Starting A Dumpster Fire: Data Exfiltration
Show transcript [en]
good afternoon everyone yes I love this audience this great great welcome here so thanks guys for coming to this afternoon's session I have the honor of introducing Josh Smith he'll introduce in a second but before that I have some housekeeping announcements one is that at 3:40 we pretty much have a hard stop in this room so basically that means you have to get out of this room and so 340 don't kind of linger if you can we have to kind of clean it up so the theater can get on creating business through different events that they have later on the day the second housekeeping announcement that I wanted to make is regarding our vendors please go and say
hi to them a lot of them have great job opportunities and and/or are explaining some of their techniques and offerings that they have and we can't hold conferences without their support so please go say hi to them and see what they're all about last thing that I wanted to announce is that in your bag everybody got raffle tickets so if you haven't had a chance to kind of go through your bag you should have a blue raffle tickets in there downstairs at the registration table is where you can actually put them in different areas different boxes to potentially win prizes at the end of the day also some of the vendors have raffle tickets so if
you talk to them you might be able to get the rat-faced raffle ticket too so now I have the pleasure of introducing Josh Smith he's a Vidant health so one he is a homegrown hacker he started taking apart stuff at the age of eight and has been learning ever since so he has his osep and he is trying to go on and get the advanced certification in that area to have that expert level as well as the CISSP so warm welcome for Josh and I also have this amazing book here it's a going rope which I think has a fun little surprise inside for him so he probably doesn't need to read it it's more of a take-home
homework assignment so if you guys will help me welcome Josh Smith and he is going over a starting a dumpster fire alright so how many of you actually have professional programming experience so a few of you I'm gonna go over extending a couple of open source tools that are used for data exfiltration by doing that we are going to come up with a common interface for I guess what you would consider transforms which could include anything as such as encryption compression any sort of data manipulation in the network transport side as well why would we want to create our own tool rather than use what's already available out there well one key feature is that you know
one tool may not do everything we need it to by using these methods we can leverage open source software I'm a big advocate for anything that is open source how many of you have children a decent portion so as you know children take up a fair amount of your free time I have two kids myself so basically reusing things as my method of creating a environment where I can rapidly test and not put as much effort in as I would writing something from scratch
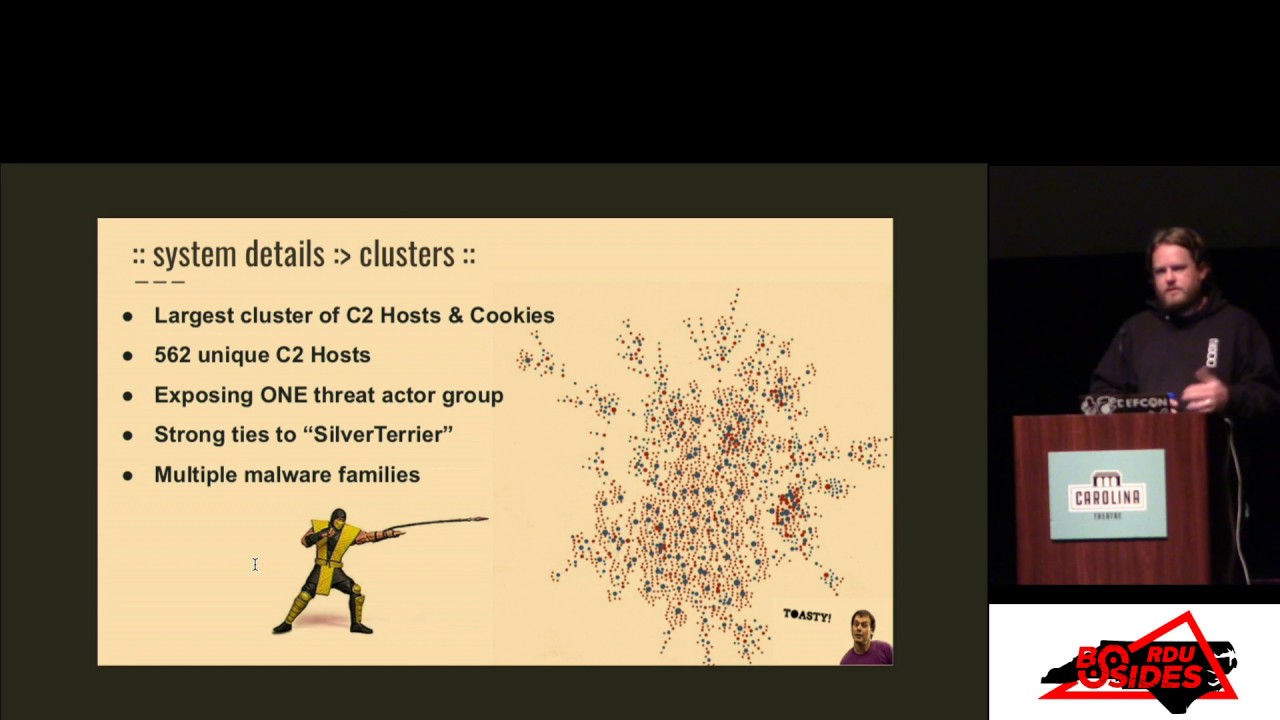
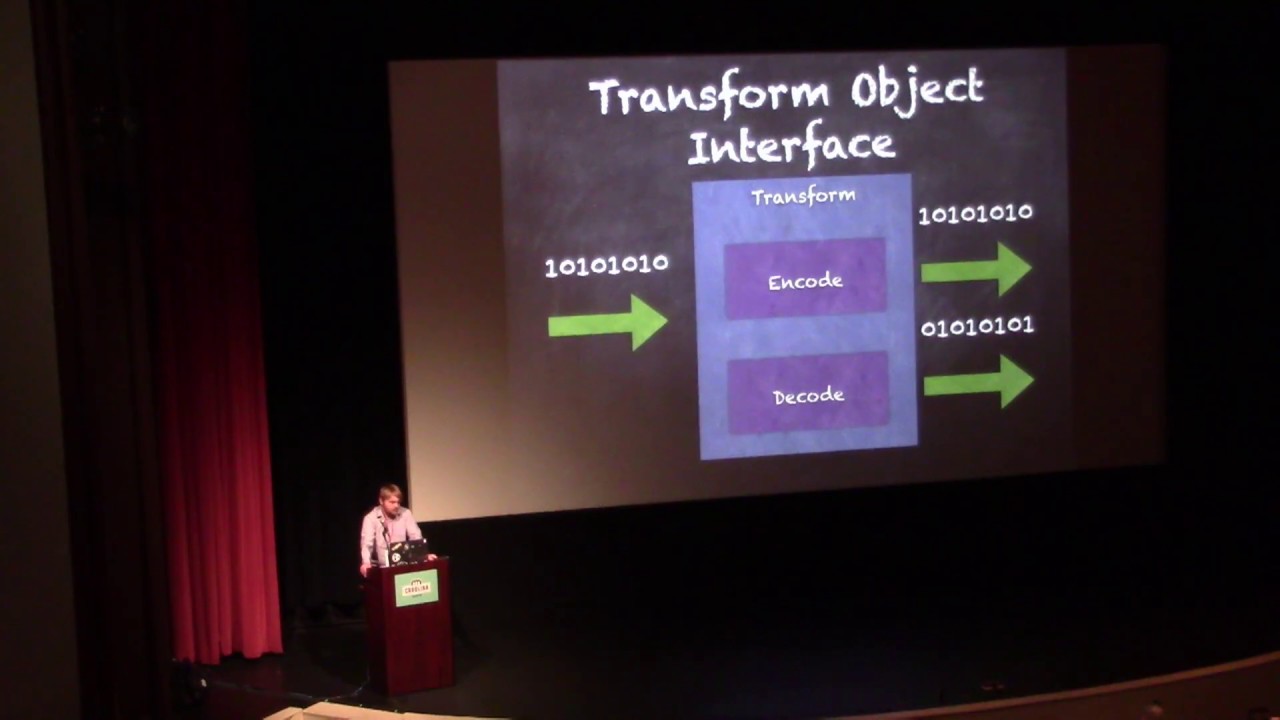
so we're gonna be using a design pattern called interface using an interface we're gonna adapt a third-party code to fit within the bounds that we want it to and with that we can reproduce reproduce these sorry the first time giving a talk apologize with it you can create a method to get expected results no matter what the input code is so the transform object that we are going to design will include binary input it does everything like a black box and then binary comes out this interface is going to implement two functions encode and decode it's pretty straightforward takes the input binary encode will encode it and the opposite is the decoder then we will group them
together like layers in an onion and an engine object so therefore the top layer would take the raw data and then pass it to the layers below and encoded data would come out decodes obviously the the exact opposite except for the engine object will process everything in Reverse so this is an example of the test code that I came up with for this concept some of the transforms that I chose were compression encryption swap actually just reverses the input binary to the exact opposite base64 which I'm sure plenty of you know and Markov chains so that's half of the equation of extol trading data is you want to implement some sort of steganography to hide in plain sight the
other half would be actually removing it from the network so with that we design a interface for the transport objects which implements two methods listen and send a pretty straightforward inputs exact same thing everything is just expecting a raw binary stream and [Music] processes the exact same way as the transform object except where it operates over the network protocols all right so this is a diagram of the entire process so starting with a client it would implement the first transform and go down through the fifth then it would actually perform the network translation to a server object which would then perform the decode operation in Reverse
so how many of you have used Det it's open source library for data exfiltration some of the features of it include slack twitter ipv6 which can be used over trade o62 for several other you know different technologies to translate from mybb 4 to 6 as well as Gmail Google Docs sip and ping the method that needed to be adapted in that is it actually implements a controller class for the application itself and we will go over how I chose to encapsulate that inside of the code so the above a screenshot is the actual plug-in architecture that this open-source project used it implements the config and it expects a app object to register several callbacks such as the send receive
so this is my implementation of the wrapper essentially this small piece of code takes the entire source of debt and all the network objects it implements and wraps it to the binary interfaces that we discussed earlier as it's pretty short compared to writing all of those Network protocols myself if it would have been a lot more work so even the register plugin win' doesn't actually do anything it's just because dead expected it so essentially this implements the application side that all of the plugins were expecting from that this is an example of just one of the protocols TCP I implement the sin and receive objects that are expecting the input
the second project I chose to use was peix ville made uses jetdirect mdns all joined a couple other different ones some of them were interesting features that had is it actually has physical means for exfiltrating data such as QR codes audio I think there's even a plug-in for AM radio transmissions using the built-in sound card and by wrapping that in the the same type of interface I'm able to leverage all of those features for exil trading data as well this is the example of the DNS implementation with MPX fill it just implements the class itself for the sin and receive it takes data X our PI X till did not need any kind of special
adapt adaptions except for some minor changes so it expected binary instead of a character input other than that all of the methods were pretty much ported over with six to eight lines of code
okay the top one I'm gonna say this word once because it short-circuits my brain markov off you stop you skate I'm butcher it every time I practice it I can't do it so it's an interesting project that takes a corpus of text which could be a book in the instance that I'm using a short demo is going to be Taylor Swift lyrics and the original authors that's the example they used as well but this is a form that we can use to encode data in plain sight and bypass DLP filters that are relying on signature analysis as well as you know base64 busy compression and encryption as well
Oh
all of the code is available on github on board slash Joshua - Smith slash besides Rd you 2019 obviously the credits go to the open source projects that I decided to use in it and we will if I can get my examples
one second please
all right so the actual code that it itself accepts a list of the transforms in this example I just chose to use the same ones that I showed in the slide but as you can see it's fairly straightforward one of the neat features about the framework that I decided to implement is the fact that any of these steps can be rearranged or removed at any point so say we want to remove the AES and with the debugging enabled it shows the entire process and here are your Taylor Swift lyrics so just to put yourself in a scenario if Facebook is allowed on your egress in a corporate environment and someone is posting Taylor Swift asked lyrics to Facebook
it's not going to trigger any sort of a response - to the untrained eye I believe that methods like this would render any kind of signature based analysis completely useless and you would have to allow them behavioral or even statistical anomalies to determine if there was any strange activity going on
so instead of the full process this just encodes the data and then sends it across a simple network connection just using the TCP engine for this I did have a windows VM set up for some of the powershell modules but i'm unable to get to that it seems unfortunately but this should be an example of the process working over the network essentially the only thing that has to be shared and and these instances would be the AES key and the actual list of manipulations you chose to use such as encryption swapping base64 the Markov chains
the input data was actually some fake information for myself on the left hand side you could see what would actually leave your egress on the network and on the right what any threat team or actor would receive on their end
sorry I ran a little bit short and for the mishap at the beginning like I said it was my first time i given talk it's hard to judge how much content i needed but there are there any questions that anyone has yeah yes sir on an off since May yeah yeah it pulls in all three of these open-source projects and allows you to utilize them seamlessly probably total time for me to develop it would be under 20 hours would be my estimate any other questions yes sir
yes so some of the road map features that I have mapped out for myself would be implementing a c2 which would then include a feature such as that but one of the ones that I wanted to expand upon would be including a pseudo-random lists I guess would be the best way to describe it so the order of the list would also be random of with each transaction yes sir
the Python client was for the Linux implementation of it there are some PowerShell scripts in that repository there's more I need to push to it but my windows implementation is actually using PowerShell and reflectively loading binary or even shell code into memory rather than writing anything to disk
any other questions
well thank you all for enduring [Applause]