Nicholas Gobern - Good Behavior is it's own reward
Show transcript [en]
all right we're gonna get started um Jake give me a thumbs up if you can hear me fine perfect so good afternoon everybody I'm really excited to talk to you about this this is going to be a relatively entrylevel discussion just about behavior-based detection I am Nicholas Gober I work as a defensive security analyst for Spectre Ops uh this talk is going to be about 20 minutes and just getting into a bit about who I am I am a veteran I worked with a defensive cyberspace operations unit before that I went to Hampton University uh where I did RC and commissioned into the army uh some things I like to do in my free time I
game a little bit I suck really bad uh I watch a lot of movies those are my top three I'm a big fan of comic books Power Rangers is actually slept on um and there's a little bit of a joke at the bottom if you don't get it you won't get it going into our agenda I'm going to talk a little bit about why I think this talk is important uh Define signature and behavior-based detections go into the theory that theory behind detections uh and then I'm going to show you an example based off of mimik cats so before I go any further I'd like to gauge the audience that I have right now so if you could just raise your hand if
you're a student okay um raise your hand if you're an entrylevel cyber security professional great and uh let me know if you work in the government or the military that's what I figured perfect so why I think this talk is important one of the things that I've been working on a lot lately is just generally interviewing for government positions meaning like hiring of them and one of the questions I always ask is what would you do to improve on a detection nine times out of 10 the response that I get is just downloading more signatures and if you don't know what a signature is It's s it's sort of a open S course snapshot in time of a specific malware
but we'll go more into that later but on top of that I just wanted to have a base Foundation of just detection Theory a detection process and just a way to understand how you can build your environment to provide the most value for your organization going into the definition of a signature based detection the way that I I like to describe this is focusing on the what of a technique and in specific example that means that I'm focusing on a tool doing something or just a specific a a specific action in this instance what you have is a picture of just hashes so what a lot of signature based detections will use is they ingest certain hashes
and they will just hash files on a server workstation whatever and bear it against that specific hash now they has its own pros and cons with that but we'll get into that in a bit with the behavior-based detection this more so focuses on the how how is this doing something how is it trying to uh how is it trying to attack your system so this is more of a abstract view an example of this would be like if you have somebody in your neighborhood who's known for picking locks what you could do is you could just change your your door which is okay but the PO the lock is still going to get picked or you can focus on the
specific behavior which is lock picking and you can do like a key code uh a drop loock one of those types of things so comparing all of these for signatures they are good for being true they are good for being something that is known because usually like if it's a hash in this instance it's a hash off known malware but the con of that is that like if I take mimic cats and I change it to Mama cats that hash has changed that's it you can't detect that anymore versus Behavior if you look at what pimpy cats does the how in this specific instance we'll just look at Elsas dumping then you can get a
better detection because you're focusing on a specific technique not just a specific action being taken so the downside of behavior-based detections is that they're not they require a lot of work and not just a lot of work upfront but they're ongoing and they have to be tailored towards your specific environment with the signature ones you could just download them plug them play them so that's good but the accuracy of that the efficacy it's not always the best so going into detection Theory we have this thing called The Funnel of fidelity and the main point of the funnel of fidelity is you want to add an exponential rate lower the number of detections that you have so that it
provides the least amount of effort to make the best decision what that generally means is if you're working with a seam or any type of thing that adjusts logs alerts whatever you're going to have a lot of events like for here uh hundreds of thousands of events is nowhere near an exaggeration for the lab that you'll see soon I had 12,000 events over the course of 24 hours off just what was in my house so that expanded across 500 workstations a th workstations it can get very exhausting so one of the things that you have to do is it's a bit of a balancing act where how can I make sure that I'm getting things that are legitimate
concerning and are not overwhelming the analysts and one of the ways that you can work with that Balancing Act is what we have is the detection Spectrum so on one side what you have is the precise detections and these are a low false positive and a high false negative and you can see the definitions of what both of those are above but on the broad side you'll see that there is a high false positive rate and a low false negative now moving into like working on The Balancing Act of that the precise ones are signatures because signatures are generally going to have high true positives but low false negatives and the downside of that is that if I'm looking for a specific
thing I'm going to find that specific thing but I'm going to miss everything around it versus a fresh off the booat uh broad behavior that one is going to be a bit more General so you have to do a bit of management to find the happy medium so that you can have an actually efficient detection so the questions that I ask myself when I'm working on this is what am I trying to detect what should normally access this what does this tool abuse and what Telemetry do I have to look at this now before I move any further uh please raise your hand if you've never heard of mimic ATS before perfect so we're going to develop a detection
based off mimic hats and this specific instance we are going to look for Elsas dumping so Elsas the local security off Authority subsystem Service uh one of the things that it does that's going to be abused in this is it uh manages the 80 database lookups which include authentication and replication meaning that this could be used to dump the will dump credentials that could be abused later on and this is the thing that we're going to actually look at so Elsas is rarely accessed by Windows native binaries and above you're going to see a handful of them that are native to it um on a Enterprise level this is important so that you can filter these out so that
you can focus on relatively true positive ones but you'd have to keep in the back of your mind that if you're filtering these out that that could potentially be abused later on so you have to do a bit of risk management for your specific environment uh as I said before what does this abuse this is abusing Elsas and the Telemetry that we're going to be using for this specific instance is cismon and windows event logs um is any is anybody not familiar with either of those you are so cismon is a system event monitoring system it's what it's like a it's a Windows native audit logging tool and it just looks at specific events happening on a Windows
Event all right so discussing some of the malicious actions that were taken we used the mimicat on disk version and you'll see you can barely see it but the commands are mimic cat.exe token Elevate which escalates the Privileges and then SEC SEC Ur LSA log on passwords which dumps up from LSS two other things that were done was I reflectively dumped passwords using Powershell so the correct number of events that we should find at the end is three key events that I'm going to be looking for in this instance is event ID which is a process access this is the main one that I'm focusing on because this is seldom actually used by a lot of
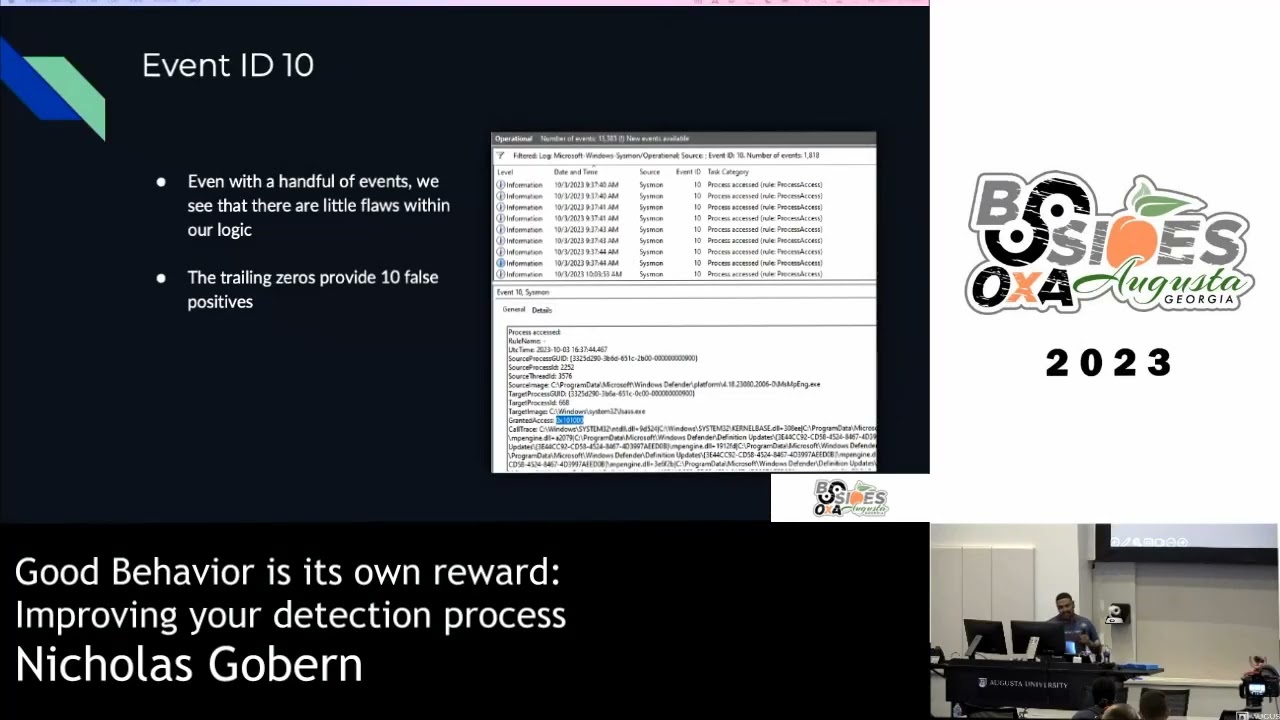
other systems so it's relatively unique to malicious processes uh big Aster on the ls key uh extra points if anybody can name a potential other access code that might be used for detecting this Max correct would you rather have I'll get it with you afterwards uh another one that could be used is 46 56 which is a handle uh showing that a handle to an object was requested so when I was using event id10 uh I started with 12,000 cismon events now there's a a whole bunch of other windows event long events but this was just tailored towards 12,000 cpon within a 24-hour period on just my home network tailoring that towards event id10 that narrow down to
1,200 uh and then the events with the uh 010 or 0x1 010 brings it down to 21 so this is a new amical representation of how the funnel of fidelity actually works so you start with a large about of events where you can if you like wasting your time just go in and individually go through all those or you can find find one trait which exponentially drops a number find two traits exponentially drops it again now this is a very wide net but at a high level makes it relatively manageable for an analyst uh this is the choppy Powershell script that I put together to Define this um but what it is happening is it's
uh pulling cismon event logs um and selecting the object property of granted access for the specific strin of 0x1 010 now as you can see there's 21 events that comes out of that but the issue with that was um within just the one Z one0 there were 10 false positives because of the trailing zeros one of the things that I found out about that was they were specifically tied to a uh a specific process in this instance which goes into the calculus of one of the things that that will go into creating the detection but as I said before a lot of these things will have to be tailored to your specific environment so with the handful of ents
you can see that uh here similar uh as the previous Powershell script but the string that we're looking for is the one one Z with the following tring zeros and that matches on 10 alerts so getting rid of those 10 it leaves you with 11 positives but I go into uh I go into it again and I identify that even with the proper Grant code it's being tied to msmp which is Windows Defender and I thought that that was weird particularly uh but the key point for this is that that's eight false positives that being attributed to this and when I was looking at this myself I I realized that if you go back to the
previous slide uh you you might not be able to see it but it's msmp which is the same process so for some reason uh Windows Defender is getting the same access code which is throwing off our results one of the things I decided to take a look at was the same results but from a different perspective so I looked at event ID 4656 and I got the same results where Windows Defender was popping uh tracking all this information but it also was simultaneously giving me the three true positives that I was looking for so I went to everybody's favorite scene Splunk uh and random question anybody here does not like spunk you got the prize
congratulations even with the relatively so I plug the same general idea into Splunk and as you can see this is a very like down and dirty search but the thing is is it's tailored to my my specific codes it's event ID 4656 and I decided to exclude Windows Defender from my search and I was able to get the three false positives that I look for and the thing that's good about this is that one it works does it look pretty or the three true positives I'm sorry thank you so there are the three true positives that up meaning the two power shell and one being run on disk and it's not pretty but it works and
unfortunately a lot of companies have a similar mindset if it works we will keep working on it and uh one of the things that I would like to add for jce search is just one pulling out the data field so it's a little bit easier adding sysmon to my search not just the event ID uh adding the 1410 that Max mentioned so that it could be a bit bit more granular but at the end of the day this it works and that's really what is the most important and that's what leads me to like one of the biggest complaints that I hear about why a lot of companies don't move towards behavior-based detections is they don't have the time or they don't
feel like they have the resources if you have pow shell or or any form of telemetry you can just work with what you have um another thing is you can build your detections like a mindfield and then work based off that MGA mindfield means if you lay out the miter attack framework you focus on one technique of each thing and as long as the enemy cannot complete their attack campaign then it's a relatively good uh sock in this instance another thing is you could just build it over time or uh a detection could be an output for threat Hunts uh or you could leverage public research that's out there so as you saw in the previous ones in the
bottom left we used hunting Elsas which was pulled from Splunk there's a lot of information that's out there so that you could just throw the throw the detach together or Spectre Ops training and uh that you or just uh make sure or you could work on some of these things where as long as you understand understand the technique you can help creating the detection around that um another thing that you could do is just focus on just very common techniques such as the process injection Elsas things like that uh and without that I'm going to see if anybody has any questions before we go
on all right yep
so if I hear your question correctly you're asking um if you grab signatures that are publicly available how can you combine that into a behavior based detection
okay so what con what constitutes behavioral and how can you limit your false positives so what constitutes behavioral um separating it from a signature one so what constitutes behavioral is just the actions that are being taken meaning you could look at you could look at that uh we'll take a malicious Powershell runner for examp example in this instance you know that there's going to be specific API calls that are being taken uh you can look for process Alec memory for example uh that's a specific API call that's commonly used in uh malicious Windows documents to act as malware to start for the Callback uh the main thing that you're going to look for is just
not you you're going to look for like that action specifically um and if you can limiting the positives is kind of just where the Theory comes in where it's going to be have to be done over time so there are things like purple teaming red teaming those type of things if you have the malicious software or the malicious activity you're going to have to just over time iteratively uh tailor out the FSE positives towards your environment uh it it it is is a process but that is the way that it would be done any more questions all right thank you for your time





