Application Architecture from a Hacker's Perspective
Show original YouTube description
Show transcript [en]
hi everyone i hope everyone is safe and sound our talk for today is about application architecture from hacker's perspective today's roadmap for our talk is what is application architecture why security architecture is important what is security analysis why application architecture review should be taken care of when developing an application now what is application architecture the principles and procedures used to design and create an application are referred to as application architecture when designing an application the architecture provides a roadmap and best practices to follow that you end up with a well structured application software design patterns can assist you in the development of an application now what is a pattern a pattern is a repeatable solution to a problem
to create more general application architectures patterns can be linked together instead of totally designing the architecture from scratch you may leverage pre-existing design patterns to ensure that everything works as it should there will be front end and back end services in an application architecture front end development is focused with the application's user experience while the back-end development is concerned with giving access to applications data services and other existing systems that are available uh the architecture serves as a starting point or roadmap for developing an application but you will have to make implementations decisions that are uh that aren't covered by the design for example choosing an application a programming language in which the application should be
developed is the first step now for software development a variety of programming languages are available certain programming languages can be used to create specific sorts of applications for example java is widely used for developing android applications there are a number of application architectures available but that is beyond the scope of this talk i will do briefly explain about the three tyre architecture which is quite popular and is wide used widely a well-known software application architecture that organizes applications um is the three tyre architecture and the name also points that it has three tires which includes presentation entire that we users see and interact within the browser while there is a popular tire while there is an application there are
also known as logic tire where the application server or the web server core business processes are defined and data is processed accordingly and how various components interact with each other in the third uh one is the data card which where the data associated with the application is stored and managed each application tile has its own benefits uh that all depends on your needs and how you utilize them the logical and the physical separation of functions is the main advantage of three tyre design each layer can run on its own server platform and operating system for example there is a web server and the application server or the database server so each tire also runs on at least one dedicated or a virtual
server allowing each uh layer services to be changed and optimized uh without affecting the other tyres so it has also uh benefits of uh there are benefits of three tyre architecture as compared to the single or the double uh two tire architectures for example there is a faster development uh that means that each tyre uh can be developed separately or simultaneously by different teams it has improved uh reliability uh an outage in one layer is less likely to affect the other levels availability or layers availability or performance and it has scalability that means that any tyre can be scaled or upgraded independently as of need and also it has the improved security for example the
presentation tire and the data tyre uh cannot communicate directly uh there is us there is a application entire between uh the presentation and the data type so uh so both of them cannot interact directly with with each other that means that application tire is acting as internal firewall between the presentation and the data attire okay why security architecture is important do we need to take care of it well uh software architects put a lot of efforts while considering application architectures for their businesses it is a really really important at the same time to examine the security issues that might arise during or after the product is developed considering information security while uh creating architecture for your product enables you to achieve
core business objectives this will help you to make your business processes more transparent and accountable such that no interruption would be observed one of the most important thing is to make your business more secure this way you will bring down the security incidents and bridges to very least and of course you will make your business and processes uh complying to the national and international uh regulations and security standards and of course the id team and the security investigators would collaborate more efficiently and at the meantime the security posture of your organization would be more i think clearer than before each year information security service providers share their threat intelligence reports verizon is one of the leading service
provider in them they have shared their 2021 data breach investigation report that describes that 80 percent of the attacks are related to web applications along with system intrusions and other various errors resulting in the security incidents so how do we anticipate the web applications we are using on daily basis aren't fallen to cyber incidents and the data of people they might have saved on their data stores isn't bridged so on a serious note software architects and the developers need to focus heavily on building the products for different businesses that is when the application analysis come into play so that the security guys and the developers should think of the necessary security controls uh if they
have left unintentionally during the billing of a product or lag somewhere the concern team needs to find out so it is very important to analyze the application uh and find the security weaknesses uh before uh uh before uh taking the product to live production environment where the where it should be freely available to the people including the bad guys who might leverage the security vulnerabilities left behind in the product somewhere that are uh that if they are fortunate to find out so such activities can result in reputational loss as the customers of the particular business can doubt on the intentions and mistrust the product so according to the statistics available um available over the internet it is found
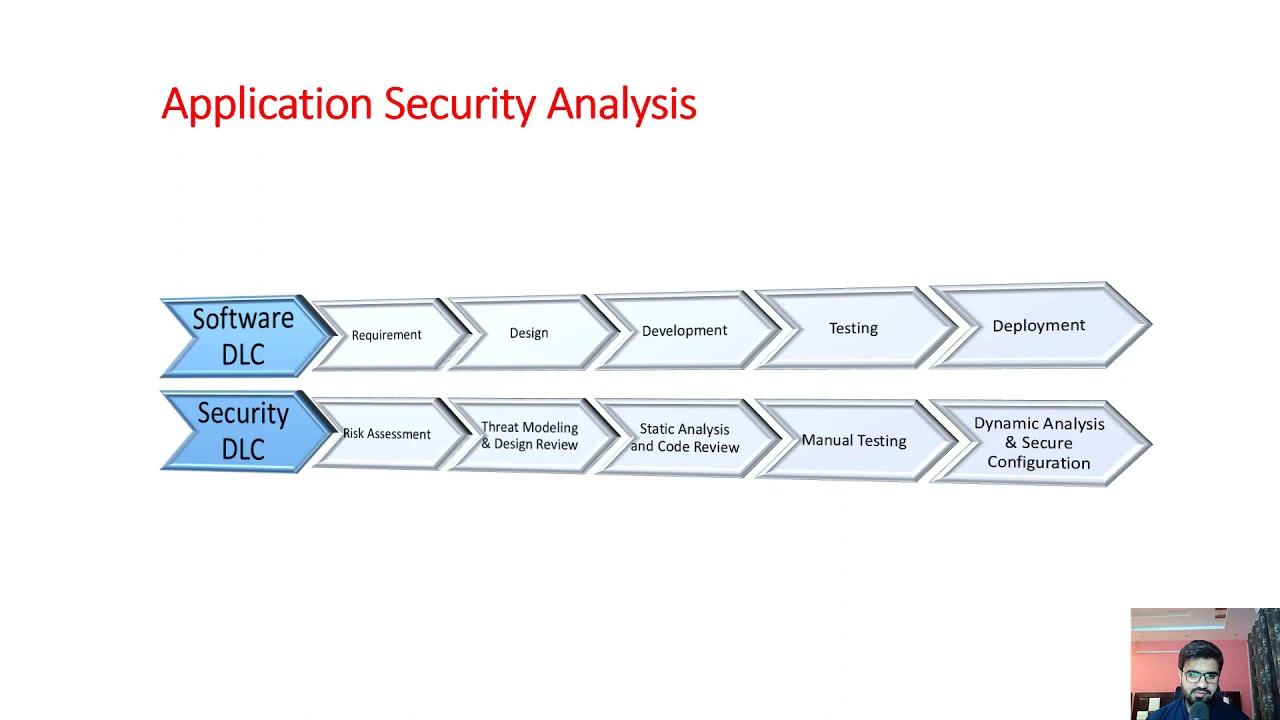
that 50 50 of the security issues that are found during various uh uh security assessments by internal or external uh teams are related to code effects uh that are primarily uh discovered while uh when analyzing the product through the static assessment so you see here different steps of software development life cycle that are mapped against the security development life cycle stages or steps there is a risk assessment activity in security development life cycle which is a process to identify the security hazards that is carried out during compiling requirements for the product and in the design phase potential security threats are identified in the threat modeling phase uh whereas during the development the penetration testing team conducts the static
analysis and the code reviews through manual and automated approach whereas during a user acceptance testing which is known as uet manual testing of the application is done to ensure no security loopholes are left behind after the uat the product is taken to production environment where the dynamic analysis of the product is happen to discover if the data isn't leaked and everything is working perfectly secure as intended along with this uh they inspect if the configurations that they have done are flawless and couldn't be leveraged for malicious purposes as of now i have discussed application architecture an example of application architecture why security architecture is important a data breach investigation report and common hackways of web applications uh
together with some statistics a working comparison of uh software development lifecycle and security development lifecycle and how different activities are managed and teams collaborate simultaneously so now it's time to explore the key areas of application where security immensely needs to be incorporated following are some of the areas listed below which we will discuss in detail let's move forward to application architecture documents and re design so the name sounds quite descriptive but this area needs to be handled very seriously that is if the security controls or the roles of the users the privileges the business processes with respect to information security are defined correctly i believe the developers would do a great job to restrict or enter the security breaches
so what needs to be done is that the application design review practices should be defined the components should be identified a high level architecture for the application within the workflow diagram of application should be produced verified that the application components are uh defined in terms of business functions and also security functions they provide so in the last but not the least security features should be addressed in the documents which will help the developers and the security guys to investigate or to find what security controls are initially implemented in the product so there comes threat modeling in order to uh think like a hacker who actually finds the security weaknesses in the critical assets of an
organization we also need to follow the footsteps or the approach uh and investigate about the possible uh potential security vulnerabilities that might be leveraged uh at any stage by the hackers so there comes uh threat modeling which uh which identifies the many forms of threat agents that can affect a computer application or system so we need to put ourselves in the shoes of a hacker uh to see how much harm we could uh possibly cause uh of course we will uh be doing it ethically that means that we we have to carry out these activities with the permissions of the management and should bring this to the notice of the higher management for finding the
security vulnerabilities and conducting these kind of activities before the hackers do so therefore organization make a detailed investigation of the software uh architecture the business environment while conducting uh threat modeling uh so it's typically done at the design stage but i think it can be happen at any stage of a new application to assist developers in identifying the security vulnerabilities and sharing those security vulnerabilities with the developers in order to fix them at the earliest uh this activity will help us to verify that the threat model for the target application has been produced and covers of risk associated with spoofing tempering rapidation information disclosure daniel of service and elevation of the privileges deployment and infrastructure
consideration this area discusses the development and deployment environment the operating systems the user handling the complete infrastructure so with respect to rolling the information security in this field we need to figure out what restrictions does the infrastructure security impose and how to work around what security protocols are addressed how things are communicating are the system updated against the public disclosed vulnerabilities and when was the security updates installed on the system uh who has the authority to interact with this machines input validation the application must ensure that only logically valid data can be entered at the front end as well as the directly to the server side of application of a system what hackers do is they abuse the
security controls implemented on the front and also known as the client side for ease and saving time to take application into the production what developers do is that they only put weekend security checks on the client side so in turn in return the hackers bypasses the client side security controls and do whatever the use case they have in their mind for leveraging the weakness and gaining a personal benefit so this is why the penetration testing activities are conducted by the large organizations in order to find the weaknesses because they cannot bear the loss for example in case of e-commerce website hackers can temper the price or the quantity of the product while buying a product so this should be handed
acutely since uh i am running out of time i have to quickly walk over the slides and conclude within given time okay so the difference between the two is that authentication is the process of uh verifying that a user is who really uh claimed to be uh whereas authorization involves verifying whether a user is allowed to do some something the impact of authentication vulnerabilities can be very severe once an attacker has either bypassed authentication or has brute force into a user's account they have access to all the data and the functionality that the compromised account has so if they are capable of compromising a high level i mean high privileged account such as system administrator they could take
control of the entire system and potentially guild gain access to the internal infrastructure even compromising a low privileged account might give them a lot of information session management in most of the online applications the session management method uh is critical uh it's a critical security component session management techniques are a popular target for for malicious attacks against the application because of their critical uh functionality so if an attacker can breach in application session management they can effectively bypass the application authentication protections and impersonate as another uh user without knowing their credentials so if an attacker gains a control of administrator user in this method in this way the attacker will have the complete control over the application
access control or authorization is the restriction on who can conduct a particular activities or access resources since we have discussed authentication and session management access control is heavily dependent on them so hackers commonly abuse access control implementations in order to elevate their privileges i have just pointed out that they [Music]
access control or authorization is the restriction on who can conduct particular activities or access resources since we have discussed the authentication and session management access control is dependent on them hackers commonly abuse access control implementation in order to elevate their privileges i will just point out that there is a horizontal and vertical privilege escalation which hackers obtain for carrying out malicious activities so developer needs uh to put role-based segregation such that uh sensitive information should be accessible to authorize users only here we have configuration management infrastructure team needs to implement patch management practices and follow the security policies that should be developed in the application architecture documents and design make sure uh that the security
controls for example encryption on communication is in use and the application components are up to date cryptography is used in order to protect the sensitive information from being exposed to unauthorized people but hackers still tend to bypass this in a way that we can procedures are implemented for example most of the times developers hard code the cryptographic keys in the source code in the case of android applications they hard code the application cryptographic keys in the source code exception handling improper handling error handling can cause a range of security issues for a website the most typical issue is when the user sees a comprehensive internal error message such as error codes stack traces database terms
exposing the user names or any sort of sensitive information these notifications expose facts about the implementation that should never be revealed such facts might provide hackers valuable information about the site's possible weaknesses auditing and logging this helps a lot in incident response when a security incident occurs each suspicious activity is recorded and provides juicy information while tracking the incidents so this is why the hackers have to mask their ips while conducting the malicious activities make sure that unauthorized users do not have access to these critical systems thank you everyone please drop your questions i will do my best to answer them