OWASP Honeypot Threat Intelligence Project
Show transcript [en]
than you good evening ladies and gentlemen I hope that you had a great B sites this is the last talk let's get this through this uh my name is karik adak and I completed recently completed my masters from University of wari uh this is what uh this is who I am I uh I have three years of experience in cyber security specializing in threat intelligence incident response and Pen testing and these are few of my achievements that and certifications that I achieved throughout my years now let's get straight into the topic so first thing that comes to my mind uh and I am sure that it comes to your mind as well why do did I choose my
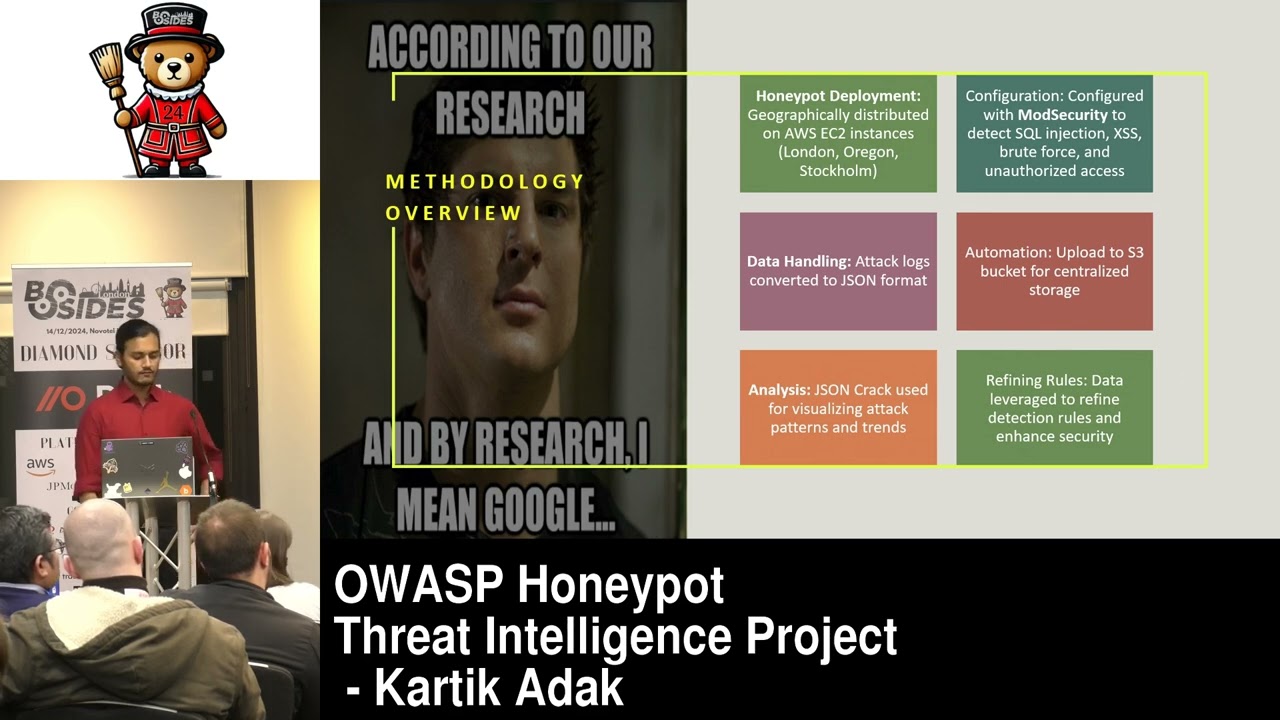
project why did I choose o threat intelligence so the first problem statement that I saw was 90% of the global attacks are through web application and the attack vectors that you see are becoming more advanced but the mechanism of Defense are not matching up so the gap between the attack vector and the solution is too high so I wanted to just lower down the Gap that's why I made project objectives and these are the three project objectives that I uh created first I thought of deploying uh honeypots uh which would just collect attack data and that would store in a uh S3 bucket that would be my central repository and I would use mod security and ovas core
rule set to just have a tagging of what kind of attack Vector is that it could be SQL injection it could be brute forcing and different attack VOR vectors so the tagging comes through o core rule set and then the entire data is getting converted into the Json format because the tool that we are using is uh Json visualizer so in generally like it stores in mlog C because it's a mod security logs so it's we have to convert it into Json format moving on to the next slide uh this this is the entire architecture of my project so if I run through how the attacker and the life cycle of this attack architecture would work is that
if you see the browsers they are the browser that the attacker is going to use and going to interact with our honey that is Amazon ec2 instance if you see in Amazon ec2 instance there are multiple instances which are uh spread across different geography and it has mod security code rule set inside the ec2 instance so if the attacker is attacking a ec2 instance it is getting the uh tagged according to mod security code rule set and then the attack Vector is being uh being noted down in logs and then sent it to S3 bucket which is uh used as a central uh threat intelligence database this you can alone use it to share with different teams and you can
create your own uh threat intelligence by creating your own rules but in this case I have used a visualization tool just as Json Json crack where you can visualize which will be seeing in the future slides moving on to the next one uh this is the entire description of my architecture so the first thing that I'm going to do or I have done is distributed geographically AC AWS ec2 instances uh over London Oregon and stok home and then I configured uh different mod security rules that is SQL injection exess as Brute Force we can also call it as honey traps and I have converted the logs into Json format because uh our jsn visualizer does not follow mlog C and
and then we have stored that into S3 bucket for our centralized storage and then we use Json crack for visualization of attack patterns and Trends after we get uh the visualization uh of the attack vectors now we know that there are certain payloads that are bypassing the parameter so if that's so we have to refine our entire Honey Trap so that is the last thing that we are going to do that is refining our rules moving on to the next slide as I said we are creating honey traps honey traps are nothing but use cases which are used to tag those attack vectors for example if a particular uh advisory is trying to attack Brute Force so how will we
understand that it's a Brute Force attack through our use cases so use cases are nothing but the attack uh V vors that has certain keywords which are just tagged when you pass or attack through certain browsers and we will see one of the attack Vector that is SQL injection we'll see the demonstration we'll also see the rules how I created the Honey Trap uh this is my uh mod security configuration file where you can see that there are few honey traps uh don't worry like I will uhx maximize the image and we'll see one of the Honey Trap that is a SC injection so this is my Honey Trap um this is used to detect SQL
injection so here if I break down the entire Honey Trap the rule says that if there is an if there is any argument or argument name request header or request URI that means anything on the URL that say is that there is a keyword called select Union update delete drop alter or exe or execute then please send a message that SQL injection Honey Trap is triggered now how does that work let's see in the demonstration so in this case you can use some uh automated attacks such as SQL map but I prefer using BB Suite so if you you can see it's a post request for a login page so in the login page there were two as as you can see there
are two parameters username and password so I have tried to Tamper the username by uh putting the payload of Union select n n null and now let's see if our log rules can just detect this uh I don't know if this image is clear but you can see that there is a username parameter that is shown which highlights that this payload is getting detected and there is a warning message of SQL injection is getting detected this is nothing but a visualization tool that I talked about Json crack moving on the key findings for uh this project was that I found that 91% of the detection rate uh was success in SQL injection the and xss brute force uh
were effectively flagged and it was the most common pattern in the attack vector and the trend Insight that I got from this uh project was that London recorded the highest activity and there was frequent exploitation of admin directories and robot.txt and the limitation that I saw in this project was there was approximately 10% of false positives that means a lot of attack vectors were getting undetected so what I was I used to do is just refine the rules again and again as it it follows the agile process you have to do again and again and challenges with this uh project was that I faced a lot of outdated components that was an issue maybe if I use some other tools maybe it
it would work better so this are the future enhancement and recommendation by me the we can have more honey poods so that we get more geographical location attack Vector because every geography has its own way of attacking maybe somewhere SQL is prevalent but some other places uh they they prefer more bruit forcing it could be anything uh we have to improve automation for faster mitigation because there is a lot of dependency of logs getting into passs into uh our database and then we are putting it the database uh data into a Json crack tool so to fasten the process we have to automate a lot of process uh although I have created an automated script that uploads
it to S3 data bucket uh but yeah there there I I did not have any solution to upload it to J crack I had to do it manually so that's why there there needs to be an improvement in Automation and for brute forcing like it was able to efficiently common attack patterns the recommendation that I would give is there should be regular update of Honeypot configurations second thing like as we created a threat intelligence data set we can collaborate with different organization and different people to showcase our threat intelligence data set and there could be continuous monitoring to adapt emerging threats if you have any questions please do let me know thank you first of all I want to thank Nikki
she helped me a lot with this presentation and she guided me a lot secondly I also want to thank B sites for giving me such a wonderful opportunity and finally you guys uh who have been a lovely audience thank you and I have been I I am actively looking for job roles if anybody has any job you can contact me through my contact details thank you we we have a question right okay so one quick question uh with Mod security are you blocking or are you just it so it's it's the the rules that we create the Honey Trap is actually alerting but you can keep blocking as well it's on you how you want to
maintain it uh if you just want to create a thread intelligence data set where you want to see what are the more attack patterns you can just put it on logging but you can block it as well okay and can you install it on any web application yes you can put it on any web application thank you yeah any more [Music] questions hi karik great presentation thank you I think the the focus for the emphasis of this sunny truck and this St is more on SQL injection and cross side scripting and Brute Force attack those are the primary use cases can this be extended to other security use cases especially around stop 10 yes yes you
can uh it depends like uh it depends on the web app application as well my web application that I created was more focused on login Pages that's why these were the more prevalent attacks but if you have more uh complex functionalities if you want to apply more apis or there is more user interaction search bar or something so there could be more injections and different overtop 10 abilities like maybe I can I can show you csrf if there is some sensitive data you can add there there's no problem with that got question at the front did you think of any of the other services like SSH or SMB or any other yeah so so this was purely on the
basis of web application so it was more focused on 80 8080 and 443 but for SSH uh I don't think so mod security does logging of SSH because it is strictly of web application so maybe we can create our own rule custom rule but this is out of scope for this project any more questions in that case thank you very much C thank you