Legacy browsers and they have to support them also certificate providers like cloudfare charge a premium um for like Enterprise fee level to be able to support some of the stronger weak ciphers um so yes that's it that's me uh hope you got something from it today I think maybe have don't have time for questions no so but I am here all day I'm here for breaks I'm happy to talk about crypto and if you know Lo's about it and want to share information with me I would love to hear it so thank you very much everybody