Bypassing Next Generation 2FA & MFA Implementation
Show transcript [en]
hello everyone my name is Dr Muhammad sham ahed and I am CEO and founder of unite Athan and viix today I'm going to be talking about bypassing the Next Generation TFA and MFA implementations let's get started a little bit about me my name is Shamir ahed I am the third ranked B Bounty Hunter um I've hacked into five 00 companies ethically I'm the CEO of unite aan and BX I written a couple of books I am uh a PhD in applied blockchain security I am an MSE in cyber security as
well agenda tofa how it it evolved into MFA implementation of TFA and MFA by passing tofa in web and mobile applications bypassing MFA using logical flaws bypassing Android and iOS Biometrics authentication and bypassing mobile application MFA we're going to look at all of these uh let's see how much time allows us uh in terms of uh you know going through all of these points here's a little disclaimer here um whatever I show in this presentation and talk it's for educational purposes only but you may you can do with it as you wish and uh you know I would recommend utilizing this knowledge in bug bounty hunting and in um in your practical experiences in order to move
ahead TFA tofa is two Factor authentication it is an identity and access management security method that requires two forms of identification to access resources it's basically someone came up with an idea that there should be another password on top of the existing password but the only difference is that that the second password uh should be time based and uh you know they came up with a word called tofa and then someone came up with an idea of making those time based password tied to Biometrics or hardware systems and that became MFA that is basically the gist of both of these Technologies let's look at the tfa's working architecture basically tofa has four steps one is application authentication
second is the logging mechanism third is the OTP generation fourth is the OTP delivery let's look at the implementation of tofa so you can combine the implementations of tofa into these eight methods you have SMS you have timebase you have push notifications you have challenge you have email you have Pho and you have
Biometrics now if we were to attack to aay in web and mobile applications I believe that there are based on my research there are 10 methods that one can use to attack to a and we are going to look look at all of these methods recursively you're going to need a couple of tools with this one is a client side proxy the second is the word list the third is a proxy server list file let's look at the first attack Vector the first attack Vector is called Brute Force Brute Force attack as you all know it is a type of a guessing game where the attacker tries to guess the correct passcode or the correct
sequence it is easier to do if the codes are four digigit but it is more difficult to accomplish if the code is six digits or longer the longer the authentication the better thought this type of attack is basically let's look at this one bypassing grab uh it's basically an API called root Force profile activation code was the parameter that was required to be brute forced uh and uh upon successful attempts the content lent actually changed to the HTML page and we were able to detect that using the burp Intruder and this is how we bypass TFA and grab it was a very videly accepted case study scenario and it was very very appreciated as well um and uh you know
conventionally we have cases like slack as well where rate limitation on tofa is on one page while on the other page there is no rate limitation on TFA so in this particular case the slack app had TFA uh Brute Force protection on the main page and slack did not have tofa Brute Force protection on the secondary page uh and uh you know then this is what what happened was user basically requested a password reset token um and they reseted the password and then they were redirected to a tofa page um which did not have TFA approved for implementation then uh this was a very peculiar and a very nice case as well it was in dash Ling basically this was uh a
very well protected toofa page in terms of brot force but what they did not have was protection against the header manipulation which were which we use to bypass the TFA protection mechanism here uh the X forwarded for header it's basically uh a method using which the attacker can bypass the throttling completely um it the X forwarded 4 header is basically uh a redirection header that allows the the uh the that basically identifies the the source and the destination IP address in this case when we added $27 0.0.1 it meant the that the request were was originally coming from uh the server itself and we were able to bypass the rate limitation um by you know simply
adding that header and we were able to bypass the tofa root Force protected this one was very interesting basically Microsoft as you know is a very widely uh it has its own authenticator it has its own uh um you know it's a giant we all know that me and a buddy of mine called zero hack uh his name is lakman um we were able to bypass Microsoft's tofa um basically he was the one who did it most of the work he was the one who did it I just you know wrote the article about it so kudos to him the TFA limitation protection was based on IP address blacklisting now this was very very fun
to do because because this bypass basically consisted of sending all of those requests concurrently at the same time with no more than a 10 millisecond delay so there were two vulnerabilities that incorporated one was that Microsoft was not uh basically identifying um if the IP address is a decoy or not the second one was Microsoft was not identifying uh if there were concurent requests on a single account or not so what we did was we came up with uh we came up with a scenario where we were able to create 11 million fake IP addresses and concurrently bombard a single account with those Dey IP addresses and in the response we got a single it was
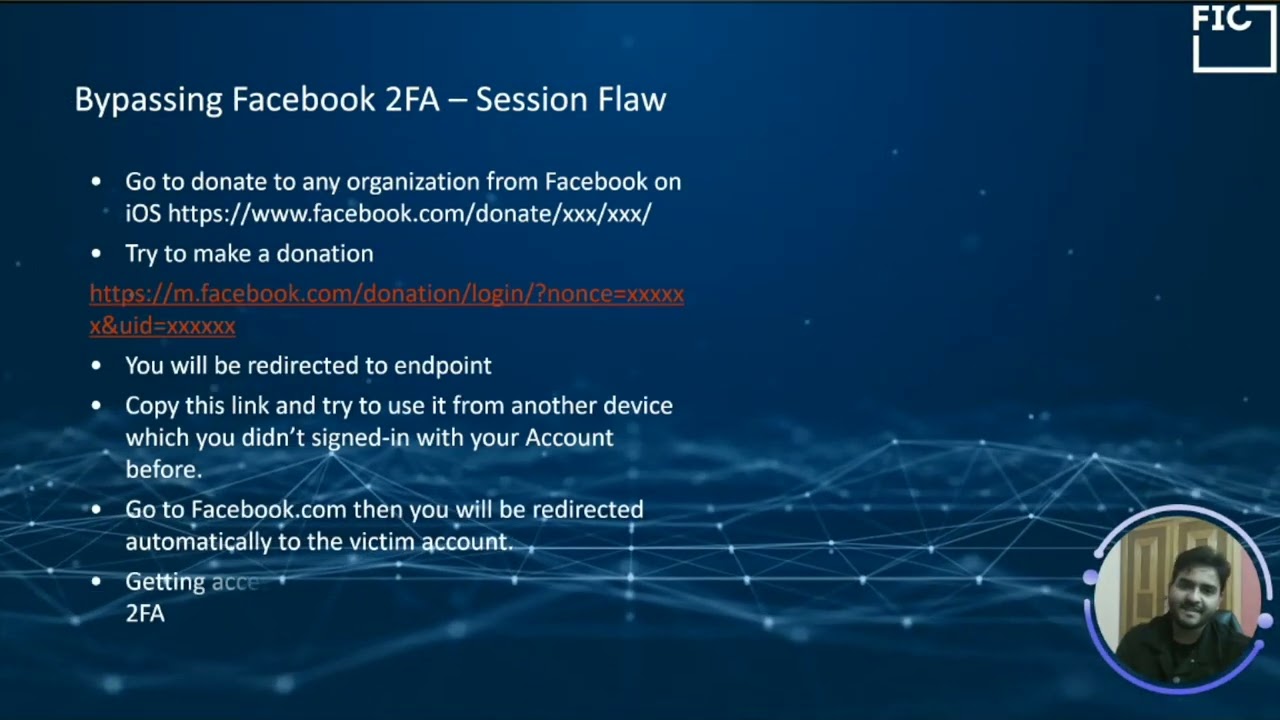
basically IP based rate limitation not an account recommendation so we were able to bypass you know the Microsoft to a f yeah this one was very interesting as well this was a TFA bypass uh within Facebook's uh you know uh architecture so Facebook has donate option right and this was funny because if you copied that donate link from one device and posted pasted it into another you basically log into Facebook I'm not even joking so if you had one account where you would just go in and somehow get the HF behind the Donate button and you would paste that into another web browser somewhere else you could easily log into that particular victim's account without even
having a password more or less to a f and then came mapbox the one of the biggest map solution providers the mapbox password reset session it was broken in a way that the attacker required access to the user's email account logs the user in but it is not prompted to to a fakeer so this was basically about the this was basically you know uh uh okay hold on I think I missed it it was a yeah we're we're in broken session management now sorry this was not Blue Force this was broken session management this was s this was a session flaw uh this was Ro Force this was a session sorry about that guys so yeah let me tell you a bit about
broken session management before we move ahead broken session management is a session based flaw where you are required to um where where you can basically log into a user session at at a point in the in the login process where you're not supposed to log in idors are a great way to uh you know I trade brok concession management um we have different other scenarios which are a great way to I trade brok concession management as well and you know um most of these ways depend on um the one way or another the most of these ways depend on basically uh uh either acquiring access to some kind of Link or acquiring access to some
kind of session for KY not as we as we talked about in Facebook this was a very widely accepted broken session management flaw and we talked about in you know uh mapbx here if a user basically reset another user's passwords or somehow got access to the password reset think they would log into the user account even if the tofa code was implemented similarly we have had cases in Instagram where a user can set tofa to secure his or her Instagram account so that no one can log in essentially to to their account um even if they have the login credentials this vulnerability basically allowed attackers to bypass toofa um and the missing checks were in
place where the user uses the secure account here option uh from the email changed notification and this was basically the the flow uh that that was in Instagram user B basically logged into user A's Instagram account user B replaces user A's Instagram uh user A's email with its own email address while you did Prof file option user a who is the victim gets and this unrecognized email and user a goes to the login activity and rebotes the session and then user a changes their account password user a then replaces the unrecognized email address from his profile with its own email address user a now sets to a face security uh for his Instagram account then user b gets an email change to
notification in his in their email and user B basically clicks on the secure account here option user B may be asked to verify if a gmail.com belongs to him which he verifies using user A's email credentials and user B successfully bypassed to a f there as creating an active user a session without any kind of to fat and you know this was the this was the video that we had in Instagram o
for
e
e
e
e e
so let's move ahead let's look at csrf we know what csrf is it's basically cross-side request forgery in which an attacker forces a victim to click on a link that is internal and that is not basically visually visible to the victim itself uh this form of uh attack is very popular in tof bypasses because it can be used to disable uh tofa uh similarly in this case the website called M Ru um um it was there was a website under its U position model called handout. Ru and basically what this website was it was missing to a fair protection on its uh on its page where a TFA was to be disabled or enabled it was very very easy to bypass
that you know uh in order to we save the CSR FP uh with the extension. HTML and then we log into the victim's browser account and force the victim to click on that particular link and there TOA would be easily disabled similarly we have something called code reusability this is a technique where the attacker reuses a certain or a particular code uh after acquiring it and you know um and they reuse the code after a certain period of time uh this particular scenario um was in a website for wordpress.com um and then you know we never navigate into the settings and enable the tofa we save the code we log out and then we can reuse that code as
many times as we want because the tofa one code was not expiring this is another um an and I think we're running a bit out of time here this is another uh very interesting scenario it is called the 2fa code leakage this is a scenario where the TFA code is leaked uh in the application responses or internal files uh and as you can see here uh that you know bypassing the apps Toof F uh leaking in the HTTP responses uh right here that once you go ahead this this was an app that we couldn't name obviously once you go ahead and enable the TFA code or you were able to request a TFA code the the tofa code itself was generated
from the client side and then being sent in that particular request so you could intercept that request and acquire the code and you know this was another um very interesting scenario and I want you all to pay attention to this because I'm going to spend a little bit of time on this to uh the mechanism of tying um an authenticator application with with uh with an account is basically based on a secret key this particular secret key is a value and it is unique for all users and cannot be rud forced uh I basically if someone can get access to this this particular secret key they can bypass any users to a f account fairly
easily in this particular particular s system what we were with the problem that we were having was if we were able to see the secret keys of other users in the responses the users in our organization uh to be fair but still other users and their their secret key was visible to us in responses and this particular uh scenario was uh that we took that we took those secret keys and we generated QRS from them and then when we we scan the QR using authenticator apps we could connect to their accounts and we could bypass uh their uh we could bypass there to a phase uh fairly easily as you can see here this is another secret key that is being
disclosed input parameter poisoning is an attack evasion technique this is also very interesting uh to a f bypass scenario uh it's called an input parameter poisoning and IP is basically an attack recor where an attacker basically crafts an HTTP request in order to manipulate or retrieve information um uh you know that uh retrieve information in a way that the server doesn't know for example in this particular scenario we had glass door uh and you know you went to glass door you enabled TFA you logged out and log in and you know notice that the OTP is asked just like in in any other scenario but the Simplicity of this is we removed the parameter itself we we just removed
the tofa code and replaced it with null characters and we were able to bypass the TFA fairly fairly easily in this case scenario similarly was PayPal now this was a very interesting and another very peculiar scenario where the attacker basically uh you know logs into the to the account and it selects the uh the CIT option to log in which is another way where you need to answer some of the questions that you initially answered what we did in this particular case was very interesting we basically removed the challenge and response Fields entirely from that request so this was this was not a code based tofa it was a it was a TFA that was based on challenges and responses
and we were and we completely deleted those challeng and response fields and uh you know we were we were we were granted access into the victim's PayPal account and this didn't even ask us for the password now another uh technique is uh called uh response uh manipulation and this is another very interesting technique where you are able to manipulate a response that is coming from the server the simplest way of response manipulation is as you see in this scenario if if and this this applies to not only tofa but other uh you know uh attack vectors as well where you are able to if if you enter a false a wrong Toof fa code it would return false if you
entered a correct Toof fa code it would return true and uh the account with the tofa authorization with would receive a similar response it would be false and then it would receive a response that is true and if you would just change false to true you were granted access taking it to another level would be that um checking here if the response of the login request was correct or not this website basically uses an authorization in token and this token is provided only if the Two ofas Steps step gets completed which is the authorization Bearer we all know that right in this particular scenario you you can see that um first of all this was also an unknown
side we enter the user ID and password and then you know we get an OTP we save the successful response of that ODP and then once we log into the wic's account we we obviously don't know dop U and so we what we basically do is we replace the successful OTP response with the false one in that particular step and in this way we are able to bypass the toofa with little tidbits of changes of course for example the the the session cookie would essentially be differentiated session cookie uh the MFA value in the session cookie would also be differentiated as well uh and you know in this scenario we can go ahead and uh bypass
it was also another uh you know very interesting scenario where where we were able to bypass toofa in in local Pakistani EOL system and this would be the the last slide of the presentation I think this would uh you know end our session so uh I'm going to show you this very very interesting video and here what you can see is in this we were able to initially acquire the encryption key from the uh application it was hardcoded they were using this encryption key to uh intercept uh to basically encrypt requests and responses um what we did was we acquired the encryption key uh and we got the uuid of the user we identified we
decrypted a couple of responses and we found out okay this this particular response means this and we were able to consequently encrypt those responses as well uh uh and you know once you try to act activate this particular wallet uh what you can see is that it's successful but then you try to enter the OTP it's not successful what we did was we we acquired the successful responses and then we changed those successful responses based on each user's uu ID and we were very much able to bypass the tofa um of that particular you know uh account and uh this is what is being shown here this is this was a salted AES encrypted version of file and uh we were
able to successfully you know bypass thep using this particular uh you know scenario and uh
situation we're replacing the responses and it will just you know it's successful and then we're going to replace another response uh and it's going to be successful as well we'll bypass the OTP here it was very interesting it was a fstep bypass and they had to change their entire authentication mechanism look at this
whoops we yeah we had to change the
SP okay by P
pass yeah we are mostly out of time here guys uh it's already been 30 minutes and we have to leave window for question and answers as well um I think that it has been a great session with you all I think that you all were amazing uh and very patient in listening to me virtually I could you know I can make out the the the faces and the scenarios that you guys are currently going through right now and I am very very thankful to all of you for giving me this opportunity to present to you to today and I will hopefully um see you in uh next year uh you guys can connect to me on LinkedIn you can email that you
can email me if you have any questions about this presentation you can get this information from the organizers thank you so much everyone else who helped organize this event and uh I will see you all very very soon bye





