Revocation Is Broken, Here's How We're Fixing It
Show transcript [en]
can everyone hear me are we okay if I just speak loudly all right yeah good okay thanks so much for coming I'm here today to talk about something called certificate revocation this is me everything that I talked about today all the technologies all of the different things you can find them on my blog of my Twitter handles up there as well so please follow me it's how I judge myself as a person by my number of followers but what's what's not there is my job title I usually go back security researcher I spend a lot of my time doing various bits of research looking into the security of websites hardware devices various bits and bobs but I I do a lot
of what a hacker would do but I don't use the term hacker I don't really like it it's a bit of a media buzzwords it also has negative connotations if you tell people you're a hacker they usually kind of like start turning their Wi-Fi off at the side but the main reason is that according to Google image search I don't look anything like one anyway so kind of may as well not bother but I have done a few bits of research I've got some nice coverage this is a more recent one password reset on any electric or gas account for a big provider here in the UK this is a really good one nice on the app that controls
their cars like in all the functions of your car they literally copy and pasted code off Stack Overflow because they even left the typo in the code sample on Stack Overflow in their app the research that I did I presented it still come a year or so ago now I did with Troy hunt and of course the breitbach's Rooter if I go into trouble for blowing up with my shotgun as well but more recently I appeared on BBC click if you want to know what not to do to build a secure device watch this episode if you haven't seen the Nomex most secure email server in the world you should definitely watch this just for the comedy value and literally just
a couple of weeks ago even mentioned DEFCON I was really fortunate to spend a lot of time there with Kate who sat down here at the front and there's another two episodes of click from DEFCON b-sides and black guy if you want to have a look at them as well but I'm here to talk about something that I'm quite fond of those of you see me talk before will know that I like HTTP I like encryption on the web and to do that we all need to go out and get certificates these are the documents that you have to go and obtain you used to have to buy them you can get them largely free now
but you have to go and get a certificate from a certificate authority if you want to deploy encryption on your website if you want the little green padlock and all the benefits that come with it this is what you have to get and I every single day actually I scan the top 1 million websites on the planet but every six months I produce a report on various different aspects of that security and every six months when I run this now you can see that the number of sites deploying encryption is going up so these are all the sites in groups of 4000 from the top sites in the world down to the last 4,000 in the top
million at least and every time I do this not only are more and more sites deploying HTTPS but we're actually increasing the rate at which we're doing it if I represent their data like this it's a bit more clear that we're actually accelerating the rate of deployment of encryption on the web we're deploying encryption on the web right now faster than at any point in history so we are making some really good progress largely in part due to organisations like let's encrypt the free Ca so you don't have to pay for these certificates anymore in February 2016 just after they launched as you would expect they had a fairly low prevalence in the top 1 million sites
but just a year later they'd increase their market share massively because we don't have to pay for these anymore and also you can fully automate the process with let's encrypt so we took away the cost barrier and we took away one of the big technical barriers with that as well so the reason that we have to have certificates like why do we need to go to one of these organisations and get a certificate it's because secure communication on the web isn't possible without authentication we have to be able to prove our identities and we do that by obtaining a certificate to prove who we are so if we think of a typical browsing scenario you open your browser
and go into PayPal and you kind of hope that's PayPal but if you're talking HTTP then it's trivially easy for an attacker to intercept a money to that connection but also to just impersonate PayPal they can just say hey I'm pay and you have no way to know that they're not that's why we challenge websites to provide a certificate to prove that they are paypal calm this is what we need them for and the the problem that we're trying to solve you've probably all seen and heard of this before in various different forms but it's essentially this on the internet nobody knows that you're a dog and that's exactly what certificates fix this problem of identity we can prove
that we are not a dog so the process of getting a certificate is really easy we have our website set up and we send something called a CSR which is a certificate signing request it basically says I'm Scott hand I've got a UK I want a certificate here's a few other bits of information and if we can prove that we own the domain typically by an email or they will ask us to host a challenge file at a random path then we satisfy the proof of ownership and the CA will issue as a certificate back we put that on our server and then when the browser comes along we just pass it down to the
browser to prove our identity and we get green HTTP everybody is happy this is the protest at a really high level and certificates are just text files there's nothing really fancy in a certificate they just have a various bits of kind of key value pairs of data the common name which domain name was this issue - who issued it so the browser can see if they trust the issuing authority and things like the valid from and to dates as well it's literally just a text file with a signature at the bottom now the idea of the certificate is we present it out to the browser to prove our identity but obviously there has to be something a
little bit more to that because if we just give up the certificate somebody else could just grab my certificate and then present it and say I have this certificate I'm Scott how local UK you have to have what we call the private key on your server that's associated with it this is the part that you need to actually use the certificate and as the name suggests they say private key supposed to be known only by you and remain securely and safely on your server hands up who has perfect security good nobody right things I all said stuff happens I'll go with stuff happens and sometimes keys get lost we had recently Hartley was probably the most
notable example of this hardly too sensually allowed an attacker to just download a copy of your key off your server so it's no longer a private key the bad guys can literally just steal a copy of it once they get a copy of your key or they obtain it in some way maybe someone left them laptop on a boss so they broke into one of your service it doesn't matter they've now got your key which means they can now use your certificate and prove they are you so you now have somebody on the internet that isn't you that can prove they are you and this is a really bad place to be because if this
was a certificate for PayPal com and I could tell people and prove to people I was PayPal com that's a really bad situation so we need revocation this is this comes from the Tor title revocation is the ability to say something bad happened with this certificate we need to cancel it we can't just ask the bad guys to delete it and stop using it we need a technical measure to say look something bad happened to this document I got hacked whatever but we need to no longer trust this particular certificate so something bad happened Harper Lee came along whatever it was we need to perform a revocation so we send a revocation request to our CA and say
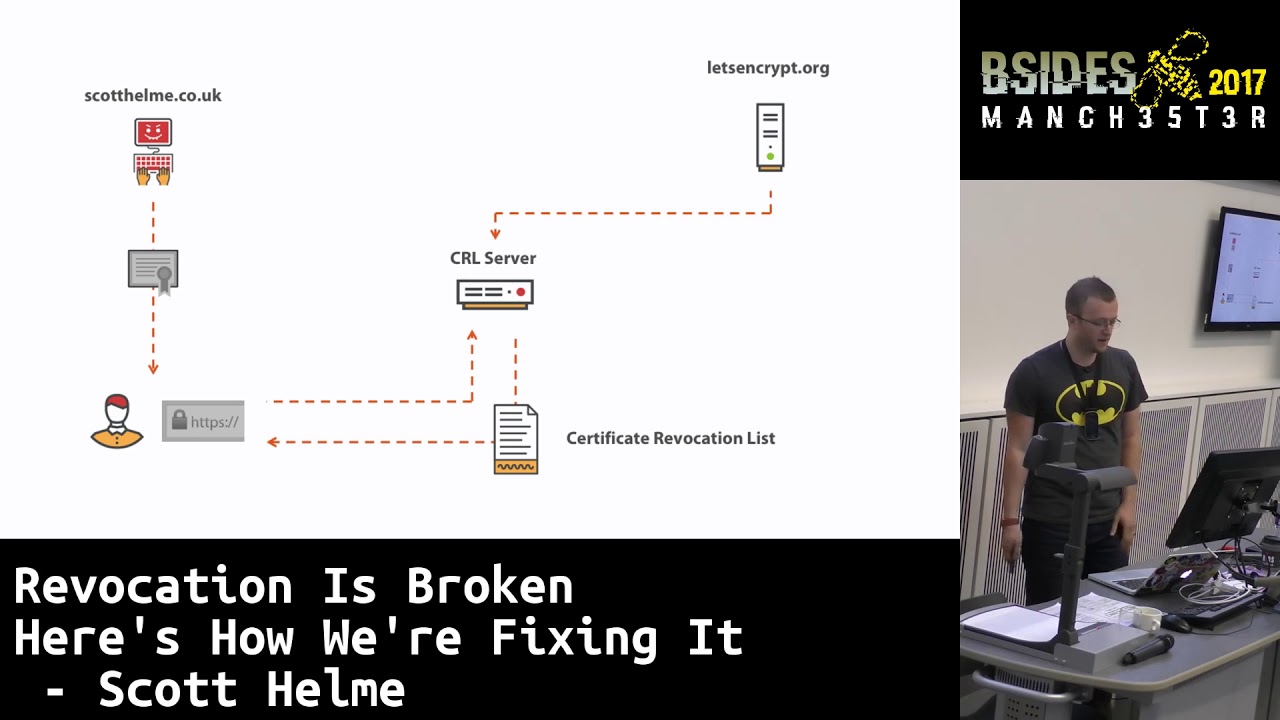
look we've had a really bad day we've been hacked somebody's managed to compromise our servers we need to distrust this certificate we need to mark it as no longer valid and the CAS have two mechanisms to do that the first of these is a CR L is called a certificate revocation list and it literally is exactly what it says it's just a file that is a big list of all certificates that have been requested to be revoked you can go to a CA and just download one of these and have a look through it it's just a document with a big listing the other mechanism is something called OCSP now this is the online certificate
status protocol and this differs slightly from a crl because it's Errol is just a honking big file with everything in it with OCSP what you do to the responder is you say is this particular certificate valid yes or no so rather than downloading a massive big file you just ask a yes/no question about one particular certificate so the idea being here is that when you've been compromised in the bad guys trying to use your certificate what the browsers actually do in the background is when they get that certificate they will check its status to see if it is revoked in the browser historically they used to use the CRL so it would get a certificate it says right I've just got
this certificate I need to know if this is good or bad so it would go download a copy of this CRL it would then look through that list to see if the certificates on it if the certificates on it is bad is revoked and the browser knows not to trust it so we get the CRL we see the service part and it closes the connection is said this certificate is revoked I'm not going to accept it we're safe similarly with OCSP it's essentially exactly the same thing that happens again except with the OCSP responder like I said it's a simple yes/no question so the browser actually sends the serial number for the certificate and says is this particular
certificate valid and the OCSP responder responds back and says it's either good or bad we essentially get yes/no answer on whether or not we can use it so if the or CSP response comes back and says revoked again the browser will reject the document it won't accept it and it will close the connection so we can protect ourselves if we lose this certificate now the only problem the browser has is every time it sees a certificate it doesn't know whether or not it's actually coming from me or from a bad guy whether it's been stolen so the idea is that the browser kind of has to check the status of the certificate all the time because we could have checked it
yesterday it could have been revoked last night and if we see it again today we need to check again because it could have been revoked since the last time we saw it so it doesn't matter whether we have been compromised or not the browser always needs to perform these checks there is some cache period in there so it's not too aggressive but we have to frequently check the revocation status now if you go to a website you get the certificate and you reach out to one of these revocation servers what happens if they look like this what should your browser do if the revocation infrastructure is down maybe your CA is being DDOS'd offline maybe someone
turned off the data center by accident it doesn't really matter you reach out to the servers and they're not there what should the bra do now this isn't the only problem with revocation we obviously this is the obvious problem of the infrastructure being offline but there are some other drawbacks to revocation as well I talks about the certificate revocation list being that big file with a list of all revoked certificates in it how big do you think that might be someone shout out a number guess what do we think because we have to download this when we go to a website we have to go and download this other file before we can connect so this this stops us loading
the webpage what if that was like a 50 kilobyte file that's not too bad maybe it's 500k we're now pulling down a half Meg file just to load Facebook what if they hit some Meg what if it hits 10 Meg what if it hit 50 Meg or like earlier this year one of apples CR Elle's hit 19 Meg in size do you want to pull down a 90 Meg file when you open facebook and the answer is no CR ELLs were largely abandoned a long time ago for this problem and many other problems as well OC SP replaced CR ELLs because we like this idea of this simple yes/no question you make a very small request and you
get a very small response in from a performance standpoint is great does anyone know what the problem with OCSP is can anyone guess what the problem is exactly there is a massive massive privacy concern with OCSP because when you reach out to the responder to check the status of a particular certificate the question that you ask is this do I really want to be asking a third-party organization that every time I go to this website and the answer is no because you're now leaking your entire browsing history to some third-party organization that you probably don't even know about you send the serial number for the certificate and of course the CA knows who they issued that to so
they can say all right great this guy's about to go to this particular website because he's just asked for the status of the certificate so he must be about to go to that website so all of these problems coupled together led to what we call soft bail revocation checking so historically if the infrastructure is down or there was some kind of problem the browser would just say nope I give up I can't check the status of the certificate but we move to something called soft fail where the browsers would do a best-effort revocation check so they would try and check the revocation status when they got a certificate the only problem was if they couldn't do it for some reason say the
CA was down you don't want your CA to go offline and pull your site down so if it looks like the CA is down or offline the browser's would just say oh well they're not there so we'll just carry on now how hard do you think it is if you're an attacker especially on the network to simulate your CA being offline all the attacker has to do or the bad guy has to do is this if they see your browser try and make a revocation request they block that request and the browser goes oh well the CA must be down they must be having a bad day so I'll not bother I'll carry on this is what we call soft fail
revocation checking and all of the major browser vendors switch to this years ago we've been doing software revocation checking for a long time and the only problem with software revocation checking is it's kind of pointless because if the attacker can block the check and the browser will skip him the attacker will block it every time because they know the browser will carry on and not throw any warnings the best analogy for this that I heard was from someone I know at Google called Adam Langley and he said that soft bail revocation checking is a seat belt that snaps in a car crash you get into your car every single day and drive to work and you put your seatbelt on and it does
nothing for you but that one time when you come to depend on the mechanism it snaps and you out the window so all the rest of the time when we were using it was completely pointless and the one time we need it is the one time it will fail this is soft fail revocation checking this is what happens right now today so because of the performance overhead of reaching out or making these external requests and waiting to see if the responders there or not what actually happens now today in chromium is this this is what the revocation check looks like in chrome right now today they don't even bother they don't do it Chrome browser does not do any form of
revocation checking for a certificate because it's pointless software revocation checking is totally useless and this is a real problem because as more and more of us get more and more certificates if you lose one you can't do anything about it you have to live with that loss there's no way for you to take it back and undo the damage that has been done revocation is broken Firefox are also looking at completely abandoning revocation checking later this year right now they have a three second timeout on the check so you open a page in Firefox if the OCSP responder doesn't respond within three seconds it will skip it and carry on but now they're saying well we might
just join Google and follow chrome and just completely abandon it that could be here later this year in Firefox and they're not about the to mainstream browsers that don't even do checks so we need to fix this we need a solution to the problem of revocation because these these certificates they are important documents and they carry a lot of power we need to be able to undo all mistakes so the first step in kind of the solution to the problem was Chrome and Firefox both bill proprietary mechanisms into their browsers they're called crl set someone crl and what these vendors do independently of each other is they reach out to the CRL servers for every
certificate authority on the planet so they go to all the different CAS and they pull down the latest copy of their crl and they merge them into one giant big file which is the list of all revoked certificates ever and it sounds really good up until this point but then what they do is they only select high-value certificates as they call them which means that I'm never going to get my certificate in there none of you will and nobody that you know will these are literally trimmed down you can go look at Firefox is because it's open they're literally trimmed down to just a few hundred certificates from the many hundreds of megabytes of lists on the
internet so whilst they're really good you know maybe Facebook would get those in here or maybe PayPal would but they're largely just for CA certificates really high value certificates unfortunately because they don't want to embed a really large file into the browser so these lists are trimmed so heavily they're no use to me or you the next option that we have a while back to try and fix the privacy issue with OCSP that we talked about where you're asking for the status of a certificate there is something created called OCSP stapling now in OCSP the browser reaches out to the responder and asks for the status that's the privacy League we're asking for the status for
the certificate for pornhub.com so what we do with OCSP stapling is the browser doesn't actually make that request instead our server makes a request and fetches the OCSP response from the OCSP responder and it's called stapling because the idea is we then staple that together with our certificate so we get the certificate the OCSP response staple them together and give them to the client and say I've already been to get the OCSP response for you and we send them both down to the browser at first glance that sounds kind of weird because we're almost self certifying our revocation status but the OCSP response is signed in exactly the same way that our certificate is signed so
just like the browser can look at our certificate and say this is a legitimate document it can also look at the OCSP response and say this is also a legitimate document so there's no concerns from like a fraud or forgery point of view there and we stopped the browser doing that privacy leaking OCSP request the only problem with OCSP stapling is it's optional now if the bad guy has a revoke certificate are they going to turn on OCSP stapling and say hey here's a certificate and also here's the revocation notice so don't accept it they're not gonna do it Oh CSP stapling is a performance enhancement and the bad guys aren't going to turn this on so
next up we have a new flag this is really new Firefox is the only browser that supports this right now actually because it's so new and it's called OCSP must staple and you can probably kind of guess where this is going from the name so when we go to the CA and request our certificate you can now ask that they set a special flag inside the certificate and it's called the Oh CSP staple flag and when the browser receives our certificate if this flag is set the browser must require a no CSP staples have been served with the document otherwise it will reject the document and not accept it that's how simple it is we asked them to set the
flag the flag goes in and when the browser gets it it knows that the OCSP stapling it OCSP stapling session it just looks like this we have our certificate that we saw earlier and we literally just get an extra piece of text in there like I said certificates are just text files so we just add a new flag in that says Oh CSP must staple is enabled for this certificate so if we then take that and think about this combined with OCSP stapling we now have a situation where we have to enable OCSP stapling but that means the bad guys also have to enable OCSP stapling if they try to use our certificate so we
can do this perfectly fine we fetch the SSP response and we staple it if we switch this situation to the bad guy the bad guy now goes to the OCSP responder we've revoked it so that OCSP response is bad they says the certificate is revoked so the bad guy has two choices they can serve the certificate without this response which means the browser will reject it or they can serve it with the OCSP response which means the browser will reject it so both scenarios the bad guy can no longer use our certificate because they have to provide the revocation status with it or the browser will decline to accept it now this is this is literally
brand-new this year as I said Firefox is the only browser that currently supports this and this is literally the only way right now that we can actually have reliable revocation of our certificates if you use a certificate right now today and you don't have the must April flag set there's nothing you can do about it and these things can be valid for up to three years if you get one of those and lose it in the first month you've got two years in eleven months with which a bad guy can run around on the internet and pretend to be you and you can't stop them so I think this is going to be a really important kind of step in our
process to fixing revocation but this is all good and well but this only applies to certificates that we know about if we are compromised then we lose a certificate and we know about it we can ask for it to be revoked what if somebody manages to trick a CA into issuing a certificate to them this is called Mis issuance it happens every now and again and it's where someone we saw an incident 2014 I think it was with diginotar where somebody actually hacked into the CA systems and issued themselves a lot of certificates for Google com Google can't request revocation of those certificates if they don't know they exist that's a problem because somebody's issued them sneekly
or hacked to CA or maybe it's someone inside your organization that's got a certificate through improper channels but there is the very real possibility that you can go and get one of these documents and the organisation may not be aware of its existence so we need more transparency in the ecosystem if a certificate is issued for our domain we need to know about it because that's ours and right now you can so there's something new coming it was originally coming October this year but unfortunately after pressure from the wider community the deadline has been backed off to April next year called certificate transparency and it aims to completely resolve this situation where right now someone could get a
certificate for your domain and you wouldn't know about it if you don't know about it you can't take any action so the idea we've CT there's three different ways that we can do this the CAS have their original infrastructure to maintain and it adds an additional requirement for them it's called a CT log this is the certificate transparency of log it's a completely publicly accessible open log anybody can go and view these logs and the requirement will be that every time a CA issues a certificate they have to write an entry into this log to say I've just issued a certificate for PayPal com here is a copy of the certs and they are required
to put that in there so we can now monitor these logs and have full transparency about everything that CA is doing these are really powerful organisations they can issue certificates for any domain in the world we should have had this level of transparency in the eco system a long time ago but we don't and it's now on the way now anyone can submit to a CT log the idea is that when your CA issues a certificate they will write it into the log and when you do that you get something back to prove that you put it there it's called an SCT which is a signed certificate time stamp so you go here you go mr. log operator here is a
certificate to go in the log and the log gives you back a proof that you've done that this is your document to say I have definitely put this certificate in this log here is my proof but it doesn't have to be the CA that does that you can do this as the operator of the site or literally one of us could just see how our laptops now and go submit a certificate to a CT log they're completely open append-only logs but we need to prove to the browser the certificates have gone into CT logs because the browser needs to know is they say publicly known about certificate this hasn't been issued in some shady deal it's not the result of a
website being compromised like a CA we need to prove to the browser when we give it a certificate this is definitely out there open and public it's in the CT logs there's nothing shady going on and to do that we have to give the browser the SCT because we don't want the browser having to go and check the logs manually it introduces another performance overhead if we give the browser the SCT then we can satisfy this requirement for a transparent certificate there's three different ways that you can do this this is the one I think 99.99% of websites on the planet will do because it requires them to do absolutely nothing this is how I think CT will come into existence
because most website operators I speak to don't even know what CT is and we were almost at the deadline so you issue a CSR you won't go to your CASL I would like a certificate for my domain and what happens is your CA will log these to the CT logs on your behalf the technical name here is the pre certificate so basically your CA makes the entire certificate but right before they sign it at the bottom it's called a pre certificate and you could submit pre certificates to the logs now the current requirements are that you submit to at least three different logs this is largely just for redundancy purposes but there's also a requirement that at least
one is operated by Google and at least one isn't operated by Google too make sure we have some diversity in the ecosystem as well so your CAE gets this request it makes the pre certificate and it submits them to the logs and of course your CA gets back three s CTS to say I have definitely done this here is my proof and it then literally just pops those SC T's inside the certificate signs it and issues it back to you so you now have a certificate with the three s CTS or more actually embedded inside it you get that certificate and you give it to the browser like normal the browser can extract those SC T's and
make sure that this is a publicly known about a certificate there's no additional checks on the browser it doesn't have to make outbound connections it doesn't have to do extra stuff all of the information that it already needs is in the document and most website operators are probably going to end up using this approach because most website operators don't know about C T it seems but there are two other ways that you can do this if you don't want to completely trust your CA to get this right for you you can take some extra steps yourself the first of these is a TLS feature extension now essentially this is very similar to what we saw with OCSP stapling so we go and
get our certificate as normal the CA will then log these oh sorry we will then log these into the CT log servers ourselves so we can pick which log operators we want we can have 3 5 10 20 it doesn't matter we get to choose and we log them and we get the SCC's back what we then do is service SCT is alongside the certificate so just like we did with OCSP stapling you can give the browser some arbitrary extra document and say here you go I've got some SC T's for you as well the browser is still satisfied the browser still got the SC T's that it needed to prove that this has been logged and similarly
there's also OCSP stapling and this is exactly the same OCSP stapling that we just talked about except this time when we got a certificate issued the CA will log the SC TS inside the OCSP response so we should already have OCSP stapling enabled and if our CA puts the SCT s inside that we will issue the OCSP response with the SCT is embedded in it now these two second mechanisms don't worry about them too much most websites are probably not going to configure this or do it because it's quite a technical implementation pretty much all websites are going to depend on the first method where they were embedded inside the certificates but there are extra options there if you
wanted kind of control your own destiny so that's like a couple of the larger issues fixed there but we still have another kind of problem in the ecosystem in that you can't actually say to a CA I only want to buy certificates from Symantec I only want to buy a certificate from digi cert technically only CA on the planet can issue certificates for you and you have no way of expressing whether or not you actually want them to do that so we need a way to authorize specific certificate authorities to issue certificates for our domains and there is a another new mechanism coming to do that because we have our preferred CA like lesson crit
but there's hundreds of other cas on the planet and all of them can issue certificates for your domain and we need a way to be able to assert our authority this is our domain we should be able to control who issues certificates for this so I really like this mechanism because it's kind of super simple it's called certificate authority authorization does exactly what it says on the tin in that it allows us to authorize specific CAS to issue for us and we do this with a really simple DNS record there is a new DNS record just like we have a records or text records there is a new DNS record called a CIA record and inside
that you can list the specific CA that you want to issue certificates for you so for me for my website I only want less encrypt to issue certificates to my domain nobody else so I put let's encrypt org in there you may be a large website you may have multiple CAS that you want to issue for you that's fine you just specify multiple CIA records but these are now the only three CAS on the planet that you have authorized to issue certificates for your domain you can start to assert your authority and your preferences and this isn't just from like a bad aspect from a mission standpoint maybe as an organization you have a contract with the CA that says
you know we'll get an exclusive contract with you guys and we'll only buy our certificates from you so when in your dev team goes off and tries to get a certificate from another CA they will block issuance they will make sure that you are complying with your agreement and you can also ask that the CA notify you as well and say if someone comes to you and asks for a certificate for my domain block it and tell me that somebody tried to do that so you can also get feedback from and this is a really powerful feature to have and it doesn't really add much overhead to the system so when we go to request one of our certificates
we send the CSR to the CA and at that point the CE just has to pause and just quickly check the DNS and say am i authorized to do this I need to go and check this CoA record to make sure I'm permitted to do this checks the DNS looks good I'm authorized to do this there's your certificate and off you go using it as normal so some of these mechanisms are really simple and they allow us to assert a lot of control or authority and we can get a lot of protection back from them see T especially most staple is quite young I think we'll speed perhaps chrome starting for early next year once we get
Firefox and Chrome covered we're a large portion of the way there though the two of the largest browser vendors I think they have like a 70 plus percent market share between them anyway but the problem still remains that right now today if you aren't deploying any of these mechanisms then there's very little that you can do to actually protect yourself if you lose one of these documents we're all in a rush to deploy encryption on our sites and to get more certificates but if you lose them if you have a bad day if something happens there is nothing that you can do to take that back and what you need to ask yourselves your organization is if
somebody did get a certificate and could prove that they were us what's what's the risk what's the harm if you're a PayPal or Facebook or maybe the BBC that's a really bad situation to be in so I want to leave you with the question can you revoke a certificate right now if you compromised if someone got into your servers if the next heartbleed came along and we have to do mass revocation could you actually take back the trust in these documents that you have had issued thank you very much [Applause]
I left time for questions I hope they're awesome yes okay go no that's really good question so some organizations deploy their own internal private CAS all of these apply to public CAS because they're the only ones that we care about they're the ones that we want to hold to this highest standard if you operate your own internal CA this all falls down to you there's an organization there's another one yeah well they and I so really another very good point is that there is a particular issue with Apache right now in that if it reaches out to do the OCSP request and it gets a bad response or a malformed response app actually actually cache that and user in
won't check that's a bug in Apache and we need to pressure the server vendors to fix their implementations of OCSP stapling it is quite young as I said Firefox is he on the browser that will enforce this right now anyway I have several tickets open with Apache and nginx to fix specifically OCSP stapling issues because I want to see people and websites deploying must staple it we need this feature so yeah it's still quite young there are a couple of kinks I is weirdly this is the one thing that I is is good at so you know Apache and nginx need to fix their bugs you know there's nothing more that we can do it's down to them to sort that
out yeah the wonderful open SSL another question there was one yes so it was really good question it was about the life expectancy of a certificate because obviously the point now is that the longer the certificate is valid for the more of a problem you have if you lose it if is if the document is probably for three years and you lose it in the first month you're screwed for two years in 11 months let's encrypt only issue 90-day certificates so if you lose it in the first month the attacker only has two months before it expires anyway instead of two years in 11 months and there are two different directions that the same direction for two different
things that we're looking at here one of them is reduced lifetime certificates which is where we can ask for things like 90-day certificates and then the next step after that is very short-lived certificates where we're talking about certificates that are only valid for seven days and the idea in the goal there would be the if we only have certificates that were valid for seven days we wouldn't care about revocation checking and we could just completely skip it because the document is valid for such a short time it's like MIT we lost it it'll be gone like by Tuesday so the only problem is that the maximum age of the certificates is defined by an industry body called the cab forum and
it was ten years originally and every time they've had ballots they've voted and pulled it down and we're currently at three years and there was a ballot earlier this year to pull the maximum down to a year and all of the cas apart from let's encrypt were like nope we're not doing that and they voted against it and we're currently trying to ballot to pull the maximum down to two years but the industry body's slow to responding to reacts most of the cas acting their own commercial interests and they don't want to pull them down they don't want to reduce the lifetime but we we just need to keep pushing that enforcing it as an organization you can also elect to
have shorter validity periods if you don't want the three year certificate you should never get through your certificate you should be thrown in the ocean if you get a three year certificate maximum twelve months absolute maximum but try and get it less than that you can elect to have like 90 days certificates and you've got a smaller window of risk after a compromise
[Music]
so that's another really good one there's been quite a debate raging online about this where if I get it to mean it's like PayPal - support com that's not PayPal but it kind of looks like you could trick someone to think that was PayPal quite easily and then you can go get a certificate and get the green padlock and HTTPS in the address bar so make it look more legitimate I'm really caught up on this and I completely disagree purely simply because the job of a CA when they issue a certificate is to challenge you to prove you own the domain there's a technical requirement do you own this domain yes you can have a certificate no
you can't have a certificate people getting really mad at Less encrypt because they keep issuing these PayPal related phishing certificates but nobody gets mad at registrar's for selling it why did the registrar sell that domain if it's a bad domain why are we complaining about certificate issuance it shouldn't have been issued why DNS resolvers resolving it wire browsers opening the page if we're pushing towards a hundred percent encrypted web and we are if CAS have other criteria for issuing certificates they effectively become the gatekeeper of what can go online they become powerful sensors of the web their job is a technical requirement and they have one make sure you own the domain there should be no other factor in that
because if we get to a hundred percent encrypted web and they can choose who gets a certificate or not they can choose who goes on the web or not and that's really not a place I want a commercial organization to be I think that we should depend more heavily on things like Google Safe Browsing which is doing a fantastic job and the other interesting thing about this now and I don't know why they're not doing this is that some CA is already elect to log to CT so if you register your brand-new paypal phishing domain and get a certificate that certificate goes into CT we immediately know that domain exists and you've not even set it up yet
you haven't even got your phishing page in place and you've just told us that your domain exists so we could flip this around and use CT to find these PayPal phishing domains why pay par not doing that why are other organizations not looking at CT now and saying oh well we've just seen this like substring of PayPal what does this look like this looks like a phishing site will take some action about that so there are a very strict set of guidelines if you want to become a CA you need to go to all the different vendors like Google Microsoft Apple and you actually need to apply to be a CA within their infrastructure within their
software so you go to Microsoft and say hey I want to be a cm in Windows you need to get into the Microsoft trust store as long as you meet the criteria and continue to meet the criteria then you are a CA if you as a CA don't meet the criteria of that particular trust or operator then it's at their discretion what action they take we're seeing a big argument about Symantec online recently because Symantec have screwed up like more times than I've had coffees today it's really not a fun place to be and there's been this big war raging online should we distrust them and the only problem is if you distrust the CA all of
their certificates becoming valid which means all of the websites that use them start working so they're kind of kind of fumbling around and looking for a way of what we need to penalize them but we don't wanna hurt or the collateral damage of the sites that you use them it's still in progress they've largely agreed on what the penalties for some on set will be but as I say it's down to the trust operator if you're a CA and you want to get in the trust or play by the rules if you don't something's gonna happen to you and you shouldn't then complain when it does because you didn't play by the rules
yeah you see anything anything that involves legislation in this kind of space worries me because legislation cannot iterate as fast as we do even in our even in the industry we operate in with the lack of agility that we have we can still iterate faster than legislation can so any kind of introduction of legislative restrictions concerns me because I worry that we may move faster than they can legislate for them and it kind of ties in well what I even said in his talking that the internet isn't like a country level thing it's a global network and you know to say okay well your Verisign you're registered in the USA you can only issue certificates to comm and you know this
Greek TLD you can only have CA issues from it I can't see that ever working and I would hate for them to try because it would probably be an absolute mess the furiously waving in the bag so yeah there was one of the problems that we have with the CI infrastructure is there a lot of people there's like there's like two different cameras we have CAS and there's an alternative called Dane and something called TLS a and we looked at the CIA infrastructure and the situation was either we fix it and make it better or we rip it out and replace it with something else we are already quite a long way down the road of fixing it all
of the stuff that I talked about today was geared up towards fixing the CIA infrastructure the only problem with using something like Dane and TLS a is the straight off the BI requires widespread and fully supported DNS SEC which we aren't even close to here in the UK because nominate don't seem to like DNS SEC countries like Norway they were doing really great they've got over 90% of their domains already fully DNS SEC supported the other issue is well is DNS SEC is controlled by governments or the root zone keys are controlled by governments which would have poor Gaddafi in charge of the da ly root zone in the Arab Spring and stuff like that
is and we're still we're just taking one entity that signed something and switching it for another entity that signed something so he's it doesn't really change anything we just change where we're signing something so it seems like a lot of effort to move to something like Dana and TLS a when it's kind of very similar to the PKI in the you know not much is not much is different I do agree with DNS SEC though you know this DNS with integrity there's nothing not to like about that Oh DNS SEC adoption is is terrible and continues to be terrible yeah and the other thing with DNS SEC is that we've already largely worked around the
problem of DNS having no integrity like you do a DNS lookup you have no idea what the IP address is but you make a connection to it and ask for a certificate in the TLS connection if your DNS had been spoofed then they won't be able to provide a valid sir anyway so we kind of largely worked around the problem that DNS set fixes anyway at least that's my view so OCSP response is a valid for a maximum of up to seven days so as the host if you were OCSP stapling what you should do is if you get a fresh OCSP response like once a day you could weather a six-day outage of the OCSP responder and CAS are
mandated by the cab forums baseline requirements to have 99.9% uptime on their responders anyway so as long as you refresh at least daily you can weather a six-day outage of the responder and that would be unprecedented if that happened anyway so I was an advocate of HP KP and have been for a long time it protects us against the Mis issue in scenarios the only problem is it's a very I've got a couple of articles on my blog about things like ransom kp/h vkp suicides I think once we get to the point where we have CT and forced and Monday Ted and we have good support for must staple the requirement for HP KP kind of fades away because we've now
got full transparency in the ecosystem and we can actually take back the trust in the document so we kind of won't need hey I mean there's still a technical use case for hey tree KP ball we're like 99% of the way there with these really easy mechanisms so we won't bother with the really hard one for the extra 1% anymore yes yes next question anymore yes so yeah the CA is obviously required to check the DNS record and then respond appropriately based on what the record says if they choose not to if they disregard what he says in the CAA record then that would put them in breach of the baseline requirements which means all of the browser's could
take action against them so that would be a really risky proposition for them because the potential penalty for disregarding CI a would be loss of trust so yeah because that would incur an outbound check from the browser an absolute minimum a DNS lookup and you know we have like trillions of page views a day that means like trillions of DNS requests no one no one's ever going to interest no one's ever gonna I kind of create something that slows the browser down because the browser would have to do that before it loaded the page which means it sits in front of TTF B no one is ever going to get anything approved that kills or has a negative
impact on TTFN B it's just not gonna happen any more questions now I think we're good then thank you [Applause]





