Deep Learning for Predictive Alerting and Cyber-Attack Mitigation
Show original YouTube description
Show transcript [en]
thank you so firstly I would like to thank the organizators for this event and also the participants that uh you're staying a bit late today it's Friday afternoon so I will try to complete the presentation in time so you'll be then free for the socializing event so the topic that I'm going to present today is deep learning for predictive alerting and Cyber attack mitigation this is a research paper that uh I have uh prepared uh is this is not working I think or there I use this one okay this is a research paper that I've been prepared as a part of my U PhD studies at burner University of Technology so besides my PhD studies I'm also a a chief
information security officer at procredit bank Kosovo but at the same time working as cyber security researcher at sense NGO so uh without further Ado let's continue so initially I will start with an introduction to the topic to the paper that I'm going to present today then I'll go a bit through the related work that have been done in this field after that uh we'll focus a b a bit in this uh predictive alerting as a model that's being used to uh detect an anomal behaviors then part of this paper was also some experiments that we have conducted in order to test this um uh machine learning algorithm that we have included in the paper and as a final uh
we'll do some conclusions related to this paper so now as we all know we are living in the fourth Industrial Revolution where the problem is is not anymore to get connected to this virtual world world but the problem is how to secure our spa ourself in this cyber space so what are the challenges in this field so in general the main challenges in cyber security derive from the complexity of cyberace and uh this rapidly evolving uh techniques and tactics of uh cyber threat AC uh as we all know it's not not a matter if we are going to be attacked or hacked but it's a matter of when we are going to be hacked or attacked therefore um
the main objective is to minimize and control the damage caused by cyber attacks and incidents to provide uh like U uh U ideas is to provide an effective response and recovery and also to prevent future incidents from happening uh let's talk a bit in this case regarding cyber threat intelligence so what cyber threat intelligence the main idea is to proactively protect our system so uh it's not a matter just to deal with uh incidents when they happen but uh the idea is to uh fight with them to uh uh look for them before an event happens in the organization uh cyber threat intelligence in General Uses Data Mining and machine learning uh techniques which aim to transform the processed data from
large data sets from large sources that feeds that we get into knowledge into information so uh part of this is this predictive alerting as a uh method that's used to uh uh check for the historical date data and realtime data in order to make this connection and at the same time to predict the future threats and uh attacks that might uh occur to our organization so the main challenge here as you can see is to transform this huge amount of data that we collect from lots of sources into actionable in intelligence so it idea is to have the actional data not lots of sources of information then we get lost on it so this is the the main uh the
main focus of predictive alerting in cyber security so what's the motivation behind this research as I mentioned at the beginning I'm uh currently doing the PHD thesis which is threat intelligence and situational awareness and cyber security with the focus of cyber space in Kosovo therefore the idea was to test a new protocol uh a new uh in this case machine learning in algorithm in real case scenarios and to see how it uh Compares with other machine learning uh and data mining algorithm in this case uh we used the Deep residual neural network as a model and compared it with sequential rule mining intrusion detection Tre intelligence intrusion detection model and scale net these were the four models that we compared our uh
model that we use for this experiments the model that we use deep procedural network is used in the image processing and we wanted to see its performance in cyber security so in order to analyze and to evaluate its performance we needed to compare it with some uh actual uh uh machine learning algorithm that are used in uh cyber security in this p in this table I have put the four main papers that have been focused and the four main methods that have been used in the uh in this predictive alerting in cyber security the first one was sequential rule mining approach from author Martin hak uh in this paper uh and this this uh method had a very high s successful I
mean rate of detection but failed to train machine learning algorithm to auto aut atically detect the good rules the second method that was used to compare our model our method uh is intrusion detection tree uh which had it was like a very good in terms of computional U cost in terms of using the uh uh Power of processing but the has in general it has a lack of generalization approach the third me uh method that we U compared was intelligent intrusion detection model this method effectively reduced the computational complexity in this case but failed to consider filtering and wrapping method for better performance so it couldn't achieve a better performance and the last one was
deep domain generation algorithm by author vinaya Kumar he this approach provide very detailed information about the malwares but um it wasn't tested on Real Environment so these were the four methods that we compared our uh model so main contribution here is uh to predictive alerting is to provide as I mentioned at the beginning actionable and prediction of alerts based on this machine learning algorithm by processing uh different sources of uh information data sets Etc so what are proposal was and the experiments we conducted was deep procedural Network predictive alerting it was used as a plugins and these were integrated in the Sabu platform Sabu platform is a platform used in Czech Republic which is developed and maintained by an um
academic uh uh uh entity in the Czech Republic and it collects feeds from third party from Honeypot from intrusion detection system then it has a database called nerd uh which calculates the rep reputational uh I mean scores for Network entities is similar to Shodan and also it has this Menat where users can uh register to this platform and get the feeds according to their uh IP addresses and the indicators they want to receive and this uh I Abu is an Al analytical component that is um uh used by the administrator of this platform so what we did we used this um threat intelligence sharing platform and we integrated uh two machine learning algorithm that weren't tested before so
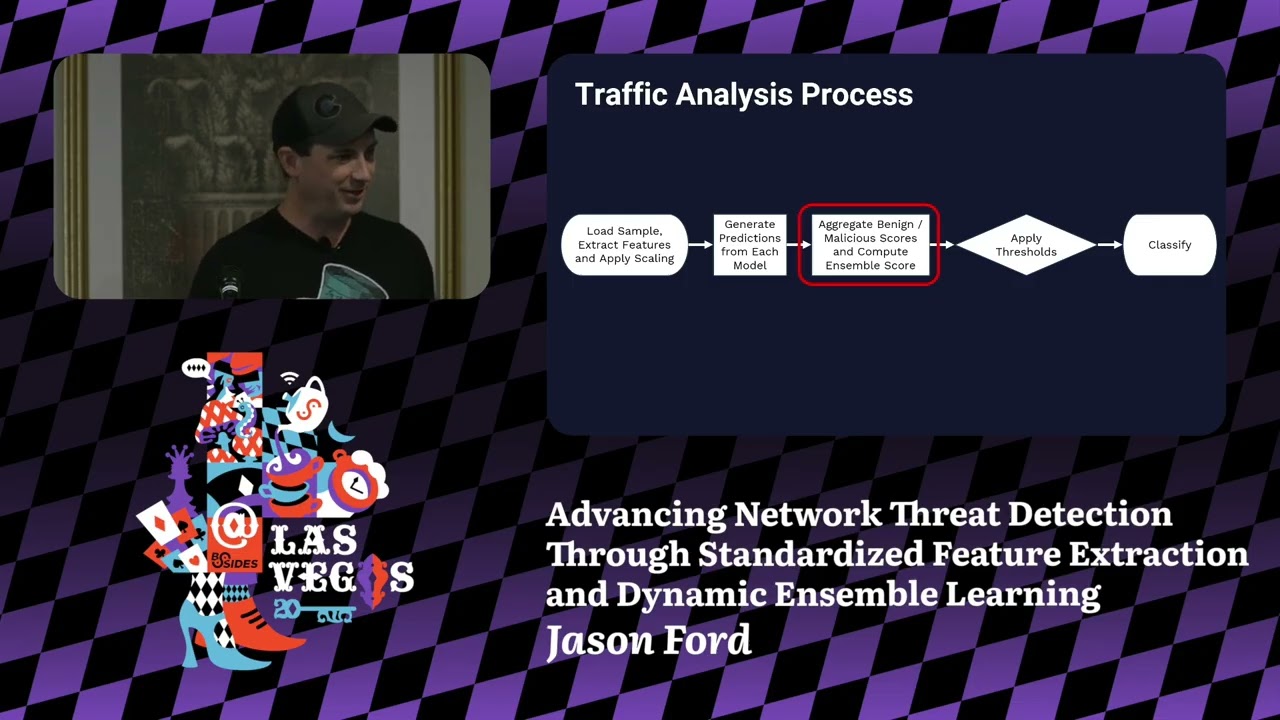
we integrated for alert segregation fit means clustering and also for alert prediction we integrated as plugin this uh uh model machine learning model called Deep residual Network which I mentioned is used in the IM Pro processing so it was the first time to test it in the cyber security how we did this so there are some stages in this U uh Sabu threat intelligence system platform firstly we get the input from that data set of this threat intelligence uh by normalizing first the first step is to normalize uh data set and in one identified unified I mean uh format the second uh stage was here to normalize them together with the inputs that we had from logs uh in the
situational awareness here we used fit clustering as an algorithm where we provided this as a plugin to the platform so we use this Sabo platform and we use this as a PL plugin with our um uh uh protocols uh I mean machine learning algorithm that we wanted to test third stage after we did clustering groups of U uh information we used feature selection in this case we used the hel finger distance uh to identify I mean the uh uh feature selection in this case third and fourth uh stage was threat intelligence AG engine here we included the machine learning model that we wanted to test and at the beginning at the end we did blacklisting by uh blacklisting the
suspicious IP addresses based on this all process so I just explained this uh theoretically how we did the experiments uh during this uh research paper so how we did the experiments we use the Python programming language database from uh this is the Sabu platform specifically The Ward and server uh where these information are collected currently it has 34 gabit of uh information there are 10 million uh events there are 25 senders and 33 receivers uh during our test we used nearly 12 million alerts generated by 34 intrusion detection systems honeypots and other data sources that we can see here in this uh design so these were the information that we used to to make this uh uh test of this
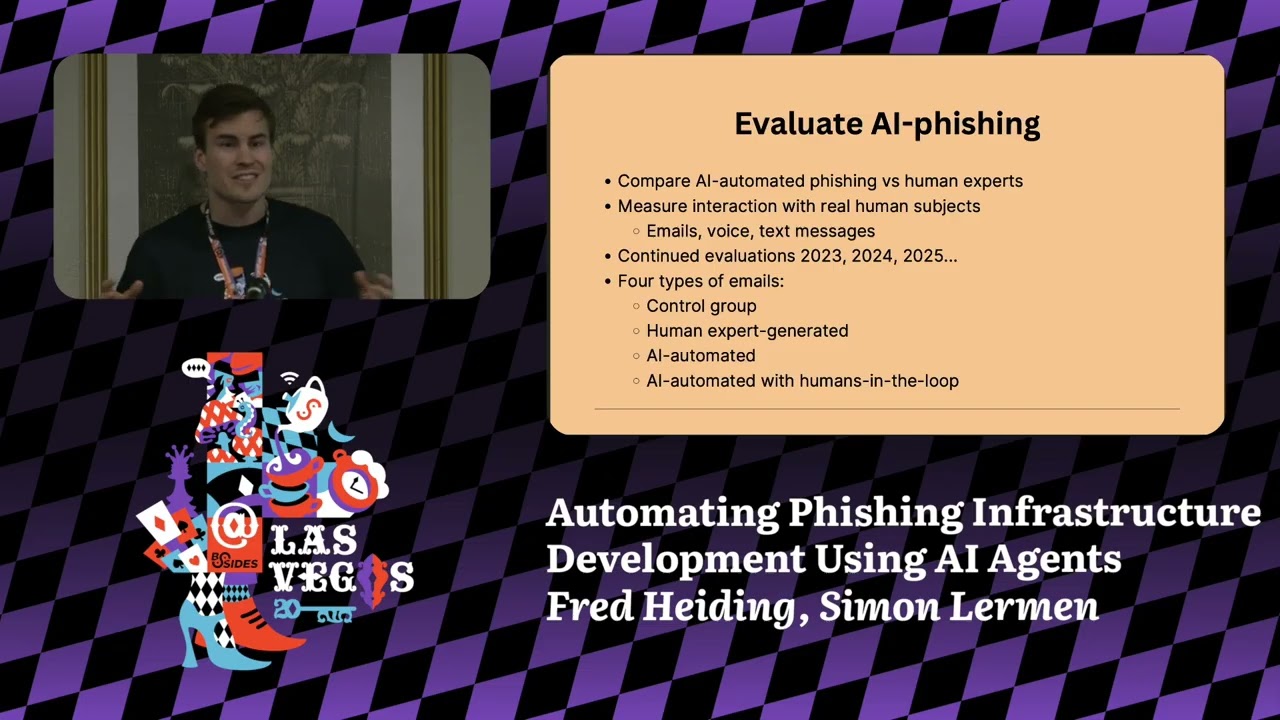
uh machine learning uh algorithm here you can see the results uh there have been several tests several iterations uh firstly with 60% of trained data then with 70% of trained data 80% of train data until 90% of trained data to to analyze the performance of this de preural Network predictive alerting uh by using this uh four uh three main performance metric which is precision uh recall and F measures as you can see here are uh explained the U uh what does these um uh measures mean Precision we have false positive true positive then we have relevant event Precision means that total number of f uh true positive divided by the entire true and false positive then recall we have a number of
true positive divided by relevant events number of re all relevant events the results here are with each iteration firstly with 10 iteration we tested all the metrics all the performance metrics with 15 with 20 and 25 iteration so this test was conducted only for deep residual Network algorithm what we did next we wanted to see how this uh machine learning algorithm Compares with other relevant uh machine learning algorithm that I mentioned in the uh beginning of presentation so what we did we tested also all of them we integrated them as plugins to the Sabu platform and we tested with 60% with 70% 80% and 90% of trained data and as you can see in the
result the Deep residual Network machine learning algorithm outperformed the other uh algorithm in terms of precision recall and F measure as you can see the first is uh around the with sequential rule mining there is around 15% better performance 80 with 95 uh with intrusion detection Tre is around 14% better with second uh machine learning algorithm that is with the intelligent intrusion detection model is 10% better performance and in scale net that was the best performed out of these four it's around the 8% better performance this is only for precision as you can see for recall the same and for f measure the same so this protocol uh provided better this uh machine learning algorithm provided better
results than the others in in detecting and predicting cyber attacks so as conclusion uh the use of machine learning in threat intelligence analyzis as you can see can improve the effic efficiency accuracy and effectiveness of threat detection response which in today's F devolving threat landscape is very critical as you all know the proposed model that we used uh enhances the performance of generalization and also it used less processing time when we used this relu function activation function which was better than tangent and sigmoid function some mathematical function that are used to test the performance uh the idea as the alert segregation fit means that we used also Pro provided very effective in clustering in the groups the threats and
as a future work of course we can improve this uh protocol by uh testing it with a higher data set and also in live live environment so this was in general I tried to be a quicker than I planned uh because it's uh Friday afternoon there's socializing event so I didn't want to uh stress you more if you have questions you can address them directly or you can uh contact me through through the um email address thank you not does anybody have any question okay you're going to make me walk up there that's fine no
problem there you go uh so just out of curiosity I I'm not going to name company names I don't want to go that route but so when I'm doing uh detection bypassing and such so you let's suppose that you have a some type of threat detection mechanism that uses AI the ones that I see often used uh have a long spin up time so they learn a company or even a person's Behavior they learn what's uh normal and then then they can detect what's abnormal the down the downside to this of course is that at the very beginning everything is abnormal right the the the LM or whatever you're using has to be trained up um so I guess my question is is this
something that can be uh user friendly so if you are if you're trying to train up an AI to detect um any type of malicious behavior are you basically looking for anomalies or anomalous Behavior or are you looking more for um machine code or or other things how how are you detecting it and do you see this impacting uh the usability of somebody's day-to-day operations but well in general uh these methods goes in combined with other techniques because of course there are lots of uh false positive rates in this case and that's the the main challenge in this field so it tries to get the best results but of course in this case you have lots of false positives which
then you need to combine with other techniques in order to uh have the a more accurate uh results in the predictive alerting is your research uh available online or yes Aran it's in itle e explorer it's published it was part of uh ccvc itle e conference I presented there and it's available in u i e explore great thanks so much any other question yeah is this project some implemented somewhere you mention in Czech Republic yes uh in fact uh similar idea I am uh trying to implement in Kosovo in National cyber security unit which is called CER so the idea started from here when I started to do I mean to when I initiated the stting studies in cyber
security I saw such kind of project then I saw it as a possible to be able to be integrated in the Kosovo So currently with some of uh teams uh from Research Center we are trying to implement similar solution in Kosovo and at this at the same time to to implement to integrate that algorithm in order to achieve better results Great any other question aror thanks so much that was very informative thank you very much