Red Team Yourself
Show transcript [en]
all right everyone can hear me all right perfect good morning I'm very excited to be here who else is excited for the first be site's Philadelphia this is awesome first off big round of applause for the staff in the organizers I've put together helped put together four b-sides up in Rochester New York and it is a ton of work so hands off to these guys for pulling off their first b-sides a lot of stuff goes behind the scenes to make this event happen so it's very cool to see it one sellout and to see it had fantastic talks scheduled for today and tomorrow so be sure to come back tomorrow too and have some fun all right
so let's get into this I am Tom Richards I am a senior security consultant for what was formerly called Citadel we just got acquired by synopsis and I'm officially the synopsis employee starting today I am our red team domain lead I am responsible for overseeing all of our delivery and knowledge management for our red team activities throughout sigil so all of our red team assessments and knowledge management on the inside sow creation client calls all that stuff falls under my domain that's my Twitter account if you want to follow me I'm not too chatty but you know more the merrier like I said I'm also a volunteer for b-sides Rock we did six total I've been
involved with for these things grow every year and it's a great turnout to be here I spoken before P site San Francisco Carolina Condor B Conger Khan and AB sec DC all right who here is responsible or participates in their security program within their organization awesome it's better than the last time I gave this talk who here in the responsible parties performs any sort of social engineering physical pen testing or true adversarial emulation as part of your security program that's way more than my last talk so that is awesome hands off to you guys for doing that sort of stuff we're gonna talk about here incorporating adversary emulation into your testing for your security or for
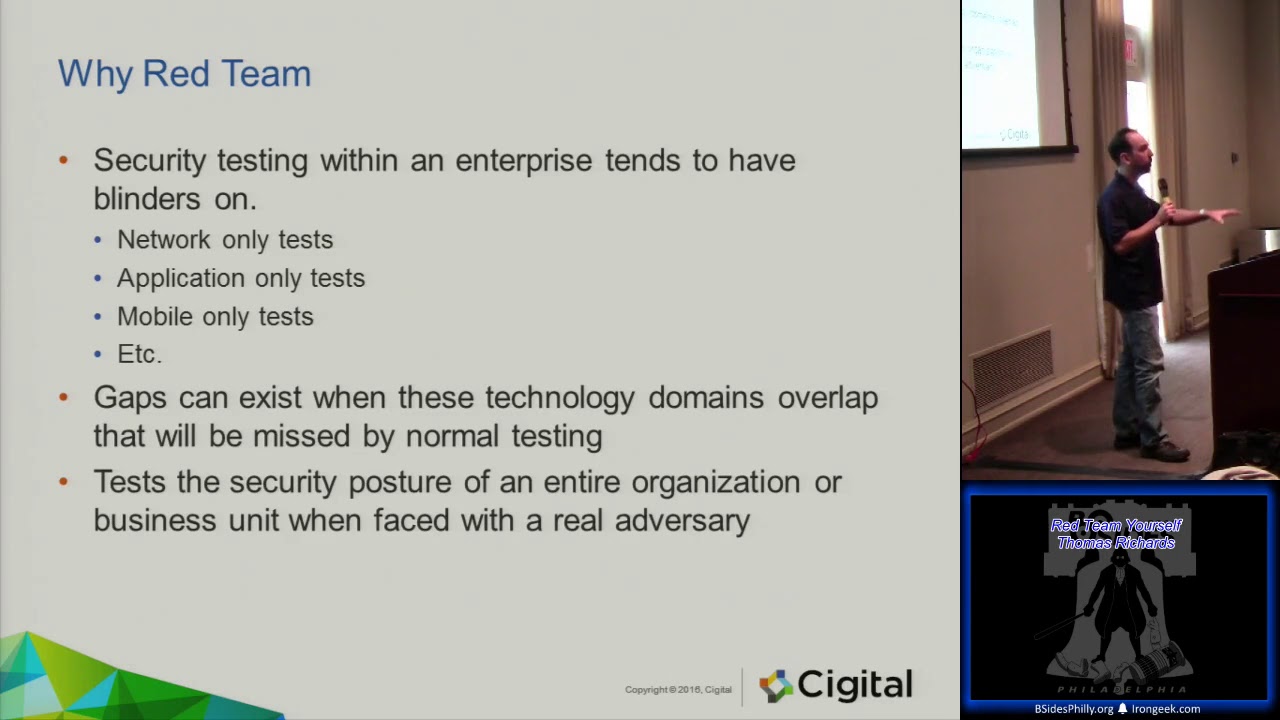
your organization to better see your security posture right pentesting sort of has blinders on sometimes you know you just test the network or you just test the application you very rarely test it all at once and that's where red teaming comes in and makes this very different so there's a bunch of different definitions for red teaming I one of them is challenging it groups perceived notions assumptions and or processes so just because you've always done something this way doesn't mean that's the right or best or a secure way of doing that red teaming also falls into three categories for what it can function in and vulnerability probes which is essentially what we do in IT
security testing simulations and also alternate analysis of any sort of information that may be coming up a little bit of the history of red teaming the Catholic Church actually had some sort of red teaming when it came to a devil's advocate position devil's advocate position was put in place to challenge the proof that someone needs to become a saint in order to become a saint in the Catholic Church you have to do some sort of performer miracle to be granted sainthood so you could see how everyone's like oh yeah I just did this right this shirt should be a saint this was instituted in the early Middle Ages to control the infox of saints interestingly enough pope john paul ii
abolished this in the 90s and removes devil's advocate position and then we had a huge influx of science into the catholic church the military used red teaming quite a bit looking at games the CIA red cell always looking at what the opponents might do or more importantly what Russia was going to do during the 50s 60s 70s and 80s it was primarily focused with the communist threat and looking at how Russia might react to certain things that the US military will do as well as the CIA red cell which is a function within the CIA which challenges a group's assumption of intelligence right so if you're part of the Russian branch and you're just washing you know what the Soviets are
going to do you might come to quite a few conclusions that things might be missiles in different spots when they might not actually be missiles because that's what your job is to do the CIA red cell would take the same information and look at it with sort of different perspective and non bias so they would either come to the same support inclusion or argue against the conclusion that no those might not be missiles those might just be like bunkers for something the government did quite a bit of red teaming internally as well the Federal Aviation agency actually had a red teaming component that in the early 90s went through and tried to break into airports and see
what they could do to damage to take down planes or caused some sort of mass terror attack there was a bunch of information that was came out of that to prove that certain threats were possible but no one took them seriously enough to actually implement the security changes that would be needed to prevent some of those things that they found from happening we unfortunately learned about those in 9/11 so after that you know they go how come no one told us like well actually we did tell you all this stuff was bad but no one listened when it comes to information security IT we're gonna define the red teaming like this we're gonna focus on just belen
ability probes right but we're going to look at it as not just a bug hunt which is what most pentesting they're just looking for right find all the bugs you can to make sure nothing's bad fix update repair we're going to look at goal oriented assessment where testers emulate the perceive adversary using any means necessary to achieve the goal we're not looking at the breadth of the organization we're looking at depth we're trying to go after something inside your organization your juicy bits your financial information your customer information any of that stuff that's available that you would be concerned about compromising assets is what bright diamond would then go after we've also done risk assessments as part of this as
well and you discuss with the relevant stakeholders understand technology and look at the wrist so it's sort of like a whiteboard in exercise we did this for a bank it was very interesting because when I was told about the assessment I kind of took back and said really they were literally moving millions of dollars by email someone would email them and then they would go okay we will move these millions of dollars from one account to another they were like the middleman between an investment firm and like a hedge fund manager and the client so the bank would never actually meet their client face-to-face the person giving them the money they would never meet face to face or has very little
interaction with it would be the hedge fund manager basically sending in this information through email about their bank information their routing in and how much money to move when and where through email there was very little checks and balances involved in this process and it was kind of a nervy and when I discovered this going through that you could just send in an email so the risk assessments the different process and technologies can be done as well off of a red teaming perspective I mentioned this earlier organizations we've been finding will have a security program right you will pen test your network you will pen test your application do you might do some social engineering which is
awesome that so many people raise their hand for that but do you do it all at once do you do it as a full assessment gaps and your security posture can exist where a technology domains overlap so you test your network which is great you test your applications which is great you test your people which is fantastic but do you test them all at the same time what controls do you have in place for where your network in your applications overlap right is that server really supposed to talk to that other server and are your people following the process and procedures that you put in place you want to test the security posture of the entire
organization through this usually trying to emulate some sort of adversary with a goal in mind right what am I going to go after as an adversary for the organization this is a great example of when I said this is not a bug hunt right so we were on an assessment of readiness s Minh and the organization had a very small footprint very small footprint we did come across an SFTP server that they had running which allowed them to transfer information for clients sorry so clients would send them information securely because it was SFTP writes a username password it was secure and then that's how they got that information now now when we were looking at this in a
normal network vulnerability assessment you would say okay there's an SFTP server list in here great is it up-to-date from what we can tell is there anything crazy about it no okay mark it down move on there might not be anything interesting well since this was a red team we were trying to break into the organization we actually had a very limited success in the phishing campaign didn't really good news many credits some organizations like to run their own phishing campaign when when you run a phishing campaign so they catch like their people first so people are more like on alert about what's gonna happen but what we found is this SFTP server did have SSH enabled so you could
authenticate we did had one working set of credentials that we got from our phishing campaign and we were able to connect to the SSH server now the interesting thing is they had the SSH server set to disconnect anyone on SSH within about five to six seconds so you would log in have the shell and then we'll kick you out but you would have enough time to launch one command so we load up Cobalt strike it was a Windows box which was fantastic dump the PowerShell payload to download beacon in that five seconds and we had access to that box that way service was running as a local admin from there we took over their entire network just because they
had SSH listening and not fully disabled on that box that's a difference between a red team and a network vulnerability assessment right we were going after we found a way in and we got in through that misconfigured SSH server businesses have threats every business has a threat and they're both internal or external there could be competitors nation-states rogue actors criminal organizations botnets how about the IOT taking down you know whatever it wants because you have all these routers out there with default passwords or even the ransomware that's been coming pretty prevalent right sometimes people pay the net just the moody system in San Francisco was giving free rides because their systems were taken over by this you know these
are real threats going after hospitals are actually paying the ransom to get their systems back because they don't have proper backup procedures and things in place to prevent this from happening we've actually had a couple clients approach us to try and emulate some sort of ransomware attack on their network what would happen would their users click would they go through what would happen when they got the alert so these things are real and are happening out there and we want to try to emulate those as best you can going through you want to focus on their techniques what would they do what would those phishing emails look like would they walk into the office not too many people would
walk into the office to break it's much easier to do remotely but it is there what tools would they have do they focus on mostly probably open source tools right the criminalization might not buy the license for something they're gonna want to steal it so we want to look at what would they have available in their portfolio their skill level are we talking about just script kiddies are we talking about people making grammatically correct and very visually authenticating a website or an email that looks like it's part of the organization to go through write the number one thing to fail on a phishing email is to spell something wrong or have very poor grammar cuz that stands
out that you're not supposed to be reading it or that something's wrong also targets are you going to go after the entire organization are you just going to go after the executives executives have all sorts of juicy bits and they usually have the least security to it's pretty funny you know I want my password to the ABC change the policy for me I'm the CEO that happens that happens when you look to bring this into your organization to get your security posture go and start doing these Red Team assessments you're gonna have to know quite a bit about yourself you need to be able to identify the things that people are gonna want to go after right
what are your assets your informational assets right your IP your customer information where do those live what is it what sorts of information do you collect on your customers your clients your people your employees right HR has everyone's social security number on it I was on the Red Team engagement we got into the office after our we went snooping around and we found one of the secretaries well one of the secretaries was responsible for also creating all the employee credit cards so all the company credit cards that were given out to employees were handled by this one secretary which was great because her filing cabinet was unlocked and everything was just in paper there so I had stacks of paper of everyone's
credit card application which was everything social security number address you know anything to open up a credit card was there your technical assets where are your computers this just happened last week we actually we're doing a war dialing assessment yes modems who hears remembers modems companies still have modems they still have out-of-band technical remote access so that in case everything goes down they can still get in it took our IT department a while to bring in the analog lines and find the modems to get the technology we needed to be able to do this but once we did it we kicked it off and we started doing the manual assessment of the modems that called
back well that we had that answered that was an actual modem we got to this one and there was no login prompt it got us right into an administrative console for what we found out to be a remote access device and we said that's pretty cool and in the menu it had four options that you can choose from which would be the four devices connected through serial port to this device look okay let's see what this is chose the first device at cisco router right into a Cisco router no creds no nothing just on their DMZ in their network through a phone line when I told them about it they were like you did what we've had this assessment for
years are you kidding me like nope I got right in I called it it's like here the screenshots they said well can you tell us where it is so we can turn it ha ha the router wasn't fully configured so there was no IP address but did have a host name I gave him the host name and they were like we have absolutely no idea what that is or where it is but it was one of their host names because they had a host name convention it was like the town you know the airport abbreviation one you know whatever for the router I gave him that information they were able to turn the phone line
off which was good they were you know cut that with the carrier but they're like oh we don't know where the where that is yeah absolutely no idea where that router is so where are your assets do you know right what legacy system does your company that's been around for 30 40 50 70 years still have in place Oh guess what our entire financial system runs off mainframe still everyone knows that right yep everything is done by mainframe batch processing at night with checks you want to be sure of your physical assets assets when we're talking about the physical assets we're talking about property generally buildings what locations do you have what do they have within those locations
you also want to know about your business processes this one should be fairly straightforward what does your business do right how do you do what you do how do people interact with your business those processes are important to understand and look at as a whole to see how someone could abuse him like I mentioned moving the millions of dollars through email they did have some checks and balances both on the inside and the outside but we found that there was significant gaps in those because they weren't looking at the big picture of what someone could actually do with what they did and we did execute some of those to prove to them that it was possible to
not only forge the documents saying to move the millions of dollars but also forward to access internally and request access they had a system they use to actually move the money like they've opened the email read it do the information look it up but we were able to get access to the system internally when we were in supposed to we did have a email account so we were malicious insiders but it was still possible just by forging email internally so this is what I was alluding to before we're a thing sort of like overlap I word electronic the social and the physical aspects of your organization so red teaming is like right in the middle
there I that's what we go after we look at everything as long as something is within scope sometimes organizations have reasons for taking things I'd ask how physical is probably the biggest one to be taken out of scope the most there most companies are worried about remote actors but the physical stuff is fun too so talking about the electronic what we're gonna go after the software that your organization uses your web apps your thick clients your operating systems and their custom rich internally we're talking about your network both your external and internal network your IP address base all your infrastructure supporting that desktops your wireless networks your mobile technologies and also your embedded technologies I was on
another engagement where they did have to factor off eye on their Citrix portal which was good but we were able to fish people and get credentials going through when we were doing our reconnaissance we discovered their error watch server air watch ISM what MDM platform old device management platform you know push the email through all that sup when we found that portal that portal didn't require two-factor off so we were able to take our iPhones and register it with the creds that we had onto their mobile device management system and as long as the device was provisioned which luckily the user we had did have another device it would offer you and then start syncing email so we were able to bypass
all their two-factor controls through their mobile device management system and just download all their email that one was fun your embedded technologies you know can we get in through your security system that controls your badge how is that even secure I was walking into my we just moved to a new office a couple years ago in New York and I was just coming back from lunch and I'm looking up at the the a monitor up top that has like the security feeds in the building so you can see that you know you're being watched well one of the screens changed to a administrative page for the security camera system and the guy was going through and doing an update so I
was like oh let's see what happens when he types in password because he had to put in your password to sign in and it wasn't start out it was just right there you know IP address username password everything to upgrade the security system that was monitoring the building just I'm watching it in the hotel in the lobby I'm Gordon are you kidding me like turn the monitor off when you're doing these things please we actually had another engagement where the consultant got into the phone system and was able to eavesdrop and listen in to calls and conference calls that was going on what was interesting about that because the guys are really good sport about it he
said I wonder how far I could go there happened to be a conference call going who is a bunch of the executives because they were deploying a new data center or thinking about moving data centers something along those lines so he jumped onto the line and started listening and they were talking about always having a specs and someone brought up security and someone else kind of shot that down and be like oh no it's not a good idea well the consultant that was on the line interjected into what was going on and said how important certain things should be and started giving them advice for what they should look for in their new data center client and they were like oh
yeah really cool you know Thanks and it wasn't until after the call our POC was in the room too but after the call someone turns to him and goes who was that on the line who I want to go talk to them and they had to tell them that we hacked into their phone system but so you're embedded stuff what other things do you have in your office you know we're seeing home automation with nests and Google home and acta Amazon echo but what does your building have that's supposed to be this you know IOT in the cloud thing how secure is that is that under an work - probably social this is gonna deal with the people and also some
technology your phone numbers your social media accounts you'd be surprised you probably do it you'd be surprised what people put on their social media accounts when it's not locked down or set to a private account your email address and also your business processes phone numbers quite easy to discover a lot of companies have directories online if they don't have a directory online they at least have some of their ranges and you can start to piece together where things are when there was a client on the west coast it was nice because I was able to call in to them you know at 8 o'clock our time but five o'clock their time in the morning and start
getting their voicemail greetings it did scare me when someone answered the phone so I was like what the hell it's 5 o'clock in the morning what are you doing but I was able to get the phone the names so when I called back in there in their business hours I'd be like oh hi Andrea how are you this is Tom from IT right I knew their name because in their voicemail greeting it had hi this is Andrea from so-and-so law firm please leave your name number after this beep you know what have you they have their name there good way to get people's names social media same client it was a law firm there was one of their lawyers
was so happy with her new office in San Francisco she took pictures of her entire desk and wall and put it up on Facebook with client data out on the desk I mean could you imagine being opposing counsel and finding that your employees are taking pictures of your case files and just putting it on social media they fix their social media policy after that email address is fairly easy to gather there's a lot of tools to get email addresses and find out the company's new email address scheme and also your business processes start calling into the phone who answers is it a machine is in person is there an automated attendant you can start to navigate through how soon do
you get to a person what happens when you call the helpdesk can you find the help number all these things fall into the social again with the physical you're looking at your facilities or access control procedures in your badge processes how do you physically get into the building what does the building look like how many floors does the building have what sort of security do you have at that building that's where we start looking at the physical to make sure all of that is good and what could be exploited there you'd be surprised I was with a couple clients where they were thoroughly convinced that their RFID cards were the high frequency more secure ones because they were the
thinner my affair type cards well I looked at the readers of the building it was obvious they weren't the the readers were low frequency cars and they were cards I could handle both and the building even though they were issuing the high frequency card only support at low frequency it's all still able to clone their cards and get in whenever I wanted so now that we went over what red teaming is in the different parts of it we're a look about building that in-house team right you're gonna want to do these sorts of things in your organization just to bring your security posture up and there's three things that I found that make these successful going
through you want to have an effective team dynamic right you got to have the right people to be able to do this work it takes a specific mindset to make this happen but once you get those in you got to have the leaders and the Assessors gotta have energy real support without magenta managerial support or executive support the right team effort will die this assessment what we do ruffles a lot of feathers it will piss people off I have been in three our meetings getting through the report just telling the client the first paragraph of the executive summary and they're all just yelling at each other about who's responsible for what I've also had clients shut down servers
in the middle of meetings - that was fun wait that system how'd you do that I got through this box that's not supposed to be on call Dave right now and get that off it was like when I called the the client with the modem that is he was on the west coast so I called him right in the Maury I said hey you know sorry for waking you up but I got into your mode into your network he was not happy he was leaving for Thanksgiving but it is what it is and you gotta have a read some sort of run book or guide right because having the right people now is great but they're not always going to be
the people that are there people leave change roles you might want to switch up your writing every once in a while pull people from different departments maybe have some development and IT folks as part of it as well just to give a good mix so you want to have some sort of run book or guide that they can follow so they understand the processes that you're doing but not necessarily a step-by-step guide for them you don't want them to go ok click a and then B no that's not read to me it's not scripted placing the red team within the organization is also a very key it has to be somewhere on the org chart right
it has to be that group who reports to what you want the group to be semi independent as soon as you start involving too many middle managers about what the team is going to do stuff is going to be cut at a scope they're gonna say oh no my groups not going to be done now you want to have the support high enough up so that the person says no you're being read teamed or it doesn't tell them they're being read team and has the authority to do so throughout different business units you want to be on top of all the business units to make these assessments effective and successful you also want to be far
enough away to remove bias but close enough that you'll be taken seriously and that's where the executive level support comes in you want these reports you're gonna come you're gonna find things things that you find that are wrong that could potentially introduce more risk to your organization that you weren't aware of before you want them to be fixed right we don't just want a hack stuff we actually want them to be fixed we don't want everyone to be broken into and our credit card information is stolen what 7 times this year over and over again and again you want the least possible levels of manage between you and whoever the top person is the most
effective ways I've seen this is like right below the CIO or the size so if there is one that's who you report to because at that level as long as this iced-over CIO has you know it's right underneath the CEO and doesn't have you know underneath the CEO oh or something you'll have the authority to carry out what you're going to do without alerting people without having to actually tell them you're doing it to make it more of a real-world exercise if they know you're coming like I said I mentioned in the beginning the talk I've had organizations run their own phishing campaign the day that my assessment starts now we're probably not going to
run the phishing campaign the day the first takes we're still doing recon but they do that to get their employees in a more alert state so they're not gonna fall for another phishing email right so you don't want to know that they're coming the team will need some sort of leader you want this to be a senior member or reorganization you want it to be also someone who has boots on the ground experience right you don't want someone just coming in not knowing how to read team works or how to write team you want someone that has done it before they will be best to understand and motivate the testers and you also have to have the business savvy to be able to
communicate the risk and the processes and why the red team exists to various levels of management they will also be responsible for setting goals and providing an oversight to the testers in the program to make sure it's successful the Assessors these are going to be the grunts the boots on the ground the people who will be thinking maliciously throughout the process now this is this is fun right what does thinking maliciously me basically cheating right how can I use X to accomplish Y even though X isn't meant to do Y you want to look at a process and go how can I get around that why is that there you also want people of varied
backgrounds you'd be surprised at how some of the crazy hobbies you have come into play when you start doing red team engagements all right but you want someone who has you know some network background sort of development background they ought they understand how networks and systems are put in place they understand how software is written how to read a code support backgrounds miscellaneous backgrounds people who are comfortable with lying cheating and stealing within the boundary of the rules right you don't want anyone doing anything really horrible but you want someone trustworthy but knows how to lie cheat and steal alright that's a fun little mix there but we're out there and they're gonna be the ones conducting the
engagements so they're gonna be the ones setting up the phishing servers setting that the attacks doing the network attacks so they have to have quite a bit of technical chops again lots of managerial support you need the executive support to be there and the program needs to be visible with real outcomes that improve the security of the organization if you come at the end of it and give your report to them and say ok hands off have at it no one's going to fix it right does your vulnerability management process account for issues that might not have just an IP address what about business process issues that come up during the Red Team engagement it needs
to work into either work into your existing process to patch fix update or be separate and more strategic in mind a lot of times we come up with quite strategic recommendations for the client to do because we see gaps in policy ok you don't have a social media guideline or it's very obvious you haven't patched anything in three years so you should probably start doing patch management on your interior network nothing like taking over a credit reporting agencies you know network within five hours because they have still have MSO 867 but you want to be able to show outcome and goals do you have enough support to actually initiate those fixes because if no one fixes
anything everything you say no one's gonna listen right but you want to show that hey we're actually fixing these things and now we went back next quarter next month next year and we were not able to do the same thing we did last year oh and you actually caught us this time which is good we have been caught before it does happen we eventually find some other ways but it's good when that happens that shows over a course of a year an organization actually fix stuff to help get that support you want to be able to set your goals right what is this red team going to do are we just gonna just spray and pray or are we gonna actually
focus on what is going to happen we wanted to protect certain assets we want to help protect the company improve the security posture and to do that you want to look for mission statements every team group might have a mission statement it says you know as the right team we will work to do X Y Z whatever you come up with but this will help to keep everything on track to make sure the team is performing the task that's supposed to and so that the leaders and the other executives can better understand what this red team is going to do right what doesn't right team do okay here's our mission statement right how many times you have to say it and
you need to be able to explain the risk that the red team will discover the first part this presentation was talking about what red team's can discover what we can find how we eventually get in what adversaries we're talking about start talking about risk this will get in the more CISSP land but in businesses understand risk and they score the risk and try to work out the likelihood of that risk and threat and how fast are going to remediate those things that's how businesses operate every organization I've been with that's how they operate to be able to know how soon they have to fix something you need to be able to articulate that to them in their terms
and say what the impact to the business will be how will this hurt us right I was on an engagement where we did a lot of application testing for a certain client and we tried to do it as thoroughly as possible and to understand the risk that the applications posed because they were all public facing applications for the client we asked that a simple question if you woke up tomorrow and your application was on the front page of the New York Times because you were hacked what's the worst thing that could be right how does that impact you and then we'd get out of them what the application does you know and how what would be bad what could go wrong
what does your application hold that would cause risk to the firm and that was key for the coz they'd be like well we went through a pen test already I'm like no you went through a dynamic you know you did a tool throw it at you now we're gonna throw a human at you and see what happens find those business flaws that the tools couldn't find the interesting side of this is that we found very few injection flaws you know code level flaws but we found a ton a privilege escalation a ton vertical and horizontal throughout this because a tool can't test for that a human test for that when you get going you're gonna
have a lot of push backs you know my users keep falling will fall for a fishery attack okay well let's try to fix that and improve it how is this different from normal testing we talked about how this is different from normal test and just reiterate that but these are things that people push back up my system network application doesn't do anything sensitive we wouldn't be a target yes you are a target if you're on the Internet your target no matter what you have computing resources you have some thing that an attacker would want to go after you're a target if you're on the internet if anyone has actually done like a packet capture of an external
facing network interface it's ridiculous what comes through absolutely ridiculous the red team will ruffle feathers you're kind of focused on sensitive parts of the organization you're gonna focus on established policies you're going to go after people that had been in the company for years it's gonna piss people off you need to be able to handle that because they're kind of I didn't yell that you will get yelled at when this stuff happens when something goes really wrong and you find that one really bad thing that like hey the company could fold tomorrow because of this no one likes that your stakeholders should have enough influence to be able to get through any political threat people
might actually try and stop this program because I don't want their underbellies exposed but it needs to be to be able to communicate that and articulate that is important the run book is a guide for the Assessor it's not a step-by-step guide it's not you know open the terminal' pseudo to bash type in MSF console and you know set your exploit no it's to go over the high level view of how you conduct an assessment all the phases of the assessment from beginning the reconnaissance attack planning and execution the reporting it should cover all that it's going to be a living document you're gonna find new tips and tricks that's where it should also go in
here you know hey we try this and it didn't work and we think this is why so that the next person that goes to do it might not try and do that or might know how to fix what that problem was so you want this to be ever-evolving not set in stone to help your Assessors to complete the tasks the different phases that we're going to go through the first one is reconnaissance this is the information gathering phase probably the most important step in the engagement is the information gathering everything that you find in those first day or so is going to tie together the entire assessment it never really ends the stuff I find in the beginning is
that the heli the stuff I find in the middle I have changed course completely mid engagement because it's something I found halfway through in engagement it's usually broken into two different groups and it's active or passive passive recon is when you don't touch duration you're not poking them yet you're just seeing what's out there getting DNS entries finding their IP address range their phone numbers what their facilities look like on Google Maps email address harvesting without actually touching the organization is what's considered a passive recon active recon is when you start interacting with the organization you start doing the port scan so you're going to start to call into their helpdesk you're gonna start doing the
vulnerability scans and you're gonna start being on site to see how it looks are their guard rotations where do the smokers hang out where does everyone go for lunch I was on a physical engagement and the company had two offices literally across the street from each other and people staff were going back and forth to those offices all day I just stood on the street corner and started taking pictures of badges I had enough information within 30 minutes to make up a fake badge to get in because everyone's wearing the badge over their neck and just walking back and forth within the buildings with stacks of papers their laptops open walking the streets of LA but this happens after you
gather information and learn everything you can about the organization you're gonna start your attack planning this is where you start to identify how you might be able to go in and start to get things ready what did you learn do they have any meetings coming out are they in a building that holds social functions who are you going to pretend to be to accomplish your goals this will help to prepare you for the exploitation phase and the exploitation phase is when you're actively going to start attacking the organization this is when you launch your phishing attacks this is when you're breaking into the environment this is when you're exploiting any vulnerabilities you find exterior now in the four years I've been
doing this I've only found like to actually exploitable vulnerabilities on an external interface one was heartbleed months after heartbleed came out which was awesome but the exterior generally will protect them like I say it's going to pretend everywhere but generally it's well protected and this could change at any moment you have to be ready to change based on information that you find or when something doesn't work also phone calling try to get password reset try to get people's passwords physical entry how you gonna get into the building tailgating RFID cloning lock-picking covert entry post X is where we've gotten into the environment somehow and now we're going to proceed to the goal something is in mind get on to X system
or sometimes just take over my network which is fine and see what is there go after the data maybe try to excellent rate it we've had clients set up dummy data in their environment that looks like real data to see if they're what's it called outbound filtering the what DLP that's yep to see if the DLP is actually working because they want to test that right we have sensitive bits will it get out to see if it works surprisingly sometimes it does you want to have a big bag of tricks the red team is gonna have a lot of crazy tools somewhere standard somewhere not standard they're also going to be things that you develop
in-house we have several scripts that we use to do a lot of back and work for a phishing to receive what's going on through sees the the creds and what to do with them we have a lot of templates that get modified every once in a while you also want to be able to have documentation for these tools and that documentation should be within that run book it's quick how to's what it's used for when you should use it when you're putting this all together the red team inside organization will help improve your security posture for those of you who do it already fantastic if you've probably seen improvements if you're conducting such a thorough assessment
you want to have managerial support you want to put together the proper team dynamic to make this successful any wanna make sure things are documented so that as people leave or things change or as you rotate staff that the team can continue to function and still be successful within the organization thank you





