Save The Chicken, Save The World - Andy Barratt
Show transcript [en]
all right I'm Andy Barett thanks to those who actually stay we M to this which is a shame um I'll do a quick intro who I am I've removed my corporate bro jacket so I'll I'll try and keep this a little bit more friends and family this is my corporate bio I have R our financial services business at hire about 90 split between the US and the UK uh we're one of the largest insurance providers um I say our job is to help really large corporates keep the promises that they make to everybody we do that with compliance programs all certification we to imagine um I'm somewhat affiliated with none of these people I do quite a lot of public
speaking um I'm going to ditch the corpor and dother who am I really so this is my Shameless acquisition in our Manchester office which St going to come try early soon I'm a bit of a copy not um shamess traveler bit of a nerdy gamer so surprises for anyone who the games afterwards Our Father were two great kids and um my team seemed to love taking the Mickey out me so the last time I was over in La I one of my team gave me a Andy as Princess rainbow sparkle which became a gift for my daughter and she thought it's a um so I'm I'm a bit of a solar nerd as well I'm desperately trying to stay in shape
which is hard when you traveling all over the world all the time but today I have the opportunity to tell a true story um and the reason this is uh really kind of bizarre is because of the article that you can scan here and I suggest you do um so I'm not going to mention the names because I know we're we're going to record this but this is a true story this is a case that I worked on personally during the pandemic I'm going to interweave another case that I'm not allowed to talk about because it isn't in the public um which covers some of the fin7 attribution um that Sarah beautifully team for um so
I'm going to do a little show of hands first I want to kind of get an idea how many people in the audience already work or would claim to work in information security cyber security RS all right fairly good that helps a lot all right so terminology 101 um all these terms are very specific to payment security for so PFI is both a designation and a type of investigation so I am a PFI that means I'm a payment foric investigator authorized by the credit card schemes certified by the PCI ccil big compliance body if you do anything with credit card you going through one of a this at some point p is not what you're thinking it's
a point of sale acquiring Bank those are the banks who take the credit card payments through the car brand so people like Visa Mastercard JCB D Etc and then the issue in bank is the people who give you your credit card and usually lines of credit so they usually manage all the lines of credit and they'll make sure that you get a card that you can use Merchants people going to spend money with CPP is the really interesting one so the CPP is what to call common point of purchase this is really important because this is how almost all credit card fraud detection gets done and it's really clever because what happens is it it works out based on where we as card
holders report fraud to our banks where we all spent money recently so imagine and in few we've been out shopping we've been a little bit crazy and we notice a few strange transactions on our statement we call our bank and go honestly I didn't spend $4,500 on a Vision Pro push up it wasn't me then they say okay we'll take off and what happens is all those like complaints get aggregated and when it becomes apparent that there is a common point of purchase a fraud alert is led by one of the big payment brands in conjunction with the issuing Banks and then they kick off what's called payment forensic investigation so this is the story of a
payment for forensic investigation that started in 2020 as the world was locking down so those of you G friends know it's a very laborious task lots of handson systems pulling drives Imaging um it appear the world was locking down everywhere except here so anyone know where this is thank you Texas um we had two substantial PFI cases that ran through Texas right in the middle of the pandemic um pandemic doesn't apply in Texas as you'll know if you speak Texans during the pandemic um and so we had our traditional forensic Friday so anyone who works in forensics knows it's the law you only get the request to come and do forensics in I on a Friday and it
goes a bit like this this is the sales person who gets the car this is the DFI person oh my God Frid it do investigation and so that was me as much as I'd like to be Ghostbuster I think i' probably grown out with that costume now um this is the reality of our world so PFI can be triggered at almost any it's commercials so goes out to a group of people all accredited to do this work uh and then we basically bid on the investigation work and so we bid on this piece of work and the salesperson said to me it's a small Cas small I promise you small is a relative term in Texas um so this Cas is a nare
from what started as a small Cas um from one franchise of a very popular um fried chicken restaurant we ended up taking on between two and 300 impacted franchises and having to do forensic investigations across the moment um the terminology we used to describe these I probably can't share in public because it's just terrible use of English but also filled with terrible exclusives we have so many different types of Point of Sales software so many different vendors in the loop so many different it companies in the loop we literally were like trying to work out the permutations just so we could report them let alone start the friend investigation so we had an awful lot of challenges in this case not
least of which was all these franchises had different ownership structures and we were trying to figure out how to manage a forensic investigation across the law with what appeared to be a fairly fairly sophisticated adversary I say sophisticated but I think when I get to the next slide so you can't see any of the phrases I suspect but detection was a nightmare so we had loads of people who were either owner operators we had some that were professionally run organiz ation we had some people who didn't know what a firewall was and proved it to us at the Times um we had a lot of people who were just totally clueless and didn't believe it was a
thing like it was kind of like the antia of forensics again fairly common in Texas so the Big Challenge we had was one we had to prove to people that they had been compromised we had tons of evidence to prove it from the banks we had all of this common point of purchase data saying like all of these franchises appear to be compromised and still a lot of people saying like we don't want to do this it's it's expensive I don't have to shut my business for a period of time detecting the issue is a real real nightmare and we had to run this case during the middle of a pandemic under travel restrictions um I was a lead
investigator and I wasn't in Texas and so we managed to scale a case and one of the things I wanted to share with this group today is some of the things we did during what was a fairly complicated case to make it work and to be successful within some reasonable bounds um so we had some scaling challenges which we address we adopted some very new technology for both forensics and data acquisition very early in this process otherwise we would have never been able to do it we actually at one point had people out on the road all over North America because it wasn't actually just isolated to to Texas fortunately um and we had people doing
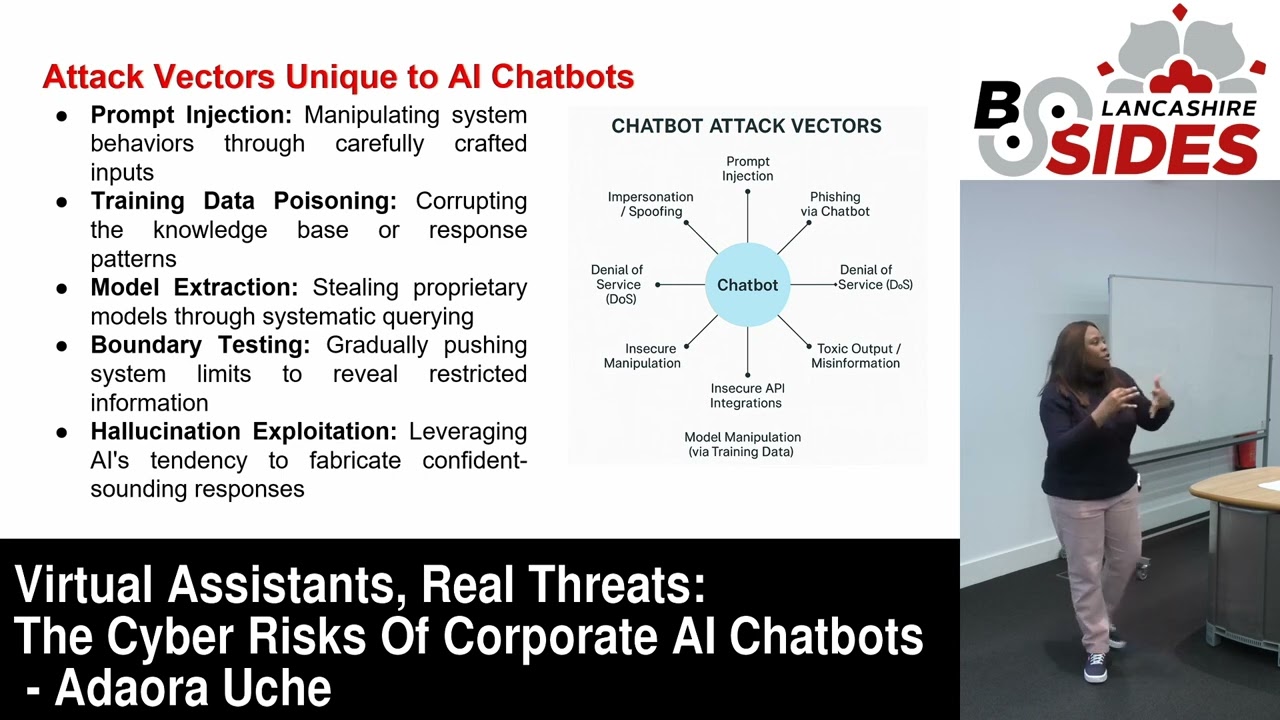
we we call them the tender forensic guys because everywhere they would go the franchise owner once they' imaged the back office machine um would offer him a big portion of chicken tenders they were very proud of that but it taking these problems with a nightmare and this is our next kind of challenge so we have capture we want to use Transit first thing we've got to do capture all our evidence and our lap is in South den Colorado so we had to get evidence to Colorado so that we could get investigate right this in itself doesn't sound like too hard of a job when you're doing one or two restaurants when you do 300 and nobody can tell you
where they all are nobody can give you actual addresses all locations this is a nightmare there's also a real scaling problem um so I had a whole bunch of of really strange conversations um the process with PFI is immensely stakeholder driven so every week typically into an investigation you have to brief all stakeholders and I imagine there's two to 300 franchisees potentially in this kind of case all of which accept payments using different banks I would have to go on conference calls where we did roll call through almost every Bank you can imagine in the world who'd send an attendee who is material to the investigation and so that would take about 20 minutes just to
get through the like hi is that Chase Manhattan yes is that J we got everybody now we can talk about the three things we figured out during this case what was happening was we couldn't keep up with the volume that we had and so we had to Pivot really really quickly but we were under tons and tons of pressure there's an awful lot of fraud being committed and again it was just a function of scale like we have lots and lots of restaurants so we believe have been targeted by um a group that was modeled around the fin 7 um ttps so we had a reasonable idea of the tactics they were using they were only in only interested
in payment card data specifically in North America track data that track data can be used to clone cards and then used to be spent in other countries and quickly cashed out so uh for those of you who were working out which things you were guilty of in the last session the these guys were definitely guilty of following the money so our challenge is getting all this data to our like analysis of in Colorado and trying to figure out how we can get through everything find evidence compromise our job was really to try and get the root cause established and then get all of these franchises to contain and the containment was a nightmare I'll talk
about that in a second so we had to scale and we had to scale really really fast and we adopted some really interesting technology that Amazon just released at the time for data center migrations um I think it was called snow drop and essentially it's like a mobile Naz and the best way I describe this is you put your Naz whatever you want to do copy all the data onto it and then you put it in a mailbox and it ends up in your S3 bucket how it does that I have no idea but it worked and we would get notifications and we could suddenly scale in parallel and so I could send forensic investigators out all over
North America with a snow Drop device a bunch of hard drives and right blockers and we could image entire like networks of uh food food restaurants for one of a better expression um and quickly get them to our lab and we would then have time tracking we could manage expectations with all these crazy stakeholders I could tell them like we will have the next phase of analysis kicking off in the next couple of days because we would have tracking information from Amazon we would know how much had been consumed in our current storage system and we were ready to kind of get containment discussion started with all these franchises that didn't know what firewalls were couldn't
tell us who their it people were in some cases like it was a friends and family in other cases fun one was we met a franchisee who'd been given their franchise by an oil millionaire as a thank you for doing their taxes honestly i' I thought I've seen everything and then that one cropped up I definitely haven't so getting to containment was just super challenging the first thing we have to report back to the big payment Brands is the crime has stopped that's the simple way to think of it like containment can mean different things when you're doing an investigation their view is has the bad guys stopped getting data out and is fraud likely to be stopping soon the
challenge with that is that once all that data has been consumed There is almost endless card fraud taking place until the issuers know all of the cards that have been stolen the challenge is we had so little data like we we we had no corporate infrastructure so if imagine you're doing incident response in a traditional corporate environment you'll probably have tool in you'll have detection Technologies you can do remote acquisition you might be able to use things that you can scale quickly because you own the network we're a third party going into 300 different networks set 300 different ways by people some cases who don't even understand basic IP address em um let alone how to use things like a firewall
for good um so containing them like we literally had containment plans that started with install fire like stop bad stuff there were think there were like AT&T connections that were just plugged straight in to a point of sales system that we could have that we could have logged on with a remote desktop session over the Internet it was really scary so containment was hard we eventually got to a point where we felt we could contain the people who were willing to do the containment actions because this case was so big we had to kind of keep the progress moving um because the fraud that was taking place was immense and then the thing that nobody ever talks to
about so when all of this is going on the people who are being defrauded are racking up a bill that they're not aware of so those cards that have been compromised have to be reissued to us so as card holders um there is a reissuance cost and in a previous previous piece of work I did I was actually a an expert witness to MasterCard and I actually got to see the price breaks involved in a large a large data company compromise and it's the most heinous pricing schedule you can imagine it's like your first 100,000 credit cards will replace a $10 a card because you had two million stolen they're now $6 a card and it's
like this the most awful set of price breaks that you can ever imagine when you're in the millions this kind of scales just beyond most people's comparison and then the next challenge is you're also on the hook for the fraud so we had to get this done and we had to get it done really quickly and we had a lot of people who didn't want to cooperate and so this is what they called a me in swn like I have Visa Mastercard all these big cars going like are we done yet are we done yet are we done yet I'm like H I need a simple explanation so I genuinely used the twinky moment from Ghostbusters where I
had to sit down I had about 50 or 60 Global Banks representation from every car brand and I said we have two petabytes of data roughly from 300 franchises with about 8 to 10 lanes per restaurant each of them's got a crappy 3 to 500 G SATA drive these things take time the literal time it takes to get from dis to lab is X and they went oh that's a really good explanation nobody's ever told us that before which my mind blew a little bit um and so they went okay just give us an update and they started to use our terminology so they say oh is it in processing now which was the language we would use to
say it's hit the we' say it's been processed we have a big tool that indexes all the data and we can do analysis with reasonably quickly and when they started to do that we knew we'd won so we were getting further and further into this case and there was just so much malware like one of the one of the team who I won't name basically coined the phrase it's like we fried them in malware it's that bad we had we had several locations where we couldn't ascertain the original point of compromise it was even potentially compromised on installation with multiple different threat actors and at one point we saw so many different tools we like
this looks like it's a pentest rig so it was that bad I mean so some examples so we had malware masquerading as the point of sale so literally it would just look like it was the point of sale software and they would launch it and then what it would do is spin up the an image that looks like the the counter so people would smack the screen on the point of sale nothing would happen they'd run the card and then it would just steal all the track information we saw tons of stock offensive Tech so I mean this was like Cali 101 you see things like MIM cats everywhere there's password dumping tools just Shameless absolutely
Shameless there was no attempt to hide it we found like folders it was like day one day two they're just dumping out big text files of track data it was awful rogel files that's quite a funny one and that was actually one of the ttps we realized was aligned with I think fin 7 at the time no firewalls I'm literally not joking this is therapy for me now and so many places didn't have a firewall it's almost embarrassing but the evidence of multiple intrusions was the thing that was really scary it was almost like there was multiple groups just tying with it because they could like there was so much access to these systems it was it was painful so what
did we do we ended up having a review all this stuff and then the funny funniest thing I think happened was when one of the team called me and said Andy I think I made a mistake and how do we make a mistake we've systemized everything we do now and he said I've got a burgeri point of sale I'm like you went to the chicken place though right like the color schemes are different and it turns out that this franchise just bought a burger 5. sale plugged it in and installed their card reader and so they had a burger five point of sale in a fried chicken restaurant our confusion was insane so we did have some cool
moments though so I wanted to share this because again I didn't go to Texas while we run this case I'm unfortunately I had some great staff on my team who were able to support the investigation but I was the throat to choke I ended up doing all the communications and I remember one night there was about :00 in the morning I had this briefing with the Secret Service in the FBI um and this is really really cool because we get to speak to the Secret Service occasionally they the owners of credit essentially the US dollar and so that's not unusual and if you ever get to see their presentations they're field agents all over the world
they're really good people generally um I had this really fun moment where my kids are in bed I'm speaking probably quite loudly on the phone and my son comes into my office he wers it and on the phone to the Secret Service in the FBI I just look at my son and he looks at me he's like why that and he says what do pH of the FBI and he goes FBI FBI FBI so that was a that was a win like we don't get to choose what's cool but your kids do so the other thing that was really important was I had to think globally by default and I think the takeaway I've seen a lot in the UK
there's a lot of like weird sentiment in the UK UK economy if you depend on News Channel you watch I think there's also a lot of strange stuff you hear people talking about boot camps there's experience there's all this stuff like I would say forget about all that we operate in an industry that has to act and execute globally and the UK is a very prominent position in the world um we can engage well with the us we provide really good time zone differences we're English speaking typically we also have access to other parts of the world where we have different diplomatic relations than the US does and so we have this unusual position where we can actually just act
as a global um a global support mechanism in some cases and so I always encourage people if you're thinking about a career in cyber don't just think about UK think about everything think about the whole world because there's a ton of opportunity if you just don't think about the one thing it's right in front of you so that kind of my tldr I know over got a couple minutes um I can take questions on this case if anybody's interested um you can also connect with me on LinkedIn I can go through some of the specifics um one of the crazy pieces that happen was having to be interviewed by Brian Krebs on behalf of the owners of their
their Fried Chicken plates um the owner had no idea and his lawyer basically pulled me onto the call and said they can do three things frying chips frying fish frying chicken and running a franchise like we have nothing else that we do that was literally this guy's expertise he inherited this whole business I remember being on the call with Brian I've spoken to Brian KBS a couple of times he's a really nice guy but he gets to the point really quickly and so what we managed to do was give him enough of the story that we could plate his desire to write a case and then I actually gave him a whole bunch of intelligence from some other cases we
were working on just to take the heat off our current uh investigation because an intelligence firm was continually leaking this into the the media and at one point we were like we're not sure now who has the most current set of information is that the people leaking the Intel or as it all work in the case um but if you're interested I'm happy to talk about it happy to talk through some of the details um if you're interested in working forensics in and response cyber security come and talk to me if you want to work in compliance GC again happy to talk I uh I meant quite a few people through both capslock and ua92 in
Manchester and so if you need some support sh I'll give you ACC to St aome