Cyber Incident Command System (CICS): A people orchestration layer
Show original YouTube description
Show transcript [en]
Good afternoon and welcome to Besides Las Vegas's I am the cavalry track. This talk is cyber incident command system a people orchestration layer given by Blake Scott and Scott Frasier. A few announcements before we begin. First, we would like to thank our sponsors, especially our diamond sponsors, Adobe and Aikido, and our gold sponsors, Profit and Run Zero. It is their support along with our other sponsors, donors, and volunteers that make this event possible. These talks are being streamed live and as a courtesy to our speakers and audience, we ask that you check to make sure that your cell phones are set to silent. Along with that, because these talks are being streamed and recorded, if you have a question, please raise
your hand so I can bring the microphone to you that is going to help your question get captured for posterity. Uh, with that, let us get started. Again, welcome Blake and Scott. >> [applause] >> All right. So, this is the cyber incident command system, a people orchestration layer. My name is Scott Frasier. I've done red teaming, blue teaming, and some incident response. Sometimes I'm the problem, sometimes I'm the solution, and I am from Denver, Colorado. [laughter] >> So, my name is Blake Scott. I am a senior, a disaster planner for a community in Arizona. We're going to be talking about how I respond to disasters a lot. And so we're really excited to share that. I have uh eight years of
experience. Uh 14 local emergency declarations and we're currently responding to the North Rim uh Grand Canyon fire. So uh just as a quick disclaimer, we're anything that we say does not represent the positions, policies, or procedures of the United States government, the organizations that we work for, or uh the places that we volunteer for. Today, what we're going to be talking about was we're going to identify the problem for y'all. We're going to talk about uh we're going to introduce the solution. We'll talk about an example of the solution at work. And then we'll talk a more clearly about the systems and how you can learn more. So, the problem that Blake and I and I
have identified is when we have an incident, the people that we're stuck with are the ones that solve the problem. There's no way to go on vacation. There's no way to take a break. It's difficult to bring on additional staff. Whenever we change jobs, we run into this. There's administrative overhead. You have to learn how this company wants it and what their customers need and how this process works. It's difficult to get involved in a new company or a new process or a new organization quickly. There's not very much standardization. Additionally, this is difficult for staff safety. It's hard for a company to bring in staff if I have to leave. If I'm responding to an incident, if I have
to leave, it's hard to bring in someone to replace me. So, I just work until it's done. And that's no fun. I don't like that. It's extremely stressful and my co-workers don't like that. Mistakes get made and that's not good for the incident. The worst thing we can do as a responder is become part of the problem. We don't like that. There must be a better way. >> So, there is a better way. Uh we're going to be discussing strategy and uh operations rather than technical tactical responses. Um uh examples like the incident response and vulnerability framework still apply, but we're going up a layer. So we're going to be talking about how to protect staff safety. We're
going to be talking about um uh reducing and uh the relearning of new processes. >> We're here to drink the Kool-Aid, right? >> Yes. >> Yes. Uh we're going to be describing a system that organizes uh people to respond to disasters and use it's used by incident responders across the entire United States. Um I use this in day-to-day work, police officers, firefighters, everything like that. And we're going to ask that you drink the Kool-Aid with us. >> Well, it sounds like you're actually describing another new standard. I think there's an XKCD about this. There's 14 standards and we'll make a 15th and this will be yeah that one. >> So this is not yes there is an XKCD but
this specifically doesn't apply and the reason is is this is not a new standard. This is an existing standard that everyone already uses. We're not building a new standard. We're just simplifying one to make it a little easier for cyber security and information technology professionals to understand. >> Cool. I got cherry. >> Thank you very much. >> Thank you. All right. >> Yeah. [laughter] >> As a reminder, you asked for this. >> We did. >> You weren't supposed to pay attention. >> I want to hear slurping throughout the talk. >> Great. Thank you. >> Thank you. >> So, uh, so the national incident management system is what we're going to be talking about today. Um, there are three major
components to this system. Uh, so it is a people orchestration layer. It really addresses staff safety and it addresses transferable operations. That's a key component of the national incident management system. So, as you can see on screen, we have uh topics about resource management, command and control, and communications and information management. We're not talking about any of that today except for the command and control, specifically the incident command system. So, we're going to break this down in a really simple way so that you can engage with this If you're interested in those other components, you can go to the documentation and find out more. The national incident management system has 14 different characteristics. We're only talking about two today. Um, so
we're only going to be talking about manageable span of control and modular organizational organization. If you're interested in the arrest, you can go find that in the documentation. So for the cyber incident command system, the simplification of the national incident management system, we're doing a lighter version of the national incident management system, specifically focusing on that command and control. And we're also adding a few new roles. The the key highlighted role is the mental health officer. So this addresses um safety of staff during a cyber incident. So that way staff can make sure that they're getting breaks and that they're addressing their needs and that they can actually go to sleep. So let's talk about modular
organizational structure. This is a simplified command and control structure for cyber incidents. We start with the incident commander here at the top. So the incident commander address is responsible for the entire incident making sure that that incident goes away. They're solving the problem and they are supervising staff members that are assigned to specific roles. So the incident commander is responsible for making sure that the problem goes away. The public information officer addresses any media questions or communications with the public. That mental health officer addresses mental and behavioral health concerns with the staff. A legal officer would bring legal into the problem solving so they're not an obstruction to what we're trying to do. operations is where most of cyber
security operations exist. This is where most cyber incident responders uh understand uh the incident response to be. So operations just makes the problem go. It's hands-on keyboards. The planning section is focused on what are we doing after today? What's tomorrow look like? When you finish what you're doing today, what are you doing tomorrow? so that we can order it so that it arrives on tomorrow with the logistics section. Logistics section is like Amazon. They bring all of the stuff to operations. So operations section doesn't have to focus on buying stuff or acquiring gear or activating contracts or anything like that. Logistics does that for you. Finance and administration does all the time coding and provides
you the burn rate to your leadership so that you understand how much this incident is costing you. for manageable span of control. This is that second characteristic. It goes 3 to seven with the best being five. Um so we really don't suggest that you go beyond this and this is that supervisor to worker ratio. This is the best way to establish and understand how your team members are feeling through an incident. So only supervise five people. If you need more, add more uh supervising staff so that way you can make sure that you're managing your span of control. >> So, a quick story to demonstrate how the cyber incident command system and the national incident management system at
large would be used in a hospital event. So if in our example a hospital is working normally, patients are showing up, vampires are drawing blood, insurance is overcharging for medically necessary care, everything looks great, there are no flaws, but help desk is beginning to get additional requests for problems. It the network is down and there's something about a message about ransomware. We don't know what the problem is, but there is an issue and it is beginning to affect the IT systems. Help desk decides that they want to declare an incident. This is what a simple incident response team under cyber incident command would look like. You have a help desk manager on the top assuming all roles not pictured. So
there's surprise a lawyer, marketing and mental health officer, but underneath them doing the work is the operations section chief, the IT help desk team lead. In this case, they're working with three staff members underneath them to get the problem to go away. What is the issue? Is it ransomware? Is the network down? Is it something else? Did a lot of people just spill water on their computers at once? It could be a lot of different things. They're looking at the problem and making it go away. So, in the logistics section, we have someone with a corporate credit card. probably this is a person that's really focused on getting staff stuff space and services to the operations section so
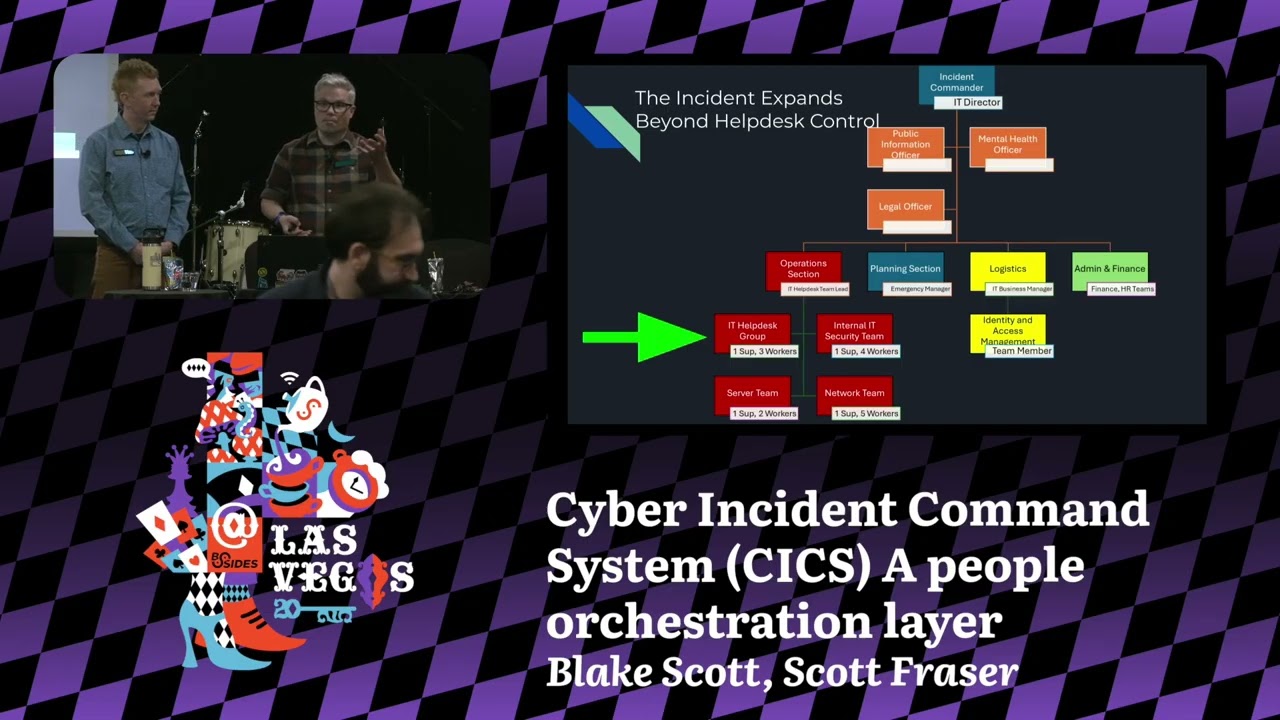
that they don't have to deal with that. We also identify an identity and access management to provision any of those credentials needed to get into the systems. That's under logistics not in operations. So unfortunately and to everyone's shock and surprise help desk could not solve the ransomware and they needed to call in additional services. it. In this example, when this the when the command stack expands, the IT director becomes the new incident commander. They're able to report up to senior leadership. They have a better view of what's happening across the org. There's now a new public information officer that can reach out and speak to the public or grandma when she calls up and says, "I heard a
terrible thing is happening." They can talk to her. Legal is now involved. They can make sure regulations and compliance are adhered to as you would expect. and the mental health officer is there and they can declare a stop to work to keep staff safe. The last thing we want is for it or any of the other branches to join the emergency as part of the problem. That is worse than doing nothing. So underneath that operations section has expanded again. There's now four teams with a single leader. This is within the span of control. The minimum is three, maximum seven, the best is five. In this case, we have the operations section with the help desk
and an internal IT security team, a server team, a network team. You may also include storage or someone else, but it's all internal and they report up to the operations section chief. >> What we also added on this slide is the planning section. So, in a hospital, all hospitals across the country require someone to wear the hat of an emergency manager. These staff members are highly specialized and trained in this particular system. And so they join the the incident command team so that we can plan on after you solve that specific problem, what are you going to do next? And so they're always looking to the future helping operations by saying what do you need next? What's going to happen
tomorrow? Okay, what resources can we bring to bear so that you're supported tomorrow? And then we also brought in our finance and administration section that's doing any time codes. They're activating any contracts. They're doing procurement rules that are required because this may be reimburseable. And so there are a lot of different ways that you might be able to actually reimburse this entire process through governmental um uh grants and and other things like that. So who's missing from this organization chart? This is the uh uh participation participation part of this. Who was missing from this organization chart? We're at a hospital. >> Chief medical officer. >> Nurses. >> Medical. Yeah, >> we heard nurses. So this is what that
organizational structure looks like with the medical team attached to it. So all we did is we just expanded operations to include the medical teams. So you got your ER, you got your O, you have your oncology and radiology teams and they're working under medical operations. Your IT operations is still there, but we added the medical operations so that they can work together. We also threw a few uh little uh sci-fi stuff that might not yet exist in the IT part. >> So the IT operations continues to exist and function. Nothing's actually changed from our previous slide. It is continuing to do their work. Whether that's with Crash Cart and the National Guard or an external contractor, they're
still functioning. But the medical staff, what they do right now at the hospital down the street is they go on downtime procedures. They're already doing this. We need to plug into the system that they are already e exercising and using, which is the rest of the organizational chart. One thing we have not discussed yet is tactics. How do you solve the problem? We have not once discussed the keyboard command prompt or operating system to deal with the issue. In this case, we're going to use the cyber security and infrastructure security play vulnerability and response playbook. You may be using agile, scrum, ned martin, killchain, whatever works for your organization. That's the tactics to solve the problem. But where do the
tactics live in the overall organizational chart? And they live underneath the IT operations section. We plug in right underneath IT operations. Nurses continue to do their work. Maybe on downtime procedures, maybe they're on paper. They're doing their work. It is doing our work and making the problem go away. So your tactics that you already use at your organization plug into this with no changes. The critical detail here is now all the rest of the kids can play with us and we can play with them. When we have this operational structure, we can begin to plug in uh plug-and-play Lego pieces from different organizations, maybe different hospitals or power plants or water plants, whatever your organization is. They can
come and play with you and with your co-workers. So, let's review. This is not a new standard. We're just adopting the national incident management system and making it a little easier for cyber security and in information technology professionals to understand. Your standard probably stinks. I have not yet seen an incident response playbook that works well with the people orchestration. Um, everyone already uses it. You're the weird one. I use it every day. Every other critical infrastructure partner uses this. All the local governments are required by law to use this system. So, um, we ask that you join us in this system. talking about that modular organizational structure again, right? We have the incident commander that's
responsible for all of the functions and making sure that the problem goes away, but they don't need to be hands- on keyboards. They can have an entire operations section that's hands-on keyboards making the problem go away. They oversee the team. So, they oversee public information, mental health officer, the uh the legal officer. Again, that planning section chief is looking on to what's happening tomorrow. We have the liaison officer that's acquiring resources, stuff, staff, space, and services for operations. And the finance and administration team that's helping code and cost and and activating any contracts that they need to do. Manageable span of control. Again, remember 3 to 7, best is five. That's the best way so that you can work with
your team members during a crisis event. This system gets super complicated. We only scratched the surface. All of these roles on screen have specific roles and responsibilities as well as task lists. This stuff can get really complicated fast if your incident is really large. This is how we put airplanes in the air to fight the LA wildfires. You have this kind of structure with tons of operational staff. So earlier this year, Blake and I had the opportunity to go present a tabletop to Blake's professional version of Bsides. It's called the National Association of City and County Health Officials, and it's a about 3,000 professionals that all work in disaster preparedness and disaster planning. They got together in San Antonio, and several
of them decided to join us as victims for our tabletop exercise. Our tabletop exercise was a complex coordinated disaster of a heat bloom in your area as well as a cyber attack against the hospital's air conditioning system and the emergency operations cent's air conditioning system. And we asked our participants to tell us what they would do to solve this problem. How would you gather resources? Who would you use where and when? 77 folks joined us in this room on at all these different tables like bides. Some of you know each other. Some of you don't know anybody else in this room. And just like that, they all agreed without speaking, without even taking a vote, with no
discussion of any type to use national incident management system to solve this problem. It blew my socks off. I was like, isn't somebody going to argue with us? Like, where's the discussion? Come on, guys. And there's no national incident management system is the way. There are no other choices. This is it. The people from Maine, New York, LA, all of them agreed. It was amazing. What that allowed them to do was pull resources from nearby communities that were unaffected by our fake disaster and place them into their community and resolve the issue without having to do a tremendous amount of okay well actually here we call it people stuffs instead of HR. No one stops that. Just solve the
problem. So, it was amazing. I was absolutely blown away. The highlight of the cyber incident command system and the part that Blake and I think is so important is its simplified language to use the national incident management system. They're already using it. Whether or not we join them, they will be using this. They're using it in hospitals and power plants and water treatment facilities and uh hospitals all over the place. Additionally, introducing a mental health officer. Our staff safety is marginal at best. It's mostly lock yourself in a conference room. We'll slide pizzas under the door. Don't get scurvy. See you in two months when the ransomware is solved. Have a great day. Uh and that's terrible. I I'm tired. I
don't need that in my life. So, how do we rotate staff out? Let's track that. Mental health officer is our way to do that. Uh legal is involved whether we like them or not. Uh so we'll put them in the command stack and they can do their best work to make sure that we're being safe for the organization. The policy compliance and procedures are adhered to. Additionally, span of control. A single supervisor with 20 employees for an incident is not sustainable. It's not sustainable for the supervisor. It's not sustainable for staff. It's nearly impossible to express individual daily goals to 20 people with enough detail to get it done. So, I've taken hundreds of classes on
this, but you don't need to. But if you'd like to start, here's two. Uh, the Federal Emergency Management Agency has provided free independent study at your pace education that's free and available online right now. Um, this ex this system is extraordinarily deep, but you don't need all of that. You can actually take what we just described right now and use it. Um, so take command of people, use the framework that we provided, define your roles and responsibilities. That's a key element. And then go fix the problem. Like this system is meant to be out of your way and usable. So we really need your help designing the cyber incident command system. It's not a fully fleshed out documentation
yet. Um, so we need your experience and we really want you to help us design this in a way that um, cyber security and information technology professionals understand. I can spin a tail of all kinds of nonsense inside of the National Incident Management System, but if you can't use it, that's not helpful. We also have our GitHub link. So, if you'd like to see our slides, that's on screen here. Um, we are asking that you join us. So, if you're willing, our contact information is here. We would really like to thank the Unsplashed community for providing copy left um photographs um uh that was made by human hands. XKCD provided us a comic that you
saw on screen and the United States government provided some images. No AI was harmed in the making of this presentation. All the pictures were made by humans. >> All right, great. Thank you. [applause] All right. So if we have any questions >> please >> a microphone. >> So I love this uh I come from an intersection of IT and healthcare uh background uh and was working at uh um academic medical center when we got hit with ransomware uh and was also part of the um incident response general incident response team. However, they are um very sold on an allhazards approach and by that unfortunately um where they struggled was they did not want what they viewed as special. Um and
they had the same thing for nuclear, they had the same thing for public health and they had the same thing for some other types of incidents where um they they were just very sold that we not do planning that was um situational situation specific uh other than within the team. But then the the place that that falls down is where you get into logistics and things like that that are that sit outside just it is doing the thing. Um so do you have experience working with that? uh selling points, anything like that. Um >> I'd be thrilled. >> I I I want to understand this situation. So, you're talking about they were unwilling to allow you to define an IT
operations section or >> sort of um it's it's more they didn't want to do like tabletop exercises and things that were very situationally specific to what they viewed as um particular hazards. They wanted to do everything as all hazards response. Are you still in healthcare? >> Uh, not there. >> Okay. Um, so >> is that related? >> So, we've done we've we're we've been doing um Dr. Evil's Revenge Cyber Sizzle is a heat dome and cyber a tabletop exercise that's in the can ready to go. It Yeah, all hazards is sometimes difficult, but if you have the if you have the materials ready to go, it's a lot easier to run it. >> So, that's what I was wondering if it
was packaged because that would packaged ready to go. We'll put it to the GitHub. >> It will be on GitHub. >> Yes, >> that's awesome. Thank you. >> Hi. So, I have zero uh experience in incident response because uh I just graduated from high school, but um >> congratulations. >> So, yeah. Um so, me and my friends uh in JTC, we we had a lot of you know uh learnings about like uh you know, military command structure and you know, a lot of problems that come with uh like manpower shortages. So what happens when you know you have an incident and you have this whole uh you know chain of command on paper but you don't have the
manpower to fill like each role uh individually and you know people have to start uh sharing and you know taking on multiple roles. What happens then? >> So you got to keep asking uh that's the only way to be safe is is to define these. So when we fight wildfires we're sending 200 people team just in operations. there's a 47 person team showing up to manage the incident. You just got to keep asking and if they are unwilling to assign resources then you say we have to go slower. There's no way for us to do this. So I I manpower resources is always really hard. Um but also don't don't um don't go so deep
inside of the structure. Um you can you if you can only staff the top stack, just staff the top stack.
I've been lucky enough to hear you planning and talking about different things. Um I think there's a couple failure modes if we expect to have bolt typhoon type disruptions in the next 18 24 months, maybe an extra year. You've talked about a couple failure modes where we come in wanting to help, but we're not speaking your language. So what happens that failure mode? Conversely, you come, you need some sort of help or you couldn't anticipate a specific trigger for this and we're not using the right love language. Like how do we not miss one more orthogonal point, what stunned me from the most in your prep was like in every other hazard, including firefighting, wildfires,
there's a maximum shift duration. Yes. Whereas in cyber security, we just work around the clock until we make unforced errors. So, um, but back to the failure mode, like my fear is we're going to have everybody motivated, willing, and able to help left a boom and right a boom, and we're going to come meet you. You're going to say like, "Go away." So, like, how do we avoid that failure mode? >> Yeah. So, to avoid us turning you away, you got to get credentialed. And the fastest way to do that is to get training. Um, we have in-person free training in your community across the entire country, managed by an emergency manager at either your city or your
county. Um, so that's like basically required across the entire country. If you're speaking this language, we understand it. I the the in interesting issue that you're talking about is volunteers coming from the outside and entering into these systems. This system will accomplish that. It's just you got to come in speaking this language or else we're just going to kick you out of the room. >> So, there is a nickname for this. Uh, this guy is named Ricky Rescue. He self- deploys. shows up at a fire with a bucket of water and goes, "I'm here to fight a forest fire." Do not be that guy. Uh so get credentialed. Show up when when you're called. That is the way
to get involved. Don't self-deploy. The self-deploying is not good. >> But I I think you're getting at a really important point is that community members are going to likely have to help their own community. But we're going to be using this like this is set up at the emergency operations center command and control and set like establishing and reestablishing community lifelines and stuff like that. So >> this is your ticket to ride. I I real quick I agree that you mentioned that the mental health officer is new at the corporate level. That is definitely the case especially with incident response. Like how do you recommend we go about bringing that conversation and who should be choosing
selecting? How is that done? because I can't see it or infosc being the group that says we found the mental health specialist officer in this role. Is that an HR function, a legal function? How how do we approach that conversation >> there? I could easily see corporate wanting to assign their um EAP programs that the what do they call them? Employees assistance programs. I could easily see them wanting to do that. Don't let them um do not let them do that because that's not effective. it it it only needs to be a small role, someone trained in psychological first aid so that they can identify a problem that's going on inside of their staff. Like we're not asking for a whole heck
of a lot here. Um a fast way would be to review the inter agency business manual. This is from the wildfire coordinating group for that work rest cycles and maintain those like set those in your contract. So this says two hours of work to every 1 hour of rest. you can only work for 14 days straight and then you have to have breaks. Go into that. It goes super deep into detail of how long you can be deployed and stuff like that. Again, it's huge. Um, but I would start there. Establish a work rest ratio so that you can at least say, "No, we're not we're not allowing this person to work 20 hours. That's insane. They're
going to make mistakes and they're going to kill people on accident." Yeah. structure. >> Does that stand up to a commercial management structure? >> So, I mean worker power like solidarity. Uh >> so I think the other thing that's going to be interesting is legal getting involved and saying okay we know that staff cannot work this long without causing harm. We are no longer willing to accept that risk. We must hire outside contractors. We must bring in outside persons or the incident pauses. We're just going to be ransomware for the next two weeks while everybody takes a break and goes outside and touches some grass. But legal may be the way to do that where they say, "Okay, you must
stop because we'll be sued for harm." It it stands up in airplanes. an airplane. >> Yes, >> I I agree with you. Like, and that's why we're asking to help start this. Is has it been I don't know. I don't work in corporate. I'm sorry. >> Lucky. >> I know. >> Legal liability. >> Yeah, I think legal. >> Liability. >> I think legal. Go ahead. >> So, uh, first I want to compliment Scott for being on brand. Same shirt in the slide that you're wearing today. Good job. >> Thank you. Thank you. >> You either have a lot of them or it's your favorite shirt. Uh so I will caveat this by saying that I have taught IC for
19 years. I am old. Um and I've used it across a variety of places. I think the challenge with this specific example in healthcare is they use Hicks. Yeah. >> And and they are their own special world and they're required to and getting that to integrate like there's going to have to be some shuffling of the cards probably. But to the mental health question, uh there's an organization called Green Cross Crisis Traumatlogy. They're a volunteer organization and you can guess from the name what they do and they are in many communities across the country. Um it's a little weird for them to volunteer for a corporation, but they could probably work something out. And to the the staffing question, when we're
saying ask for more, ask with your credit card and your purchase orders because that is how you get past that we're going to work 20 hours. You can't do it. I have sent people home. I have been sent home because you cannot be effective when you cannot keep your eyes open anymore. So anyway, there's like I love this. I think this is a fantastic thing and I will happily help you with it. >> Thank you. Great. Thank you. >> All right. Okay, [applause] >> we got more minutes. Yeah, we have more minute. We have more time for discussion and questions.
Hello. Hello. Uh I think looking at the incident command structure here is that there's a preassumption of and you may have answered this question previously in a different forum but there it seems to be that there's a prepoundonderance of human uh just bodies and ability to fill those slots and I think one of the sort of hurdles that integrating this into cyber security is going to be just the amount of people to fill that even in a most basic uh command structure you have here. you need minimum fiveish people like you can combine maybe like the legal and the mental or but like essentially you need four plus incident commander plus legal right and so you know most of the cyber
security I guess industry like you're running about that many people in moderateiz companies which is hard um and I think that is going to be a difficult problem what do you guys think about that of the sheer weird like you just need these specific people in these specific roles. Um how does that play out in your planning with that? These roles don't have to be cyber professionals. So planning section chief logistics finance and administration this top stack don't need to actually be cyber professionals. They could come from anywhere inside of the organization. So yeah, if you wanted to get a smaller uh frame of this like we can shrink it down. It's you add modules
where you need them. You don't need to have the whole thing. If you don't need finance and administration, which most organizations don't um in an incident, you just need a cost code set by some person in accounting and you pass it out to all staff. That's it. That that's literally their entire thing. You're done. Like, as long as everyone's spending on a single corporate credit card and all the transactions are tracked, it's easy. You do not need sometimes to add these larger components. you only add them if you need them. >> And I think additionally, when we use this standardized framework, it would be much easier to say, hey, we're a large health care system. We have staff that's
in maybe 10 different hospitals. let's transfer them into this one and we can get across the staffing line to deal with less than enough staff because now it's this framework you can plug into or bring in an outside firm one of the IR firms you know Croll or Google or whoever and they can go okay we know what you're using we can plug into that and be much more effective than ah yes incident framework of the day hooray and then nobody else can use this so I think standardization will be the long-term way to get there and then using only it inside the operations section. >> Thank you. >> Yeah, thank you. >> Uh the questioner asked a really good
question and I'm interested in your thoughts. I have a hypothesis and my hypothesis is running a no kidding exercise within that organization can illuminate to senior management. Oh, you know what? We have got to get a human from legal to keep us from breaking more laws. We have got to get a PIO, a public information officer, somebody from comms to help us with our reputational management. We have got to get person A, B, and C. And I I I know not every organization is a 10,000 person organiz like I get that but most organizations have corporate counsel because they don't like being sued. Most organizations have some flavor of communications expert who's ready and able to do what needs to be done. Most
organizations have a a controller, a treasurer, a CFO. So most companies have most of this and it's getting the right people plugged in at the right point to but to show that so question can this be demonstrated with an exercise with with the company do you think? >> Yes in general. >> Yeah. Yeah. Absolutely. >> Yeah. >> Showing up with a complex coordinated disaster. It's a heat dome which you cannot change. There's no way to make that go away faster. And a cyber event which you can change. Here are two things we can combine together to bring the right staff to the command structure at the right time to get the issue resolved. >> So yes, the tabletop exercises, they're
a little stranger. I think that my idea of a tabletop and cyber security and information technologies idea of a tabletop are very different. Um I've walked into a few of them like ah this is not what I was expecting. Um uh so we more or less focus on command structure. So where are we going to put the people not what tech tactically is happening inside of the keyboard or what the vulnerability is that we're attacking. We're more interested in these structures. Who can we put in this role? Where are we going to put them? And then we really, especially with the cyber incident command system, we're really concerned about that staff safety, that work ratios. I recognize that's a hard
thing. I want to talk to you. Let's talk about it and see where we can sell that. Um, but it's it's if if you're working for 20 hours straight, you're going to make mistakes. I've worked for 12 and I start making mistakes. I don't know how anyone can work longer than 12 hours. So, >> all right, I think that is all that we have time. Maybe >> we'll be around. Please feel free to Oh, sorry. Nope. Okay. We'll be around. Please talk to us after. We really appreciate your time. Thank you so much for attending. >> Thank you all. [applause]