The Homeland of Things (HoT) Framework
Show transcript [en]
alright hello everyone and thank you for attending my name is Daniel Wes and today I'll be discussing the homeland of things frameworks alright so a quick bio on myself I'm a cyber operations NCO here in at Fort Gordon in the US Army I'm also a graduate student at Penn State in the homeland security program and College of Information sciences and Technology I'm originally from LA not the California type so lower Alabama hey class how you doing so I started working with computers about twenty years ago when my grandfather built my first workstation out of some spare parts he got from his college and then from there I I just played around with the computer cuz I
didn't have anything better to do we had a couple bootleg games but that was about it so I learned how to fix the computer myself and my teachers frequently pulled me out of class to fix their computers for them and then since then I've gotten a wide knowledge base of from anything from cyber security to information assurance and NIT so originally what sparked my interest in the IOT was my trip to Hamburg at the chaos communication congress so I came back from there and I was like why is there so many problems with this thing called the IOT and I had never heard of the IOT prior to this so I went out and I researched and I learned more about
the IOT and then one of my previous bosses was like hey you know you should ask more questions and seek more answers and then try to build some kind of product to actually do something about it so a fun fact about me I love jamming out to EDM music with my daughter we love dancing around in the in the living room on Saturdays and Sundays ya know videos of that of course online all right so a quick disclaimer so the homeland of things framework is not affiliated with the US government you're gonna see a lot of US government doctrine in here that's cited however it's completely separate this is all from publicly available information so
everything that you see in here you can go out and pull down yourself and all of my opinions in here are mine of course and they're not opinions that reflects what the US Army says or what any other US government entity says all right so a few acknowledgments so Michael and Sonny were my fellow classmates at Penn State that helped me to write the hot framework as part of a paper for our information security management course dr. M he he allowed us to write this framework and had no objections it was a little beyond what was required for our paper so it's you know it was overboard but a lot of my classmates at Penn State
they'll they want to do what it takes to get it done not necessarily go the extra mile so I was really appreciative to both Michael and Sonny that they allowed me to to expand a little bit further and pursue my dream of doing something about the IOT my cyber Syndicates family kealan and alex both of these guys have mentored me for quite some time kealan spoke last year here at b-sides and Alex spoke the last two years I saw them come up here and talk and it really helped me to want to come up here and actually speak before you today so dr. McGee so dr. McGee is my current boss he's been quite a leader so sometimes you'll
meet some of these folks their credentials they define who they are that's not the case with dr. McGee he he puts all that aside and he allows it he allows collaboration to occur between him and subordinates so I really appreciate him and the boss that I was talking about I previously had who who helped me to to actually go out and do some research was Scott Smith I want to tip the hat to him as well so Aditya he runs the pentester academy an IOT exploitation course I've never met him personally but I want to thank him for making that course publicly available and and very cheap for us to go out and get some training on IOT
security it's very accessible and then the Olas peyote project Daniel and Craig I've never met either one of these guys either however I want to thank them because without them the hot framework wouldn't be what it is today and then my family and friends I want to thank them they allow me to pursue my crazy projects and they don't give me grief about it they don't my wife she knows that I'm sitting up till 1:30 in the morning working on one of these things and she just falls falls asleep turns over the other way and lets the light just she ignores it too I'm thankful for that and then the b-side Agusta organizers specifically mark
Baggett I ran into him last year after I had written the original hot framework and he told me he said you need to come up to b-sides and you need to give a talk on this and I was like me in front of people and talk there's no way in hell I'm doing that no way so you can see I'm a little bit nervous and I'm kind of sticking the shadow it's kind of guy and get things done from there so I you know I want to extend that thanks to him and then Lawrence of course know Lawrence for a couple years now and he's always been very helpful and providing me some knowledge and feedback on what
I'm doing all right so the ghost of the hot framework so number one we want to bridge the gap between the Department of Homeland Security strategic principles for securing the Internet of Things and then the tactical application or user application so there's a gap that exists there so DHS says do these great things and you'll be secure however how do you get there that didn't exist so number two I wanted to wanted to prevent and adversaries being able to use IOT botanists to attack critical infrastructure that was something that was near and dear to me and then want to promote awareness so people understand the issues but with IOT security however at the same time I
don't want people to just say I'm not going to use IOT I'm not going to have a smart home I'm not going to get connected because that's not the right route to go either innovation is good getting connected is good all right as I stated before the hot framework started as a paper so we were all interested in the IOT as we had heard the buzz word before so we went and we actually did the research however some of the stuff that we came back with was a little outlandish has anybody in here heard of a stealthy doping level Trojans anybody yeah exactly so it's it's a little out there this stuff exists it is possible
to manipulate devices and create backdoors at them at the at the logic levels so like at the hardware manipulating the amount of dopant that's on a logic gate it so however the only way that you can actually discover this stuff is little electron scanning microscope which I'm sure not a whole lot of people have laying around their house or their organization so we kind of I had to dump that when I revamp the hot framework this year all right so the current hot framework consists of thirty thirty seven unique target areas of interests and twenty attack services this totals to about ninety sixty a is across twenty attack services and three layers of cyber space so the current
approach is actionable and it is tactical it is open source and Industry and device independent and I'm hoping it will be dynamic and it will actually react to the changes in the IOT ecosystem and the threat itself so it will also be community driven if I can get help from all of you and then others out there that are interested so I haven't completed all the TA eyes yet but I will completing them over the next few months with what information I have however back to it being evolving and being dynamic it's going to change so it'll never be in a complete state ever and I'm using get booked right now because it's easy for me to push and pull
updates back and forth and also it allows you guys to go and comment and then for me to get that comment as an issue then I'm able to go and reintegrate what you put in there immediately all right so there's several key pieces several foundations to what makes the hot framework what it is today not one who really read it off the slides but I wanted to make sure that you guys had all this on here so the hot framework combines a strategic understanding of the IOT within cyberspace and US government doctrine that wasp IOT project comprehensive vulnerability definitions in this framework for improving critical infrastructure cyber security no NCV he's known IOT intrusions attacks at use
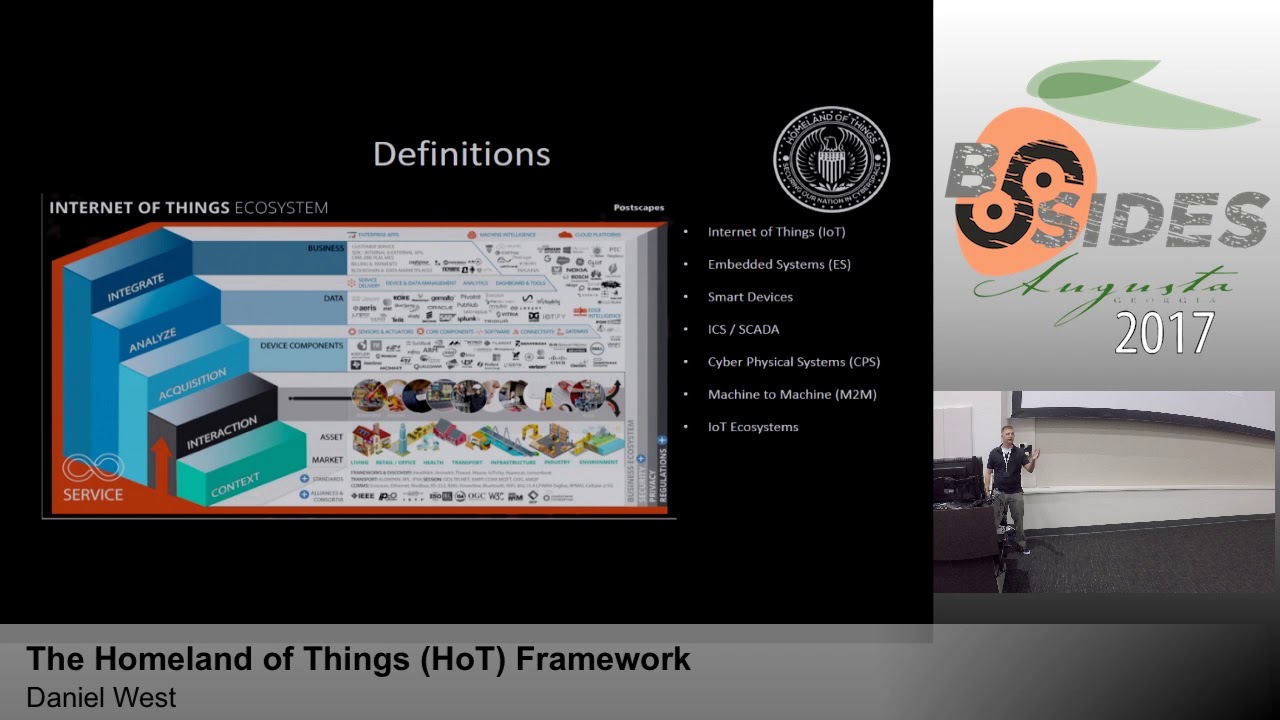
cases and analysis tools training and teaching piece there's a lot of stuff so before we go any further we need to define some of these terms all these buzzwords they're great they're great when you want to get money just like cyber you know yell out cyber and money comes flowing in that's trust me so the IOT typically it processes data is connected and interacts or does some kind of sensing of its environment I read one I Triple E paper that said that there is no universally accepted definition of what the IOT is so it went as far as to say that current definitions vary so much that they are reminiscent of those old story of the
blind man and the elephant leaning towards the partiality that people have you if you're blind you're filling an elephant you have one perception different than another blind man filling that elephant alright so embedded systems are typically a small computer system that is designed for a specific purpose and part of a larger computer system ICS SCADA I'm sure everybody in this room has heard of ICS SCADA at this point ICS SCADA or industrial control systems and supervisory control and data acquisition systems are responsible for controlling a wide variety of functions and industrial equipment on the next slide you'll you'll see something called a IOT with an industrial Internet of Things so that's the new lingo for ICS SCADA
cyber physical systems cyber physical systems are engineered engineered systems are built from in depend upon the seamless integration of computational algorithm algorithms and physical components they're highly highly interactive with their physical environment and then machine-to-machine communications are exactly that they're the communications that are directed between machines and this has actually been going on for a very very long time since when I say the 1960s and an IOT ecosystem I looked for several hours for a definition of what the IOT ecosystem was I couldn't find one single paper that gave me a straightforward definition so was even worse than finding a definition of the IOT so I came up with my own and I basically defined it as a
conglomeration of all the IOT assets applications data and communications interacting with one another in cyberspace and externally with the physical environment alright so these are some of those terms that have been created recently you know hopefully that's not too hard to see my favorite one on there is the Internet of people I don't I don't get that Internet of what what the Internet of people are supposed to be but that was one of those terms that are out there one of the most interesting ones to me being in the Army is to internet about things there's good papers that are published out there about the eye OBT specifically from the army research lab and it's publicly available
you can go read it alright so another key piece of the Hotte framework is understanding the layers of cyberspace this is something that's been debated several times some people say there's three layers some people say there's five layers some people say seven nine there's all kind of definitions for this particular slide right here so just know that Jaypee 3-12 is the ultimate source joint publication 3-12 it's the ultimate source for understanding what the layers of cyberspace are for us in the DoD so that's what I'm using as my source to define what these layers are so the physical network layer is typically defined as the geographic component where the network resides and physical network components comprised of Hardware
system software infrastructure that support the network so when they're talking about networks you got to think a little bit further than just tcp/ip networks so a network can be a can bus network in a car for example a network can be a Modbus network between a master and slave PLC in an industrial control system and I'm not talking about Modbus over tcp/ip I'm just talking about Modbus over the serial links so another important thing that JP 3-12 doesn't actually elaborate on is the fact that a device doesn't actually have to be connected for cyber effects to be applied you can apply cyber effects over the electromagnetic spectrum to a device without actually having any connection
any sustained connection to a network it's interesting so the logical network layer there's this whole the definition really doesn't make sense to me so basically what our team did in the original paper was equate the logical network layer to where the cloud is so that was just the general understanding cloud is here and anything else that uh that would allow an otherwise geographically disparate node to logically replicate a physical connection so if you're here and your server is in Asia somewhere and it in the connection appears as if you're and one network like a Virtual Private Network then that would be something that would reside at the logical network layer and then the cyber persona layer
this cyber persona is essentially just a projection of a persona in the cyber space it's the people on the network that's it all right so going back to SEMA so this is a cyber electromagnetic activities this is essentially the consummation of electronic warfare and cyberspace operations all right the important thing here to understand what the IOT is a the fact that the IOT has a vast amount of protocols and frequencies area use as you can see up there in the post gapes of image and we've been doing Wi-Fi and Bluetooth penetration testing for over a decade now so it's really not anything new you have to use different devices to interact with it so you're not just
going to use one of these appears that I'll be throwing that show here soon one of these alpha cards you're gonna have to use something a little bit different maybe a software-defined radio or maybe you're gonna order some kind of device that is specifically used for one of these protocols so for example no dr. McGee in his in his study for his doctorate he demonstrated the ability for an attacker to manipulate a smart home security system using the z-wave protocol and in this example he was actually able to peer with that with the security system itself with his laptop and he was able to tell the security system to disable itself and he was able
to enter his home steal some things and then rearm the security system as if nobody had been there so this to me falls in the realm for cyber electro-man and activities are if there's a lot more to it than that but at the the basic level this is SEMA all right so the bottom line here I really want this to soak in for everyone we need to just put all the height to the side and we need to focus on the fact that no matter what the buzzwords are you have a computing asset it's made of hardware and software and it can have cyber effects applied when we're talking about the hot framework we're talking
about securing at the device level right so I don't care if it's a your smart home security system and or if it's a thermostat or if it's a PLC you can do the same exact things to them all right so the the actual doctrine that I was discussing before when we wrote the original hot framework there was no doctrine out that was specifically targeting the IOT when we finished our paper around the exact time we finished that's when DHS released their strategic principles for securing the Internet of Things as I oh man so now we have this whole new thing that we could have used during and writing of our paper so what I did was I stepped back and I actually
used it to write the newer version and this is basically these are the six principles that the DHS strategic principles covers the ones with the green plus sign next to them those are the things that are mapped into the hot framework itself the red ones there they really lie at the manufacturer level so how for the promote transparency across the IOT it's concerned with how is the manufacturer sourcing their hardware are they buying them from China backdoored they need to look into that themselves that's not really something you have to user level can do anything about without you know special equipment you can do something about it but it's it's kind of outside the scope right now of what I'm
trying to trying to get at so incorporate security at the design phase that's definitely outside of the scope of what the user can do because you're not designing the IOT device and then connect carefully and deliberately that's up to you so you have to make the decision on whether your IOT device needs to be connected so do you have to have a lexer plugged in all the time no probably not I mean I do sometimes either stay plugged in for two days straight but it's not really necessary if you want to interact with Alexa on a daily basis throughout your day okay but if you're just gonna you know interact with Alexa for a few
moments and probably keep running plug all right so the IOT cybersecurity Improvement Act this came out last month so this is going to address some of those manufacturer level problems that we can't really do anything about as users however they only did this for the federal government one of the things I learned while I was doing my research was that the Federal Trade Commission they wanted to be kind of hands off with do with actually going out and regulating the IOT and forcing manufacturers to incorporate certain certain principles into how they were designing their their devices up front so this was done because they want them to be able to quickly innovate and put deliver a device to the market so
without anything regulating these manufacturers there's a lot of opportunities for them to deliver a product to you that is very vulnerable
so the OIC IOT project again this is a one of the foundations for the the hot framework so I did some some changes from the from the OWASP IOT project itself I removed some of the vulnerabilities that they had in there because they were redundant so I collapsed him or aggregated them into one cwe category and then there was some attack services that didn't believe her attack surfaces so like privacy I thought that should come out so I took it out of the framework so the fic I see one of the things I talked to a couple of folks about when I was incorporating this into the ha framework that so it says critical infrastructure in here but you
can use this for more than just critical infrastructure ok so it builds from existing standards that are already out there and actually maps those standards into the framework for itself and it is technology neutral and it provides a common taxonomy to be able to essentially describe your cyber security posture and where you want to go with your cyber security posture and then how you go about assessing your improvement and then how does to actually related information to stakeholders all right so I'm gonna talk just briefly about the IOT threats landscape specifically with malware and botnets alright so so far these are the this is a malware and botnets that I've researched and I've actually been able
to incorporate into the hot framework there are other ones out there I'm sure that I haven't found yet and so keep that up for one more second because I might ask a question from this so the key takeaway from these examples is understanding where the threats are currently focused so out of those examples 63 percent were directed at password or credential management vulnerabilities it's a lot and you're talking about vulnerabilities that have been around for 20 years so hard coding passwords into devices or having default passwords on your device that's that shouldn't be existing anymore but a lot of these manufacturers are doing it for ease of use for the for the user all right so you can see that 31% were
injection attacks and then 6% were insecure third-party tools so this really demonstrates the need for some kind of IOT security really it should start with the manufacturer but we can't rely on the manufacturer to do something about it alright so here's another example of SEMA related attack that occurred this demonstration really of an attack that occurred this year so she'll demonstrated how to do a how to use dvb-t or digital video broadcasting terrestrial to it to essentially push commands to your TV and then tell your TV to go and pull a web page from his website that had exploits sitting on there waiting for you okay so and then once those exploits were pulled back
down to your TV's browser boom you have root on the box he had root on the box and then he could go and manipulate the firmware put backdoors into it and then he could also make it to where the the back doors would be persistent across firmware updates so you may be asking well how can I actually defend against this because it comes across dvb-t well you could actually monitor your network itself and you could see that your browser was communicating out and pulling down that webpage so there's other use cases out there I've seen something some good ones from black casts and good ones from chaos some good ones from Def Con I want to incorporate these in as well and
the G pack is a good example of this all right so let's actually get the hot now all right so this fire the next four slides mapped the TA eyes to each attack surface and each attack surface to the the lair of cyberspace can you guys see that I know it's yeah I should probably shouldn't done black huh all right so I've also went and broken down the cyberspace layers into sub layers for this particular sign this sub layer will be hardware and firmware so you have the device firmware device physical interfaces such as JTAG and you are and then you have device memory local data storage and sensors and of course I have supply chain on there I haven't built
any te eyes for it but if you really think about it you can attack you can use any of these attack services at the supply chain so it really is a go thank you sweet that's that's great now I can stay in the shadows okay so the next stop up the physical network layer is the application sub layer so here you have the Vice Network Services and from the device network services Oh ah spooled out the administrative interface and device web interface which is no surprise because a wasp is focused on web applications so of course they're gonna pull off the web applications and put them stamp on and it's also a big attack surface anyway so it makes sense
all right so you also have mobile applications however the mobile application isn't typically on the device itself it's on your phone and you're interacting with the IOT device within your local net I thought about taking this out but it's it's basically an extension of the IOT device it could be up in the cloud layer but not really so I just decided to go ahead and leave it here for now if anybody can give me feedback on where they think it should be I can change it all right and then the update mechanism so this isn't focused on updating your device is focused on vulnerabilities with the update update mechanism itself and the next layer is the communication
layer so I added in from the OWASP IOT project the device RF and wireless interfaces they had this underneath a different attack surface but I went ahead and brought it out as its own and if you really think about it this exists at both the hardware and the communications layer so you can attack the RF spectrum itself or you can attack the protocols that are riding across the RF spectrum all right and then you have network traffic which is essentially the same for ecosystem communication and ecosystem general you have the same type of tais across them I thought about collapsing ecosystem general and ecosystem communications together but I wasn't sure exactly why I brought these
two apart so I need to talk to somebody that knows a lot about ecosystem communications and figure out what the best way for them of doing that is ok so the cloud so the first to attack services here are focused on API so that's the data going back and forth between the device and somewhere some application up in the cloud itself or some service that's up in the cloud the last one is focused on the cloud web interfaces so whenever you're assessing the cloud web interfaces or anything that exists up in the cloud you have to be cognizant of the fact that this stuff doesn't actually it may not belong to you so if you're using another providers
cloud service that connects to your IOT device like Amazon for example you can't just go up there and just start scanning stuff and you know using hydro to test passwords you might get a phone call and - - to come to your house the possibilities are endless there but you know make sure that it's not a violation of your terms of used to be doing something like that okay and then the cyber persona layer so right now I have user awareness and psychosocial up here this is a research adventure for me to figure out exactly how I'm gonna work this one out so in the original hot framework we discussed the possibility of future devices having artificial
intelligence and basically having their own cyber persona and what that would look like but right now we're focused on the the user the users interaction with the IOT device itself in their projection into cyberspace okay so now we're gonna go over a hot tea I and these are the parts so we're gonna go over individually so part one it contains the vulnerability summaries made up of the mitre common weakness enumeration and wasp cut their testing framework alright so this particular T this part of the TA I maps back to build on recognize security principle practices from the DHS security principles here we have an overall risk assessment that's consists of the technical impacts business impacts
detectability prevalence and exploit ability this is also this risk assessment also comes from the attacks themselves and how prevalent these attacks are and then you can see this which principle down below this one maps back to alright and then the attack services group by layer a cyberspace this just Maps your does exactly that which Maps your own attack services back to the layer of cyberspace alright so I couldn't I wanted to just call this cyber threat intelligence but it's not quite that yet so I just put knowing intrusion to exploit a cases because an intrusion an attack are not the same thing know that but right now you can see Maria I always mess up how you say say
that properly but Ricker bought and some other ones you can see on this screen where there's a lot more just for this hot ta I that have utilized credential management vulnerabilities in order to gain their initial entry onto a device okay so the par-5 really acts like a checklist so it informs operator organization individual of which particular fic I see functions and then the sub sub functions underneath that that they will meet by actually going and doing part six which is the actual implementation of those functions and then part six is the analysis tools and training so this goes function by function and walks you down it's not super granular but it says like hey you
can test for telnet week pass for weak passwords with telnet he's in Hydra for example and on the left side of the screen this was a the password list that Maria used when it was first launched and some of the subsequent botnets they use the same password list so you can take this and you can pull out the usernames and then pull out the passwords and import those into Hydra and then you can test your devices at home or at work or whatever alright and then the last two parts are a link basically you click on this link and it'll take you to that cwe that was referenced in part 1 on the nist NVD or national national vulnerability
database pull up the vulnerabilities the actual sea bees that are out there for that vulnerability right now there's no IOT specific check box that you can check and pull up IOT specific CVEs however there was some talk there was some language and the iot improvement act that discusses them being able to do that and I might even I'm thinking about it sent an email in there and asking if they could if they would be interested in putting that into VD all right and then the last part is just a references so we don't want to plagiarize anybody else's work okay so just with that one ta I you have gone through all of these attack services at
the end okay so you've assessed that vulnerability across all these attack services and these layers of cyberspace right now I have respondent recover grayed out because I don't have respond and recover built into this particular ta I yet and really that's going to be inherited from your response and recovery plan anyways so for if you want to go do this at home just go go home test your password your your individual attack services out test the passwords and then combine that with a firmware update today and you've already decreased your risk significantly all right so you actually have to build an approach from the TA is not every organization or individual is gonna have the same resources and capabilities so
you're gonna actually have to go out and figure out what capabilities do I have what resources do I have available with me and then once you figure that out then you can pull out the TA eyes individually that you're gonna go in there and actually utilize so this is also going to be prioritized based upon risk what individual threats exist for your organization
so shortfalls in lane heads so there is definitely a lot of room for improvement there's a lot of things that I can do to improve it but really I need a community input that's that's the ultimate goal here is I need more folks to to come in and help me to build this thing better than what it is today so one of the other things that I want to do is a streamline the cyber threat intelligence and research integration this is a slow and tedious process right now there's no threat intelligence feed coming into this it's like these IOT attacks are occurring and then it just goes in and if that means moving off a good book and
putting it somewhere else building a database then that can occur - I'm willing to venture down that path and then the final part is building a better risk assessment process right now this is just based on what Wes says not really anything quantitative so I want to build that out better - so this is how you actually get involved and you can go in and provide feedback each section within the gate book has a little if you actually hover over the right side of it or pull up a plus sign you can basically type in a comment as long as you have a get book get book account and then it'll push that into the backend for me to see and then I can
take your comment and then integrate it into the framework so it's quick and easy for everybody if you want to get more involved in that then you can always send me an email and then I can meet up with you and we can talk about getting you account getting you hooked into it so you can actually develop it on your own so one last acronym for you guys so Patriots was something I came up with recently I thought this would be cute for the kids too especially so patriotic American American technologists reinforce an IOT security so I was talking somebody the other day and they were telling me about how they bought a home and it came with all the smart home
stuff built in I was like really and did you ask for that they're like no it just came with it I was like oh that's great I was like do not add security any of it and they're like no I don't even know how to update the firmware or anything so and it doesn't do it on its I was like that's great so basically what Patriots would be and what the goal of Patriots is to do is to actually go out and assist the home consumers they need help especially people that are disabled people they can't do anything themselves to elderly who aren't that familiar with technology but might buy a home that has this stuff built-in so we
want to create guides that help them to go and fix these things and then actually go out and give them a hand so website get book Twitter and email you can contact me on Twitter or email and then of course instead of having write down that long get book if you just go to home land of things that work there's a link on there it says get book and then you can go in and grab it from there and you can get hooked into this alright so I got to give out some things let's see so anybody remember what the first botnet I had up there was was that no no like the first one on the timeline so
like yeah you anybody else can add okay so I'm gonna give you the Alpha card with the expansion see come get it after we're done all right the next one is the USB rubber ducky so try to thank you something I got no such a fancy so I got one for you what was the first sub-layer of the physical network layer what was the first sub layer of the physical network layer within the hot framework yeah is it firm where it's hard wearing fur
sorry I'm having trouble thinking of questions what percentage of attacks are intrusions were password and credential management I should have known an easy one for me was gonna be easy one for y'all tree I know you can see the slides you can't see what's in my comments yes like this one okay what was the publication that describes cyberspace operations there's one that's not on there all right what was the army FM that discussed cyber and electronic warfare operations I may not have said that well I actually never mind what was that yeah I got one sorry I should have had questions ready for you guys before this there was something I heart on if this is for the book it's a blue team
handbook incident response edition there was something I heart on about a about cyberspace and something dealing with the devices something that they didn't have to be yeah she had her hand up saw all right that's all I got you guys got any questions sorry I was a little nervous and [Applause]





