HG - Penetration Testing Experience and How to Get It
Show transcript [en]
oh good afternoon and welcome so my talk I'm giving today is pentesting experience and how to get it so I'm Philip Wy I have my cissp OSP and gwp C certifications I'm a security solution specialist and evangelist at Sai uh I've been working in offensive security for over 10 years uh spent 5 years in Consulting worked as an internal pentester led a red team for a global product consumer product company I worked as an instructor I used to teach at Dallas College I taught uh pentesting web app pentesting there and I'm also the concept Creator and uh co-author of the pentester blueprint which is based on my College college lecture from Dallas College which I gave
at the each uh the beginning of each semester telling my students about pentesting and what it took to get into pentesting and so by the end of 2018 it turned into a uh conference talk and I presented that at bid DFW in uh Dallas Texas and it was really kind of cool because when I gave that talk uh there were some people from our community I offered my class as continuing ed and uh credited because I knew there's a lot of people in the community they wanted to learn the pentest but they didn't want have to worry about transferring credits taking all these prerequisites to get in to the course so really had some really
cool people from the industry so when I gave that talk at bides DFW in 2018 some of you may have heard of uh Juno from infosec Twitter she works for Bishop Fox she was one of my students so she sat in on that that talk I knew her from the community but I recently found out like last year this year that that's what motivated her to become a pentester so she end up taking my class the next semester one of my best all-time students a total rock star she's part of cult of the dead cow now and and doing some really cool stuff in the pentesting world uh one of my favorite moments was uh when I was the the red team lead at
the global consumer products uh manufacturing company I had a pentest done so we did all the network pen testing and red teaming but we outsourced the web app pin testing we had uh different Consulting companies do that so one of those pentests I had uh Juno and another former student one my very first students were on that pinest they were working for the consulting company so to see the email come across them getting ready to start the testing was kind of a a proud uh teacher moment to see my teachers my students go on to be pentesters and kind of a cool fact most of uh the people that went through my class that got jobs were were mainly
women that actually got pentesting roles so there's quite a few in that class that went into pentesting or went into it years later uh I had another student that was taking my class another one of the rock stars like Juno that was a uh junior in high school and he's taking college classes so he took my pen testing course and now he works at one password in uh security research there he help create one of the uh some of the Technologies for the key exchange for their for their their app so it's it's a lot of fun and I really love mentoring and teaching I kind of learned in 2018 I've always been very competitive always
trying to be the best Fester I could be but all honesty I never thought I was the best I tried to be really good and then in 2018 I decided to focus on mentoring teaching and helping others so it's been a good change it's something I'm a lot better at and one at the time when I started that I thought you know the world needs lots of teachers and mentors and so it's been a fun fun Journey I've got to meet a lot of uh people through that it's been very fulfilling so I'm also a a podcaster so I have a former podcast called The Hacker Factory there's 118 episodes out there on the podcast platforms but
recently went independent with the Philip Wy show same similar format but I'm also doing video now uh before it was mainly just geared towards people's stories and advice and get in the industry but I have different people sharing Technologies and we get into some discussions about content creation because you'll see in this presentation later on one of the things I highly recommend when you're trying to break into the industry is content creation so that's a good way to get noticed recognized information that you can go beyond your competitors that are applying for that pentesting role to show them some of the things you do that are above and beyond what that role entails so I always like to share my story of
how I got into infin of security and part of this is to motivate and encourage other people so when I graduated high school uh I didn't know what I wanted to do with my career I didn't take High School seriously I love science so science was the one class that I would take I didn't have to study for the exams because I took notes paid attention loved it when I was a kid I was always checking out science books instead of uh you know novels and so forth and fiction so that's what I was really into but when I graduated high school I didn't take it serious enough so my grade point average was too low
based on my college entrance exam scores I could have got like eight references from teachers and got into the school but I just really wasn't into it really didn't know what I wanted to do so being a powerlifter at that time still still a powerlifter but uh back then my my classmates told me say why don't you be a pro wrestler because where I lived was a big uh wrestling area in the Dallas Forth areas because the Von Erics were very popular there so I went to wrestling school and so I got married and I had to have a job that had benefits CU as a pro wrestler you don't have life insurance or health insurance
if you get injured that's out of your pocket and I wasn't you know when you start out they refer to you as a jobber or a job boy so I was paid to lose I was paid to make the superstars look good I mean some of the people I wrestled were like Mick Foley uh the rock and roll Express The Fabulous Free Birds uh some of the The Rock Dwayne Johnson's cousins wrestled as a Samo and SWAT team and so I had to change jobs and so I had worked in retail sales tried to go into the military but for health reasons I couldn't get in when I was 15 uh my brother accidentally shot me so since I
had a bullet my body the military wouldn't take me either one branch wouldn't take me because of the bullet or other branches wouldn't take me because I was a powerlifter and I was too heavy so I gave up on that so I tried retail sales which was probably one of the things I enjoyed the most cuz working with people but then also tried construction which I absolutely hated roofed houses put up fences and for me I've got to have a job that I enjoy I mean because my first year out of high school I had 20 year 20 jobs my first year and that's because none of those jobs I liked so I had to find something
I was passionate about so one day I was home at this time I was working as a jewelry salesperson at this jewelry store and I was always like the top not top salesperson either number one and number two the family that hired me on to work in this store wanted me to be eventually an assistant manager move into management but the guy that was a manager of the store had someone else that he had considered for that role and they were highly qualified and deserved the job just as much as I do and I understand that but what I decided is I needed to acquire a skill where I could get a good job regardless of politics
you're going to have politics everywhere you go or sometimes not even politics it's just someone thinks this person is another candidate doesn't mean it's right or wrong so I knew I had to acquire these skills so since I was working jobs where I was home during the day one day on daytime television they were advertising this trade school that taught CAD drafting so I liked drawing when I was younger I took some drafting classes in high school so I decided to give that a shot so when I became a cad drafter I was exposed to the world of it when I went into CAD drafting I had minimal to no computer skills probably the worst in my class by the time I got
out of of CAD school got into the field doing drafting my computer skills surpassed my peers I would find uh just different features in the latest version of AutoCAD that my peers that have been drafting longer than me didn't pick up Windows 95 was fairly new uh I was able to get like Windows 95 printing to work with the noville network whereas one of the the IT people there which actually was an accountant that that did it because the main IT staff was two hours away he couldn't figure it out and I did and it was funny the first time I ever got called a hacker was because I was working on systems but I was trying to
get things to work and I was successful so I decided because you know the company had one of the previous companies I worked at they had a a consulting company come in and so as a drafter I was making $15 an hour we're being buil out of $30 an hour so this consultant coming in building you know $15 an hour so I knew he was making you know more money than what I was and it looked a lot more interesting so I taught myself how to build computers took a novel Network course and so I worked as a CIS admin for 6 years and then in uh January 2004 I moved into infosec and then about a year and a half
later the company hired a new ceso the ceso came in had a better idea of the way security organizations should be run and set up so fortunately I got put in the appsec team and being on the ABC team I got to find out about pentesting I was managing third party pentests I was performing vulnerability scans with web inspect and app scan and so I really got interested that so in 2012 I got laid off from my job and I applied for a role at Verizon as a pentester Consulting as a pentester and one of the things that helped me on that was I had vulnerability scanning experience some security experience at absec but what
really won over the hiring manager is I was self-taught on a lot of things he was a person that believed in building not so much learning the hacking stuff if you know how it works then it's going to be easier to hack into it or secure it so from that he took a chance on me so I went to work there spent about 5 years as a consultant got tired of all the travel and then moved internally so if you ever get the chance to do Consulting that's a really good way to get a lot of experience pretty quickly so as an internal resource uh for a bank I used to work for we got four weeks to
do a pinest whereas a consultant we only got one week so you had to do things quicker so you're doing so many more pin tests so many different uh variety of pin test all these different environments cuz it's not always the same company so you're able to pick up a lot of experience quickly so I went into the internal side uh also worked as a red team lead for a global consumer product company and so that's kind of where I got started I like to share the story because you know you hear of impostor syndrome or lack of confidence I never thought I would be using my mind for a living I always thought it'd be
the physical because the pro wrestling you know I used to be a pro wrestler and back in my pro wrestling days I actually Wrestled a 750lb Bear so I never thought I would do that and so I like to do one of the things I like to do is encourage people and that's one of the purposes of my podcast a lot of times people just need to realize that they can do it uh when you think a good analogy is a sports analogy you look at any records Olympic records Running Records uh distance and time or whatever or even weightlifting competitions any kind of sport sometimes those records stay there for a very long time but once someone
breaks that record you notice how all of a sudden it starts getting broken easier it's because someone proved it could be done it wasn't because people couldn't do it is being proven that it can be done so that's kind of the purpose of my podcast and one of the things I hope you take away from this talk is you can do anything you want to you just have to put your you know put your heart into it if it's something you're passionate about you put the work in you will succeed so kind of just to briefly go over what pen testing is so it's assessing security from an adversarial perspective using uh hacker tools and
techniques also sometimes referred to as ethical hacking but truly ethical hacking is really the hacking part of the pentest so you can do ethical hacking not necessarily do a pentest uh but this is some of the terminology that you'll hear so there's different tools that you need to get experience with and then also too you may hear about uh red teaming and Pen testing there is a distinct difference because real true uh red teaming is adversary emulation so you're going in trying to find a foothold in sometimes it requires social engineering or uh you know fishing sending a fishing email to gain a foothold in so you're looking at one way in you're trying to go
undetected uh you try to maintain access so you're trying to emulate a real world thread actor so sometimes you'll actually be using uh some of the things you see on miter you look at some of the APS and you emulate that so one of the things you can do is look at popular APS that affect your industry and base your attacks off of that with pentesting you're trying to find every vulnerability that's exploitable and make sure you validate that they're vulnerable and then try try to exploit them exploit anything that be exploited to make sure you know what can be done if it's exploited anything during post exploitation but they're both both important so you really want
to start out with the pen testing and as you mature add in adversary emulation because you can get really secure but maybe you're easily social engineered or fished because some of the fishing tools out there uh companies are using less pentesters that do it they just get some package that sends out these random uh fishing emails and what those do they they check for clicks they're not really seeing what happens if someone clicks on that length you really need to see what happens past that can someone get initial access into the organization you know sometimes it may be really secure but if someone with the right access clicks on it then they can get access to
the environment so they're very important so with the pen testing you're making sure you're find all the vulnerabilities trying to exploit those and document that with the adversary emulation then you're just trying to see if you could emulate a breach you're also testing to see if the Defenders are able to detect and protect against this is the technology protecting against this so someone clicks on that email are they able to gain access or you so you're also uh testing the security and one of the quotes I like to share with red teaming is the founder of Dallas hackers Association wifall uh his description of red teaming is a very simplistic form is the red team tests
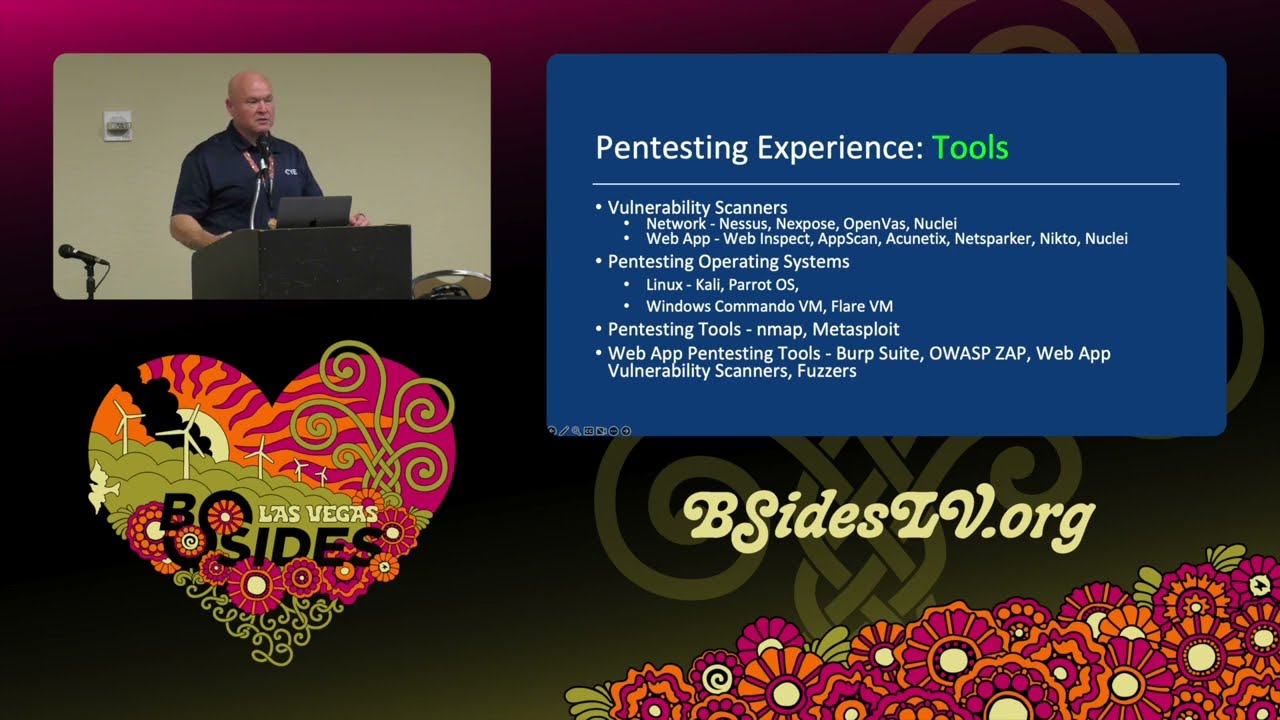
The Blue Team so that's a really good thing to keep in perspective for that so some tools that you need to to to get experience with to be a pentester is vulnerability scanners so mind you you still want to learn how to vulner to manually test for vulnerabilities but you also want to use vulnerability scanners so you got Network scanners nessus nexos qualus is another one not L there open boss and nuclei are free and open source vulnerability scanners but one of the things with the vulnerability scanners is as a pin tester you're so limited with time so you need to be able to do things quicker uh one time there weren't vulnerability scanners and what
vulnerability scanners have done is help help uh pentesters scale their work and that's one of the things too that I see coming with AI I'm really looking forward to some of the tools that AI produces uh because you look at tools like metas sploit trying to obus gate your payloads I can just imagine what you know you can do things with chat GPT to do that but I see some of the next generation tools making that even easier so for your web app vulnerability scanners web inspect app scan acuns net sparker NCT toe and nuclei and so there's also vulnerability scanning capabilities in the commercial version of burp site the professional version and then also AAS app does some
vulnerability scanning so you need to learn operating systems for pin testing and also this is a dual purpose so you need to understand Linux and windows because most of the environments you're going to encounter will be Windows Linux or Mac OS so understanding how to use those are going to be very helpful if you get C command on access also referred to as a shell to a system if you know the operating system and how it works you're going to be able to to do a better job because if you if you have to Google everything it's going to take you a long time so understanding uh pin testing uh operating systems such as Cali Linux and windows is going to help
you uh do a quicker job so you don't want to have to do all the all the different U all the Google searches to try to find that so having that is a CIS admin level so you're able to connect to to the network able to understand basic tcpip Network and so forth and so other pen testing tools like inmap is a very popular one it's a important service scanner there's a lot of really good plugins for uh inmap that you can actually actually function as a vulnerability scanner sometimes when the latest vulnerabilities come out they create a script to look for that so like log for J came out they came out with a
NSE script that you could quickly test everything in your environment to see if it's vulnerable and so metlo is an exploit framework so most of the exploit Frameworks don't have a free version so but Metasploit is a really good one uh so understanding how to use these tools and then web app pesting tools like burp site zap and then the web app vulnerability scanners as we mentioned earlier in this slide and also fuzzers learning how to use these so when you're learning how to use these tools when you're going through a job interview you're able to discuss that because someone may say ask if you have experience with burp Suite maybe you don't have it professionally but maybe
you've done bug Bing which that would be professionally or if you've done a lab environment if you're able to answer the questions for that a lot of times that's that's uh that's good enough so the skills you need is networking uh operating systems is mentioned you need to know that is assist admin level hacking and pin testing so when I got into uh pin testing this is the piece that I didn't have I didn't have the hacking piece I didn't know how to hack so I took the ocp certification so reverse engineering is another important one too so I've seen cases where I've done pen tests for companies and went in and found like a
Java jar file and is able to reverse engineer it and sometimes they have hard-coded credentials in there like database connections username a password and sometimes this is a way to get in the system uh so be able to reverse engineer is a good thing and this doesn't take this take doesn't take a ton of effort it's doesn't it's not as intimidating as it sounds also you can find some good stuff in in like APK files for Android apps sometimes you may find this on a website sometimes you'll find apis in that so uh a tip that I hear from a lot of bug bounty hunters is to look for those apks reverse engineer to look for any kind of any kind of apis
that are in there and as far as getting the skills it depends on what you're wanting to do so if you have an application background then application pin testing may be a good route to go and so this is going to kind of determine the skills you need what area you're wanting to pentest if you have like an ICS iot background then that's going to be valuable then understanding that and learning how to pinest those environments so you need to get the hands-on experience and what we're going to cover in this presentation is just actually uh environments that you can use for educational reasons that help you gain those skills so mind you even if it's a
lab environment you write up uh hack the box or try hack me box you do a write up on it do a walkthr of it you're able to prove that you're able to use these pin testing tools and that you know how to pinest and even though you don't have the professional experience if you can demonstrate that that goes a long way because you take some people coming in may have like a c or pentest plus but they really don't know the hacking piece of it if you're able to dist you know able to show people demonstrate that then that's going to help so some good options there are ctfs you hear some people that put down
the OCB saying it's CTF like but the thing about CTF ctfs are not easy sometimes they're not real world scenarios it could be something more difficult like going through the ocp it could be more difficult than what you would see rural world uh but doing hack the Box try hack me and then creating your own uh lab using vulnerable VMS is a good way to to get experience and so getting that experience you're able to prove to an employer you know how to perform a pentest you're able to answer questions during that job interview and so to get real world experience and professional environments stuff like bug bounties are great crowdsource pen testing these are
even better options so like bug bounties uh you're paid per bug you find and one of the things I like to describe there if you really get good at bug Bounty and stuff like that you're going to be a better a better pentester because as a pentester you're paid for the pentest if you don't find any vulnerabilities you still get paid with a bug Hunter it's like someone that fishes for de feed thems or fishes for game game if so if you're going out there just doing it for fun if you don't catch a fish you're still going to eat that night but if that's the way you have to feed yourself you don't you're going to get better at
it you're going to try harder so these are good ways to learn and some of the best uh pentester I've seen do bug bounties uh bug crowd hacker one and synac do bug bounties but then you have some pentest as a service and these are ones I really highly recommend like Cobalt so Cobalt is nice because you get paid for the pentest last time I heard it was like $1,500 per pentest I don't know we got an expert here and she validates that that's true so this is kind of a better option in my opinion if once you get those skills down you learn how to do a pen test you you pass their skills of Val ation then you're on their
platform and you're able to pentest so you're able to get real world experience so once you get that Real World experience it's going to help you to get a role as a pentester uh you know opposed of not having the experience and sometimes these are easier barriers the entry even like synak has an online uh challenge you go through if you got certain certifications that bumps you up in the interview process so these good places to start and like bug crowd and hacker one doesn't require that you have EXP experience you just sign up for the platforms and you start off right away so it's a good way to get practice but don't get discouraged if you find
duplicates because you find duplicates that means you're still finding vulnerabilities so if you're performing a pin test on your own then you're actually finding actual vulnerabilities and you can also do pro bono or lowcost pen testing for nonprofits or business you know a mom and pop business that needs some security work maybe you're able to do one for free a pen test for them for free either that or low cost so if you're doing it at low cost you're getting professional experience you're actually paid to do it so there's something there maybe it's not that much but uh still you're getting something for it and as you get the experience to build that up you could actually have
your own consulting company then maybe you get into where you're uh getting jobs that are paying a decent price but the pro bono work works really well to you because you can find churches different religious organizations nonprofits that could use a pentest and you're able to do that for them and another thing you're doing there when you're doing the pro bono stuff uh the security Community people that involved in the industry they like to see volunteering and helping out so that's good to have on your resume and another one I really like to emphasize too as far as trying to get experience is getting common vulnerabilities and exposure cves so this is one of the
things that I see more value in over a certification although if you go through the ocp it's tough and it proves that you can do a pen test but finding a doing finding cves you're able to find vulnerabilities that didn't previously exist which even a vulnerability scanner doesn't find that so you're able to find cves which is basically kind of like a zero day because no one's discovered it yet and you're able to document this on your resume or your LinkedIn profile so really what brought my attention to that is the the mayor also goes under the uh Joe heli calls himself the mayor he did a medium article on one night his board and found two CVS so
basically he was downloading free and open source software for like Hotel registration systems installed it on his Home Server did a pentest against it found vulnerabilities wrote it up submitted it and he got cves and so you can put this on your resume or your LinkedIn profiles and that's going to help you get that job you're able to actually to find vulnerabilities and these are more difficult to find than uh you know running a vulnerability scanner and finding stuff that exists so that's and in my opinion that's a lot better so cve is basically a database that that's kept by like miter that they keep all these cve numbers when these cves are are detected so what you can do with
these is you can go in there take that cve number put it on the publication section of your LinkedIn profile so that way people don't have to just trust you that you got this cve they can click on that link they go to the vendor site and they see the cve the details of the cve and your name associated with it so some really good articles on that uh Bobby cook has a article on his blog that's called called beginner's guide to uh zero day and CV abck research so Bobby was going through the OS oswe certification through offensive security and an advanced web app pentesting certification so to prep for that he was doing some uh looking for cves and then
Joe hel has his article that his board one 19 found two cves so if you go to his medium page you can find multiple articles so since he did that he's done several past that he does a conference talk on that topic but I think that's a really good way that people Overlook I mean I'm a pentester I don't I've done pentesting for over 10 years and I don't have any cves to my name but I think it's to me I would be more impressed with someone with cves than a certification so demonstrating the skills so you've been going through getting this experience so how are you going to demonstrate that so if writing is your thing uh do writeups you could
do articles blog posts on GitHub medium or your own blog and these are things things that you can put on your resume put on your LinkedIn profile so people can go through if they're looking through your profile they can see some more in depth information then just I've got this certification I did this or that you're able to uh you know kind of show people writeups so if you find a hack the box that you you did a uh were able to solve you can do a write up on that or or you know and and keep in mind the different platforms because like try hack me there's certain boxes they don't want you to re reveal the answers to so
be careful what you're doing that so you write this up you can create sample pentest reports uh and that way people can see that you can write a pentest report see the way you think detail that really well and also if you if you are writing any scripts that you could put that on your GitHub to as well and as far as trying to demonstrate those skills uh if writing is more of your thing then gravitate towards that and the CV cve IDs as mention you can put that in your resume or LinkedIn profile and also tool and Tool techniques and walkthroughs on YouTube so if you like video then do video walkthroughs if you
don't want your face seen online you don't have to turn the camera on just show the screen so I'd recommend find the platform you're comfortable with because content creation is a great way to get experience and get exposure we're kind of living in what I would call the Golden Age of content creation for cyber Security Professionals I've seen a lot of cyber security professionals that have started their career based on they were studying and they were creating videos to kind of show what they were learning in their journey to share with others and so a hiring manager can see those videos and see your thought process and see your your Hands-On skills and see some proof of
that uh so also like scripts or programs that you write that you can put on GitHub so as far as the content creation find an area that you're comfortable with you know speaking at conferences are another thing speaking at meetup groups there was a recent college grad at our DC uh 214 meeting in Dallas that had just completed their degree that they were doing like a a talk on malware analysis and there was a hiring manager from City Bank in the audience saw that demo asked for a resume they basically already had a technical interview they could uh vouch for their skills and so they got an interview with the company and then end up getting a job uh so
going to these conferences and speaking doing demos of the stuff as a way to show people not only your your technical skills but your soft skills uh a lot of cases you're going to work for a company you may be presenting uh you know to uh clients or if you're you're doing you're a pentester then you do the debriefing uh uh meetings where you read the the pentest report so be able to do this stuff is helpful so uh you can do video content creation streaming YouTube or Instagram writing speaking at conferences and cyber security meetings so professional networking so this is probably one of the biggest things there uh most of the jobs I got in cyber
security since 20 2 my first job was actually applying for a job but I think I've only actually applied for jobs that I wasn't recommended for people didn't reach out to me so get to know people when you're in at these conferences make it an effort to meet people talk to people with someone that you may know that you've seen that may have been in the industry for years don't be as afraid to talk to them because most of them would be happy to help you out and so just network with people when you're going into your meetups don't sit in the corner uh if you're introverted you know you're amongst your crowd you're in your
tribe they understand this when you you're talking to people with similar interest it's a lot easier to talk to so uh do that get that helps get your name out there people get to see your skills uh one one of one of the people from our community had recently graduated from college and a lot of people reached out to me for junior pentesters since I was teaching pentesting and one of the people I knew from our community I knew they wanted to be a pentester so I was able to refer them and he got his first pentesting job and that's because I knew him in the community he talk to people let them know what he's
looking for so people knew him if he'd just come to the meetups and be quiet no one would have known and you know he probably would have missed that opportunity so there's other opportunities there to like your online communities like Discord slack Reddit and so forth and in Twitter whatever they're calling it this week uh I still haven't give up X yeah I really think I could think of other things to call it you know he W Elon walked in with the sink he really should have walked in with a toilet cuz that's kind of where it's went but fortunately it's doing okay it's doing okay it's still a good source it was really weird to see how
many people left Twitter because I used to monitor my follows and unfollows because I really put a lot of effort in my social media and I noticed at one point I'd lost like four or 500 uh followers I looked at this unfollow app and actually people deleted their accounts but people are coming back too so so those are good really good places that's where I get most of my information infos Twitter is how I found people in the community so that concludes the presentation so if anyone has any questions I'll be happy to answer your questions yes so I'm already creating content but I'm having trouble get do you have any okay so the question
was uh they're already creating content and asking how to get views so if you can find anyone to collaborate with find people that you know have a good following ask them to to share the content find people that you can help we I'm a member of a Discord and it's a content creator Discord and we share for each other so we ask each other find people to help share that and if you could ever get someone you ever have guests on or something you could collaborate maybe someone else that's got a bigger audience get them on and do that so really just kind of really sharing on social media and then maybe if you're remember of some Discord
servers especially if your content is like cyber security content then find an area that people are trying to break in in the industry they're always looking for for new content a good example of someone that built their brand off of beginners is the Cyber Mentor so he had a lot of information out there to help beginners and so really also if you're doing this on YouTube uh I actually start using tube buddy and it gives you some good recommendations on what type of tags to put in to your content tube buddy tube like short for YouTube tube buddy uh there's different levels of it I got the the lowest level but it's really helped me increase my
SEO and gives you some useful things to to help you improve the views on that uh that particular video and so also to when you're where you're creating that also put like uh a call to action so at the end of it have like a screen for people to subscribe and maybe even uh recommend another video or something that's what's what's kind of helped me out with that so really to collaborating with others helps a lot I was on David bbl's uh show a while while back and I picked up like probably about 2,000 new YouTube subscribers so also kind of being frequent with the content you know consistently created uh some of the things I've done to help enhance some of
my uh content from like my podcast is using some of these AI tools I use a tool called descript so it write a transcript on that content so with that the cool thing about descript it'll write it'll take the transcript create a transcript for you create show notes even create an article so then you could put repurpose that on a Blog not Everyone likes videos so repurpose that on your blog and so that's a way to get more SEO Improvement to your website get more views to your YouTube channel and stuff like that so that's been really great if you get like the pro version at a SE a certain level uh it'll actually uh give you like short videos it
automatically creates short videos with the subtitles like you'll see like on Instagram and it also creates like audio so short audio clips so you can take some of that and and also like creating shorts from your videos so if you got a 30 minute video maybe if you can work it out to where you can create like 10 or 20 minute chunks and just take that one specific piece uh that's one of the things like David bomble does and he's got like 2 million subscribers uh when I was on his show he went back and cut it up so he may have done one thing on recommendations and learning resources or certifications or books goes back and
clips that specifically and when people go to that shorter form content maybe that's what they they recommend you know attention spans are getting shorter and so you have to kind of uh you know like Tik Tok and Instagram Reales and all that you got to kind of feed that audience and sometimes it brings you people over to the the longer content form anyone else whoever who's first first cool hi how's it going uh I have a question for you so I'm a assistant administrator my guys here are uh support guys if you were to give us one thing to do today to get started on our path as pentesters what would you suggest we do I know that you had those
tools listed there where you can stand up some environments but what what's like one thing you would do if we were to go home today that we could start and really get the most experience and the most interest to stay focused on on this career so if you hadn't started yet I would start out with try hackme try Haack me yeah try hack me oh okay how's that spelled try hack yeah tryck me because it's very educational it's similar to they came out after hack the box but they had the educational piece so it takes you step by step through there and as you graduate from that then you can move on to hack the box and then hack the Box
Academy hack the Box Academy is one of my favorite resources and if you go to my YouTube channel I've got like a whole uh semester's worth of lectures on my pentesting class which was based on the pentest plus certification so if you go to my YouTube channel it's just Philip Wy MH and so if you go there I've got uh there you go that make it easier to see how my name is spelled but if you go to there I've got like a whole semester's worth of lectures and I've known several people that have taken the pentest plus to said that actually helped them on their pentest plus so getting started and the thing I like about tryhackme is
it starts out kind of easy and they walk you through it and you actually do the Hands-On activities and you'll build up a good base knowledge so they've got tracks there based on pin testing like vulnerability management there's even one that you go through you're using nessus in that lab so it pre it prevents you from having to build a lab which building a lab is a good thing but sometimes you can spend more time troubleshooting and fixing a lab than actually doing the Hands-On work plus the cloud-based stuff you can do it from anywhere you can study at work or home if you travel or whatever so try hack may be the first step cool thank you
you're welcome I have a question uh about AI tools you mentioned there was um AI powered uh red teing tools or pen testing tools and I'm worried that uh a lot of jobs will be automated out of existence as far as pentesting so what particular um subsections of pentesting are would you say more uh AI resistant and um and what is your take on AI uh taking over some of the uh roles I think it's going to be difficult because one of the things I joke about and I wouldn't want my manager to hear but I think I think AI could out could uh replace management before it could replace pin testers because you know you
decide and there it's more easy to decide until they get really we don't have to worry about much until they get General AI because AI now uses large learning model so you have to train it in feeded information once General AI comes around it can do its own decision learning and all that on its own find things but I think really what it's going to do is it's just going to help the tools help automate it help us automate things so I would say use things like chat gbd to help you be more effective one of the my favorite quotes I've heard is you won't be replaced by AI you'll be replaced by someone that
uses AI so I think it's and some stuff's really hard and it's you know honestly because if you look at some of these vulnerability scanners you know there's breach and attack simulation tools that will find things that you have to find in with your vulnerability scanner and use something else to breach it to chain that all together try to find zero days that's going to that you were a long ways from that really the more medial jobs it's going to probably replace now like your vulnerability scanning and some of the preliminary boring stuff like validating uh certificate based stuff like that I think it's going to help in some of those areas and give pentesters more time to focus on the the
hacking piece and more of the manual pen testing so I don't think there's really anything to worry about I think you should embrace it and learn how to use it in your workflow that's been a question before chap GPT became popular that people have been asking for for a long time this isn't really a question but more of a comment I've known you for several years and I've seen you take people under your wing and Foster them and teach them and I've seen you literally change lives so I just wanted to say thank you well thank you it's an honor thank you it's really an honor because when I started out doing this like I said earlier that
I turned my focus towards mentoring and teaching and all that and I never expected anything in return but my guy the the what you get in return just from the satisfaction of helping people is great but I get opportunities for jobs and opportunities to make money all the time that wasn't the intent but it's a nice side effect and I don't know if you're what your religious beliefs are I'm a Christian but I think also if you buy into un the universe or whatever there's some mechanism there whether we can explain it or not but if you do good things good things happen to you if you're if you negative all the time putting negative out there then you're
going to turn negative you're always looking for the negative that's what you're going to find but if you're putting positive out there and just helping other people because you never can't tell these people you Mentor could end up being a ciso of a company down the road and you work for them I've seen a lot of cases where people have been like Junior to me and they've went on to be you know higher up in company and being highly successful and one of the things to keep in mind when you're starting out don't think you're starting too late you see the pentesters has got 10 years I can show you a lot of people that took less time to get there that
are better so don't worry about time restrictions that you have to be a pentester for 10 years before you hit get that level cuz you have your natural intelligence to begin with the amount of work you're willing to put into it the hard work and time you know that will beat out tenure one of the things I hate to see in in companies is too many times they focus on tenure the amount of time you've been there maybe you've been there 20 years but did you bring any value are you actually doing your job or you just showing up for a paycheck you could take some young uh passionate or just a passionate person in General
trying to break in that's willing to work put in the time work circles around everyone else and those are the people that should be rewarded not just because you've shown up for work for 20 years and I mean there's something to be there if you're doing your job and you've been there a long time you deserve it but that's just kind of my my thought we need to change the way we see these things if you're coming in doing a good job you shouldn't be restricted I mean for instance my wife works for a company and they told her a couple years ago oh well you have to be here so long so and so was here so many years but yet you
know she's outperforming her teammates like three times or four times the bill rate of them working that hard and so you really should W people because especially you're a company and you're making money off of Consulting if they're helping you build more and be more uh successful you should help them out because eventually they're going to leave and one of the things I tell you when I Mentor if you're somewhere two or three years and you're only getting 3% raise when you first start out yeah you're GNA have to start out lower but at some point you've got the skills if you left and went somewhere else you make more money so we really need to
reward those people to keep them around if you give someone a career path uh get them training be you know good about giving them raises and stuff they're going to stick around there's going to be loyalty loyalty is a two-way street sometimes companies worry about the Loyalty of the employee but you know that goes both ways yes hi um so you talked a lot about technical skills uh so what would you suggest to folks who have built up the skills they're really good pentesters but they need to work on their writing a little bit they need to work on their report generation and I know that sucks uh but it's one of the more important
parts of being the pentester because you have to deliver the report so what are some of the recommendations sure that you would give for communication yeah one of the things I would do and this was before I got into pentesting you know I went back late in life well I still in my 30s when I went back to school for uh to get my associates degree one of the best classes I took it took was an English composition course so one things to do if you're really not good at that I would recommend uh going to Community College taking an English composition course learn how to write another thing is just practice start writing just like mentioning writing
blogs and stuff start working on that one of the things you can do to get practice too is go through and find some cves from like nessus or whatever go back and work on rewriting those vulnerabilities because uh you know one of the consulting jobs I had some of the vulnerabilities did come directly from nessus but I worked at a I really thought this was a good idea they went back and created custom writeups for that cve so that way it doesn't look like a nesus report so maybe go through find some different cves and reword it or practice writing executive summaries say you did you know a pentest or you did hack the box or something write a
pentest report so the best way to get experience with writing is writing so if you really need a lot of help then do you know take a course English composition course and also using tools to help with your grammar and stuff one of the things too you'll find out some of these tools are not foolproof I use grammarly a lot and sometimes it's incorrect but just practice writing or take a course to help help with your writing and one of the things i' advise too with writing pentest reports if you I found a better experience if I try to enjoy it if I try to not only just show some company how bad you hack them but
look at it is more of a way this is how thoroughly I tested you you may come back and not be not find a bunch of find but if you can go through and say this is what all I did and really explain that in depth that way they're going to see that they've got a quality pentest even though maybe you didn't find a lot of things but yeah so that's one of the things every time I found that I tried to enjoy writing the report it was a lot better experience take pride in it uh really you know work hard to create a good report and that's been one of the better experiences that I've
had hi to here you know when you when you wrestled what name did you go by I just went under Phil w because at first you had to lose all the time and I didn't want to ruin my gimmick although I names I'd considered one name I'd considered was Phil Ferrari because I like Ferraris this is back in the 80s uh Miami Vice you know they had a a Ferrari on there Magnum PI uh but I did wrestle in Florida once like under the the name uh Corporal chaos so I painted my face with camouflage makeup and all this so I did that one time but yeah I just went under my own name because like I said you have to lose all
the time it's really funny the way wrestling works because I was the guy they had to lose all the time and there was one time that they did some they had some storyline that they were working where this one bad guy turned good guy and the fans were really starting to get behind him and I never really got cheered when I went the ring because I was nobody but he was getting beat up so I went in to try to help him and I get beat up too and so after that for about a month people would cheer for me come to the ring because I tried to help their their their hero or the
star uh hi I'm over here yes um so you mentioned infosec Twitter which is something that I've recommended for years uh for people like just getting into um security but uh there was a data scientist that posted I think like a week or two ago a little while ago um about uh how infosec Twitter has actually dropped 87% since the day before Elon Musk took over um and so I I've noticed a big drop in the amount of like learning material and connection points in there and I know that a lot of people have gone to Macedon but there's also things like blue sky and Discord but there's not really a centralized Place anymore like there was with uh
infosec Twitter um I guess I'm wondering is uh is there any place that you think any any social outside of Twitter um that you could point someone to that that is looking for a commun community of Learners I think you just really have to get on several of them because everyone was going to Mastadon and so several of us from like our Dallas uh DFW hacker Community went over to Mastadon several years ago but it just really never did seem to catch on much but my opinion is to get on maedon get on threads get on Blue Sky and just kind of see which one benefits you the best but I do see that Twitter
has been coming back which is cuz all of a sudden I was I we used to pick up like aund couple hundred uh followers pretty pretty consistently then all of a sudden that big drop and it really dropped off and then over the past couple months I've seen a higher uptick you know I gained like 500 uh followers like a couple weeks ago so it's kind of getting better but I would say just get on the different platforms I don't know if if Twitter is going to tank but I think it's a good idea to look into other Platforms in case Twitter goes under and really don't underestimate like LinkedIn so if you know these other people from
these other platforms follow them on LinkedIn that's one platform I don't see going away for a long time so I'd say uh put a lot of effort in there a lot of people are starting to put more effort into LinkedIn because they're worried about uh Twitter so my question is you know the the recommendations and how you set yourself up and everything like that is there any difference between the goal being more of the contractor Consulting do it yourself get hired for a specific job version versus the in-house do it for a company on their product full-time pen testing I guess that's all going to depend on your risk if you want to go into business for yourself you can do
that and I've seen several people do that if people know your pentesting they may come to you because you may be less expensive than some of the big Consulting companies Contracting is a good way I think sometimes Contracting is probably easier to get into than a full-time W2 uh pen testing role plus you can use multiple companies the contract through so I know people that'll contract for multiple companies and sometimes you pay out it pays better but sometimes you don't get the benefits but one of the things is once you get the experience then you can go pretty much anywhere you want to starting out and some of the contract roles pay pay pretty decent because I know several of
those you can find around a 100 bucks an hour or so and so yeah it just depends on what you want to do if you like being in business for yourself contract maybe what you do there and I've uh and one of the things I've constantly had people reach out to me knowing I'm a pentester asking me if I was interested in doing work so once you kind of estab establish yourself then people may reach out to you for that work or just you know connect with people in your local community because not everyone has the $250 the $300 an hour to pay an organization but maybe you're doing on your own you could charge 150 bucks an
hour they're still coming out cheaper and then you're able to to make pretty good money that way all right I did a I failed at keeping us on time so uh and we got to get ready for the next talk so one more question raise your hand if you have not already asked a question all right and if you have questions after this feel free to reach out to me I'm happy to answer your questions thank you





