Introducing DropEngine: A Malleable Payload Creation Framework
Show original YouTube description
Show transcript [en]
absolutely that sounds great um all right if if at any point um people have trouble reading stuff because of like text size and stuff just let me know um i'm still getting used to this you can see a little bars thing up here anyways so my name is gabriel ryan i'm an offensive security engineer as a cloud provider i'll say no more um i used to work for a company called spec drops and before that i actually worked for a company called gotham digital science uh so i've got a few years under my belt in the consulting world also uh now kind of out of the consulting world still you know just trying to stay active the open source
community what not um so this is a talk that has to do with initial access payloads um so what are initial asks payloads so if you're not someone who does a whole lot of red teaming or um would have a lot of exposure to this um it's an initial access payload is a bill that's used to gain access to a system environment so essentially if you have an implant or some kind of shell that you're trying to drop on a remote device this is the thing that's going to set everything up for you um a pretty simple design uh it's it's only jobs to execute an implant or a second stage payload and you know pretty much get you off the
ground um they're also known colloquially as droppers or shellcode runners i'll probably be using the terms interchangeably throughout the talk so just kind of bear with me on that um yeah so although i mean so initialized failures they perform a pretty like mundane task at least like a face value right i mean all they're doing is they're loading code into memory and executing it um however it does get a little more complicated that because although you have this relatively simple task to perform um their the actual obstacles they end up facing and doing this stuff are can be pretty significant start out with you know you have to figure out a way to deliver the payload to its intended
target this usually takes the form of sphere of fishing although there are other ways to do this but um you know while you're in the payload delivery phase you're gonna be your payload is gonna be exposed to signature-based detections um both like at the veil filter level um it's gonna be also like exposed to automated behavior allowance um analysis and the form of automated sandboxes and then you know finally once you actually get it onto disk uh you have to do so without triggering antivirus then you have to execute it execute it without uh triggering edr and that was the execution so the payload has to be executed from disk and uh load shell code into memory
without triggering antivirus or input detection response also known as edr um in windows environments uh they could see that like it gets even more complicated because um application white listing like app um is pretty much the vehicle that's on enterprise with those environments um specifically and you'll see it on a lot of other types of environments as well um so what this means is you have to rely uh pretty much exclusively on on whatever it is live off the land mine or your scripts or law boss um in order to actually get your payload running essentially uh what these are it's it any like a law bid or a law boss uh sometimes a binary or script
that usually comes with the operating system although sometimes it's just present on the environment you don't really know why but it's something that's done the environment usually usually comes with the os and essentially it allows you to um it usually has some kind of like hidden functionality or or what have you that allows you to do things that are useful as an attacker so for example uh there are a number of law bins that will allow you to uh execute code which is great because you know the law of it is you know not it's whitelisted essentially so if you're trying to bypass whitelisting you feed your payload to the mall bit and it kind of actually use it for you
um but you know the downside of having rely on lobbins is that a lot of them uh when you are feeding your payload to them uh you're feeding it to the the law button um in the form of a script usually and you know within a witness environment they usually mean special basic or c sharp uh which is all run through uh microsoft's anti-malware scanner which is which is not good because it can look at your code and see what you're doing so um once you move past that right then you also have to your payload you have to assume that at some points could be compromised it's just the stuff you have to make
and when you're paying a little bit spurred it has to be able to withstand manual analysis from threat hunters and particularly reverse engineers uh because if they are able to figure out exactly what your payload is doing um that's where attribution happens and also that is where um that could cut your offer whole operation pretty short so none of these obstacles are insurmountable um it's been done over and over again it's just a giant cat and mouse game um but the important takeaway though is that if the actual evasion techniques that use to overcome these obstacles all have a relatively short uh shelf life defenders will eventually catch on to what you're doing i mean there are some pretty smart
people working on the blue team and they tend to write you know especially the writing heuristic based detection so they're looking for patterns of behavior rather than just static signatures once once they identify that you have to pretty much move on to something else um and and this is really why we do red deep engagements right it's to it's the kind of this interplay between red and blue right between offensive these defenses overall how we improve you know like our security postures but you know what this means for for you as a red teamer is that specific payloads you know your invasion techniques are are gonna have a short shelf life to begin with and specific payloads so
specific implementations of those techniques are going to have an even shorter shelf life because whereas um there's a little more work involved with writing heuristic based detection signature-based detection is pretty fast you just need to grab a hash of where the payload is you know if you see that pop up anywhere you you fly on it um and actually that you know they're that kind of detection that provides a lot of value for defenders because it gets rid of a lot of noise and you can focus on the i guess the more sophisticated threats um but what this means from from an advertiser's perspective is that reusing payloads over and over again is likely to get you burned
which is not great um and this kind of you know makes initial access payload it's kind of a major pain point for offensive teams because you usually have to write them by hand or at least modify them um there aren't a whole lot of great ways to automate that i mean there's there's a lot of like kind of semi semi like imperfect ways to do it but um and the more the more code you reuse the more problematic this is the more likely it is that someone's gonna trigger on it so you know essentially what you have is like there's this very simple purpose essentially all this work is going into just launching your your your implant
right and starting the operation and to do that you actually have a lot of moving parts that despite the fact that this overall purpose is super simple um so drop engine is a project that i came up with to kind of make this a little bit easier and you know it's kind of it's in its emphasis right now it has its overall i guess um you could say uh you know it's gonna keep growing but essentially it addresses this problem by providing valuable framework for creating shell code runners um the core idea is to you know basically look at all those uh components that actually go into initial access payload and and you know kind of isolate them as
just components and then modulize them and you know this lets you do is you can kind of mix and match excuse me uh different uh you know payload attributes and put them together into something cool and then as a bonus continue to lose my voice um as a bonus uh it also provides built-in application encryption and symbolic substitution substitution capabilities um which makes it pretty easy to evade signature-based detections so what this does is that the idea is that you you can do this to greatly extend the shelf life of your of your payload components which makes you operate more efficiently let's talk about how it works um in order to really understand how dropbench works and what it does we kind
of have to talk a little bit deeper into how initial access payloads are built so at their core initial access payloads are pretty simple as we talked about they really involve two major steps um you load the shell code into memory and you execute it if only things were always so simple but um yeah so the terminology here uh just because this kind of matches up with the component that we have for a good drop engine um we'll refer to the routine that performs these two functions as the executor or executor routine or executor function uh from this point onward so if you hear me say executor we're talking about a subroutine that literally does this right blow the shell
cut into memory execute it um so there are many ways of achieving shell code execution um you know there's dll injection spawn of thread i mean you could do p injection there's process hollow there's all kinds of ways to do this and it just kind of keeps growing um but you know i think what we actually want to do is we want to kind of abstract away from specific uh details that zoom out a bit and and kind of look for like a broader pattern um also i mentioned that uh um you know application whitelisting is is ubiquitous so we have to look at how you know when i said there are actually two steps
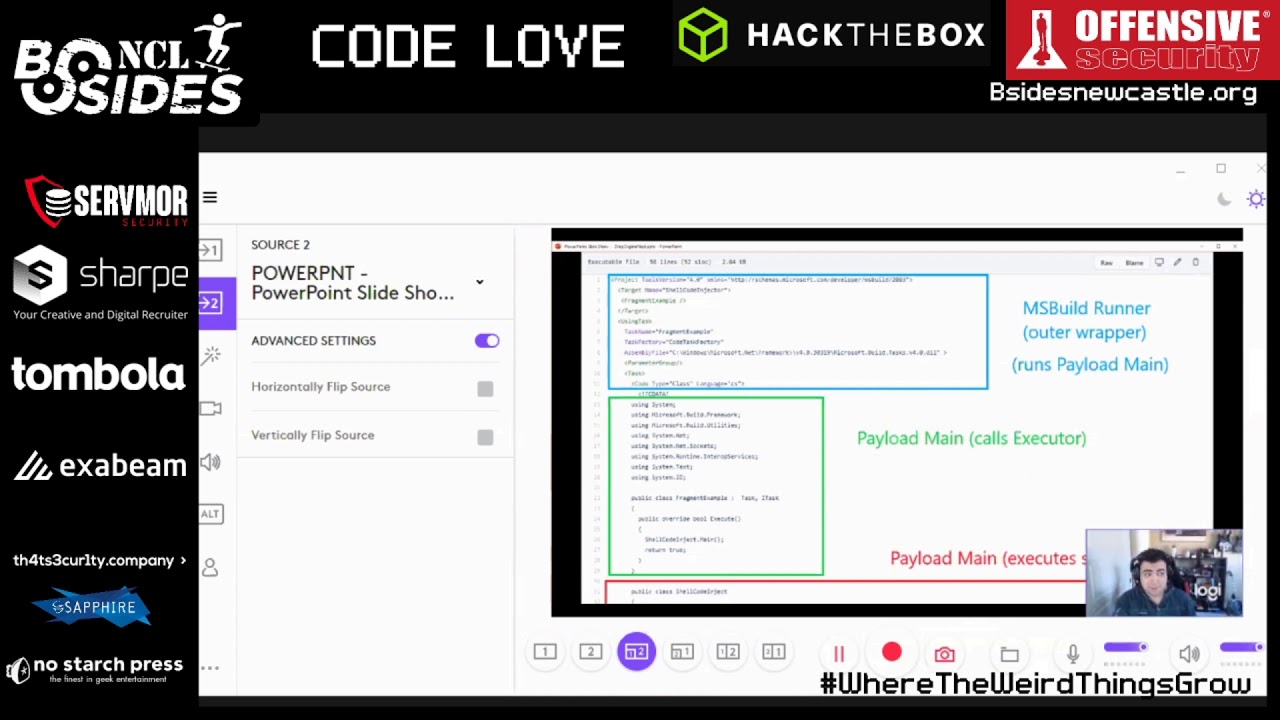
there's there's really three steps involved because remember we have to load our shell code it's when we're using a like a lull bit of some kind so really we actually have three basic components when we actually look at the context of executing this environment where you have to use law boss so these three basic components are the shell code runner um i know this whole thing is technically the shell code runner but you know if we're looking at components let's just call the outer wrapper that can be executed using a wallbuster login or shellcoderunner um our payload main is our is our application entry point so this is the function that's going to be calling our executor function
and finally we have our executor function so you kind of see the structure here right and and that's what's actually loading our shelter membrane execute again so drop engine actually implements these basic components as base classes that's like the fundamental where everything is built off these are all isolated and you can just if you're writing a module for it you can just inherit from them um you know you can choose any kind of executor you want and wrap in any kind of shell code runner you want and the overall structure of the payload remains the same which gives you a lot of flexibility and also you could figure out by the way it's like if a specific part of your payload
ends up getting burned you can just replace it it's um one of the uh the the biggest innovations for you know modern infantry was the development of replaceable parts you know you no longer have to replace the whole musket if something breaks you just replace the component that's kind of the same concept here you know just to kind of look at a less abstract example so this right here um this should stay executor uh pretend it does but um yeah this this basically corresponds to this this is this is not my code this is um actually from a move kit uh so i think it's actually based on the casey smith wrote and then uh
steve flores actually turned it into something else uh but this is uh an ms build payload so essentially the way that ms bill payload works xml file that's used for compiling um well it's it's it's i guess intended purposes is for essentially allowing you to compile uh visual studio projects without having visual studio actually installed in the system so pretty cool from a developer's perspective um but from from an adversary's perspective you can also have it run c-sharp um code which you know because it's on every system everywhere essentially it's a really easy way to get around application whitelisting um so you can see here that you know it this actually this payload actually does follow this pattern that we that we
mentioned if you're out a wrapper and that's this xml that you see and then you have your payload main which literally all it's doing is calling this shellcodejack.main and then you have your your that down there your actual class shell could inject and that's your executor and that's where everything is is actually being run from so um that's how basic payload works um we did mention that you know it's essentially to maximize your chances of success you should pretty much always protect your payload with some form of encryption uh what this does is it prevents your your signature-based detections from flying on your shell because it's malicious and makes it a lot more difficult for human
analysts to reverse engineer your payload um so if we take that that that um process that we talked about earlier if we tack on the encryption step um your your payload execution process looks like this you'll load the encrypted payload into memory you decrypt it using the encryption key to obtain plaintext shellcode and then you load the plaintext shellcode into memory execute it um so if we're going to start encrypting our payloads though that actually presents another problem what do we you know where do we get the encryption keys right because you're you're encrypting a payload and storing it on something that's going to go on adversaries um adversary system um and then you're gonna have to decrypt
it you're gonna need the same encryption key right that you that you encrypted with so um in this case uh i mean we talked about earlier you should always assume that your payload is going to get um compromised at some point and if you're storing the encryption key on the payload then you know whoever's is is looking at your payload could just grab the encryption key and use it to um to to decrypt everything and see what you're doing so it kind of defeats the it's self-defeating essentially um but with that said you know we essentially have three options um if we're going to uh encrypt our payloads we can we can derive the encryption key
we can give our payload the ability to drive the encryption key somehow and that prevents us from having to store it um we'll go into that more detail a second uh we can also retrieve it for remote source that's a pretty secure way of doing it as well um or we could actually just like store the encryption key on the payload which is you know it works for passing bypassing sanctions but the second human looks at it it's going to be less than optimal um so let's talk about the first option though you know how how do you derive an encryption key on it on a on a payload in a way that a human analyst
you know essentially couldn't figure out how it was derived from um classic way of doing this is environmental keying this is not a new technique it's been around for well it's been documented for several years but you know it's i imagine it's been and um in practice for a while if you i don't know if you guys remember stuxnet right it was that uh um that malware that was affecting iranian centrifuges that's more or less how this worked is using environmental keying is how they're able to to uh you know target specific types of devices with with high degrees of accuracy essentially the way environmental keying works um is that you derive the encryption key
uh entirely in part or in part from values within the environment so for example you derive the encryption key from you know like an internal fqdn external left qdn um you know your username so if you want to target specific users or user groups um or even the hard drive serial number if you want to get really precise and essentially what this does is you you feed those into that when you're actually encrypting the payloads you drive your key from that and uh then when you're decrypting the payloads the first thing you do is you you grab those values and use it to to derive the the decryption key and of course if you aren't on the intended target you know
it's doesn't have the right serial number it doesn't have the right username that that encryption keys could be wrong and the payload is not going to decrypt successfully um it's a really good way of turning a reverse engineer into a password cracker essentially because if you if you're really clever about this they actually have to guess um you know what the serial number's gonna be that could take a lot of work and that's what you want you're buying yourself time um so the advantages of this technique it's very targeted uh your shell code will only be decrypted on machines that match the key specific attributes um you know like if you want to go after
one person by infecting a million machines this is how you do it um also it's highly resistant to analysis uh the encryption key is not stored on the payload and it's it's very difficult to guess um and all right here's what we try to do this live demo thing so this is gonna be interesting right um i'm going to do some screen flipping for a second and i have to figure out how to do this using right okay so first things first i want you to see this okay so this is full transparency this is my my current av setup on this machine that i'm running off of um i have defender turned on although i
don't have automatic sample submission for cloud delivery delivery because i don't want this stuff getting pushed up to the cloud at this time um you know his demo guys and everything um also but i do have an exclusion set right and that is this folder here and the reason for that is that um you know in an actual scenario what you'd be doing is you'd be taking your implant and then you'd be obfuscating it somehow then executed on someone else's machine so obviously the machine that you're you're you're obfuscating it on probably wouldn't have av turned on in this case i'm kind of doing everything on like one or two machines so and and both of those steps are
happening on this machine the execution and the obfuscation so if i didn't do this what would happen is that the second i try to load that payload into memory from the obfuscation framework it would trigger antivirus which is kind of you know counterproductive to demonstrating this so essentially anything in this directory um it's if he isn't going to trigger on with that said that's only one directory when we actually demo this the finished payload is not going to be executed from the exclusion directory okay so just going back here really fast now i'm going to switch again to hyper and this is it's a cool text editor it's written in javascript but it has been kind of buggy
lately stuff i have run the problems i do apologize um so the first thing i do ls is not found that's off to a great start okay that worked all right so uh this is and i've got these just because i don't want to have the you know i've got these pre-written down because i don't want to waste time trying to fumble around with commands but essentially what we're going to do is we're going to run it essentially we're going to say you know pass it this argument here build uh we're going to pass it um this is just a this is this is a um m2 shell.bin is an interpreter payload so if anything's going to trigger a b it
should be this right um then we have our our our interface we're going to we're going to this will be a c sharp payload that's why we're specifying that interface for the purposes of drop engine you can think of the interfaces like the glue that holds all the components together uh so if you're wearing a c sharp payload to use the c sharp interface um encryption key we're gonna use a static encryption key so it's actually gonna be stored on the payload uh but it will show us you know just kind of what we're doing and we also have a decryption key which is the the matching you know algorithm essentially this can actually be on the payload itself uh we're using
as encryption um and then we're just going to use a virtual outlet thread executor and it's going to be an ms build shell code runner which will be using a lot just for the sake of consistency and not messing up these demos on uh on a live zoom meeting so i'm going to copy this which is essentially just that command right there and i'm going to run it and we should have a payload here right
now i'm going to set up a um session there use ms build to run this thing and you've got a session the accession stash i session 21 because i was practicing earlier and i'm just going to exit this so that's just a basic statically key payload know what a environmentally payload would look like using this process of this same deal this time we are deriving the encryption key from the external left qdn um yes this is my external fqdn don't worry it's going to change i mean after this talk and also the current username um and i'm gonna just go ahead and do this it's also gonna be another build payload
because that lets me just do this and restart my listener and yeah so you'll see essentially it worked
yeah so that's that however watch what would happen for example if i if i specified the wrong username right so if we didn't know the username that this was targeting yeah so i'm just going to put like two days after that right
my job's just to be safe i'm going to [Music] start my reverse handler i'm going to execute my payload again and you see this that failed so the reason why they failed is the the decryption didn't work um so i mean a username is pretty easy to guess but imagine if that was a hard drive serial number essentially just it just wouldn't work right and that's that's the fundamental thing about um environmental keying is it'll only work on your target system if you do it right which is great um i'm going to switch back to figure out how to do this let's switch back to my powerpoint cool all right here we go computers all right so just another cool
thing that i added um symbolic mutation so essentially um you know actually let me let me generate another payload really fast so i can show you well yeah let me keep going actually i'll show you a second so um yeah essentially like you know one really almost like necessary to be honest i mean you should pretty much always be doing this if you're running something like a c-sharp payload and you're using it multiple multiple times you should really you know basically look at every single variable name in that payload uh because remember this is this is kind of a pseudo-compiled language but it can just be it's like java you can essentially decompile it and just look at
everything in the payload so because it can be analyzed that way you really should you know get in the habit of every single class name every single function name every single variable name um needs to essentially be substituted for something else every time that you run the payload or at least on every op because you know otherwise people start to say that around your stuff um the problem is doing that is the pre-electric process i mean some some payloads can be like a thousand lines long and have a lot of variable names and there's a bunch of different ways to do it i mean um actually uh some of the guys from mdsec had this
thing that they released while back when they're using um some company like azure devops to like you know call us i think it was like some specialized compiler essentially they were building a tree abstract sensor x3 i think out of it and and going through doing it that way you can use like regex but it'll it'll you know mess up a lot essentially um so one thing that i wanted to do right about was was at a really easy way to do symbolic mutation which is just you know you use an algorithm to change all this stuff um and you know essentially you know the way that drop engine does this um is that it has mutator modules but
they're not actually payload components but essentially before the payload is rendered um the the combined list of symbol cell names for for every single module is passed to a mutator function the mutator function does one thing one thing only and that it just takes those symbol names and it maps them to something else and you know essentially the the um the algorithm for doing that's like up to the to whoever wrote the module so i mean you could they're pretty easy to write so if you have like a mutation algebra you can just kind of toss them in there it's pretty easy to do um currently supportive methods for mutation um you know mapped to random strings
essentially to substitute all the variable names simple names for for random strings there's row 13 i clear that there just as a proof of concept because it's both easy and funny um there's also a symbol substitution using word list that's actually super useful because if you want to make your payload not stand out as much you can essentially just create a word list out of yeah existing innocuous programs and you know take variable names from real stuff that actually should be running on the target environment um and then you know use that to create your your word list um and also there's a null mutator that just doesn't do anything at all and that's mainly there for deep
debugging purposes but i don't know if you don't use the mutation that's how you do that so just to kind of quickly show you how mutation works i'm going to switch again to hyper there we go um all right so by the way for this one i'm not going to be using the actual metasploit playload i'm going to be using essentially this little dummy payload here that just is something that's called a bin file but it's really just a text file that contains the statement um the reason why i'm doing that is because the actual look out okay if the actual metasploit payload is pretty big so it's kind of hard to walk through so if you want to see for example what
what the null mutual looks like it doesn't actually mutate anything
um oh that's sloppy
just not getting everything i know the dress again i ran into this problem earlier this should work yeah there we go okay so this is your actual payload right and you know here's a lot of stuff and you can see essentially that it's not it should be mutated
there we go so here's your payload name there's your actual payload um you know here's essentially where the decryption happens and here's where the execution happens your executors here and your decrypters up here but you notice you know nothing has changed now watch what happens if instead say mutator random string but we kind of saw earlier suddenly all these variable names are randomized so good luck signaturing on that and you know if you want to see the wordless example um you know say yeah i'm just gonna try to copy this guy and hope it works so and here's how the word looks but now it didn't work copying pasting but not really copying pasting all right you know what i'm
gonna do
let's go up this is your list
yeah so i'm just using a word list of stuff to teach everything for games of cities in the us but i mean you know once again you could you could use a more a more um i guess realistic word list so yeah that is um that's symbolic mutation let me switch you guys back to powerpoint all right there we go um cool so now we've covered that um they're actually we mentioned some other key techniques right there we went over um environmental keying uh but we also mentioned you know retrieving keys from remote sources um so that is that's a technique called remote keying um so essentially the way remote keying works is that you know
the shellcode encryption key is retrieved from a server somewhere you know either every https dns or some other communication channel um this is actually a really effective technique especially if you have a really well well-designed non-attributable attack infrastructure if you want to know what i'm talking about uh go check out uh the red team infrastructure wiki by jeff dimick which is a compilation of a lot of different stuff about this but it'll go over all this stuff but um yeah essentially if you place your your you know key server behind a redirector this is this is particularly effective um but essentially the idea is that you you run your payload then you basically make like a get request or an http
request or reach out somewhere and grab the encryption key and that way you don't store it on the payload um of course you know the question is if an analyst analyzes your code and they find the function that's retrieving this key well what's stopping them from going and and you know hitting the same api endpoint somewhere and you know trying to uh get the encryption key that way well that is where one team one time remote key comes in it's a variant of this technique where the server actually tries to delete essentially the server you know as soon as you make that request the server once the key is retrieved from the server it's deleted uh from the server's
database so any future requests for that key will will not return anything they'll either return they'll either be ignored or return junk data or if you want to be really sneaky redirect to something completely innocuous so like hey it's just a normal website um but yeah once again the advantage of this very similar to um you know essentially the environmental keying it's it's um it's resistant to analysis you're not storing the encryption key in a payload file and it can also be protected in transit using tls um also the advantage is that it's significantly less targeted right this doesn't really help you when it comes to uh or at least as much right out of the box
when it comes to like ensuring your payloads execute in the right place but sometimes you don't want that sometimes you want a payload that is is highly secure but less targeted you know so for example if you want to hit a particular organization or even like a user group within an organization that's still like a pretty easy thing to guess especially like oh wow this organization's been infected by malware right you know how are we going to um you know decrypt this key well let's try the domain name you know you don't always want to be specifying like a hard drive serial number so if you combine that stuff with the um with the remote keying uh it
can it can kind of help you have a slightly less targeted attack a broader attack uh area of effect essentially while uh uh still getting that that security for your for your inner payload so another live demo and should show you how that works in drop engine um all right so oh wait i'm not showing my thing aren't i okay i need to get better setup for this i'm not used to this okay cool um all right so here's some here's the syntax for that essentially so we're gonna do two things we're gonna run this this remote r2k server just a very simple uh poc for this kind of thing essentially just it's a key server that behaves in the
way that we just described um and then we're gonna run this uh this drop engine command we're gonna run the build command to build our payload um but we're gonna pass it the you know ip address essentially and protocol for our key server and import and all that um and that's where it's going to get the payload so first thing we're going to do let's start that that one time key server over here this bottom left terminal if copy and paste is now i don't need to
come
only make once all right
cool so that looks like it worked despite the fact that it looks a little janky because i'm zoomed in but yeah so looks like it ran um i'll set up our handler again here sessions or jobs start a we're handler execute this thing now notice here essentially we've retrieved this implant id right or we've the server has received this implant id and it's returned this remote key right here and you know the payload was able to use that that remote key uh to decrypt itself and now it's this interpreter session's been opened up and i'm going to kill them because i'm going to make another point yeah okay
oh i could've sworn out of curl command this way yeah here we go no okay well i'll see if i can get this hang on so if i if i curl logo local host right and where it's something hosted and i give it this id again what should happen is that
yeah remote is not so essentially it's it's received this and you can see the response of this it's just got a bunch of garbage data essentially because we've already used that encryption you've been exhausted um so it gets executed once and then if someone tries to replicate what the payload did uh they can't unless they get another payload which hasn't been executed yet but all right so just to wrap up the keying section of this um the last thing i want to talk about is key stacking let's see if i can just flip back over all right so what is key stacking this is um key stacking is not a real technical term i guess it is now but
like i this is one of the things that like i'm pretty sure like this is something that's been done by malware for like a decade at least um but i needed a term for any way of labeling the process of essentially taking a bunch of keys you know putting them together so i'm calling it key stacking but um essentially it's the practice of combining the results of multiple key methods to create a single combined key um you know so you're for example you have a key that's made of four parts uh you could grab the hard drives field serial number an external ip address um you know and also like a a one-time key uh that's stored in the
payload file um and also a one-time key that is uh retrieved over https um so the advantage of this um you know is essentially you can you can get all the best attributes for all the different key types this way um it gives you a high degree of security difficult to compromise um you know you can you can make it as targeted as you want essentially essentially uh the disadvantage of this is gonna be that um you know this is the more you know key derivation methods you put in your payload the more complicated this gets the more work you have to do once you're using framework which is kind of what we're doing here so
but yeah just to give you a better idea of how key stacking works so you know let's rewind a little bit right so we've added um a dynamic keying to our to our payload um so we had that original architecture that we talked about where we have those those initial components we actually have to update that once more to add this stuff to it um you know we see our our usual suspects though the components that we saw earlier right we have our payload main um which calls everything at this point it's not just calling your executor it's calling everything um it's coordinating everything going on your payload we have our shell code runner which is like your outer wrapper
and that's just responsible for kicking off payload name and is usable by a law banner or law boss right um you also have your your decryption routine and what that's doing is that just taking your decryption key and decrypting your shell code so it takes both your shell code and decryption key as inputs output is plain text shellcode which can be understood and executed by the executor as far as how we were getting those keys we essentially have a series of subroutines that um are performing key database we don't have to worry about how they're performing here key derivations we've this it's more advantageous that we can set up a black box uh for the purposes of building
something like this uh but essentially you just you know take the output of uh basically just depend on all the outputs of all of your keys to one another and that's how you get your your final encryption key and in fact i'll even show you that well actually i'll show you that in a second because i don't have to keep switching back and forth between hyper and powerpoint more than i have to um but this is your updated payload architecture um you know that kind of we saw before we talked about the interface earlier it's the glue that's holding all the stuff together right um if you kind of want to know how that's actually working
uh if we're going to encrypt payloads essentially your shell code is going to be passed to the interface your encryption key functions are going to be passed to the interface um the interface isn't going to pass that combined data to your crypter which is then going to send it back to the interface this is this is cool like if you're actually if you're interested in how kind of like things work at a low level like with a drop mention but if you don't care that's fine that's totally understandable too but essentially this is kind of what it's doing it's just taking this stuff passing it to your crypter that you select back to your interface and then
finally just kind of takes all that stuff and puts it in payload main for you um and the interface is facilitating communication between all these components that are doing all these things and this is our live demo so now we're the most complex demo so far so let's uh let's do this all right back to hyper via demo stack file which is a couple cheat sheet here all right cool so here's our our command that we're gonna run um and we've we've kind of been doing this already i just haven't really been telling you but uh you can see here everything kind of looks similar to what we're doing before this time we have lots of different
encryption keys they're going to pile on top of each other we have our e keys flag which are encryption keys um and then of course find the keys flags right so the the first round is going to be essentially we're just going to be pulling the external fgdn um and using that as the first part of our key then our username then a static uh announce that we're deriving then uh a you know a one-time remote key like we saw earlier so we're gonna take all this stuff that we saw and just to create one big encryption key which personally for us now just to be thorough i'm gonna actually restart this this thing right here
start our payload handler so far so good i haven't had any failed demos yet so pretty happy about that i'll talk on wood right yeah we're going to run this it's going to it's going to build our thing it worked cool
24. sweet all right so i'm actually going to exit that so i mentioned i'd show you kind of what the actual combined row key looks like if i rerun this command the build command this time instead of using our actual our actual implant implants interpreter
and we're just going to use that shell.then file which if you remember it's just a text file also fun fact the reason why this particular string is useful for testing cryptographic stuff is that it has every letter of the alphabet in it so if you want to see if your encryption's working or not working that's that's a classic one to use not that i really know anything about cryptography but i know that
all right there's example all right so this is essentially let's not use indicator i'm so sorry i'm gonna i use the random string indicator which is going to kind of be counterproductive so this is our ms build payload kind of similar to what we've been seeing make sure that this is actually selected yeah it is cool and you know first thing that gets run well if you look up here actually right this is the first it's we're going to call our payload name and our payload name is going to have this encrypted shell code although it's not string essentially we're going to derive our first key and we're just going to keep appending all these different keys that we drive
to each other and then we're going to pass it to we're going to decode it we're going to make it ascii first or we're going to make it into like a byte like array um and then we're going to pass the falcon dependent key to our description key to our decryption function all the way up here and essentially what's happening in the back end if you're curious is there just like ginger tech ones that are used to kind of like glue all this stuff together um but here's your here's your decrypter it's gonna you know basically decrypt your shell code turn it they're going to execute yourself your executor function which is this big mess here yeah
and that's it really all right i'm going to go back to powerpoint start wrapping this up because we're beginning to run out of time um how do i do that i found the button again all right cool so that was our key stack um last last little kind of feature that's baked into this are pre modules and post modules so what are these well essentially sometimes it's advantageous to have something that executes prior to your shell good or immediately after your cell phone finishes executing so for example like a pre-module that could be useful is an amc bypass we mentioned amc well there's actually a bunch of ways to bypass amc out there and you know you might want to
run that right out of the box before we do anything further well if you you know pre-modules allow you to do that you can say i want to load this particular amc bypass and run it before my shell code um and you know sandbox checks if you don't even want to do any of this stuff unless you check that you're like not in some sandbox somewhere right like not a virtual machine or whatever um you know you could essentially you know start stacking those those sandbox checks subroutines and spring models as well uh post modules uh similar concepts just it's executing after the payload execution so if you have a cleanup task you want to
you know delete stuff from disk or you know do some log file deletion or modification anything really um after your payload terminates that's how you that's something that you could implement using a post module um both pre-models and post modules are completely modular and beautiful pretty much like the rest of the payload components um you can see in here you know essentially just take all your preload modules or pre-models and post modules and kind of put them you know before or after everything else that we just talked about so i'm going to do the
okay all right so here's an example of uh well two examples of using green modules um and i'm gonna obviously have i did last uh last time i'm gonna show you kind of how they're being incorporated to the payloads first and then you know i'll uh um actually execute them so you can see them but you see this first example here we have several pre-modules loaded we have a bunch of sandbox jacks uh this one here is just gonna simply sandwich check you look for the minimum number of usbs that have ever been plugged in uh so if it's a sandbox you probably don't have a whole lot of like keyboard and mouse plugged into it
right so you know that's that's essentially gonna you know be some a way you could do that um you also have your your mc bypass here that's kind of executing at the end of that um so if you go ahead and generate that right and i'm gonna
our plaintext shell here okay example.cs project you'll see that our premodules and payload main all get included right before everything else we just talked about and they're just included up here the actual definition somewhere so if you actually want to run that just take this but this time let's use our real shell code actually call that directory hello okay and let's start a new step for our handler and yeah so now we've just essentially done all that stuff right and if i execute that from vm that wouldn't work also mg is gonna get disabled for that one process i'm
switch back oh that was not looking at hyper was it well that was useless okay all right let me go back to that um really fast all right quickly start the handling boom everything everything works okay
and finally and what we were talking about earlier yeah here's our payload man i mean here are our free models that we added somewhere up here okay going back to now going back to powerpoint all right and we'll just get that one because time is running out um okay so yeah um essentially as far as like creating drop engine modules goes um so the goal this project really isn't to provide a you know a bunch of pre-bake methods for bypassing av and edr that's not really the point it's kind of counterproductive if you know they're people who've tried these stuff like that in the past and it ends up just being a kind of a
mountain mouse game and the performance if you start releasing stuff like that doesn't last very long and um really the goal here there's two goals for this right for you know red teams the goal this project is is to allow them to gain maximum value from their payloads um by converting them into to reusable modules this is particularly true for consulting companies because they typically have much shorter time spans um during which to do this stuff whereas like internal teams can drag this stuff out over months for defenders this is also really really useful because it allows you to quickly create large sets of sample payloads from which to build a learning strategy so you know basically
from a defender's perspective what you want is data and you know something like this um particularly if you leverage an api uh you can you can very quickly create large amounts of sample data from which to derive detections and signatures and all kinds of stuff so we've got two types of modules input modules everything that's going in to the interface to generate the payload and output modules and that's responsible for the rendering the payload itself and so the input modules um they always pretty much correspond to you know one of our matching output modules and they're really you know pretty much simple um to implement just here from base class uh and then you create a
constructor which should always it yeah it's it's pretty you know self-explanatory blue dogs to be honest um major shout out to the bike leader or marcelo uh because you know without his previous work for dynamic module loading that's you know for with silent trinity and crack attack probably this wouldn't look quite as good because i i kind of simplified what he did and extracted a little more of the functionality away from the module devs and other central dispatcher which is pretty neat and output modules essentially if you want to build a corresponding output module um all that you need to do is you know defines a bunch of metadata and then just point it toward
ginger template and that's pretty much it and i'm actually not going to show you how to do this because it's going to take forever but yeah if you're interested in checking out the project it is on github um solstice drop engine and that's it i'm going to open this up for questions what have you sure um listen man thanks very much for that that was that was pretty cool um i'll leave your slide up to for people to follow you in github but then i'll i'll flip it back to your if i know you don't have a camera do you oh um is it showing it's just while i'm getting up the questions um
can you see the bottom right yeah i can see that that's that's good man we just want to see your pretty face all up close um there's been no questions in the chat although people are welcome to post questions in the chat and if you're if you're on zoom absolutely ask away um however i do want to point out there have been a couple of people have said pray to the demo gods now f in the chat for ls being missing um genuinely i've not seen a presentation with as many demos in it that went fluidly so massive hats off to you there that is that is serious serious praying that you put into the demo gods there man
no um really cool presentation does anyone have any questions for solstice
cool i i would absolutely recommend check out his get up page um go i mean you're going to be hanging out in the slack right so yeah absolutely yeah um so people can ask you questions speak to their yeah um no listen man you want to hang around in the zoom that's cool you want to is there anything else you want to just kind of wrap up you've still got about four minutes so you can you can um show something man no i think that'll do it no you're good you don't want to promote reach out shadow legends or no i'm just i'm joking with you man um listen that was that was brilliant thanks so much um
thank you thank you