Best Practices Crosswalks
Show original YouTube description
Show transcript [en]
all right and for our final Talk of the day we've got Jared Winn presenting best practices crosswalks
hi everyone big crowd tonight so what I'm going to talk about is best practices we all should know them if you don't know them you're going to find out about them you may already know and probably have been doing these for 20 plus years and the crosswalk is really how I'm going to talk about meshing between Frameworks uh I in my professional life let me just move this here I've worked in the military I've worked for a city in Virginia and now I work for a private Equity Firm so what I do is I take about 150 of the companies that we own across the globe and I take them from a mom-and-pop shop and I turn them into part of a much
larger holding company which ends up getting sold for billions of dollars so there could be 15 to 20 companies that could be 100 companies so right now my company has about 250 of these softwares and service companies uh and my role at that company is to help bring their infrastructure and their security together so a lot of what I do is I take their compliance from where it is Bare Bones and I try to bring them up to a point where they can say that they're certified they can gain compliance they can get themselves some cyber security Insurance because otherwise they may not be able to what I'm going to talk about here as far
as best practices has already been said about 15 times today so I'm not going to rehash too much I'll Blaze over a lot of those things inventory is key always has been key if you don't know what you have you can't fix it you can't protect it the account security passwords and multi-factor email security policies I'm not going to read the rest you can basically everything that every framework puts out in its long-form format I try to take and I try to put it into a very simplified best practices parallel approach parallel meaning do one thing and have it apply five different places at the beginning of a lot of the the companies that we have we're not quite
sure we may know their Market or their industry but we don't know where they're going we don't know if we're going to be going down a sock 2 road if we're going to be talking PCI PCI DSS or if we're going to put that to a third party so I like to check all boxes that I can from day one and I only like to check them once so if I've already done some work I try very hard not to redo that in six to 12 months and after I've turned over my responsibilities to a CTO or a CIO of these companies I really don't like for them have to question what I've done and or do it again themselves
so what I have done is I've taken the nist 853 the nissiusf which is based on the 853 as well the CIS controls which is not a framework per se but recommendations and ISO 27001 and the dates that you see next to them these are actually the dates that they were last updated so if you're not in a position to have gone through all these read through them tried to apply them you'll very quickly realize that we are behind the times realize that this is government and in most cases this takes two to five years just to get published put out there go through a comment period and actually get finalized so the expectation that these will be regularly
updated is unrealistic so what we try to do is we try to again check that one box MFA can be checked in all of these Frameworks and all of these security controls so if it's checked once let's account for it every place because in 12 to 24 months we may be looking at a certification that requests specifically for it rather than going back and checking reevaluating and redocumenting the processes you can refer back to the original the cost and this is a very large estimate but this is based on the four of those combined the cost annually for any of these could range depending on the size of the organization from five thousand to a hundred thousand
uh and realistically like I said these are designed to be future proof based on what is true right now TLS 1.0 1.1 was true when it was put into effect okay no longer true but still in effect
so 853 uh if you've ever read through it I don't remember the page count but it's excessive uh you have to check boxes thousands of times and many of these boxes are very much the same in nature so if you have a project or if there is an anticipation of a replacement of an email system and I'll talk about this in a second an email system by itself accounts in large part for let's say office 365. for an identity system an email system a data access system there's multi-factor there's a lot of things that we can check the box on with that one fell project the one Fell Swoop and so what I try to do is isolate these
into much smaller groups and task drive them on individual projects to say in the next three months we're going to accomplish these five things they'll cross walk across different Frameworks but ultimately instead of trying to sell MFA which no one wants I can sell an email migration or I can sell an upgrade and security and I sell it and then I bundle in just like the government does I put a bunch of little riders in there and those Riders just happen to check a lot more boxes than what they originally anticipated ISO 27001 is also a beast if you do an international business that's your option uh if you're working on government that's where 853 will likely
come in in most places if you're utilizing HIPAA or if you're doing Government Contracting you'll want to stick with 853 anytime you go outside you can crosswalk and come back but to be realistic you should follow the guide that they're actually going to be putting up for you cyber CSF uh I love cyber CSF but I can't really see these ones sorry about that this is the framework itself it is very basic very Bare Bones this will not check a lot of the boxes on 853 but you're at least starting the process uh niss CSF is being revamped so on the original slide I think it said 2016 2018 but now it's coming back up so it'll be a new one
hopefully coming out quarter three of this year uh to try to keep up with other things that have come up in the industry Cas top 18 again this is not a regulation this is not a federal this is a recommendation by an industry uh you'll notice that if you look at the terms here everything in white is a control these controls can be individually addressed with a specific tool or you could do what I like to do and I like to parallel enforce which is running one project that targets multiple aspects multiple controls so I showed you earlier the regulations sorry the Frameworks themselves and the dates that they were last updated there's a little bit of nuance here some
people will argue on the dates that these were last updated because there have been some add-ons but if you consider how important HIPAA is on our daily basis if you're in healthcare and it was last updated in 2013. now it was designed to be future proof it does reference things like nist so it reference their standards but those themselves haven't been updated since 2018. so it's important to stay ahead and just because these all don't necessarily apply to your organization we can take very specific items that they have with exception of Canada I don't think most of us will need that but you know the Privacy Act the high tech again if you're working International you want to
go with uh gdpr But realize that now I think there's I think there's nine states it may be eight that have an individual privacy policy is it a eight eight or nine there you go they have their own policies that are more similar to gdpr than our own Federal policies so if you've ever been involved in a data breach one of the first questions that Council will usually ask or the incident response company is uh where are the impacted users or customers because they want to know exactly what their reporting requirement is for the specific incident that you're having now aside from regulations and aside from the Frameworks that we're talking about the controls that we're using to
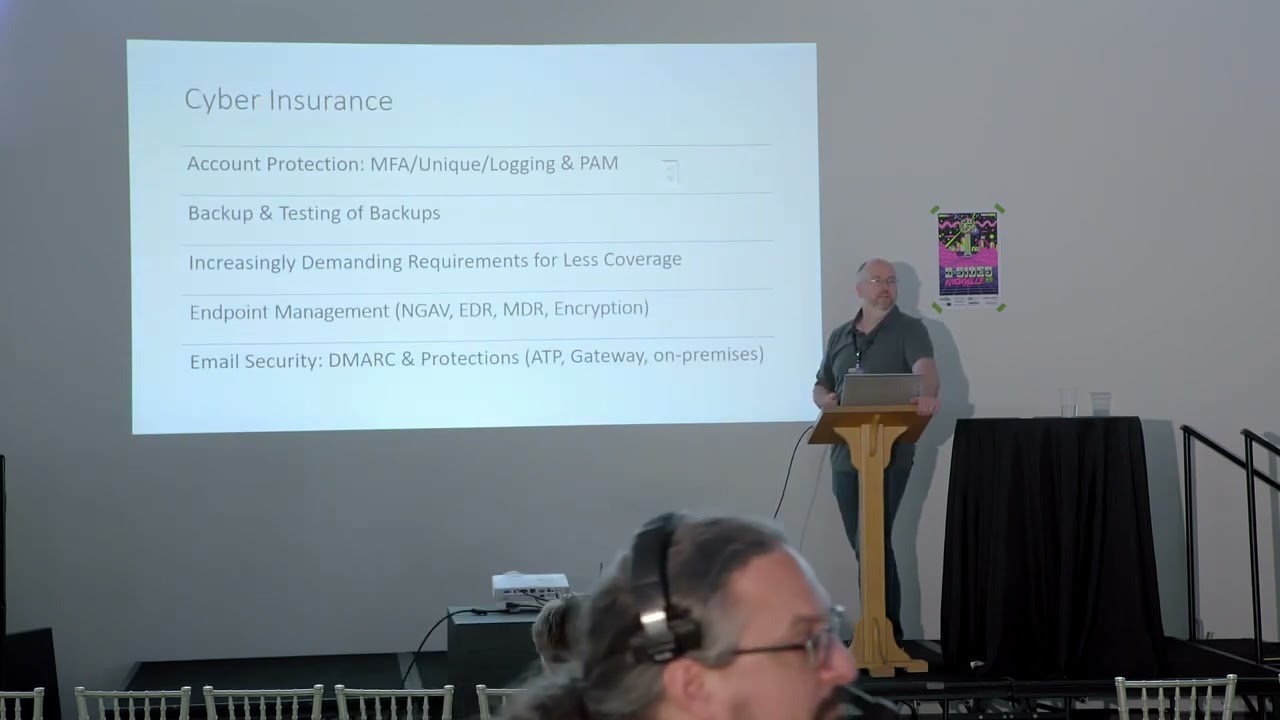
fit in place cyber security insurance has become this elephant in the room that everyone has to have no one wants to talk about people seem to forget that it's a used once and then throw away kind of plan because you're never going to get it again uh maybe three four years ago when they were giving it out and just taking premium dollars but as soon as they had to start paying they realized very quickly that it was not going to be worth the effort to insure so it's become extremely demanding as far as what's required if you're following a framework if you're following or you can state that you're in line you're not compliant until you've been audited but if you're
in line with let's say HIPAA or something along those lines and an insurance carrier comes to you and suggests a premium I would argue that you should hand back what your security program looks like to them and say what's my premium Now if you've never documented anything and you've never done anything to secure your infrastructure to document your infrastructure and to show the proof the people practice and proof is what auditing is all about when you can show that to them and you can show them that you've done more than just buy cyber security tools then you're able to actually in from what I've heard I've never done this personally you've been able to get them
to renegotiate those annual rates or provide you coverage where they wouldn't have otherwise uh thankfully I haven't had to run into that yet uh knockout wood again uh cyber security insurance and they're asking all types of questions if you don't have the the great experience of having to read through all of these and answer them for 150 companies that are all over the world uh you're welcome I do it for you for the companies that I have at least my experiences is that everything that I do on a daily basis with these companies and all the new companies that we acquire is a result of what I've had to read what I've had to comply people to
whether it's a framework or a regulation whether or not there has been a specific question on a cyber security questionnaire knowing that we need the insurance and knowing that those Insurance questions are based on best practices in the industries but also on whatever the Frameworks are let's say it's Healthcare well there may be a different questionnaire for health care they're very generic at this point I don't expect that they would be very generic in the next 12 to 24 months because what we're seeing is very highly targeted attacks against specific Industries the payouts on those Industries are huge because the customer accounts or the record counts are so excessive in Healthcare systems are Healthcare Providers if they're not able to gain
Insurance they're going to end up self-insuring and unfortunately for everybody who has a human body that's going to reflect itself back in healthcare because they're not going to pay for it we will um so all of these things feed directly back into those Frameworks and all of these things should be done and I heard it said several times today you know MFA should be everywhere I guarantee it's not there's always an exception exceptions are business risk it's the business's job to make the decisions about those not ours as Security Professionals right which is great too because if and when something happens and there's a documented exception signed for by the business it's not our fault we're not going to
get in trouble we will have to fix it but uh it's not necessarily our direct fault so consequences of let's say any type of cyber incident whether it's a data breach whether it's ransomware whether it's someone physically accesses and steals a laptop something along those lines something that a lot of people don't necessarily consider and it's very difficult to put a specific dollar value to us the reputational loss right that is revenue loss it's also whatever the profits for that year lost because there's PR there's SEO losses remarketing if you happen to pay a ransom uh then obviously that's a sunk cost it's unlikely from what I'm seeing that most of the insurance carriers will pay your
full Ransom if you choose to pay it if at all it depends very much on your policy regulatory fines uh I'm trying to remember off the top of my head I think it was 12 500 was the average HIPAA cost for an individual violation that's an individual person violation so is there something to someone else have another number no okay we'll go with that then so that dollar amount times the number of Records in your system that were impacted maybe your large hospital system can take that but no little doctor's office will so those are the same fines regardless of who is the holder of the information and as service providers as SAS companies if we're providing a business
associate agreement type service with a health care provider and we are the cost of the breach we are going to be subject to well they get the fines we get the lawsuit so legal issues the actual remediation cost we said before completely uninsurable after any event uh there was a mention earlier I think in one of the talks about uh do you do you contact your insurance company as soon as something happens and the knee jerk is like oh don't do it well I have a policy that requires a 24-hour reporting period from the moment you find out about the actual breach the problem is the companies in the UK and it's a U.S provider
so what's the time difference eight hours nine hours so we just lost that so it doesn't matter where you are in the world you're going to end up having problems we own the holding company they are a subsidiary they get targeted under that policy we end up having this much shorter time window all right so crosswalk or a mapping uh if you're not already aware of what this is I mentioned before try to check all the boxes at once if you can do that in such a way that you're documenting things I like CIS I like CIS because of how simple it is for non-technical people to actually check boxes I can give a spreadsheet to someone who's a
CEO maybe a Founder who has never done anything insurance or compliance related in his entire career and he can fill out 70 of this thing for me so when I say crosswalk I'm referring to and CIS is really good for crosswalks they have the tools that are out there for free to be able to say if I satisfy section A of let's say a specific regulatory requirement well that crosswalking will satisfy section B of A different framework don't do the work twice I hate doing work twice so when you do work once and it's in a location where you can easily crosswalk it you're able to check that box twice so I checked three or four boxes for each
effort that's made and I do that so that they have the means in future to be able to state or provide to an auditor that they have met the standards or the requirements so CIS does a couple other things as well if you want to pay they have hardened images so you can get the hardened vdk images for your VMS you can spin them up and they're already pre-hardened if you're if you've ever worked in DOD or have a reference to DOD The Stig is a very similar tool Sig is going to be basically a baseline how you should have done it not how you did it but there is a tool where you can
actually compare the two and then simply report on it so there's a viewer for that the policy templates the control mappings and the control framework the control items that I showed before where everything in white was a specific item that should be individually addressed they all have between five and ten sections but all of this is provided free of charge with exception of the hardened images and they do have some tools that they do charge for uh again crosswalk we talked we just talked in the last talk right about how spreadsheets are never going away well this is the spreadsheet that I pass along to people this tells me exactly what the standard is in CIS uh it gives me a this is why
it's easy for people who are non-technical to be able to understand and fill this in because it actually lets you read some of it is a little bit of mumbo-jumbo but for the most part I do find that people are able to read through this and at least have a question at the end of it if not a definitive answer so this is PCI specifically so this is a crosswalk from CIS to PCI now with PCI there's an unmapped section at the bottom and I'll talk about that in a second it's not that one CIS Spreadsheet will cover completely the entire next framework PCI HIPAA anything else so but in the case that there is something
missing you have a very easy to use map at the bottom it's called unmapped this is everything that is not covered from CIS over to the other so for smaller businesses for businesses that have no resources no talent pool to be able to specifically address compliance every time you're handed some kind of a worksheet or something from a vendor and you have to answer it this is a very good way to very quickly provide some type of a hand-delivered document to them to be able to show that you do have some idea of what your security looks like all of this no matter who you are what vertical you're in has to take into consideration what industry you're in
that's where the regulation that's where the choice of Frameworks will come in uh the business location geographically where you are where your people are if you're in California but none of your customers are you're held to a different standard for your customer records than you are for your business records so that's the custom home record the type of assets whether you're Cloud whether you're on-prem again this is not necessarily answering all the questions for you but this is how you start your inventory most companies are probably well beyond this point but what I find from a discoverability perspective with smaller companies especially mom and pop companies that have been around for 10 or 15 years and I'm on the back end of
that acquisition that they they get bought into a larger group of companies they don't have these because they've never needed them and they've never been asked so I have to immediately step them up to that so where I come from is I say you know where are you based on gdpr based on HIPAA based on uh you're in California uh that single effort that I put in towards multiple results that's key in what I do because at any given time I'm working with 10 to 15 companies and each of those companies has their own systems some are at AWS gcp Azure summer Colo or on-prem and because of that we have different needs different asks and we have to speed up certain
projects for them get rid of that on-prem Exchange Server now yesterday versus the people who are in AWS every account had keys rotated or passwords have been changed over the last 365 days I worry less about some people than I do others and this is all about future proofing so to be clear I'm not doing this alone I have a big issue with taking ownership of absolutely everything in a company I keep ownership where the data owner resides so if someone is in charge of accounting they are in charge of everything for accounting I'll walk with them I'll make sure that the all the tools that they need to provide that job are there but as far as
regulation as far as complying with you know the CEO or board level requests for this type of information they are the owner they can delegate it down but they can't delegate it back so that risk acceptance is their their decision their responsibility to take uh whether or not they're going to choose to spend 50 percent of what on the proposed budget is they'll get 50 of the results out of that so the remainder of that is a 50 risk exception uh I find that the board does not like a 50 risk acceptance so typically what they'll do is they'll ask them to dial back in other areas of their Department's business to accommodate that because they realize a
lot of the value here in public companies and also in private like my own we're right on the edge uh the the company that I work for we have taken the approach that we might as well be considered public for the purpose of the board having a cyber role the board has now had those requirements put on them so they're taking a much more hard-line approach towards the lackadaisical security that has been and a lot of the smaller companies for a very long time haven't needed the response or the need haven't needed to buy a hundred thousand dollar a year tool to provide a specific function but now it's obviously it's going to impact Revenue to a point where it's it's going
to show value very quickly so parallel efforts is the uh the term that I've put to this uh it's my own it's my own use um basically I like to do let's suggest MFA I think MFA password complexity password managers inventory in those accounts in my mind that's one project that's one we'll plan for it for three weeks we'll communicate it properly it'll happen on Tuesday night at 9 00 pm and and Wednesday morning we'll have a triage session to make sure that everybody's good but those are four large potentially six to 12 month long projects where everybody has a say everybody wants to hold it up for their own reasons this becomes a single project
and sometimes when those get bundled in I think they're easier when they get bundled in with something like an email migration or increasing the security deliverability or putting simple things like Footers on emails you know people have issues because it breaks up your thread and it doesn't this five Footers at the bottom of the email if you don't do it right so all these things to me are one project and that's the parallel effort idea is that we we accomplish these all they're all very relative so we keep uh we keep everything in order inventory we talked about everybody's talked about today best practices this is about best practices so let's talk about passwords password managers password managers I
sell the ideas business continuity yes it makes it easier yes it's more secure uh unless you're using LastPass and then it's not necessarily more secure um three four times in a year they are very consistent thank you I appreciate that I've never thought to use that uh so yeah um multi-factor authentication it's not an option it should never be an option if you can log into it it should be secured the account types I always love this because I know that there's a lot of security and developers in the audience today trying to enforce two accounts one admin and one user account on people that's always fun right I've never been successful with that but I can very
easily take away everyone's and use a Pim I use a lot of 365 so I use Azure ad so if I use the Pim functionality I can provide just in time give it to them for an hour they use it they're done and that way I still satisfy the requirement that say HIPAA has or any cyber security Insurance question here that says is anybody an admin on their devices it was before are any non-it people or non-it administrators admin on their own devices and it was easier to check the box then now it's not so easy so the box has changed slightly because the context has changed um does anyone know I'm curious does anyone know what nist put out as
far as the complexity requirements and passwords universe so 12 I believe is the current does anyone know what server 2022 standard edition uses for the default GPO password complexity well you can read it so in 2023 the minimum password length is seven characters I just walked into someone's office the other day and it was set to three because it could be and I was like why do you need a three character password and the CEO is the one who put that in place but it very quickly turned into this and then it very quickly turned in everyone's changing their password so the the project that I mentioned on the previous slide is real world that was
I'm going to go in modify your GPO your GPO is now going to say 12. it's going to not require you to reset your password every 45 or 42 days which is again the server default on Windows server nist also put out in addition to a longer password they said well change it less frequently because what that leads to is a higher frequency of repeat passwords or the one exclamation point type passwords where they grow by one character and it's consecutively on the number series on your keyboard so adding two or adding three or adding four so changing things like that from whatever their default is Microsoft puts out server software they do not put out policies on server
software we have to refer back to Frameworks best practices industry recommendations and multi-factor does anyone know how to put multi-factor on active directory on-prem anyone ever done that before everyone's looking at me strange you know what smart cards are in the Navy we had to carry our card around that's how you logged in people still forget about that a ubico key can use the same functionality as a smart card for an on-prem active directory so when people say I can't use a year ago or I can't use a smart card or I can't put MFA on my RDP that's public on the internet I would argue that there's actually a way there always has been a way
that right there is a a forest and this is exactly now I don't mind so much with the last 24 passwords I don't want people repeating passwords so this is the default minimum password age that's fine but seven characters and at least the complexities on because before 2019 complexity was a disabled feature it was turned off by default an active directory
uh Microsoft put out while I was here today I started putting out maybe three weeks ago number matching does anyone use the multi-factor from Microsoft you have the push notifications it was approved yeah and then they were like you know what CEOs at three in the morning after 4 500 approved messages pop up on their phone they just hit approve well that's not a good thing so they switched over to number matching well number matching just means that there's a number on your computer and now there's a space for you to type it on your phone and if you don't have that within a period of time I think it's 60 seconds then it times out that's your
failed on MFA I put that into place 30 days ago Microsoft was enforcing it universally across all o365 accounts unless you've explicitly turned it off on May 8th at least they gave us a week or so right so if you have Office 365 you might want to get ahead of it let people know there is some public information out there from Microsoft on it it's very simple it's there's very little impact I flip the switch at nine o'clock on a Monday morning nobody complained nobody even noticed it they just saw that oh it's asking for a number now when they did it so it shouldn't be a huge deal but again the industry is pushing where other people
are not multi-factor methods are not equal obviously SMS text messages should not be used in production environments again this is a best practice this is something that has changed in the last 12 months Microsoft LED this charge uh Twitter if anyone wants to hear that word again Twitter decided to start charging for it right do you think it was because they needed a revenue well they may have needed another Revenue Center actually but no it was costing them 80 000 a month to send text messages so it just made sense and at the same time as soon as they did it and everybody the world went crazy over it everybody else started revisiting their own SMS methods
if you send out text messaging it's not necessarily part of this but if you send out text messaging you pretty much have to re-register your campaigns now on a weekly or monthly basis with twilio or whoever your text back end is because they want to stop the spam they want to stop that so we're not really worried about people stealing people's phones it's more about people taking over other people's accounts so I'll flip through this here you can see this
email security I'll kind of go through the rest of these fast is everyone familiar with dmarc dkm SPF spoofing getting an email from yourself yeah getting an email from your boss it looks completely legit I heard a message today from someone at one of my companies that said uh one of the CEO's tactic was to misspell his own name on his legitimate emails so that if it came in correctly you know it was fishing so and I can't make that up it was quite literally I spit out whatever I was chewing at that moment because that was what was relayed to me um so all this is is about making sure that who's sending emails on behalf of
your domain and you hope your vendors this was brought up today as well is in fact who they are who they say they are is who they are so if you want to send an email as my domain um good luck because I put these in place they're not it's not rocket science it's very well published if you go to any other domain that you deal business with and you check they don't have dmarc enforce if they have it but it says none none you can send them an email from themselves all you need is a Linux Linux VM it takes a few minutes and that's how no before actually does the spoofing check which so if you give
them permission they'll basically just spin up a Linux VM and send you an email from yourself and then try to sell you their their fishing product which is not you uh deliverability again monitoring it monitoring the reports someone had mentioned over here about the the CSP a couple talks ago the CSP the content uh for the webheaders web application headers if you have a a policy in place but you're not monitoring it how do you know if it's working how do you know if people are taking advantage of it how do you know if it was taken advantage of until you actually have a breach um so I'm real big on monitoring for email deliverability purposes
I feel like it helps in a lot of cases I can tell marketing that they're wasting money but when I save the money because I can guarantee their deliverability and give them results now they're on my team marketing with credit cards normally are the number one cause of Shadow I.T for me but what I do is I get ahead of them I find out as soon as they're signing up for something and I involve myself and I give them demarc and D Kim and SPF and I give them the reporting tools and I give them access to MX toolbox or to Markley whatever I'm using for that company so that they can actually see what they
need to do differently to get better deliverability and better results policies that's a can of worms so I'm gonna go over that a little bit but realistically we all know that there's policies that none of us have read most of us have written sometimes you can purchase an entire pack of policies uh control F and just change out the name or find and replace for you know the name of the company the state that you're working in and or just changing the picture on the logo at the top right right everybody's done it make sure you clear the properties on the files too otherwise it's going to show whoever made the file just from my experience
I've seen that enough times so a policy is only as good as the c-suite that actually executes and actually pushes it down and if no one's reading it it's just more trees dead so realistically what I suggest we do is we try to make them bite size we try to take an acceptable user policy I have a two-pager the only reason it's two pages because I left a lot of space at the bottom for people's comments and then also for their signature if someone ever does put a comment in there which they don't but I had to fill the space and I didn't want to make it just a one pager because that seemed like a one-page resume and no one's
going to take that seriously right so that's really where I was coming from I was trying to give them two pages but I find that people go through them and people will ask questions they're just scared to put it in writing so people will actually ask well what about this and that opens up a different conversation so for me it's actually a an icebreaker with the people who I'm actually trying to help secure these are the three and I know this incident response is definitely one I consider that part of the business continuity only in the manner that I set them um acceptable user policy don't click on links that doesn't do anything BYOD that's
much more applicable now but the incident response and the business continuity for me is how I tell the business if and when because it's when not if uh this happens this is what you're going to be dealing with it was mentioned during one of the other talks today you know you have to print this out right first off print it out because you're not going to get on your computer to look at it but everyone needs to know their role they need to know their job and they also need to know how to go through and actually respond without putting hair on fire I don't have to worry about it but some people do so business continuity is
what's going to happen if and when and that's how we deal with things training and testing again I'm just going through what the Frameworks or the requirements would be do you train your employees yes does the CEO always click yes uh if he does them at all so to be clear there's always a question of how do you deal with it the way I like to deal with it is I like to celebrate the success those three people that did it when they were supposed to do it yay um I don't punish the failures but I will reward people who consistently don't click on the links and actually complete their training that could be regular I.T swag it could be you know
those big yeti bottles that I I give out all the time to my people so celebrating it providing them a means without treating them like children to be positively reinforced endpoint protection is great when it works and if it's installed and if it can't be uninstalled right I have a lot of different environments not everything is azure ID connected but something I realized very recently was you know selling me on the idea of Windows Defender it's not the old Defender I was told but selling me on the idea of Windows Defender assumes that all my devices are Azure ID connected because if they're not then it's useless it's not going to give me the same value that
I could get out of a regular free antivirus because realistically there's no reporting there on the back end for me so you pick a tool that works with your environment you don't pick a tool because it's in the quadrant the quadrant is very expensive to get in actually I don't know if you're all aware it's not a free pro bono operation so you may want to obviously consider whether or not you can afford it but also if the uh if the tool will give you enough visibility and be exportable I have some tools that have no exporting for log functions long term those aren't a long-term tool for us they work for the moment but as
soon as I start needing to have a SIM and bring in syslog and things like that then right off the bat I don't have a tool that functions in that way so remote access stop the madness no RDP anymore even Rd web I love when people put it on Port 3390 or 88 that's a fun one they don't realize that scanning it is very easy and it shows up just the same VPN I love when vpns are deployed in their split tunnels and it's sensitive information so they're surfing the internet in one browser and they're on the company Network and the other so MFA everywhere uh IP restrictions conditional access if you're lucky enough to have ZTA or any
other type of tool DNS filtering or any of the Meraki Rocky's a great tool but if you're lucky enough to be able to afford those at the scale of your company then great good on you you're going to have good reporting you're going to have good controls if not you end up getting what you get uh documentation for me it's always if and when I get hit by a bus I tried to make this a little cheerier and say when I win the lottery or when you win the lottery but realistically this is about training your replacement in the military it was never a question of whether or not you were going to stay in that job it was always you're here
for three years so leave it better than you found it and then at the same time make sure the next guy doesn't have to call you when you're at your next Duty station to figure out where the passwords are or to figure out how to log in we know about login and retention third party vendors their breach is your breach I know I'm running short on time so I'll chop it down back up in recovery we talked about it earlier today does anyone think that Microsoft backs up their 365 for them good they guarantee service availability of their product not of your data zero backup on Microsoft 365. and SharePoint and Azure unless you program it or you pay for it you're not
getting it I know some of you will giggle a little bit base64 is not actually encryption in case there was a question I ran across a database the other day where someone based 64 and they told us that it was encrypted um but it's not I just want to put it out there uh so uh I talked about a lot I bruised through a bunch of it realistically if there's a checkpoint somewhere in a framework somewhere on a questionnaire it's related back it's somewhere you're going to be audited for somewhere you're actually going to be held accountable for if you're going to walk in and ask someone to completely do a compliance or a GRC program for you they're going to
be there for two years and you're going to pay for that if you want to pay the 1500 two thousand dollars a day for an auditor to come and sit in your office and actually do an audit for you you do the work yourself so you pay now pay later it's up to you I would argue that there's a lot of good ways to check boxes along the way without having to keep records that would require a third party or another person on the staff just to be able to keep up with it people process technology that's really the only thing here I like to say that end users are not the weakest link but
they're the most targeted so if you consider that you don't blame victims what you do is you support them you protect them and you prevent it from happening again we're not doing that for users instead we're blaming them which is much easier I suppose quick question I swear I did not plan the beetle thing there's like five people today we're doing Beetle stuff anybody YouTube needs to know what the answer is how many are there is five I can't see further down the road but yeah there's five any questions I got a kick out of that just giggle with me well thank you very much I appreciate it okay [Applause]





