Gabriel Bassett - The 2019 Data Breach Investigations Report
Show transcript [en]
hi folks hi okay so I'm Gabriel Bassett I'm one of the co-authors for the 2019 Dvir who here knows what the report is like okay who's who's read it cover-to-cover yeah who skin the pictures yeah there's the high point in the curve you know who's like read the headlines and knows that stuff like yeah and we understand that and that's why we put so much effort into the patience I particularly like that because I'm the one who does most of the figures so if there's figures you liked you can thank me for them if there are figures that are incredibly weird I'll apologize for those later in the talk but I'm not the only author these
are the other four authors and so there are lots of people at Verizon they claim to be dbi are authors there are very few actual authors Dave Highlander Suzanne white up mark Spitler who led the team and Alex Penn - who's taken it over where the authors for this year's report and then we're adding filling wah to the team as well for the 2020 report and so by the way I'm going to talk to a couple of lists of cool things things to fix things to pay attention to this link goes to a presentation that has those things listed out cuz I'm not gonna put them in the charts like I said I do figures and so I've got lots of pictures
and lots of bar graphs and things like that on my charts and no list of texts and so if you want list of texts which I always like list of texts take a picture of this I'll come back to it later it'll be at the end of the talk while we're taking questions so if you miss it when I switch off of it here in a second it's not a big deal and so what the DVR is we all kind of heard about but just to repeat from like a decade ago when we looked at Dean about security a lot of times was anecdotal whatever the most recent breach was everyone went out and tried to go fix that problem as if that
problem was everyone's problem and a couple of guys Dave Wade Peter tippet said you know what let's go and look at a set of data and like do some actual analysis around this and come up with a data in report and since then we've continued to add authors add contributors add data and with the main goal of reducing bias and improving context in our report but always is data-driven as possible you know we want to be able to tell people what the normal organization should see and how that they can react to it and what they can do about it and so to get a couple of things out of the way first one the majority of
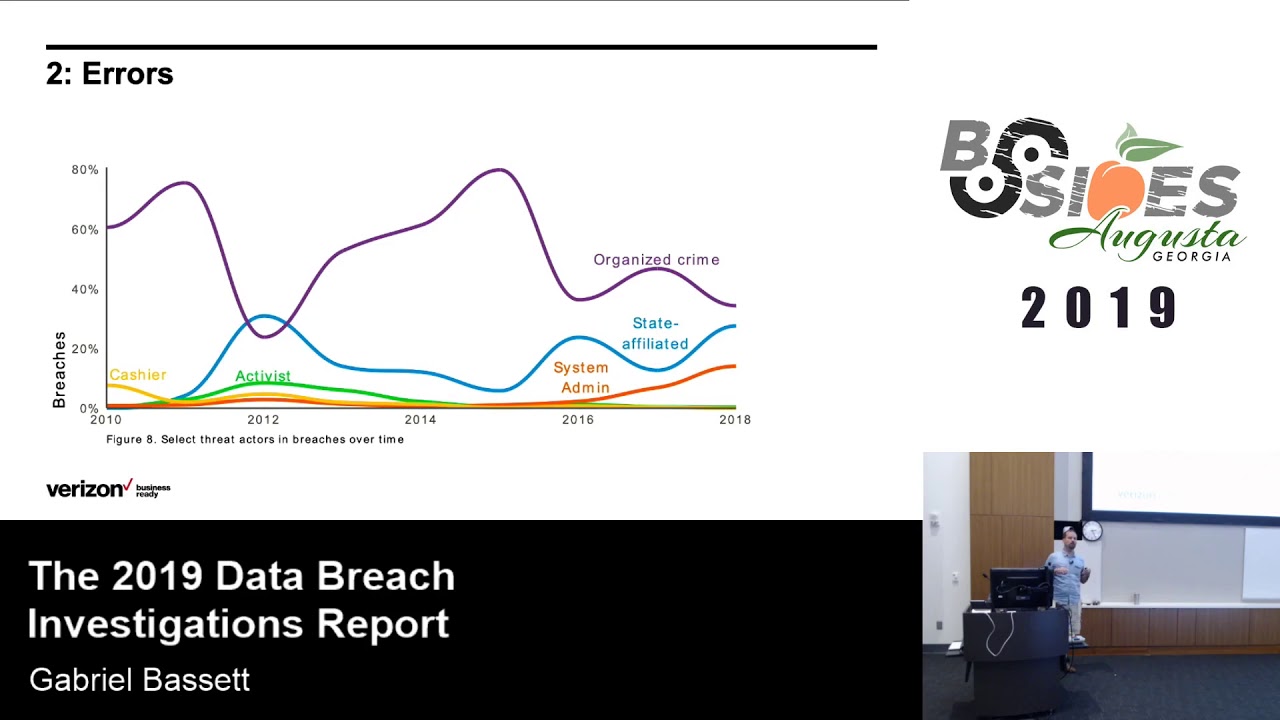
breaches are externally motivated the actress are almost always external and this is because we always hear like oh it's an insider you got to worry about the insider and things like that and that's not what the data says in fact the reason internal is going up is not because insiders are all evil people it's because we've started actually reporting when people make errors internally these are errors these are mistakes they're not malicious and so the reality is the majority what you have to worry about is external the other one is espionage versus financially motivated most people we'd love to hear about espionage voted espionage motivated breaches right because they're so cool and they're exciting and they do fancy things and
the reality is they're not that much mmm they're a very small percentage or about 25% of breaches the vast majority are financially motivated the attackers that are coming after you are more than likely financially motivated and this is incredibly important if you take nothing else away from this presentation this is what I want you to take away is that most threat actors want not nothing just the easy they won't the easiest way and this is important for you because this means that you don't have to be perfect you just have to be a little better than worst because those guys are financially motivated and all they need to do like they want to get the greatest return on
their investment and if they want that return on investment they can't be spending a lot and so they're going to take the absolute easiest way to get it and in reality is that's 85% of breaches and so let's talk about the four horsemen and breaches they are patching errors social attacks from credentials and we'll talk about each of these individually starting with patchy and when I say patching I don't mean like your normal like trying to get everything perfectly I mean like try to patch that thing that's facing the internet and is 10 years old like where the bar is low it's really not that high because the attackers are not going after that advanced stuff necessarily not in bulk
they're going after the obvious stuff and so what this is it's the rank ratio of honeypot data to Internet scan data and so what we're talking about is telnet is the number one most common port for attackers to hit on honey pots it is only the 15th most likely port to be on the Internet and so these are the highest ratios and if you look at these these are obvious things like these are vulnerabilities but they're not like last year's one durability so the last decades vulnerabilities and so these are the things you need to patch you need to like it'd be nice if we all got everything patched every week could be it'd be good if we got it past every
month but like if you can get things passed after a couple years or maybe just like throw a firewall on it that'd be great like that would actually do something about the attackers but to be able to do that is not just about patching it's also about asset management you need to know what assets you have facing the internet so you need to have discover and I think a lot of times for the people in this room who are probably already patching at least something that's probably the big part is understanding what you have now the next part are heirs so who here is spending a portion of their security budget to fix errors and to mitigate
errors that's like a few that's it that wasn't even like the number right that's like just a few hands kind of who's spending 20% of their security budget to fix errors yeah no one right we might be spending twenty percent of our security budget to fix vulnerabilities but certainly not heirs and vulnerabilities in the DB I our lead to it most six percent of the breaches let that sink in versus 21 percent for errors errors lead to a lot of breaches and so system admin down here is trending up as an actor the reason the system admin is training up as an admins make mistakes and they're the ones that get blamed when cloud storage is left on the internet and is
exposed or when databases are exposed to the Internet and become breaches and as not that we're getting worse it errors what it is is that we're now actually talking about them and we've known this for a while because in the DB IR if you look at the public sector and healthcare who have mandatory reporting requirements always report really high percentages of errors just now the standard has become that when you go in as a security researcher if you find you know that that database sitting on the internet you go tell the company and then you go tell a news organization it gets published publicly and when it gets published publicly we can put it into
our data set we can find it easily and so because of that it's trending up as a report but the reality is airs are happening a lot and so the question is what are you gonna do about it and so a plan needs to be to fail gracefully I'm gonna after this talk I needed to drive back to Nashville and on the drive back if my tire springs a leak I don't expect my car to explode but that happens right we have a breach and all of a sudden like some minor thing didn't get configured right and becomes this big breach of tens or millions of records it's ridiculous so we need to go and
look at the data we have inside our organization say what would happen if this data was breached is this data that we become a significant issue if some air exposed and then we need to look at the people and the processes and the systems to touch it because the reality is no and I try to get this through every single presentation I do know people know processes those systems know security tools are perfect nothing you deal with is perfect so you need to plan for it to fail for it not to work the way you expect and it's necessary to prepare for that and it's okay it's natural it's normal but you need to be
prepared for those failures and so that means understanding how the systems will fail to touch our data and when they do fail having a plan and you don't have to develop this on your own process improvement has been around for a long time we just don't do a good job of applying it to security and so go look at those process improvement systems that are already in place and see how you can apply them to your security processes that deal with data that way all that spinning you're doing on vulnerabilities doesn't get wasted when someone accidentally puts the database on the internet and that becomes your breach excuse me okay now let's move on to the fun stuff
social engineering social attacks and we're going to talk about this in two slides social tasks kind of come in two different flavors the first will be financially motivated social engineering attacks and this is my favorite quote from the entire report this year was it you have to hand it to the attackers at some point one must have thought you know why don't we just skip all the whole all the hard hacking stuff and you know just ask for the money and it works in fact we started to call these business email compromises in the report and then we started con decided we had to call them financially motivated social engineering attacks because you don't actually have to breach an email
address you literally can email from an external address and say hey will you give me money I promise you I'm the CFO and you're like sure whatever it happens and it happens so much and you know why are executives the ones that are targeted executives are the ones that can transfer money easily and I sympathize with this just right it's like ah no one would ever send money around and then like we're getting ready for b-sides Las Vegas and I'm the CFO for a non-profit and the CEO goes hey you know I had this other guy print out some stickers for me I need you to send him a bit of some money to reimburse him
I'm like okay like I gotta end up in my own data set when I do this you know because I'm doing the same thing and I completely understand where it comes from but the reality is you need to be prepared to handle these types of situations because it's not even a large breach that causes a lot of large amount of money that normally gets transferred and we'll talk about this a little bit later but it's like 24,000 is the median and so you may have a process for dealing with that transfer of a hundred thousand dollars or a million dollars but do you have a process for that 24 thousand because that's the one that
normally happens and second is social attacks and so if financially motivated social engineering is the nice quick one phishing is the very common one and the reality is we're getting better at clicking stuff this is phishing testing data so in these city officials coming down but still we're hovering around percent or more breaches involving fishing and you can wonder how in the world does this happen but a good example is my wife over Labor Day was we're at it my brother-in-law's cabin on the lake so she's down on this really nice dock that goes out of ways and she's fishing but she's fishing along the shoreline and now I'll bet this is a big lake out in the middle of that Lake
I'll bet there's a bunch of big nice fish like ones you really be proud of in fact it may be that 75 or 97 percent of the fish are out in the middle of the lake but right up there along the bank there's more than enough bluegill to keep her happy for the entire day and that's the reality for fishing right even though the majority of people may be out in the middle of the lake there's certainly enough people along the bank to keep the people that are attacking happy and so what can you do about this well for financially motivated social engineering or business email compromises you need to have a process for having an out-of-band method for
confirming money transfers and any money transfer that goes beyond what you're willing to lose because right the normal the median breach is not high and for fishing there's a lot we can do we know that the majority of breaches to come by fishing they come as links in emails executable attachments or macro enabled office documents so filter those things when coming through your email like I mean some people get links but like we're pretty we're starting to get better trained about doing that we shouldn't get links by email second none of us are getting our Windows updates by email like no one emails you the executable windows dot exe you're like this is a good idea in
macro enabled office documents there's probably someone in your company who needs to use them but find that person let them do it and no one else needs to be using it have a process and then give people way to report because the reality is that the majority of reports of phishing emails are gonna come in in the first hour but only a third of the clicks then the next third come in over the over the day and then the next third come in over the week and so potentially if you're acting on the reported phishing you can stop two-thirds are the phishing emails from getting through I set people up for success right because is IT people it's very easy for
us to say I can't believe those people click links in their emails I I would never open that attachment you know the reason is because no one sends you a PDF blindly like if I get a PDF blindly I don't open it because that's not something people do to me on the other hand if you're in public relations and someone says hey we're running this story about your organization next week would you like to comment you're opening that PDF right away if you're in the legal department you're gonna open that attachment you need people in your organization need to be able to open attachments and so set them up for success for those portions of the organization they probably don't
need a normal full laptop you know give them a sandboxed operating system on a tablet or something so that they can open attachments and such without feeling the stress of whether they're going to be seeing the security people will show up at their door the next day because they're gonna do it anyway you know set them up for success and then finally the fourth tip okay do we remember what the other three were what's the first one who said it first okay I have gifts you pass this back to him Thanks now have questions later on they'll get goes from but what's the second one there's good what was the third one great in credentials is the
fourth and the biggest 29% of breaches started with credentials who here knows what credential stuffing is yeah Matt credential stuffing is when the attackers take a big body of credentials and they try them against everything in fact like a couple years ago they found like 5 billion credentials on some foreign file server that we're being used for this and they try and against everything they try Mia's financial institutions against retail sites against like your cloud email or your cloud infrastructure and again it gets here directly against your organization and they work they get the attackers in and this goes back to that financial problems too if I'm saying I want to go make money being a hacker and so what I'm going to
do is I'm going to go buy some credentials I'm going to log in to whoever that organization is and whatever that logging directly gives me access to I'm gonna go monetize if it's personal information I'm gonna go use their credit to go buy things and sell it for money if it's medical information I'm going to commit medical fraud if it's payroll information I'm gonna go kit commit tax fraud most of these things can be monetized pretty directly if it's access I can drop ransomware and so credentials are extremely common and letting the attackers in and so what we need to do about them is well two-factor authentication so one of my people I was doing an interview for this Dvir like
we're chatting you know before the podcast starts up and he goes you know the DVR is kind of an ad for two-factor authentication isn't it and I'm like yes it very much is because it's one of those things is very very important because credentials are so important but I say that knowing that is not easy like it's easy to say all these things we should be doing or that our organizations should be doing as if like you just you know snap your fingers and it happens in reality if you're small organization maybe yeah you can turn on two-factor authentication on the cloud service but then you have to worry about maybe it didn't get applied to the
legacy services you know I math and pop3 and so you gotta check that out and I know you turned it on in your organization not particularly IT savvy and so now you have to reset everyone's two-factor authentication every week and this is on top of all the other things you do as an IT person within a small organization and it's a big burden if you're in a large organization yeah maybe you have dedicated resources for it but now you have to go gee does anyone really remember how the VPN concatenate er works cause like some guys set that up like 10 years ago and no one's touched it since then and we've got this huge complex single
sign-on that this has to work with you know and on top of that we've got all the other infrastructure it's it's hard all of these things are hard work within our organizations and so it's important then that we dedicate the resources to the things happen most often these four things before horseman and that we then go and look at the other things and that we also appreciate the people who do them and understand how much effort they are putting in to make the security work so that we don't just say hey yeah turn on two-factor authentication oh yeah sure that happens just magically additionally for passwords there's a couple other things we can do in our
organization's encourage password management encourage people to use password managers right because it's its password reuse it is leading to this and so when people use password managers they don't reuse her passwords as much also have a same password policy right this now has pretty reasonable recommendations don't be the organization that requires people to change their password so here it is this is my corporate iPad iPhone I just got it recently and I put a good password on it and then after three months it asked me to change it the pin on my iPhone my iPhone pin is now 20 1901 ish something like that and the next one's gonna be 20 1902 it is no longer a good pin because
I am not willing to come up with a good pin every three months your employees are the same way set them up for success finally you can look at services that provide access to existing passwords password dumps so that you can look to see if passwords are in a breach the attackers are using the same sources of dump data as we are and so if you can go look to see if your passwords haven't breached that's an opportunity to clean up potentially compromised passwords in your environment so and by the way that was to 85% right which obviously leaves the other 15% the advanced attacks the ones that are fun to talk about and they
follow we're gonna talk about a benefit but not a lot because they follow kind of a standard process they're normally external motivated by espionage they follow this kind of chain of social attacks leading a malware leading to hacking leading the compromise of internal information or secrets the interesting thing in that though is that they're starting in the same place they're starting with social attacks and more so social than credentials because if you're committing a advanced attack particularly a targeted attack we're gonna want to do is you're gonna want to target a specific organization and you're not gonna get that by just buying bulk credentials and so the next easiest thing is phishing the attackers are the advanced attackers are just like
every other attacker they want to find the easiest way to get their job done and then go home and you know barbecue they're gonna follow the same process they're not using some crazy way to get in the majority of the time particularly when something like phishing works so I told you I would apologize for these charts here this is where I only kind of do it it's like one of those like half apologies like I'm sorry I didn't do as good a job explaining this as I could have but I am gonna try to explain this here so the way you read these charts these are the steps and in tactics and so every path through here is a breach
and you don't read this the way you would read a book you read it kind of more like artwork and that each of these is like a story of an individual breach and what you want to do is not just get the individual stories you want to get the overarching theme the narrative and what we're looking at is the number of steps that the attack took from starting here to the end of the attack right here at 0 steps we had one that was 14 steps one that was twelve and the maturity or short attacks we'll talk about that later they all start the lines I'll start at the actions so you see all the
brown ones up here start at the same spot those are all those attacks that started with social these down here attacks it started with air and see they're all short and then it bounces back and forth between the attribute compromised and so this one was a hacking attack that compromised integrity followed by confidentiality excuse me confidentiality and then integrity and then malware and it bounces back and forth this one started with the social attack compromising integrity and then compromising confidentiality and confidentiality again you get the point now I want to look at the most common attacks in the long pass first these are the 15% of advanced attacks and one of the things we see kind of the narrative
is that there's a lot of hacking a lot of malware in here and a lot of them start with social but they're the long social and so these are the attacks that started with phishing and a social attack that led to then hacking and malware being dropped in that advanced attack and this is be the first but I nearly got caught there this is gonna be a first of our defensive opportunities around paths so the first defense of opportunity around paths is to pick where you want to meet the attacker and this is nice right because if you stop thinking about breaches it's like a point in time and you start thinking about the steps you can start saying
where do I want to address this attacker I think they kind of talk about something like this in the keynote a little bit you know you don't have the attacker takes steps and we've all heard the saying you know the attacker has to be right once we have to be right all the time and then the corollary to that obviously the attacker has to complete every one four steps correctly we only have to stop one of their steps and so you can say you know maybe I want to stop that first phishing attack or maybe I want to stop the Mauer internally or maybe I want to stop that hacking actions they pivot internally or maybe I
want to try to address them in all these places or maybe I want to address this this data leaves you can start picking where you want to stop the attack if you think in terms of paths now on the other side when you look at the short paths we start to see the things that we talked about before right there's a lot of error you look at the brown ones down here there's a lot of social and misuse and the social here like the financially motivated social engineering attacks and a lot of hacking and this is use of stolen credentials and so we see a lot of that as well as physical attacks that normally are short as well and this kind
of brings us to the second point about paths we see that the attackers like short paths the majority of attacks are one or two or three steps and the reason they like that is because when it starts to get out to five steps or ten or fifteen steps the attack is a lot less likely to succeed this is breach data and this is simulated breach data from a company that emulates witches and so this brings us to our second point try to lengthen the attack path for the attackers ad steps so who here was at Derby Con this year a few people was anyone at they liked the Laser grid thing that they were jumping through no
did anyone see the pictures of people jumping through the Laser grid yeah there we go so they had liked the competition and they had this Laser grid and they've got some really good pictures of like these big dudes like diving through the lasers but you can think about that it's another step in the path the attackers had to take and even in that weird kind of silly situation I think they said that maybe half a people failed to get through it and so you know what would it take for you from a control standpoint to filter out half of all attacks that sounds like a pretty good deal particularly if it's even a simple control and I mean that's half right
look at something like two-factor authentication where you know none of us believe that two-factor authentication is perfect there are always ways to defeat two-factor authentication no matter what kind it is but it's another step in that path it lengthens the attack for the attacker and the attackers don't like long paths and if two-factor authentication filters out 90% of the attacks that's a huge improvement that leaves 1/10 of the work for your ops team that would have had otherwise and so try to lengthen the attack path for the attackers because the 85% of attackers want the short path we're gonna move on yeah there we go and then the Third Point is shown here and so these are the actions that happen in
breaches these are the actions that happen to the beginning of breaches the use of the actions that happen in the middle and these are the ones at the end and by the way obviously for a short breach like a breach that's one step the beginning is the same as the end there is no middle so there is a little overlap between these and the interesting thing about these charts is that the point is not the top it's the bottom well I need to step back I'm getting too close to the microphones at the bottom we see them the least likely action to start a breach is malware and no one here is going to like give me
brownie points for pointing out the malware has to come from somewhere yeah like intuitively that makes sense now that you think about but how often do we think about that in a breach or in an incident where we say hey I see malware that clearly means I need to look backwards in time I'm thinking in terms of a path I need to look back in the path on the other hand it is very common in the middle and so we can say that this path breach is going somewhere in fact social is the least likely thing to happen at the end of a breach so if you're seeing a social act that means you need to look forward for where the
attacker is going and this brings us to our third point for defensive ideas around paths you know based off of what you see you can guess it what you don't see you know if you see malware you can guess that you haven't seen things before if you see social you can guess that you haven't seen seeing things after you have the opportunity to work through and work regularly understand what's happening in your system and what you don't see based off of what you see and so this is an interesting one so the only we talk about breaches like we would all think that the breach starts when the attacker starts messing with us and ends when the actions on target
cease that's that's kind of where we mentally define kind of boundaries for a breach but how often do we really seriously think about what happens before the breach and what happens after the breach and that was one of the things that I kinda want to explore in the DBR this year so we collected some data from criminal forums and marketplaces and like I'm expecting like the you know the Amazon of evil like you can like put in that I want ransomware and it gives you the nice thing it says like star ratings on all of it you know some good comments and feedback like I'm expecting this nice set if it's nothing like that it's like like watching 15 year-olds
chat on halo it is much less lower level of discourse so to speak in fact a large so we'd already put in filters to try to get down to just like the security related stuff and still just drugs lots lots of drugs that's what criminal forms and so when you hear like darknet don't think like you know masterminds have evil you know think like the guy down the street trying to get his weed it's not that bad and what is there was very much credit card related because I expected to see a lot of trade in like malware or you know stuff in the tool chain for attacks and that's not what I saw I saw mostly credit card trading and
other things around bank accounts and there's a little bit of other things related to it but it's mostly here in this cluster around that the only other cluster was around accounts and so things like VPN and proxy accounts which the attackers use in part of their attacks but also not listed here are video service accounts both the legitimate kind that you you and your spouse share and then like the more adult kind those were traded a lot as well and then the one thing that isn't in listed in here is there's a lot of cell phone cells and so attack we saw lots and lots of meat messages buying or selling cell phones and that tends to be
one of two things it's a lot it can be multiple things so a lot of times it's people that are selling illegitimately guns cell phones as a way of cashing out their crime but it's also people that are buying cell phones as a way of laundering money that they've gotten illegitimate lee and some of it is even just normal cell phone sales but these are the things that are happening it's not like this you know incredible criminal architecture and so after looking at that we wanted to look at what happened after the breach and we went to the FBI I see three the FBI internet Crime Complaint Center and got data from them and for those who don't know you can go
in report they have a nice simple website where if you have a breach or an incident you go in your report what happened and you know they at least collected and maybe are able to help you as well and you know what we found is that the majority breaches weren't particularly expensive you didn't have a lot stolen by the attacker like it's like eight thousand dollars or twenty four thousand dollars it's like the cost of my car at eight thousand dollars or the cost of my wife's car at twenty four thousand dollars she has like the nice fan and as a complete aside I love driving a minivan there's so much nice there's room in the
back it's like you know it was not it was not something I expected the attackers aren't taking a lot of money and so where the cost from the breach is coming from if you go back and look at the 2016 report one of the things you'll find is that the majority of the costs for breaches come from outside legal assistance or IR and both of those apply even if you're breach came from an error that you made you still have to do the legwork and so if you're planning to secure your system and plan to decrease the cost of breach one you can't ignore errors and two you need to plan to deal with IR and with
legal and have contracts in place to minimize those costs because the attackers aren't always taking that much money now obviously the caveat is that there's as many breaches between the median and a hundred million as there are between a median zero so there are some big ones in there now the other part of this is that when the ic3 recovery asset team acts upon a business email compromise and works with the destination bank half of all US based business email compromised victims had 99 percent of the money recovered or frozen and only nine percent had nothing I recovered in that frozen is like frozen so that they could go back and get it back from the bank and what this
means is that even if you've had the money stolen there's a chance to get it back that money with somewhere it went to a bank in banks in general act normally and so if you report quickly one it's possible the FBI will be able to help you but there is a chance don't just don't give up just because the money is left you know go after it see what else you can do don't let the breach just be the end of it and so now I'm going to talk about industries and for the industries the reality is none you care about more than like one of these industries and so I'm going to go through them relatively quickly try to
hit the high points for each and not make you wait through the other like eight industries that you care absolutely nothing about so this is going to go relatively quickly we are going to show the common paths for each industry or the the paths for it and then the most common path here in accommodation food services you can see that malware and hacking tend to be very common and that's actually part of the theme for this industry their most common path is hacking leading to a breach of confidentiality or hacking leading to malware and malware later breach of confidentiality and the reason is because accommodations and food services has a profound problem with point-of-sale breaches importance no
malware I don't know why it is that this industry gets targeted this way but I even saw one this morning where a major food industry food chain in fact I think three major chains had their point-of-sale systems for about a year compromises point-of-sale malware which obviously steals credentials and it always gets caught by fraud detection it's the credit card companies coming back and telling them hey we noticed that credit cards that were only used at your organization tend to be breached and so we think you have a problem so if you're in accommodation in food sales you need to do one do a better job of protecting point of sale devices and to work on detection because detection is
all happening externally when detection happens externally by that time the attack is over and gone the damage is done next we'll move on to Education which is a lot fun or they've got a lot more diversity and what happens but their most common breach is something you're going to see a lot of which is air leading to breaches of confidentiality and this is going to repeat a lot because it's a short path a straightforward path now they have an interesting case where 35% of breaches were due to human error but they also had a substantial amount of espionage however it's going down it used to be 43 percent now it's 12 on the other side
financial is going up in in education and one of the things we didn't see this year that we saw last year does anyone remember like the w-2 breaches like the attackers would steal w-2 forms in January and then go and cash them out through tax fraud and for some reason that just didn't really happen this year I don't know if it's the threat actor you know gave up or got caught or you know retired but we didn't see it both here and in manufacturing where it was very big a year or two ago moving on to finance and insurance and this is one of the major trends that we saw which was really interesting again
their most common breach was errors leading to breaches of confidentiality but they had a lot of breaches of financial credentials and this data is part of our breach corpus but it's analyzed separately because if you take 2,000 breaches from everything else and add it to 50,000 breaches of botnets all your data is about the botnets and so we analyzed them separately and one of the things we find is that the vast majority are related to financial institutions with a significant amount still of information organizations and professional organizations but what this means in combination with this is that the attackers are going after accounts they're not going after payment data this is credit card breaches and
financial institutions like skimmers on ATMs and such the attackers aren't going after the payment cards and financial institutions anymore they're that's going down um instead they're going after the credentials that's going up and so if you're in a financial organization you have to be prepared to protect your customers and protect your customers accounts because that's what the attackers are coming after moving on to healthcare and healthcare it's always a really fun one because healthcare has like they have like a little city right we've got the medical side but then they've got the utilities side and they've got the finance side and they've got the retail side and they've got the accommodation side and they've got so
they've got like this little city of all different things mixed together and because they have mandatory reporting errors leading to a breach of confidentiality is again their most on path but they have something that no other industry has they have more insiders than they have external actors anyone want to take a guess why but disgruntled no but I will give you a book for actually answering the question I really appreciate it it is so nice when people will answer questions because that helps and we get to think about it and what's happening here it's very similar that but it's it's almost the opposite it's fun the attack like its internal actors that go and look at data a lot of times and go hey
you know I want to go look up how someone was like someone was in the news and so I go look up someone's medical record and that's a breach it's also health care people who want to make a little extra money on the side so they steal some healthcare records and pass it to their friend who knows some people and it becomes healthcare fraud in fact we were coding one so I stream on twitch by the way like Tuesdays and Thursdays turning news reports into structured data if you ever want to watch it and one of the ones we did this week is three guys that were caught they still had logins to their formal former health
care institutions where they had worked they were logging in stealing healthcare information and turning around and filing fraudulent medical Medicare reimbursements with it and that kind of thing happens all the time and so it's that kind of misuse paired with the mandatory reporting of errors that lead to breaches right because if you send someone's medical data a person as medical data person be like that's reportable you know if you accidentally leaked 50 records of medical data that's really reportable and so those kinds of things cause internal actors to be more common than external actors in health care that said I expect health care health care also has a ransomware issue over 70% of malware in healthcare is
ransomware and so it doesn't show up in the breach data because ransomware is rarely breach data but it is a significant trend in health care as well so moving on to information all the tech companies right like if you're in Salesforce and you pull the pull down it's got technology that's these companies and because you know historically our industry classification systems don't have like a technology option so they all kind of end up in information and information companies again are a little bit distributed social and hacking a little more technical in the attacks but again their most common breach is related to Aires is Aires leading to confidentiality because again they're using lots of services that it's easy to miss
configure they've got a lot of space to get cause errors the interesting thing here is errors are the most common thing but there's a very high amount of espionage and the errors causing internal attack has to be pretty high and that's due to all the MIS configuration so cloud services exposed to the Internet or databases exposed to the Internet but they also have a huge amount of espionage twenty-nine percent of breaches were related to espionage and information 22 percent of breaches leaked secrets and so information that technical companies need to be worried about espionage and manufacturing is a weird one because they're the ones that are not really on the Internet right the manufacturing companies like
have the like the one web page from 1995 that's static and basically says nothing about them because that's not how they do business so we kind of wonder like how did they become breaches you know it's not like they're exposing a bunch of cloud services it's not like you know they're you know doing a lot of work through their online presence but they do have a lot of things to lose and so their most common path is actually misused cleaning the confidentiality I kind of suspect it's because they don't have that internet presence but the interesting thing is they're becoming much more financially motivated traditionally it was espionage corporate espionage that it led to breaches but
over the last two years we've seen a transition to financial and like I said before we didn't see the w-2 breaches that we saw but I really kind of expect that the value that a manufacturing organization will bring to attackers is going to be a lot of times in the workers they employ and so if you have a lot of staff you have a lot of healthcare records you have a lot of tax records you have a lot of personal information and all those things can be directly turned into money what it is not normally is it's not normally attacking the systems on the manufacturing floor like that's the cool the cool breaches you know the breach
that like takes over the robotic arm and grab someone and throws them across the room but that's not what really happens you know it's hard to like make money on that and so the attackers are really not going after that maybe we would see ransomware in that but I think that there's a general awareness about security an OT that we're gonna try to track ot a little better but I suspect that the majority of breaches we will find will not be related as we get better at tracking ot versus IT security moving on to professional and technical service who here's akin consultant yeah this is y'all this is all the people doing services when I did you know
actual engineering I'm my background so as an electrical engineer this was me and it's kind of a nice this diverse structure but still air is leading to breaches of confidentiality or the most common path and here we had lots and lots of business email compromises right this is I'm not really sure why but this is where we saw executives being breached this is where we saw fraudulent transactions so the CFO being told by a fake CEO account to go transfer money and the CFO transfers money those were up 18 times from last year they were 1% of breaches here last year and they're 22% this year this is an area where we need to worry there's a lot of
protecting the financial staff for the ones tarted there's use of stolen credentials because if you're going to compromised an email for a business email compromised you got to compromise the email and a lot of its executive staff being targeted because those are the ones that can transfer the money now we're down to two industries thank you for if you've seen your industry already for waiting through all the others public administration in retail public administration air is their most common path because they have mandatory reporting but the interesting thing is here the big uptick in espionage this year was related to public administration and the scary thing is that over half of breaches took years to
detect that now just think about your organization you know if the majority of breaches you detected took at least a year to detect you know how would you come out on your performance form right like this is not a story we want to be telling on the other hand it may indicate something good maybe we stepped it up in public administration and we're catching those old breaches now and that's why it's coming in the data this way regardless if you're in public administration you need to be worried about espionage and we need to see improvement in our detection and finally retail which is one of the funner stories from the report here physical breaches leading to breaches of
confidence the integrity of their most common but we saw this interesting switch because we saw a point of point-of-sale breaches so non web app servers are card-present are going down the attackers aren't attacking the point sale and retail as much anymore instead they're attacking online payment card not present and web app server based breaches in this this is our breach data this is data from the NC FTA and there's a couple of things you can leading to this right the shift to chip and signature in the u.s. is probably part of it and our data set tends to be kind of us biased by the way if you know international sources we'd love to try
to get a very holistic view internationally so come see me afterwards tell me about organizations that might help my international corpus also we saw vulnerabilities in retail payment card online services right there was a software package that had a vulnerability that was remotely exploitable that caused a lot of breaches and finally we didn't have any of the breaches that breach like a point-of-sale system like so what happens is you have the point-of-sale company and they've got a bunch of customers and then they get breached and then the attackers used that to breach every one of the customers underneath them and that becomes a lot of point-of-sale breaches in retail and we didn't have any of those last year but
we had one that came in after the report got done this year I'll have time for questions afterwards and so that's the last industry but this is where this gets to be kind of a an interesting point this is where we have to step back and have the discussion about you know what are you willing to do to balance cost and risk because there's really kind of three types of organizations the first type of anything gonna be the kind that can't afford to mitigate even the basics so I live in this little three stoplight town right my liquor store their point-of-sale device is leased they don't own it my dentist he owns his computers but he
doesn't own the software on him he's leasing that and so what they had the opportunity is they're taking advantage of the economies of scale because there sale vendor can then hire a knock or hire an MSSP that then manages all the point-of-sale systems and if you're a little small organization you don't really have a lot of opportunity you can't buy your own NOC you need to invest a service that can now where I suspect the majority of us stand is in this area kind of medium error we can invest in security and so who here remembers the the four horsemen someone that hasn't answered before you sir blocking it sure tread a middle or the
four in front of you beard Balbir yeah you okay yes ma'am hashing heirs social and credits perfect here I brought one copy of the printed report like I get six of these things a year and so there's one of mine you need to address these things first patching known external vulnerabilities especially the old and eating ones prepare for graceful degradation when errors occur protect against financially motivated social engineering attacks and phishing and defend against credential theft two-factor authentication the other tools you know and that's kind of the obvious thing but then the question becomes what do you do after that and I think the problem is a lot of us say well now I need to go after those
advanced threats and this is where it gets complicated because after you've taken care of the threats that are able to that only have like or one-trick ponies then the threats can pivot and if the threats can pivot they can take advantage of input any problem you have and if they can do that you have to stop everything and so now instead of five mitigations you need twenty five mitigations to stop them so the question is are you going to invest in that entire additional twenty mitigations as an organization and do them all well and if you're not it may be a good idea to stop at the four and take the extra InfoSec money you have
and put it into your team and trying to deal with the places that you're for mitigations fall down because right nothing's perfect and so you can use ops to help deal with that and then you know to deal with the advanced threat so you really just need to know your local national the local chapter your the national law enforcement they are there to help you in the case of these larger more complex breaches and it is much better than Oh them before the breach then after on the other hand if you are that advanced organization you want to spin you want to stop the advanced attack you need to be prepared to spend a lot and to lose a
lot because this is no longer you're no longer playing in the minor leagues you're trying to you're spinning like blank check right there's some of the big companies give their security department a blank check you know and we're not talking like small blank check we're talking really big blank check you need to be prepared to make profound changes across your organization it's Google changing all of their services to the zero trust model to basically segment all of the users off from all of their services you know you need to be prepared to do that - it's like the minor-league team going up and playing the majors and you're gonna lose a lot you're gonna spend a lot of money a lot
of resources trying to get better and for a long time it's not going to matter because you have to stop you have to cut all the paths out until you start winning and if you're not prepared for that if you're not willing to do that as an organization you need to be prepared to just stay at that medium level and that's okay because you're gonna stop the majority of attacks and so with that the only thing I want to leave you with is no matter which one you are it's okay to be small it's okay to be medium it's okay to be large but no matter what you do do something because you only have to
get that much that itty-bitty bit better to get away from the attacker and so with that I'll open up to questions yes
so on Web Apps right the credit card number has to be put in through the web app and so if there's an hour on the website they're going to get it that way point of sale devices are still scanning you know particularly like accommodations they're still scanning mag strips and if you're scanning mag strips and you're reading memory if you don't have an advanced max prep reader that encrypts at the reader you're going to get in so do I know whether these organizations are following PCI well I would have to go back and look we've got some of that in our data but it's not it's not something I look at regularly but I suspect that what it is they're
kind of these traditional ways because if you're using a more advanced processing or using chip and sig is less like we haven't seen anything that seems to indicate that there was kind of a robust attack on chip based credit credit card authentication oh yes sir
so the question is attempted breach is for utilities and we do collect that and we see it's a small sample size and due to some statistical reasons we've traditionally had not been able to report on we are making changes to our process to be able to talk about it at least in a statistical manner but the story is generally that it's not the Ooty systems or if it is the Ooty system it's the HMI the human-machine interface and it's the normal attack processes I don't doubt that there are nation-states and there's probably few of them in our dataset they're making these minor you know that actually actually attacking the embedded systems but the vast majority of even industry utilities type
breaches are like fishing on the HMI why people are opening emails on the HMI I don't know but it happens any other questions two more questions oh yes
my understanding is that normally it's and just logging in and emptying out the bank account in most of cases that we've looked at directly but that doesn't mean that the other things don't happen because just because of the way the data comes in the monetization may not have been explicitly written down yes and then our data it lags by obviously roughly a year and so shifts in the last couple of weeks or couple of months won't be captured in the reality as we've seen some really interesting trends subjectively we've seen trends in the last couple of months that I expect to show up in our data this year to make the 2020 report have some interesting
changes from the 2019 report and so I it's been fun kind of seeing these potential trends show up and I'm excited to see if they actually show up when I look at my data as an aggregate set any other questions I'm missing anyone I'll see one so thank you [Applause]





