The Hashcat Chronicles: Cracking Passwords Like a Pro
Show transcript [en]
Jon Milkins: Hey everybody, thanks for coming. I appreciate it for those of you not wearing your shoes, I applaud you specifically, because we got yelled at for it last night. So you know little inside joke there, but yeah, I'm John milkens, also known as caveman, with my wonderful crew. So a little bit about me currently working as a pen tester and red Teamer. Was on the Mandiant red team for a few years. Before that, I was in the army for quite some time, and with Center for Internet security, where most people are familiar with their secure benchmarks, and not really anything else, but they have, you know, a lot of other stuff going on, avid role
playing. Game player, primarily D and D. And then I brew a bunch of hard cider every year, because I live in Vermont, so tons of apples. And then we also just started brewing or distilling brandy as well as a fun hobby. So we're going to talk about Hashcat today. Nothing really novel here, but nothing really is in the pen testing world. It's really just creating efficient processes to help you get the job done faster, because typically you are on a time boxed assessment, so really narrowing your scope is what you want to do. So what is Hashcat, right? It's open source software. You know, open source, right? They have a huge development team in contact with
them very frequently. I'm sure they hate me by now. And you know it does actually go through rigorous code reviews before every Hashcat release is made public. But if you want the bleeding edge, just pull it off the repo. Do the code review yourself. There are some networking functions that you can take a look at doesn't technically need them to operate, so it's on you to remove those if you wish. It supports over 500 hashing algorithms. It doesn't support everything. And primarily, why most people switch to Hashcat was it they were one of the first to support GPU cracking really revolutionized the cracking game, primarily before that, people were hoarding rainbow tables, which are absolutely insanely large. Just to give you an idea, an eight
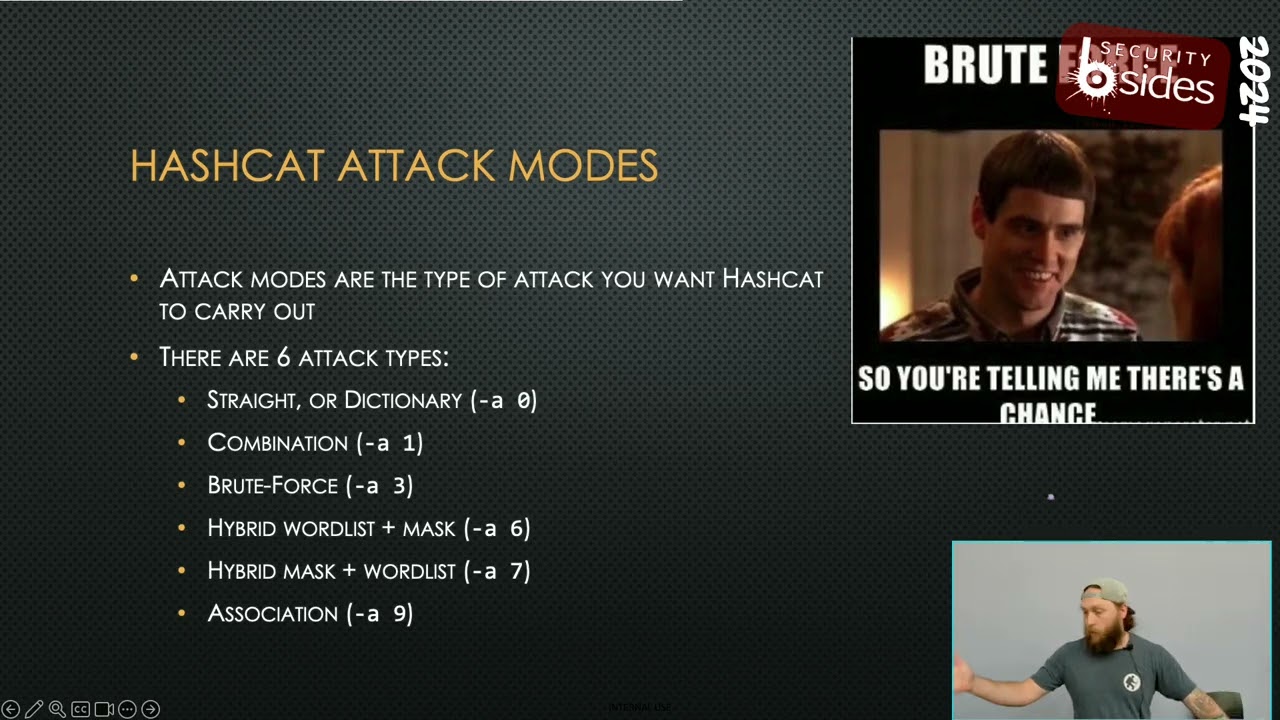
character rainbow table for an NTLM hash set is approximately one terabyte. So as you add an additional character for that, it increases exponentially, and nobody has the money or the place to actually store this cloud costs are through the roof. Don't know if you have a bunch of cloud assets, but you know, it is not cheap. And the real good thing about Hashcat that we've been seeing, and I've been using a lot lately, is they have so many different attack modes, right? Not just the hash modes, but you can combine these modes and come up with unique guesses that you otherwise wouldn't have with something as simple as a dictionary and a rule set, which is the most
common cracking method outside of brute forcing. John the Ripper was once our favorite, but, yeah, it's a CPU cracker. Yes, they do support GPUs. It's kind of finicky, but it did take for ever to crack hashes. So we all moved to Hashcat, you know, and got to have the obligatory meme here. But, you know, this was literally the pen test community as soon as Hashcat came out and really started taking off. So, you know, just pretty funny. But an eight character brute force on John the Ripper is going to take quite a long time using just CPU. For instance, our eight GPU rig does an eight character NTLM crack in about, you know, eight hours, just shy eight hours. And
that's on some old, old cards that we need to upgrade. And, you know, still not in the budget yet, but, you know, we're working on it. So I dubbed this the pen tester pack. These are primarily what we see on a day to day basis when doing most of our pen testing, it's going to cover your ntlms, all your Kerberos hashes. So kerberosting as rep roasting. You've probably heard those terms before. You know they came out in like 2013 2014 still viable methods for getting domain admin and corporate networks. Was doing a test for a client recently cracked a da kerberost, who used the password? Password one, yeah, yeah, no, it was a DA. They didn't split the. Account.
It was his normal user account mailbox, the whole nine. So, yeah, zero to da in probably an hour for that test. Most of the time, I would say we're da within 30 minutes of coming in. So pretty interesting. You got your net NTLM hashes here. Those are associated with tools like responder or invade man in the middle six that's capturing that network authentication material, good way to get it cached credentials. Those are extremely slow to crack due to the number of rounds associated, as well as it salts with the user name. So they're all the hashes are unique in a way, and it's just slow, but can be done. I have gotten da that way. It's just slow and painful. Ms, SQL
hashes, my SQL hashes, Wordpress, Joomla, and then SHA ones, MD, five. You'll typically find those associated with your your internal web apps and things like that, or external they have support for tons of other things. If you've ever done any sort of CTF, or, you know, any certification, you know, you can crack zips. You can crack docs, right? You're going to need John the Ripper to create hashes for those. Or you can do it yourself. I don't suggest that it sucks. Just go ahead and use the the wonderful tools from the John the Ripper crew. But yeah, then things like IPMI, IPsec, you know, Ike, Aggressive Mode, things like that. You'll come across them, but this is primarily what you're going to see on an
internal network, little bit on the external side. So you might not know what these hashes look like. Hashcat gives you this wonderful page. I'd probably use it multiple times a day. It's their example hashes page. So if you don't know what your hash mode is, it can try to figure it out for you some hashes a little you know, like MD five, ntlms, they're all 32 characters. They're all hex characters. So it doesn't know which one it is. Kind of got to know where you got your hashes from, but if you don't know how hash is formatted, this is a great resource, because some tools do not output your hashes correctly, and you will have to troubleshoot it, because you
will get that, that terrible separator, unmatched error, and then you have to sit there and troubleshoot, okay, well, what's wrong, What's wrong, and this is a great resource for that, especially for like Wi Fi hashes, sometimes Kerberos hashes, because some tools do screw up that output, especially when you're going through a c2 that is splitting the output and you're rebuilding it yourself. So highly recommend looking at this page. It is an invaluable resource that, you know, I stare at frequently, even though I do this day in, day out and just play with our cracker at work all the time. If this thing would change slides, we'd be good to go. So here we got the
Hashcat attack modes. There's six main attack modes. You got straighter. Dictionary mode, this is your default mode, so you don't need to specify it. It's specified by default. But being good stewards, you want to know what you're running, and if people come across it, just give it the a zero, just for brevity and verbosity. Combination mode is where you take two dictionaries, append the guesses together to create new words. Brute force is exactly how it sounds, trying, character by character until you find whatever. Very slow. Once you get over eight characters, that becomes extremely slow. Hybrid is actually my favorite to use. This is really great because you can combine a mask. So what you're going to use with those
brute forces, you can go ahead and combine those with a word list, right? So a six is an append so you can append a mask to the end of every guess. A seven is a prepend so it puts it at the beginning. Really great for creating a bunch of different combinations. The creator of Hashcat Adam, these are his favorite. He did a whole talk on the use of these and why they work so well in corporate environments most of the time. We know just through how humans are, we know, oh, we need an upper, we need a lower, we need a number, we need a symbol. OK, well, what's easiest for us to remember is, OK, typically,
let's just put a upper at the beginning of our password, because it's like a sentence. Boom, there it is. There's our upper. We got a bunch of lowercase letters because we're writing a word, we're writing our daughter's name, we're writing our dog's name, we're writing a season a month, you know, whatever. Throw in the current year or your favorite number and then hit it with like, an exclamation point at the end, right, or typically, an exclamation point, an at symbol or a hash or $1 sign. In most cases. Is right? Because we're all lazy. It's just human nature to be lazy, right? You think I'm going to create the best password? No, you're going to be
lazy. You're going to follow a pattern, and those patterns are recognizable, especially with enough data. So when you see a lot of these passwords and you run you can run analytical models across them. I don't do that. I'm lazy, like I just said, humans are lazy. But every time I crack I look at all the cracked passwords and I try to compare them to other cracked jobs I've run to see, Okay, are there specific masks that I can create that will guess people's passwords for me without necessarily needing a word list, because people follow a pattern that first character is always an upper last character is always a symbol. Majority of the word is a lower case, right? You
can create custom word lists, not word list, but character sets to specify. So if you know that it's likely going to be leet speak, you can do a lowercase and digits, maybe, maybe a symbol, but you're increasing the time because you're increasing that character set, and you just throw those in there, and then you can kind of pick up a lot of people's passwords. So this isn't magic, it's just research, examining, you know, human behavior, understanding what people are likely to do. So a little psychology comes into play here, and then using that to help facilitate your cracking, so that you can be as efficient as possible, right? That's what it boils down here. For instance, a standard pen test is, you know,
two weeks long. That's not a lot of time to crack. By the time you get the hashes that you want to crack, you know you're already a couple days in. So realistically, you have five, maybe eight days tops for any sort of cracking unless you're doing a long term red team engagement. Then obviously that those windows are are well extended, but not a big deal here. And then Association mode. I don't use this mode very frequently because I never know what hashes or passwords are created on. But a great example of this is using bcrypt. Right? Bcrypt is an extremely slow hash to crack, but if you know that all the passwords use the timestamp, like a Unix
timestamp, in the creation of these passwords. You can feed that in with the association mode, and the time to crack is like a few minutes. So it's really useful, but you need to understand how they made those passwords with that data. So we don't typically crack those, we'll run them through, but we don't typically use Association mode, and it's just like a job that runs in the background on like two GPUs, and it just runs indefinitely to hopefully crack that and develop it for later. So again, this is the intro to password cracking. Right? How many of you here play online multiplayer games, or have in the past, you ever seen this in general chat? For those wild
players, I've definitely seen this in the Barons chat. It's absolutely hilarious. But yeah, brute force cracking is what everyone thinks when you first start password cracking, then you do your dictionary attacks and your rule sets, and then, yeah, just social engineering is just the easiest way is ask somebody for a password to likely give it to you. So I have a nice little tool called just ask. So if you're on a box, through a c2 or something, just run, run a little C sharp code, and it puts a nice little pop up on their on their page and ask them for their creds. Actually fished the head of red teaming for a very large CDN company in my career with a WebEx prompt on
Mac. So dropped a nice little Mac through OSA script and and J script and told him he needed to update WebEx live on a WebEx call mind you. And said, Hey, why don't you go put your admin creds in here? And he goes, Oh shoot. Hold on, guys. I gotta update. And sure enough, got his creds. And then use those to pivot around the CDN network, which was a zero trust network. So I used those to pull down his key chain, open his key chain, and then we extracted his device and user certs, which is what they relied on for their zero trust. So pretty hilarious. So password cracking can also be done via social engineering. You
know, it's not it's never off the table. So again, general cracking methodology, this is how I approach pretty much every crack job that we have always start with a smaller word list. The more guesses you have, the longer it will take. Again, people are lazy. They will create terrible passwords when able. Nobody wants to write a 16 to 30 character password that they can't remember and have to go into last pass every time to. Go get and it's just a huge pain in the butt, especially in corporate networks where last pass or one password is not required, they're going to be as lazy as possible. So start with smaller word lists. This is especially true when you're
using harder or more more intensive crack modes. So your B Crips, even Kerberos. Kerberos can be a little slower, but your fast algorithms, like NTLM, MD, five, SHA, one, not, not a super big deal. But again, you just want to be as efficient as possible. Every time it's cracking, I'm staring at it for the first like 510 minutes of the crack, looking to see if there's any good passwords coming out right? If I see a lot of passwords that start with the word password, I'll kill the job, and I'll run a brute force job with a mask so it starts with password, and then I'll throw up to five characters after that of any character, because that runs in less than
10 minutes on our rig, and it's just a good way to dump a ton of passwords. Same thing, if you identify just random patterns that appear over and over. Okay, all these passwords have six to eight digits, and they either end in three characters, or they end or begin with two to three characters of upper and lower, or symbols, or whatever, you can create a quick little mask. Run that again and you can crack it. Had a client last year with my pen test business, cracked a couple of the passwords in two minutes, found a pattern that they were using, ran that pattern, made some slight modifications to use any characters, cracked 98% of their passwords in less than 10
minutes because they had a terrible password policy, and they gave every user a patternized password. So again, people are lazy and follow patterns and things that are easily identifiable. So like, if you're a blue teamer, looking at attacker activity, we all do the same thing, right? We're going to look at directories. We're going to move around, look for things that we can abuse or leverage from the system to complete our goals. You can kind of do the same thing with passwords and password policies. So that's the Examine your crack passwords for patterns. Next you want to increase the difficulty of your jobs, start using larger word lists. Start using more complex rule sets. The most
common rule set out there right now is one rule to rule them still, it is a Redux. It's about 52,000 rules. It takes the top 10 to 15% performing rules from a bunch of different well known rule sets. Combines them into one. It's relatively efficient, but when you add that to a massive word list, it can take a day, two days, you know, up to three days for a job to run, right? And as I said, we have a time box assessment. So you know that might not be your best course of action. And then the other thing that I always recommend, and I see a lot of people not doing, is taking all those cracked passwords from
their jobs during the assessment, parsing out those passwords and then using that as the input list and running it through the most complex rule sets, you have to generate additional passwords, right? Password history is a big thing. If you can grab that, go for it. You'll get historical. It'll kind of give you a little bit into that psychology, into how that person thinks, and you can kind of guess their their passwords again. But my personal word lists and rule sets that I use in every job are here. I do love the standard rock you mainly because it's just funny. When I find people using passwords in Rock You Like in 2024 that's hilarious to me, and
it's just a relatively good rule set. It's about 135 megabytes in size, so it works really well with large rule sets. So things like one rule to rule them still super unicorn the Royce rule sets, because Royce is a hash cat developer and has some really good rule sets, but they are quite large. Hash killer is a great one, the combined cyclone hashes.org, hash killer one is, is my go to dictionary. I use that one first all the time. That actually was a recommendation from the Hashcat team themselves. They said, This is what we always start with, and we pair that with the inside Pro passwords. Passwords, pro rule so that came directly from Hashcat developers. They said
that is the most efficient combination of word list and rule sets that they have identified to date on most GPU rigs. So shout out to chicken man for that one. I appreciate that Sam's probably talking. Hearing from me again, but this is where I start. It's not the end all, be all, but all of these rule sets are either come with Hashcat. If it doesn't say included with Hashcat after it, you can find it on GitHub just quick searching. They're pretty easy to find because they are very popular. And then all these dictionaries you can get on the internet. Week pass has all of these. And all those dictionaries are vetted. They also have tons of other lists of
varying sizes, from many all the way up to extra large, you know, like 130 gigs unpacked for one dictionary, super inefficient. Don't recommend it. But if you have nothing else, and you've done everything else, go for it. Run it. But it's pretty slow,
too far. Lastly, another good thing to do is always generate your own word lists, right? I know you do this for web app testing when you're trying to find some stuff that might be custom to the organization. But it also works really well for password cracking, because you're going to find words or references that you didn't think of that were associated with a company that they actually used for passwords, but was found on their website. So you can use cool there are other options out there. Not really going to go into all those. But the other good thing, and something I do pretty frequently, just because I find it interesting, and they do a lot of really unique hash
types, is there's an annual crack me, if you can competition. So Hashcat competes in it. John the Ripper competes in it. Hashes.org competes in it, and it's like for bragging rights, essentially, because mainly the your cracking teams are the ones that win, right? So your hash cats, your John The rippers, are the ones that usually do best. But the write ups are really good for this, because they talk about creating automation to generate words, and they start introducing really interesting word sets that you would not be able to crack with just dictionaries and rule sets, and even combining them, they add spaces in between words, and they're pairing entire phrases from source material, right? If you figure
out the source material is Star Trek, it's probably a full phrase from Star Trek or game Thrones or whatever. I think they had Vogon poetry from Hitchhiker's Guide and one of the in either 2023 or 2022 but they knew the source material came from Hitchhiker's Guide, so they basically got a text copy of the book, converted that into a word list, and did some automation around WORD LIST creation with that, and they were able to crack those passwords. So it's you can always pick up good tips and tricks from them, for sure. Again, I keep talking about efficiency, right? We're always on a time crunch with this, so don't just throw rock U 2021 right? It's a massive word list, like 90 something gigs with the
one rule word set that's not efficient. It'll run for, I think, on our AGP rig, it runs for about two and a half to three days, and it hits, I want to say, like, 25% and just face plants, because the operations on the rules get complex, and it just doesn't know how to do it with all those guesses, and then it just the speed drops to like, 40,000k or 40k instead of, you know, gigahertz. So don't recommend that. And then keep it simple, right? Anytime you crack passwords, put those in your own word list. So if you're a pen tester and you work multiple jobs, even if you work at the same job, take all those cracked
passwords, make your own dictionary with those people will reuse things, or they will take them, mutate them just slightly, and then, boom, you're cracking those again. It also saves you a ton of time. So was playing around with this with the have I been pwned word list if you want to do cracking on your own, just be forewarned, if you're doing it at your house, your room will get very hot no matter how much AC you pump in it, unless you have an industrial AC somewhere that can, like, actually push, you know, have some good CFM, but, yeah, no, a standard AC does nothing for the room, so it gets super hot. And your power bill. My wife was pretty pissed when
we got a $600 power bill one one month, and I used, you know, 3000 or 3500 kilowatts. So yeah, she wasn't too pleased with that. And I had to kind of cut down on some of the cracking activity. But it was just I was running a bunch of test modes and doing efficiency checks and yeah, so a couple things keep in mind. But that hash list is free. He has it in NTLM, MD five and SHA one. I believe it's massive. It's like 3940 gigs of hashes, just pure hashes, at least. On the NTLM set. And if you run a crack job, even with rock, you it just scrolls forever, so you have to hit cancel, wait like five minutes
for the terminal to eventually catch up. But another great way to generate a word list, because no one's done it yet and made it public. I know people who have done it, they just don't make it public because they took the time to crack it. So we're going to jump into a couple attack mode examples here. The big thing I did with this is I stuck with the rock U dictionary for, I want to say 90% of it, just to prove a point that you can use rock you to crack a ton of passwords. So like using just rock you alone. Can we see it? Yeah, we can't. Sweet. I modified these slides earlier because I was at a talk, and I
noticed the nice little video of the speaker was kind of down that bottom right corner, so I shifted my stuff up. I'm not a graphic designer. Please don't judge me on that. I just wanted you all to be able to see this. So just with rock you here on this data set. This is a corp data set with 6900 hashes. We got 300 passwords just from rock you. So last pretty hard at that one. Again. This is just using that a zero mode, but we're not feeding in a rule set yet. So this is just checking what passwords are in the list that we specified. Never. Really going to be efficient, but it's always a good check, because
it's funny, and you can be like, dummy, like, right here, I think we have Hello, 123, yeah, great. Password. I mean, password one again, I literally just cracked that for a DA who would use that? I mean, somebody clearly used it, but you can then this is primarily what you're going to, I would say use most when you're doing this, you're going to use that a zero mode, but with a rule set, right? So here I just gave it the one rule to rule them still. And here you can see, now you're getting a little more complex passwords here, and we got an additional 2700 hashes just by adding a rule set so that put us upwards
of over 3000 right, 43 43% crack. This didn't take super long to run. Total time between these two jobs, I want to say, is two minutes, and we just cracked 43% of an organization's user and service account passwords guaranteed there's an admin in there or someone that has excessive permissions that you could then leverage to do other things. We were already da at this point, so it didn't matter. But just goes to show that adding rules makes things complex. There is one setback to rules. Currently, there are no public rule sets that are updated for 2023 and beyond. So typically you see users adding 2023 exclamation point, 2024 right? Those haven't really been added to rule sets,
so you have to make your own for that, we're trying to put something together so we can get that out there and try to update some of these. But that it's very manual and slow going. I don't know if anybody makes hashtag rules, but it is. The syntax is a pain in the butt and not super easy to automate for what you want to do, trying to work on a tool for it to make our life easier, but not super easy. So you'll you will have to create custom rules at some point to add various checks. For you know, modified years like I just made one. It was 1000 rules, and it covered 2023 all the way to 2035 plus some other
rules in there. And I think I ran it through an older rule set, or one of these crack jobs, and I got an extra like 900 passwords just from doing that. So you can get it with other modes, but rule sets are going to be pretty quick. One thing that I learned, and I had no idea, was you could stack rule sets. So what is rule stacking? Rule stacking just means you can feed in Hashcat multiple rule sets, and it will say, okay, take rule set one, apply for rule one, and rule set one, apply all these additional rules to that guess, and you're creating all these extra unique guesses. This is extremely fruitful. However, it does rely on the virtual ram of your GPUs.
So you can't use, like, one rule and one rule on itself to make crazy guesses. You don't have enough memory for that. I think that alone is like you need like 90 gig 80 to 90 gigs of virtual memory for that. So it just does not work. So you want to use small to medium rule sets for rule stacking. I like to do like best 64 and inside pro mix and match, and the order does matter, because it's how the guesses are translated. So if you. Do best 64 and inside Pro, flip it around and do inside Pro and best 64 you'll generate completely different guesses and crack a ton more passwords. This in the past year has been very
fruitful. So this is definitely something to do. I would not start with it. I would start with your traditional rule sets first, and then go into the rule stack. And again, if you identify passwords, stop what you're doing. Go crack those crack those patterns. You'll get it done more, and you'll laugh again. It's all about having fun, right? As a pen tester, we like to win, and we also like to have fun. You know, take you know, it's little things in life. Sometimes I want to change people's background. I can't, because that would leave a bad impression. As the company, you know, we want them to hire us again. We, you know, as much as we want to change your
background to something great, you know, can't you always find really great passwords in here too, when you're cracking like some really good ones, most of them. I know what you're all laughing at. I know which one. Well, you find some good ones. You see a lot of I hate this place. F this job. My boss sucks. You know, all sorts of variations about that, right? Because you can tell people are disgruntled about work, but they're like, well, shoot, I need this job, man, I can't quit, but I'm gonna take my frustration out with my password. Every time I type it, it's gonna make me feel good. So here to generate this one, I use the combination attack, and I
just appended rock you with itself. This is not the most efficient crack type. So I don't recommend running it towards the beginning. This is something you do after you've run all your more efficient jobs, because you can find some unique stuff. But yeah, this one, man, oh, it doesn't say, I think this one ran for this was an hour with just rocky on itself. But again, we only got 2020, hashes. Probably not the best for us, but it's worth trying towards the end of your your crack cycle, because you can find other things. Now this is the bread and butter here, right? A six, a seven. I always start with a six, just because I like to append, not prepend, and in
this scenario, we got an extra 67 hashes, and it ran for a minute. Really cool thing you can do with this you can also add increment flag and it will go so if I did three A's, which are three ones here, I did yeah, which is just lower Digit Symbol. In this example, it'll iterate that it'll append one character, run that crack job, then it'll go to two characters. Run that crack job, go to three characters. So it's it's really good. You really especially with people with numbers and symbols. Man, always put them at the end of their password. You crack so much extra stuff this way, just a little rule set. Here, you can
see it didn't do us that well, this mode does not support rules. So you cannot feed it a rule set, like one rule or whatever it just it does not support that. There are ways around it, which I'll talk about later. A seven Same thing here. We're just prepending. Grabbed an extra 16 hashes on the data set. Typically, if you're going to do it and you're not going to run all characters you want to do upper lower symbol are usually the most common at the start of a password. And now please pray for me. We're gonna see what happens. We're gonna we're gonna do it live. We're gonna do it live. I hope it works. So this is just a simple brute force attack, right? We're
going from three to five characters. I made a test hash list just so you guys kind of see it. Please work. Okay, sweet. So this is on my my m1 mag. It's not the fastest, but you can see we're getting getting passwords that I had written just for this test. I do have Corp data set, but they do not have terrible passwords like this. So it's just quick little, little thing there, and where's my mails get out of here. Found it all right, yeah, sweet. Oh, ignore that. That was my backup plan in case it failed.
So is there any significance to these passwords on the screen? Number. Yeah, they have numbers at the end, and sorry, it's super blurry. I tried that screenshot like six times, and still super blurry. But yeah, you're right. So there's a bunch of numbers at the end, and you can see there's two to three characters at the start of it. It's a common pattern. That's what I'm talking about. When you're cracking and you see things like that, it's always good note to write those down or copy them out into a notepad. I usually do that. I have a running list, and I just start making masks. So they're common combinations that we can then run through that brute force
crack mode to get a bunch of passwords. So this is how I got 90 plus percent on that one client in 10 minutes is finding things like this that you just go, oh, that kind of looks like a start date for the employee. Oh, that might be their first initials, or first initial last name or something, right? And it's just, it's wild. So with that, we can create masks. Forgot about the video on this one, but this is like what a traditional mask looks like, right? So we did the all the A's, which is every character, upper, lower Digit Symbol. This we're saying, Hey, start with an upper, then do a lower. Follow that by six to eight digits, and it will try every combination of
that. So let's see. We're gonna try it again. We're gonna try it again. I'm just gonna get it ready over here first, since I can't see behind me, alright? So I put these in a mask file already. So we got crack type. I'm just doing a pot file path because I don't want it to overwrite my good pot file, not that I have one on here. Hash list. We're doing a three so instead of feeding it those masks one by one, you can put them in a file. Can be a text file. I do HC mask because that's what Hashcat does. Hashcat mask file is what it stands for. And then you just run it, and it will iterate over
each mask in that file and attempt to crack. So right there we got three, three the hashes out of the 20 something or 30 in my in my pop file. And then it moves on to the next one, which I know there's none, so I'm just going to go ahead and skip it for brevity. And then it moves on to the third attempt. So you can see guest queue here tells you what mask it's on, and then it above it shows you what mask we're running. And then we can see it's two hours long, because, again, this is my MacBook. It's not a GP crack, you know. But look, we can go ahead and we can still get a hash out of it, right? This.
This actually works really well on Corp data sets. So I've been compiling these for months and months and months. Have a really nice mask list. Does run for several days, unfortunately, but, you know, I'll throw it on like four GPUs and just let it do its thing, and it ends up cracking me a ton of hashes. So all in all, masks are the way to go, but it does require you to analyze those cracked passwords, develop what masks, and then you got to test them with your specific hardware, and then go, Okay, how long is this hash run for? Oh, this runs for five minutes. Okay, let me log that. So I've been making like a
spreadsheet. I need to find a better way to do it, but a spreadsheet that shows this mask runs for this long on eight GPUs, just so I have, like, a base timeline, and then can be like, Okay, maybe I'll skip that one today, whatever, because it runs long. And then I actually have them in order by time, because a lot of them just crack in five minutes or less, and they net us a ton of stuff. Ignore that. That's me being cautious again. Take those cracked passwords you had, put them in a word list, run them through with rule sets. You'll crack additional passwords. So like here we had, I saw good for you in one of the other slides. This one found good for you a
bunch of numbers, extra symbols, right? Because it's applying all those extra rules. Sometimes you'll get things that say dollar hex bracket and then hex code. You will have to convert those. Typically, it's because they have symbols that will break parsing tools. So things like semi colons, colons, couple other symbols like that, we'll go ahead and break tools. So Hashcat just puts it in hex mode, calls out that it's hex, and you have to manually convert that, or have script that does it. There are some of those out there. Now, as I mentioned, some of these word these modes do not accept rule files, right? So A, one, A, six, a, seven and brute force modes do not allow you to
specify rules. One thing you can do is feed Hashcat into itself and read from the standard in and apply rule sets on the second instance of Hashcat. So take the first Hashcat, right, which we can see here. D just means, what devices Am I using? I'm using all eight. Right here we're doing a one. So we're taking rocky we're comparing rock u with itself, writing all those guesses to standard out pi. Tweaking that into another instance of Hashcat, pointing it at our hash file, and then giving it a rule file. Downside to this, it adds a lot of time to your cracking. So do this towards the end of your crack cycles, and you get no notification on how long this
will run for, because Hashcat has no clue. It has no idea how big that list is coming from the first instance of Hashcat. So it's like, yeah, it'll be done, sure. So in this scenario, I ran this thing for four hours, and I got two extra hashes, right, but it found waters. 12345, 6% when you know it otherwise might not have. Could have found that with a rule set and some of some other stuff. But you know this is just to show you that this is possible. Again, can do it with a six and a seven or even brute force. Again, very, very slow runs forever. This one, I ran for almost three days straight, what I get 81 hashes cracked,
right? But it was just interesting, because I'm getting, you know, things with extra symbols that I probably would not have guessed. And then you got, like, Blue Horse pen. That's someone trying to follow xkcds, battery horse staple. But yeah, it's it's cool. This was a nice shout out from the Hashcat team there for showing me that you can actually feed through standard in or standard out into standard in. But also really useful for generating your own lists if you need them, for various things like password spraying if you have a list of surnames, really great way to do some simple stuff without having to write Python code. Just saves time. That's what we're all about here. So again, special thanks to Hashcat team. We got
Adam for one creating it chicken man for being my sounding board every other day, and just generally, being a good dude and sharing knowledge, because he wants to see the, you know, cracking community get bigger, see more people participate in crack me, if you can, and if people can, you know, if you're if you're good at coding, definitely always looking for more people to help fix some of the hash modes. Implement new hash modes. I'm still fighting with them to get them to add PFS support, because right now, the only tool that does it is John the Ripper to crack a PFX certificate. So when you find a nice PFX in a share that's password protected and you don't
crack it right away, it's pretty slow on John the Ripper. But again, thanks to John the Ripper for maintaining all these wonderful tools for zip to John PFS, to John, so on, so forth. So I'll open it up for Q and A, if anybody has any Yes, right here in the green. So a bunch of questions. Unknown: But this one is, when you present this to a Print test plot, they say, Bucha very much or something. And they're like, cool. We did that. I thought it was strong. What's the package you craft? What's wrong complication or things etc, like, is this a lost
Jon Milkins: battle? No, actually, that's a great question. I had a client recently that actually had a very robust password list. We cracked less than 20% of their passwords. Big thing is Microsoft, entre Azure, whatever you want to call it, released a password auditing tool that you can deploy both either on prem or in the cloud, where you can put in a loud list or a block list. So you can block list, seasons, company name, sports teams, locations of businesses, and that's been extremely helpful. So we always recommend that they implement something like that so that users can't make terrible passwords and they get denied by that tool. So that's probably the biggest change they can make. And then,
other than that, it's really just educating users, which is extremely difficult. Yes, all right. Blue shirt when creating Unknown: your own word lists, have you found that business verticals or regional correlations occur, or the better, like social graph type correlations, Jon Milkins: if you're targeting them, I have in recent months seen regional winning out. Mainly people are and I'm gonna, I'm gonna, if anyone's from Texas, I'm sorry, but Texas is the worst about it, because they always put Texas, Dallas, Houston, and then they put all their sports teams, cowboys, rockets, whatever, every single time, and you crack so many passwords, because they always do things that are local to that region. But other clients, like I've done, banking clients, and
they traditionally are a bit more secure, and they force them to use and get out of those habits and use stronger powers. Words, yes, right here in the black from Unknown: the sounds of it sounds like you guys are using one box. Have you sort of experimented with tools like our hash, Top list, or something like that, to like distribute workloads across them? Or is most of your stuff smaller scale? Because I know some of your recommendations were keep it small to start with, and they can get can get bigger. I'm guessing hash topless. Hash Jon Milkins: topless is a great hash. Topless is a great solution. We're not using it currently because our box is
Windows based, because they decided to build a Windows box, for some reason, that was not my choice. But hash topless is great. I highly recommend it if you can distribute that workload. And yeah, so running out of time here, definitely available after this. If you have questions, just come find me. I'll be up, up walking around, definitely open to talk. But thank you all for coming. I appreciate it. And as Michael Scott says, we'll catch you on the Flippity flip you