PurpleTeam 101 by Chris Peacock
Show transcript [en]
started uh and then are you doing time on your own or do you want me to let you know five minutes left should be fine okay cause I got the time right here
tomorrow
foreign
[Music]
yes
Library
[Music] that's what everyone's doing all the cool kids are doing
literally nothing public
it's kind of crazy how did you find this deal all right everyone so we are in our next on purple team 101 uh if you would please help me walk home thank you [Applause] all right good day after lunch uh spot so hopefully you're not too tired and maybe if I can get my clicker to work all right here we go uh Christopher peacock I go by Chris I started out doing Health test we've learned to network administrator then work my way up through security operations at the time really wasn't called Purple teaming my boss was like hey we have an upcoming pin test and you know some pin testers maybe if you ping them and see what
they're doing and then let's test those out before our pin testers come in so at the time it was
people still can really power show well through an environment but I was cat mousing myself with some of this triple team tools that I knew we were seeing and I made my sister always great but then also got me a bonus so I quickly learned I was like I like this purple team thing it makes look good if it gets me more money um so I was like purple teaming seems pretty cool and that's how I started out with purple two from there I went to Raytheon where I led the threat hunting team there uh from the the Texas engineering side as well and actually I have my replacement is right here in the front row so follow him not me he taught
me so I'm just kidding I'll answer any questions later yeah so anyways I asked for certifications I'm a top contributor to law bass if you don't know what lavas is I highly recommend you run into it it's how adversaries leverage existing Windows Microsoft uh utilities that are built into the windows they use those maliciously so when you see an alert it says powershell.exe and your sock analysts tastes that hooks up the hash on virus toodle and they say hey that's Simon Microsoft and the task is good and they close the case with a false positive that's kind of what wild Mass is like I also do Sigma and we'll touch on that a little bit later as well but
that's enough about myself my clicker's not working again there we go so current threat landscape honestly when I did this we're talking mostly to like large Fortune 100 companies but as I've grown I realize that most of the time we just have blue team we don't even have a red team and oftentimes we might not have CTI people are like I have a CTI feed Chris I'm like but is it actually giving you actionable intelligence that makes your stocking was better and typically it's no it's just it's hash values and IP addresses from no ingredients not the breach that you're having now or that you're going to have tomorrow so with that we have a bunch of Silo teams if we even
have all these teams this thing's really jumping around on me okay there we go so the biggest takeaway from this is that right now the most blue teams don't validate anything I've been in an organization where we we went in and we ran a DNS query for the one I cry we make it's a very well known domain it should raise an alert within the stock that says hey you have Wanna Cry in your environment and when we went in and we did that we actually realized that there was no alert we're like oh that's not good you know you could have one or cry in your environment and not even know it and then we talk even deeper and we realized
that well for this organization they've not even actually logging their DNS I'm saying this is a fortune uh 200 company they didn't know that they were logging that they weren't logging their DNS we also had another one we went into a financial company and we started executing actions we're like all right let's check the EDR what's going on with the EGR like are there alerts or anything like that and we actually found out that the ER had been reporting for two weeks so it's a very common thing that people aren't actually validating that their tools are reporting and what they're reporting on so we need to answer questions like can we actually detect our adversaries
so that's the key thing that we're trying to drive right everyone well not everyone I get a collection advice as I work with very large companies but most people right now that I talk to they're talking about how do I reduce my mean time to detection how do I reduce my name my mean time to response and the way you do that is you figure out what alerts can we work with or generate that are going to catch that adversary early in the attack life cycle we have to test to know that but also are there logging gaps oftentimes we're not testing that as well if we do have CTI team often it's focused on these Atomic indicators and
we really need to evolve to procedures and behaviors Atomic indicators specifically if you are worried about a company over here what ransomware hash they had that's not going to be applicable for your organization because it's going to be a new path but it's likely going to be new IP addresses as well so we need to evolve from that I'm going to move on Beyond those that should be an automated process also if you're paying for an IRC fee I highly recommend just looking at a misf instance because most of the time you just get those for free and miscompiles like 50 some into one instance and you can hook that up to your sim the other area is the red team typically
we don't actually typically have these that's the sad part of it but if you do have a red team or if you do have a pin test they're often not talking with your blue team so they hide their tricks they also might not replicate what adversaries do um Red Canary actually talked about this in their yearly report but there's a great talk by Katie Nichols as well where they go in they talk about what real adversaries are doing and what tests they're seeing and they typically don't the line so that's something to be concerned about so how do we shift our landscape into purple if we're just doing blue team if we're just responding to alerts how do
we move beyond that well it comes down to two key principles and those principles are the threat understanding and then the detection understanding of that threat so with the threat understanding we need to understand what our adversaries are doing if we're just going out and just trying to detect something because we think it's cool to detect we're going to miss what our adversaries are actually doing the other thing worth mentioning here is don't get focused on other threats so I've seen it before where say like an elementary school will actually focus on what North Korea is doing to South Korea you don't need to worry about that if you're at elementary school focus on maybe all the other elementary schools
that have gotten popped by ransomware study what that ransomware adversary is doing instead and then we get that detection understanding but that detection understanding comes from the threat understanding which will drive our validations once again we want to validate that we have detections that we have our logging if you don't if you don't have metrics around things you can't manage it it's just you're just hypothesizing at that point that you will detect it we want to confirm that instead so with threat understanding what are the adversaries doing you know a lot of times I hear people they think that ransomware is something that a user clicks an email and then it just spreads through the environment that's not
actually the case oftentimes there's an initial access broker that gets in and then they have to laterally move in a manual format through the environment to find data worth Excel trading then they also have to get domain admin creds so that they can push the ransomware to all the workstations and then once we get to an area where we understand what the adversary is doing that's where we can start thinking about what the adversary could do on their next engagement and we call that procedural variance so if they're Gathering credential credentials with mimicats and memicat starts flagging on a lot of their engagements well maybe they might use like proc dump instead of mimikats so we start thinking about the
procedural variants that they could have in their operations and then we want to test that so do we actually test the coverage of the adversary once again can we do that validation foreign
understanding too are the behaviors log or not this is a huge one if you when you're doing purple teaming we're validating this and we're going to log any sort of visibility gaps oftentimes when I go into organizations one of the biggest things we we check is name pipe creation and why we do that is because a Cobalt strike the default for Cobalt strike will actually have certain name pipes it creates but a lot of edrs don't log that one thing we also want to consider is when we trigger alerts I've often gone into operations and a sock is like hey we caught that activity and I'm like cool what level of alert was that and
you're like well it was an informational loan informational level or a low level alert how many people here actually work low level alerts if you look around the room right now no one's raising their hand it's because no one actually works those so if you tell me we have an alert for that it doesn't matter unless it gets in front of someone's eyeballs as I like to say because until we get it in part of someone's face it's not an actual it's not actionable for our stock so we have to make sure that those alerts are actually getting to the sock to be worked so that's something to consider as well and then when we're
thinking about this what we can do is if we have a low-level alert from our emulation and we live for the past 30 days and it doesn't trip except for when we run our emulation all we have to do is just raise that alert level we have detection engineering already there we don't have to do it we just have to raise that alert level so someone works it after that we look at can we develop alerts for uh actions that we've missed and then we also want to do detections uh we want to validate those as well usually that's in a repeated cycle of our purple team and then another area that sometimes we also test is and I don't recommend doing
this uh at the beginning of purple teaming but this bottle in here is is the response correct one time I actually saw a there was mini cats on a domain controller the AV removed mimikats so then they close the case because they said that the incident was solved no one actually stopped with him okay how did a credential dunking tool get all the way to my domain typically that's going to be a long attack path so some sometimes we actually have to go in and we have to make sure that the response is correct as well but I don't recommend doing that until you're more mature in the purple team cycle so what does it look like when we're
talking about doing a purple team cycle we get that threat intelligence of what our adversary is doing then we replicate the attack and then that's where we get those tracking metrics and we can also look at our detection and response side of that as well for our tracking so when we're considering this one of the key areas is that threat intelligence make sure you have existing coverage of what your current adversaries are doing one of the great areas to look for that by the way is actually in your email security gateways that's going to tell you some of those initial uh actions on objectives that your adversaries that are currently targeting you are doing so why do we purple team for one it's to
train our Defenders we can go through and we can have them ready so that they're not marking mimikats as a closed case when it gets removed by AV we also want to test the process between teams one time I went on I went on an engagement and with that we went to the threat hunt team and we're like hey do y'all create custom alerts and they're like no the CTI team does that and we go to the CTI team and we're like hey we heard that y'all create the custom alerts here and they're like no no sock must do that so then we go to the sock team we're like hey do you all do custom alerts and they're like no the
threat hunt team does that and then so everyone's around here it's kind of like that Meme where it's like a poor Spider-Man all like pointing at each other and no one's actually responsible for it so understanding that uh teams need to work together and actually discuss this is a huge area we say test ttps when I think about ttps I really think about behaviors is what we're testing we're testing what actions the adversary does on the network is because technically TTP is something that we took from like the military because of cyber was coming up people were like oh we need terms all right well let's just use the military terms because that's where cyber kind of
started was the military side of the house but really what happens is they execute a procedure that procedure gets mapped to a technique and then that technique gets mapped to a tactic so we're really just talking about behaviors the other area that we also might want to do is replay red team engagements oftentimes we have systems they have a nice report from a red team and the red team got domain admin they got to the domain controller they did their thing and they wrecked the environment not like you know physically wreck the environment metaphorically uh and with that oftentimes they want to go through and they actually want to replicate these and start building detections
around it so that's another reason the purple team but the big thing up here is actually fostering collaboration that's like the huge side of this is just having collaboration between teams oftentimes if you are wanting to do a purple team engagement from a manager perspective get a bunch of people in a room order a pizza you know two pizzas however however large your team is and Foster some collaboration that's really the Big Driver here of purple team and one of the big things is at the end of the day even though we might have different silos in our organization it really comes down to this piece up here all of our teams are really focused on
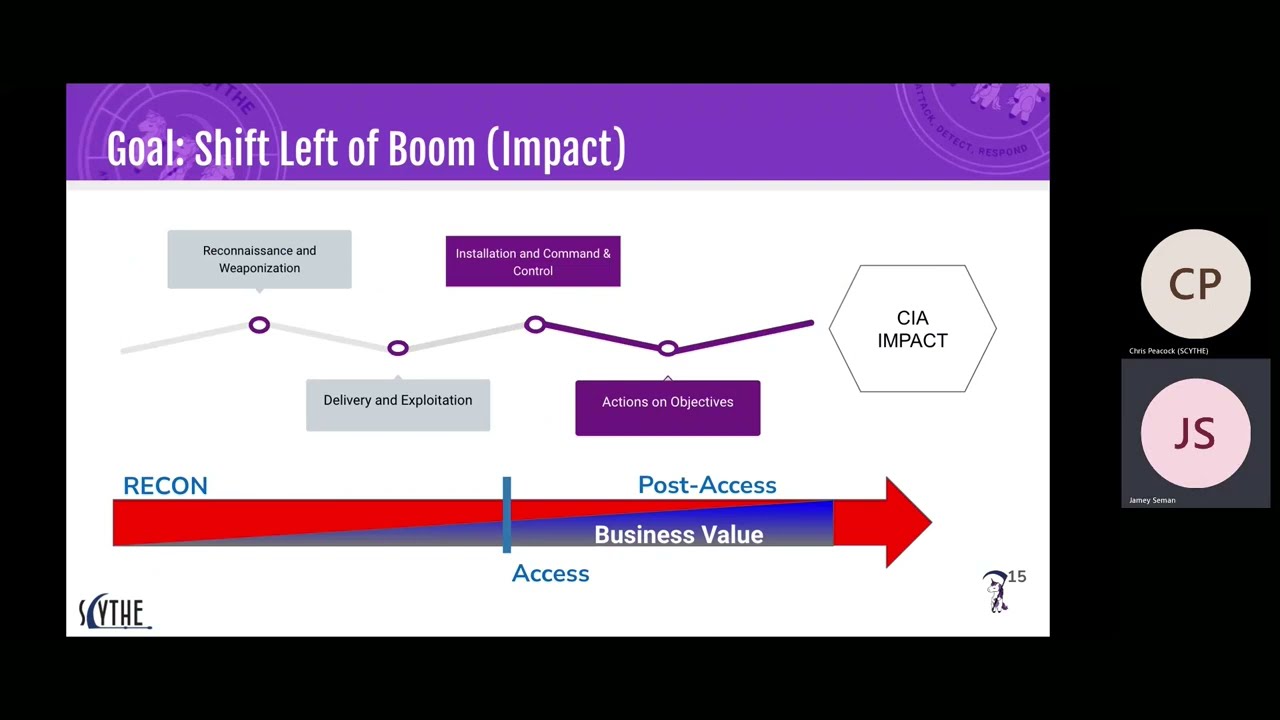
security operations whether you're a pin tester whether you're just doing um some sort of compliance driven type work if you're actually doing detection or response all it comes down to is we're trying to keep Bad actors out of our organization so we're all on the same team when we also talk about purple teaming one of the areas that we like to focus on is the post access because access can be expensive one thing cisos don't like is just spending money to spend money I typically want to be efficient with spending their money because we all have limited budgets so if we're on an engagement or someone asks you to do a purple team test can you fish your way
in sure it might take a day it might take two days might take a week but we know statistically users will click links that's just that's a fact you can you can put an email that says this is malicious you can literally send an email it says this is malicious don't click the link and statistically someone will click that link it's crazy right but it happens so let's just assume breach and then we want to focus on that installation setting up that command and control right now if we want to replicate this we might do some sort of like ISO smuggling that's really big right now in fishing attacks so maybe we make a custom ISO and then we
replicate the dot lnk click so we don't actually have to fish a user we're going to say okay this is what they would do with our current threat landscape and then typically once they click that lnk file it's going to do a dll execution using something like run dl32 so now we we have a lot of the front-end detection opportunities that we're covering by doing that emulation and then after we get that initial command and control setup and installation it's the actions on objectives so what do adversaries do once they have Hands-On keyboard access with their command and control but the biggest thing here is we want to catch it before impact right Canary report this past year is
actually really good and one of the things they talked about they said look we haven't really seen ransomware incidents and what they said was is we see a lot of precursors to ransomware and it's because this installation command and control and these actions on objectives they're catching the actors there they're catching them there before we have impacts to the confidentiality integrity and availability of the data so that's where we see a lot of the business value it's one of those things where prevention is nice but we know it hasn't worked if it worked ransomware wouldn't be a thing and also this conference wouldn't be huge because everyone would install AV and then we wouldn't have jobs
so let's focus here and we can prevent that impact if we catch those ransomware type precursors other uh precursors of attacks as well so we see a huge business value there once again Provisions nice but detection is a must some other areas why we assume breach we've already talked about that efficiency in cost fishing Works Insider threats as well that might be another reason that you want to do testing misconfigurations or you could already be breached the other area is zero day if an adversary uses a zero day you you know they're gonna get on to your host so that's another reason we can assume breach also by the way I do not recommend Testing mobile devices for one the
Telemetry is not good on them and also yeah just talk to Legal before you do that because you're going to get into a bunch of weird areas so if someone asks you to purple team mobile devices maybe rework them to only testing Linux and your your Mac OS your laptop workstation servers one reason though we don't uh do zero days replicate replicating zero day type activity is because of the cost of zero days so oftentimes people will be like hey can y'all exploit and gain access we want to replicate that like our threat is you know aapt X Y and Z and they have a zero day stockpile so can you replicate that and be like look they're
gonna get on your network let's just replicate setting up the C2 because then it doesn't matter what uh zero day they use and then also they're like well we really want you to use a zero day well up here uh for from uh the rhodium a Windows remote code execution zero click zero day is going for a million dollars so if someone comes to you and say hey use a zero day to get on the system be like you got a million bucks and then they'll probably say no when we also talk about purple teaming once again we start the first step here with that new Cyber threat intelligence and then that drives us to run the
analysis on it we then map that to uh attack by the way miter if you're doing the miter or if you're mapping a miter just a a curve tip here I don't know what that means because a miter is a defense contractor that manages ffrdcs so if you're doing the miter I don't know what that means because that means you're it's like saying I'm doing the Publix like this is the company so attack is a special uh a special CTI type product that miter developed and put out but what we do is we map it to attack then always get in step three and call this the permission stage because before you execute anything on your business
Network make sure that you had permission to do it and then we emulate the attack and then that's what drives the detection engineering and that might be the things like elevating existing alerts or deploying new alerts um so okay we know that we probably should do this new purple team thing we know that we need to evaluate our security operations but where do we start so when we're talking about where to start one of the first areas that we go to is atomic red team with atomic red team in this example there's a nice GUI that they have uh on the web and you can see all these different areas over here so you have like this by the way this is
for technique 1218.005 so it's sub technique and it's executing with mshta by the way Microsoft has a list of built-in window applications that you should block it's like there's like 50 of them if you just like Google like Microsoft blocked recommendations it'll come up and there's like 50 built-in like applications and scripts that they recommend you block why do they still put them in there you know that's another conversation I guess backwards compatibility but they're like yeah we put these things in there and you probably don't really need them and adversaries commonly use them but we put them in there for them it's like okay thanks Microsoft but anyways so for this sub technique that I chose
and if you just go to like atomics up here you can pick they have a whole list of different uh techniques and sub techniques that you can execute and then on the on your right my left they have Atomic tests for them so here if I just click Atomic test one that would be like a nice little script that I can grab and I can execute that in my environment I don't need a red steamer I don't need a blue teamer to spend a lot of time oftentimes people are like man it's really hard to do adversary emulation or purple teaming like because our our blue teamers they don't know how to set up a command and control they
don't know how to use metasploy they're not really proficient at Cali you know the list goes on and on but here as long as you can copy and paste into Powershell you can pretty much execute what you need to execute so we don't have to spend a lot of time training uh someone to do something new I mean I'm pretty sure most people can copy and paste so this is where we typically recommend starting is going over these there we go now instead of copying and pasting they also have invoke atomics so this is something that we can set up and install by the way whenever we're talking about testing I recommend testing in multiple ways typically what
we do you go and you say hey help desk y'all have a gold image you grab that gold image you deploy a VM it's going to have your EDR your AV all your logging stuff on it and you can install this on there and you can run these actions also by the way if you have a different server policy also do your servers as well and then typically we'll also set um the test box one in prevention mode or whatever your organization is running by default hopefully the running in prevention mode but you know we'll take the default and then if we need to we'll also test on a different box where we just have it on alert only mode because
we want to we want to run analysis on the alerts but with invoke Atomic tests as you see here all we do is we tell it the technique ID that we want to test and then we tell it which test numbers for that technique ID and then it goes it automatically just executes those for us so this drives that telemetry so now we can go ahead and we can look do we have logs for this do we not have log service we can answer that question confidently now and then we can also look at alerts and we can say do we have alerts for this or do we not have alerts for this and from there if we need to fix
anything we can fix it as well so that's a little bit of starting and this is just kind of if you're starting out this is a basic process so we test do we have logs or not do we have alerts or not and then if you want to you can eventually get to the point where you respond to it and like we said before vary we always want to vary so what happens when we don't have an alert I'm here to tell you today you can be a freaking amazing uh detection engineer without actually doing detection engineering I know it's crazy right there's a product called well not it is an open source framework called Sigma
and you have over 100 people on Earth that contribute to this so you have detection Engineers that are out there deploying rules to Sigma that you can use but the problem is you don't know which ones to deploy yet well the same people who made the sigma project they also made the EDR that's based on Sigma I say EDR kind of loosely because it's not like a full-scale PDR in my eyes but it's pretty good and the cool thing is is if I install this on wherever I'm doing my purple team actions it's going to tell me what Sigma rule is available for me to deploy so if I do an atomic test which by the
way typically Atomic tests they actually if you look in their files they're going to have Sigma rules for them so if you don't have an alert you're going to have a recommend a recommended logic to create an alert for but if you're testing new activity and you don't have an alert for it install or of run that activity on that box and it'll tell you the signal the signal rule that you can then deploy so you can look like an amazing detection engineer by just doing that run whatever you need to run on a test box without with over installed grab the rule that someone else has engineered and then slap it into whatever product
you need to slap it into so this is an example of that process here I just ran a who am I command and then it gives me the output so it tells me okay we have a rule title of who am I it tells me who the author is shout out Florian he's one of the creators of Sigma and then it gives me the rule link so I can actually go and look at the rule um by the way this is actually in Splunk there's different ways to set up the logging and then it tells me the match strings so if I ran multiple steps I can see what the sigma actually alerted on because of the match uh strings and it
gives me a rule description so here what I can do is I can copy and paste this uh URL into my browser and when I do that I now have the sigma rule so here we can see I need a log source of process creation the detection is pretty simple it says image ends with who am I or the original file name is who am i.exe so what I do now is I'm looking at this I can go ahead and write a rule if I need to or the other thing that I can do is I can simply copy this uh we'll come back to that I can copy that put it into this uh you
are this this website called uncoder.io and then I can select over here whatever the product is that I needed to go into and then it translates it for me so once again it tells you if you run the actions it tells you what the rule is that you need to gain coverage of that and then you can translate it to your EDR that's simple so that's cool because now I can start doing detections on that I can start validating areas but the problem that we run into as we start growing as we start doing purple teaming as we start validating our detections is okay so for process discovery if we run these Atomic tests what if the
adversary is actually doing this so that's where we have to grow and we actually have to study our adversaries by the way whenever there's a procedure so Vice run taskless it does map to process Discovery uh 1057 but if you look there's actually a command line execution here and here we say Powershell so most procedures actually have two technique IDs there's the execution method and then there's what it's actually trying to do and that's why if you look at like some reports especially like the Red Canary one that I've kept referencing one of the top things that they saw was Powershell why because you still need some way to do execution so that's something to
consider so what if the adversaries actually do a native API well we need to think about that we need to test that that comes to how do we understand what threats are threats have to have hostile intent capability and opportunity if it doesn't have those three things it's not a threat um we can control opportunity through things like patching and doing stuff like disa stigs deploying hardening our workstations but they're still going to have opportunity that's just a fact the capability as it grows your threat also grows and then hostile intent that's something that typically we can't control but you you kind of can so like in the case of Sony maybe if you don't release a movie
about targeting the North Korea as a dictator then maybe North Korea won't actually Target you for those of you who are unfamiliar with this story uh they released a movie of them going and killing her trying to assassinate or something the North Korea dictator and at the end of the day Sony got breached and they had some embarrassing emails leaked from North Korea so you kind of can control hostile intent that's something to consider but if it's not those three things it's not a threat so finding out who are your threats what you need to do is you need to identify the adversaries of who your threats are gather the threat intelligence and then extract those behaviors what are your
threats doing and then you can test those so that's how you mature more as you're starting to purple team more you start growing that way when we talk about what we want to test we want to think about our detections so we have here the Pyramid of Pain by David Bianco you get he gave a great talk um it's been 10 years now it's been a decade since he released this but he gave a great talk at b-sides Augusta highly recommend looking into it one of the big things he said is associated ttps he would have probably put behaviors up there but that's where our focus is we don't need to replicate hash values IP addresses so on and so forth
we have ioc feeds that should be taken care of that automatic Auto uh automatically then we get to areas where it's like Network artifacts well and host artifacts and tools that's where we're focusing on our av and our our next-gen firewalls we're using stuff like snort and Yara that's more vendor focused what we want to focus on is those behaviors those are the that's the detection validation that we want to run and when we talk about that when we talk about behaviors this comes down to getting up to the procedure level so if you tell me that an adversary did credential access I don't know how if you tell me they dumped lsas memory I
still don't know how so if we get to procedure level of what the behaviors are that we need to replicate that is key so don't often like oftentimes people will go to like hey can you test you know credential dumping and it's like all right but which one and why so these things matter because procedures they map two techniques techniques don't really map down if someone just says Hey run these techniques it's like all right well we can run the atomic test for those techniques but we are not validating that we would actually detect the adversary in the environment because we don't know what they're doing yet why we focus on the procedures is because of the human element
so this comes down to humans have specific training they fall back on their training they have certain tools and those tools have certain capabilities built into them they also have approved actions oftentimes uh threat actors are in large organizations and they they only have certain actions that are approved for them to take we also get to run books and habits so with habits if an attacker has been successful doing a procedure the last five engagements do you think they're going to replicate that on the sixth one most likely yes you know until something changes within those operational environments they're going to keep doing what they've done habitually and finally we have run books so here's
an example from the Conti Playbook where they actually they're supposed to replace this IP with an actual IP address but they just copied and pasted and so they're into their C2 so they they will go through just copy and paste and it's one of those areas where we have to understand our adversaries at a procedure level because they will they will reuse procedures in fact I believe it was relia Quest said that they even they uh published recently an event where they actually saw the actor copying and pasting from the Conti Playbook still even though it's publicly available and out there like other ransomware operations are still using it because it works because we're actually bad at validating that we
can detect procedures and with that why are we bad at or how bad are we at detection detecting procedures so this over here is the amput one report this was a decade ago if you look at these procedures of them enumerating the local group administrators and the domain admins that was 10 years ago and it's still working here's the Conti Playbook they're still doing those procedures so I would highly recommend going back to your organization running those commands and seeing if it actually trips a response from your sock or your mssp because if it doesn't you should have some concerns so how do we do this testing though based on Cyber threat intelligence this was a report from Microsoft that we
just grabbed and if we were concerned about what this threat actor was doing or if my sister or my boss said hey did you see this new report from Microsoft there is a zero day being exploited and here's the follow-on activity it's pretty simple here we can do some micro tests so we see mshta going outbound all right let's test that and see do we have that activity in our environment can we flag on that if the adversary were to use a new odame and then run that command but also see who am I being piped out to a text file all right let's test that does that trigger a response from our sock or not so that's how we get down to
just trying to do some micro tests when we're starting to see CTI and that's actually making cyber threat intelligence actionable not just iocs coming in but actually taking something like this and then testing it in our environment that change nope okay it like linked like it did but it didn't really so as we evolve from that we finally we'll get to a point where where we're uh more mature and with that this is an example by the way the defer report is amazing you should test pretty much everything on there like every organization should be testing that but this is where we actually get a full scale um attack cycle that we could actually go in and we can test so this is where
what we would do here is we'd actually extract each one of these steps so we see that the user clicked the dot lnk file so we build that lnk file we'd replicate it and we'd also go through all these steps we see ipconfig Slash All System Info net config workstation look we have the domain trust uh net view all domain net view domain admin see this is a common one highly recommend testing that one but what we do is then we can actually do full replication so we can actually get a C2 you can grab one off the internet by the way if you don't know which uh command and control framework to use there's
actually something called the C2 Matrix you can go on there you can see which ones are free you can use those for free and build out your mc2 that then you can replicate all these activities with otherwise if you're just starting out most of these can just be ran within uh CMD command prompt or Powershell so that's a great area so after we've done our testing this is where we get to an area where we want to document and this is kind of what documentation looks like one of the areas that we wanted to focus on at the time this was a ice ID which typically what happens is this would come into an organization
and it would execute these commands and then the initial access broker they would sell off the access to a ransomware group and then they would come in and they would drop Cobalt stripe and then they would go through an organization they would laterally move and then they would deploy grants somewhere later well when we're talking about shifting detection left we're talking about detecting it early on in that attack chain so we wanted to get that initial one by the way incident response is a lot cheaper if you catch it on the first box when something laterally moves your incident response to Costco is way up because the hours go way up and incident response is not
cheap so what we did though we tested these five common uh commands that we see isid do at the initial stages and we did this against a pretty well-known EDR but we won't say which one and as you see as you can see ipconfig Slash law didn't get an alert uh one alert but there's a sigma recommendation remember if we execute something and we run it against Aura it'll actually tell us our signal recommendation so we could go and we could fix that yeah but why did an ipconfig is probably not the best thing to do some detection recommendations aren't always applicable but how often you know do we see it with Slash all in our organization
I might go into an organization and with Slash all there's there's no activity for that so that could be a really quick win and catch an attack early in the cycle you know in some organizations in common it just depends but maybe then you can figure out a parent process or whatever is actually causing that shape we went to System Info once again no alert who am I slash groups we got one little level alert but who works lows workstation once again no alert net used no alert so we're we're looking at this data and we said okay so when the initial access broker comes in and they run their commands to figure out where they are before they sell off
the access you would not actually get eyeballs on this activity so that's what I'm coming down to is we need to fix that we need to be able to actually get eyeballs on a screen that's looking at these alerts and that's the major thing is we we can't evaluate our response unless we actually do the purple team cycle where we're actually testing some of this activity over here so we have a few options when it comes down to what we want what we want to do to execute that activity and the way that works is we have the atomic test iv74 this is easy to automate once again they have that uh invoke Atomic script that we talked
about and we can do some detections around it then you get some micro emulations and this is as you grow from testing atomics you'll start chaining them together to see how your correlation trips and then that's usually using about two to three techniques and then when you grow to a more mature environment finally what you get to is testing that full emulation and that's going to like and running all those steps through because you want to validate them the reason why we use whole emulation is so that if the adversary changes any of those procedures that we've seen they're probably going to change all of them right so if they have if we've seen 20 procedures that the adversary did has
done they might change 10 of them on the next engagement but they're probably still going to use the the same tin uh at some point so what we're trying to do here is we want to put out enough landmines in our environment that the adversary will step on one that's what we're trying to do and that's why full emulation is kind of the top and that's how we go from the walk phase of or the Crawfish of atomic the walk phase of micro and then when we're running that's where we get to that full emulation side so with that I believe that's my last slide oh oh two more things resources this is publicly available it is a
framework if you want to dive into purple tuning highly recommend reading this uh my buddy George he actually published this but he was at City Bank at the time uh or briefly after Citibank either way it's mid for a very large organizations there's Frameworks that Frameworks to your organization and the resources that you have right so you probably don't have as big of a team as City so adapt it to your organization great link I highly recommend checking it out version two is out we also do templates so this is a basic template uh We Gather a procedure we then map it to the technique and tactic and then always cite your CTI Source because oftentimes
you'll be like an adversary wouldn't run who am I and you can say yes they do and we have the link that you can click and we can show you so that's something to consider it as well all right so happy hunting and now I open it up for questions [Applause]
[Music]
the clock is off