Bypassing Anti-Virus Using BadUSB by Cristian Cornea
Show transcript [en]
so welcome uh and thank you for joining this presentation during this session we will be talking about how can we bypass antivirus using this little device how many of you know about this one but USB yeah it's it's pretty famous but have you wondered how can we have one one interaction initial access using it basically even if the client or the target uses antivirus we can have just single interaction uh initial access using bdsb we'll see how we can achieve this during the the presentation um our Target antivirus for for this presentation will be Windows Defender so to be vendor neutral we'll use the windows default antivirus but firstly let me ask you how many of you rely on
Windows Defender okay another question how many of you from those who raised their hands are confident in this decision okay some of you so let's see if I can convince you to switch to a more advanced solution after this after this presentation or to an uh ADR uh approach so let's start uh towards the ball myself um I'm certified with some certifications or my main expertise is offensive as you can see uh I'm founder of the zero tax security a cyber security provider a company and we are providing offensive security all over the globe through all the continents basically and trainer for some entities including the Pentagon and speaker to multiple conferences and also part of
the AC Council certified technical hacker committee which means that I'm part of the group that creates the the syllabus for this certification as a side note I'm not responsible for the nmap questions if you know what I'm talking about Okay so this was basically the boring part let's move to the to the most interesting part uh what we will be talking um today about is the following so on our agenda we have uh an MC bypass technique that we'll use to to actually uh evade the antivirus how can we leverage the education policy in order to run Powershell scripts on a local and non-administrator user uh how can we develop a payload runner in order to to
have our payload directly into the memory so we'll have a file less deployment of our little uh initial access and how to do everything on this this nasty device so uh let's move forward we have the following scenario we have Bob Bob works at let's say insurance company Bob goes to the parking lot to to smoke a cigarette but found a little device on the floor and he will pick this device once picked uh Bob will go to the office and will plug the device into his computer what happens next is basically the following an attacker now is connected to Bob computer uh basically it's connected to the organization that Bob is working for which means that the
attacker has initial access to that company but how this happened because Bob has Windows Defender enabled Bob is not an administrator on the on the workstation and the company policy says that removable media storage is disallowed so let's see because the the answer for all of those questions will be during the the presentation basically the the sequence of the the attacks is the following uh we have the answer bypass which is used to to trigger the evasion of the antivirus we have the execution policy bypass which is used to evade the um the policy that says okay non-administrative users are not allowed to run uh malicious scripts or Powershell scripts on Windows we have the payload runner in order to have
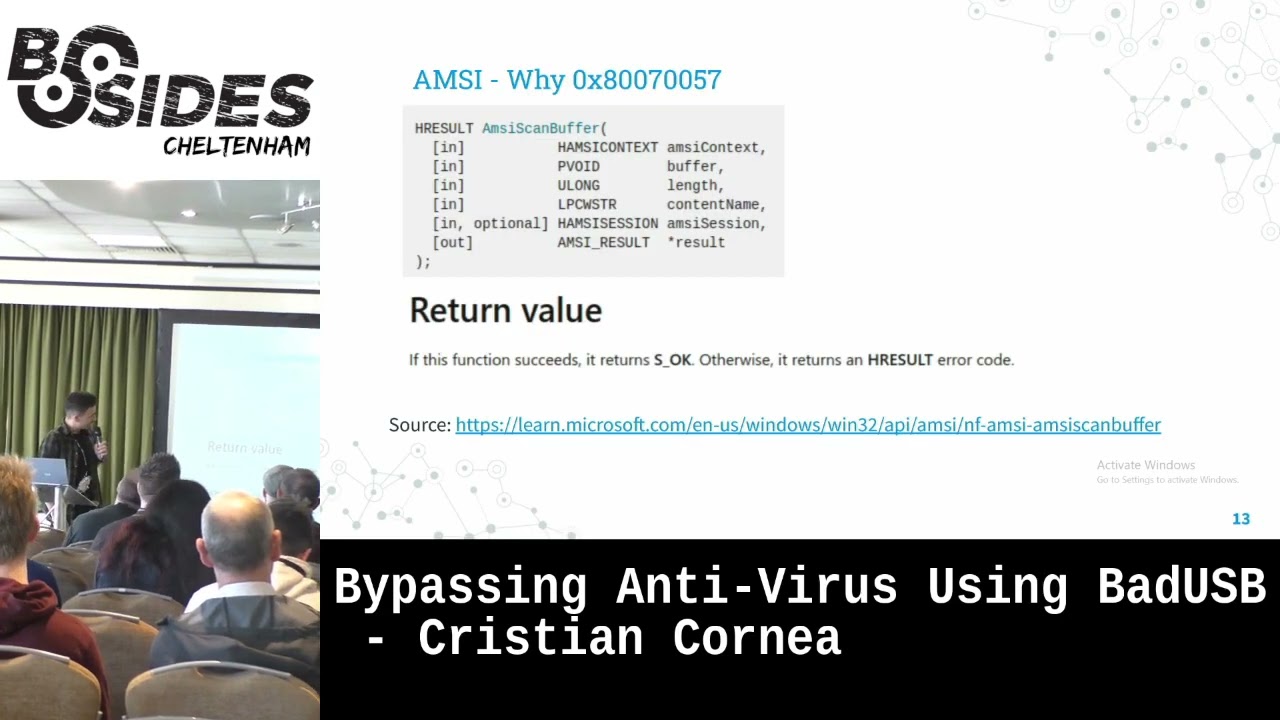
everything in memory and to not leave any artifacts on the system and some post exploitation techniques so the DMC bypass uh how many of you knows about the MC okay perfect so for those who uh don't know about the MC basically it is a middleman between the antivirus product that we have on our computer and the the workstation the operating system basically once we run a Powershell script for example the OMSI will try to send that Powershell script to an antivirus engine in order to check for any malicious indicators so if we try to cut the armsy and try to pitch it because we can make AMC return any value that we want to we may be able to to
bypass even some of the advanced antivirus Solutions but for the purpose of this talk we will solely uh rely on Windows Defender to bypass so uh if we take a look over the internal usage of AMC it has the armscan buffer function the MC scan buffer is the one responsible for scanning Powershell scripts and the function is taken from amc.dll library which is the official library for OMSI uh and now you can you can assume what we'll do basically we'll manipulate the anti-scan buffer function to return on arbitrary value in order to pass all the malicious scripts to execute even if they are malicious or non-malicious and we'll play a little bit with the memory uh at this at this stage
so let's get let's get into the technical things here we have uh the first part of our payload uh do you do notice something strange what languages are here there are two programming languages any ideas yes and yes and Powershell so we have C sharp and Powershell how can we do them together so how can we play with them on a single script our main script will be Powershell but Powershell doesn't know about some windows native API functions so in order to call or to modify those windows native API functions we need to use c-sharp how we use C sharp with Powershell we will use the add type for for Powershell basically in order to to
play with the with the functions with the windows API native functions and here as you can see we have three functions that we we defined so we have the get proc address which is used to uh to get the memory the address uh within the memory of a specific function what function do we want to get the address in memory sorry yes exactly the answers can't buffer um a function that we discussed previously uh from where do we get that memory address from the amc.dll how can we find the memory address of a function if we don't know the memory address of the library itself so we need to Define also the load Library function which is
used to return the memory address of the amc.dll library and then we'll use the virtual protect which is basically used to pitch the memory address within that that function basically we'll use the virtual protect to to play with the with the function with the ansyscom buffer function and the Second Step here is to load the amc.dll into the into the actual memory then we use the get proc address as we discussed previously to get the armscan buffer uh function address within the memory and then we have here a sequence of characters that we use to build the return address of the MC scan uh buffer function why this why this sequence or why this value basically will see during
our next slides because this value is not random so it's not a random value it's taken from somewhere but we'll see during the the next slide and then using the Marshall copy technique we'll patch the address within the memory of the of the armscan buffer function okay so uh we were talking about the the value and here is the the explanation basically if we take a look over the official documentation by by Microsoft of the armscan buffer function you'll see here at return value that code if this function succeeds it returns s underscore okay otherwise it returns an H result error code end of the code basically what is missing here and it's a very very important uh part of the
documentation is that Microsoft doesn't tell us that if the function returns H result error code any script can be run so any scripts can be executed on the workstation and unfortunately they forgot uh forgot to um to write this down on the documentation so you researchers have to to figure it out about this one and basically you may assume now that the next step would be to what would be the The Next Step here basically sorry yes basically to return on each result code so we'll pitch the MC scan buffer function to return an H H result error code and that value is an edge result error code and where we can find the H result error
codes within a Microsoft documentation basically they have also a documentation um page with the H result values for example this value uh is basically invalid argument so you can take any value and it's it's official basically if we search H result values on on Google let's see okay it's loading do we have internet yes we have Internet okay so all of those are age result codes that we can use to page our MC scan buffer function so anything from here would work okay let me go back to the presentation so we have this payload which is the MC um DMC bypass payload but this is detectable do you know what we can add what flavor we can add for this payload
to make it more uh let's say undetectable any ideas it starts with o exactly obfuscation so we can obfuscate this partial code and it will look something like this this is obfuscated using using invoke obfuscation which is the the most well-known uh obfuscation script for partial scripts and you can see it uses a normalized functions uh conversion to um to hexadecimals four characters and then reconversion back to um to character arrays and basically where we cannot apply obfuscation because that's a very important part we can apply obfuscation on the partial code but we be very cautious when you apply a formification on the c-sharp code because you uh May trigger some errors if we apply too much obfuscation so in
this example normalize over the c-sharp code will not work so what uh I tried here is just to change the the variables names so changing the variable's name to some random characters but not nothing more okay so we have the the answer bypass uh payload let's see what's next execution policy how many of you run into this error okay so uh this error uh yeah the light is a little bit Yeah to light um so this is the execution policy which tells us that you are not allowed to run this partial script because it's not digitally signed because running scripts is not allowed on the workstation because we are um a known administrator uh user so what
we'll do in this case basically Microsoft allows us to to set our own execution policy so for our own user to unrestricted we cannot as a non-administrator user we cannot change the global execution policy for all the users but we can change for our users which is pretty cool right we can we can basically bypass the execution policy for our user and allow us to run any partial script and once we we discussed with Microsoft about this they their answer was the following it's it's not a vulnerability it's a feature so so yeah so cool feature right and this is this is the whole this is the whole bypass it's it's just just a single line
nothing fancy nothing complex just just a single line yeah sorry if you're expecting something more complex for this part but that's it it's just abuse of a feature um and then we have the payload Runner development so let's see how we can put everything together in order to uh to inject it within the within the memory so uh we'll use also Powershell for this purpose and we have multiple uh multiple functions here including the the lookup function which is basically used to search for some uh assembly references within the within the memory and uh will not get into this uh this function because it's pretty pretty complex and requires a lot of explanation but it is used to search for
assembly references within the memory and then we have the get delegate type function which is used uh to um basically to set the argument types what it means it means the foil basically Powershell we we are using here as we've seen previously we are using C sharp plus Powershell some windows API native functions doesn't know about pointers doesn't know about uh int32 foreign so we need to to set all of them using the get delegate type function which basically is used to to pass all those uh argument types to the windows API native functions that we'll call later including the create thread uh function that will see we'll see later and then we need a memory space within
uh within the the victim uh workstation and as you can see here we have the virtual alloc function from the kernel32.dll library and we are allocating here the the memory space and as you can see we are using an integral pointer which partial doesn't know about it so we are using the get delegate type function to set that integer pointer for the for our function for the virtual alloc function and we are allocating um a number of bytes within the memory that can fit our Shell Code in this case our shell code is over 2000 which means that we need enough memory address memory space and we are setting here 3000. and as you can see we are pretty lazy we
are not using something like copper strike or blue throttle or something like that we are using meta split which should be should be caught by any antivirus Solutions in the in this world and our payload is not even encrypted it's not even obfuscated so we are generating a reverse row reverse uh TCP matter Shell Code which should be detectable by by any antivirus right it should be and then we we basically uh Define our Shell Code within within partial and using the same Marshall copy we inject the Shell Code into the memory and then uh basically into the into the memory that we just uh assigned space and then we execute it using the create thread
function and here the same we are using the get delegate type function in order to set the integral pointers and all argument types okay that's that's fine we we have a payload um bypass execution policy plus payload run sorry a bit a bit ill because the the weather here I expect it to be more uh more warm so uh how can we deploy this attack using the the little bit USB so as you have seen Bob policy uh said that removable media storage are disallowed so what what happened why it was allowed do you know why sorry exactly it's a keyboard it's it's basically a keyboard it's not a USB it's a keyboard it's a keyboard
and a mouse within a single little device so how can we program things on it um there are two ways how many of you heard about rubber duckies so you heard about Robert duckies and you didn't hear about bad USB okay so uh for those who don't know basically bad USBS are half the price of a rubber ducky or or less so why it is very important to note this thing because uh rubber duckies can be used uh because of their price uh can be used very specifically so if you have a Target only a single Target a very specific Target you can deliver a rubber ducky to them but if you have like a
whole organization you can buy a bunch of videos bees and drop them everywhere on on the organization uh smoking place or within the uh within the parking lot you can you can use them as disposable uh devices because they are very very cheap but I want to to do a sub note here because it's also very important to test them those uh are usually bought from countries that I don't want to specify the name of but they usually come with a back door mine mines because I bought like nine or ten of them all of them had a reversial on them so once you buy them test them within um an isolated environment such as the
sandbox or virtual machine in order to see what they are trying to do and then use the Arduino compiler to erase everything from uh from them okay let's let's get back to the uh to the principal part so we have two two types of deployments or programming uh types for for this bad USB we can use the digi spark scripts or we can use the docky script um what is the difference between those two basically the digi spark or the Arduino scripts can be can be used to to directly compile uh to program to directory programming compile C plus plus code on those devices and but if you are not very familiar or if you are
not comfortable with C plus plus I'm not very comfortable with C plus plus and with all their libraries that are used to uh to build things into the bad USB we can use something like that script duck scripts are basically used for rubber duckies and they they are very very very very simple to use so they have a very simple syntax and we can use a script like dakuino on on Google on GitHub I think it's on GitHub so it's open source to to convert from a duck script to to bad USB script and then just put everything in an Arduino compiler and that's it and when I say simple is that simple so uh basically this is the rubber ducky
or ducky script syntax we have here the the string and basically what we type after the string or command it will be typed by our bed USB so anything type after the string will be typed by our bad ESP then we have delays we can use delays basically um to um when we assume that the target computer is very slow why because sometimes our bed USB can be faster than the target computer so we need to put some delays between typing the commands in order to have the perfect flow of execution because you can crush or you can um it it help us for the btsb to type very very fast and the system to not receive all the
keys that are typed by the by the bed USB then REM is a comment repeat it's the it's a loop of the last command and you can repeat that last command um sometimes repeat one it will repeat one time repeat then it will repeat 10 times and if you want to uh to type like to press enter or tab or control or all the the special keys from here like shift backspace insert delete all of those must be typed uh on the on the command line on the script as they are written on the on the keyboard guy is the Windows key and with mouse underscore move we control the coordinates where the pointer of the
mouse can move and L Mouse air mouse Elmos stands for left Mouse error right Mouse and middle Mouse are the buttons from our from our mouse that we want to to press by bad USB and uh some some tips after the exploitation after regain initial access basically if we have a meter pressure shell what we can do we can migrate to another process such as explorer.xn pretty easy basically because we we have a matter platter and you can you can migrate pretty pretty easy with that one and I think this is the most awaited moment basically we'll have a live demo now we'll use uh an AWS infrastructure it seems that I'm signed out so as a command and control we'll use
the AWS just one second because it's loading
until it loads or how many of you deployed a successful attack using bed USB or rubber ducky okay one anybody else two okay two people okay
one second I'm trying to log into AWS
okay it's loading yeah so uh our our demo will be the following uh let's assume this this Windows machine is our victim the victim plugs in the btsb into the device it has Windows Defender with real-time protection on and uh we have a command and control infrastructure hosted on AWS so external uh C2 C2 infrastructure and it seems that it's loading let me see okay
uh and let me tell you until it loads uh let me tell you about something else uh have you seen that uh there are some USBS so not bad USBS but uh killer USBS how many of you know about about them nice nice pretty pretty nice okay basically those killer USBS just send some electric shocks into the into the devices and it's it fries out the the motherboard and all the internal stuff okay will SSH into our uh C2 endpoint of course using a private key here
okay it's loading it's loading loading loading come on
yeah I think also the the internet is pretty pretty slow okay
am I looked oh no I'm logged here already so uh basically let's no I I was locked out here one second
hope it will be faster a little bit um yeah basically when we want to um to test the the bed USB payloads and we want to uh to debug it we can use something like Arduino ID Arduino compiler which is used for all the Arduino boards development boards you can use it to to write and compile code for um forbid USB okay here we will use the msv console it's it's a little slow console basically the Metasploit framework for the purpose of this presentation which should be should be detectable by by any antivirus Solutions okay it is starting we'll use the exploit multi Handler which is the which is the listener and our payload will be for Windows so
set payload Windows uh x64 matter predator reverse underscore TCP so here very important to note we'll use the same payload that we set up during the generation step of the of the Shell Code and set lhost will be 0.0.0.0 so we catch everything okay set listening Port L Port 443 something common and we start the listener okay we start The Listener let's check antivirus okay um view security dashboard
and we have real-time protection on so window Defender using real-time protection on put this okay and we have the the bdsp which will simulate the action that Bob dad did so he inserted the BET USB and let's let's see what happens
okay so this is the the arms bypass uh payload uh basically here is the get delegate type function I've put it to run slowly in order to show you each function uh we have here the Shell Code that we are injecting into the memory but here it's just trying to um to Define it and here using the Marshall copy uh we injected the payload and we created the thread here and let's check our our listener and we got a connection it's meter Pressure connection shell and we got a shell let's exit it we got matter predator and we got Windows Defender let's let's try something else that any antivirus should catch load mini cuts yeah I need to update my my uh meta
split but just wait and just wait just wait oh it's not too visible so
let me put it and here we have mimiket success so that's that's basically that's basically it you you can have uh initial access so one interaction access within uh within any any devices that are running for example Defender or I have another thing uh for you here
after prevention I have a little little statistics that we will discuss so um how can we prevent against uh those those attacks basically Powershell is one of the one of the main root causes so let's let's just cut the problem from its root cause let's just disable Powershell for the for the end users disable it without any feature allowed so disable partial disable command line for end users uh for physical part uh enforce Access Control lists on the USB port uh also try to switch from an antivirus perspective to on more advanced endpoint detection prevention protection or Solutions like an ADR and also security awareness of course all all security tips sales security awareness so I
should I should also put it here uh train the users to not pick PSP USBS from the parking lot and insert into the corporate devices yeah so so is not fictional Bob of course the name is fictional was not Bob was somebody else but it was it was a real scenario so it was a real scenario it happens and you have you have pretty pretty good success rate sometimes especially especially if you have the the delivery methods um very well put in place for example as a side note uh how many of you remember the I think it was Best Buy fishing no okay let me show you then uh I think it was the best buy fishing Best
Buy USB fishing let me see yes this one this one was a real Attack loading basically they used a Best Buy brand to deliver you videos bees to to victims and said that your discount code is on this USB and uh it was some some years ago but it was pretty pretty efficient right here uh I can see what it tells but I remember that yeah if you get a Best Buy gift card on a USB drive in the mail don't plug it into your PC code by PC Mac so it's it's real those those attacks are pretty pretty real okay uh some research basically for the purpose of this presentation Windows Defender was used in order to
keep uh vendor or solution neutral um basically the issue was reported to to Microsoft they didn't consider it uh as an issue because they said you need physical access you need social engineering techniques so it's not a high on it's not basically a high impact issue especially that we gave uh real scenarios where basically our team was able to to infiltrate within organizations using this using this technique uh but besides that the the next report uh basically was using this technique so uh the the next level you can guess you can assume what is the next level so Microsoft didn't consider this an issue because of the delivery channel so let's switch a little bit of the deliveries
Channel and I can tell you that those payloads are working even within macros so if we switch the delivery Channel a little bit um they may consider it as an as an issue but the the macros needs a little bit of escaping and a little adjustments but it it works you can get to to a version that it works and you can have a silver bullet for uh for macros and uh basically the bad USB scenario was tested on 20 antivirus vendors uh seven from 20 pound uh matter Predator reversial uh basically allowed us to load mimikits into the memory 9 from 20 spawned on normal just a normal reversal and four from 20 block the attempt at
the add type function so once they detected the add type function within the Powershell they blocked the the attempt uh and I think that's it thank you thank you very much for your attention
now if you have some some questions or Curiosities yes please
text on on speed input space and when that's not the bad USB if they could see okay all this has been timed out super super fast cannot write this last there's no typos let's block it cannot look can it not be developed or is it developed that's a very nice idea I I'm not aware about something like this one but you can propose that one to to some antivirus vendors because it's a very cool idea and it can stop the the bed USB scenarios
exactly but if they copy paste it yeah yes or or simulate a human yes
uh yes for example you can remove the Sleep commands and it will be like this like in a second it will be in a not even in a second in like milliseconds so it will be lighter and fast you you cannot observe it and also for example if the the target uh has a policy in place that says okay there uh the devices will be locked out uh after oh after some minutes you can uh try to use the bed USB to unlock the the Windows screen so it is also possible space
actually none I use Linux I'm a Kali Linux you see I have also Cardinal status
any anything else do you see like they're more people when lyrics becomes more popular they're going to be more targeted viruses than malware impellers targeted for Linux and and properity virus that you can pay for ETC being developed for Linux do you see that happening in the future uh usually people that uses Linux cannot be caught very easily in a fishing attempt or to run some malware on their workstations so usually people that are running windows are more non-technical while people that are running Linux this is from an attacker perspective so if I was a hacker normally I would Target Windows uh workstations because those are being used by non-technical people and what they want to Target Financial
HR marketing things of the nature where they they have loads of work and they ignore the some security best practices while Linux users they see oh it's a it's an elf executable or it's something something nasty here yeah yes please uh yes I I have actually uh an article but it's basically the talk is based on an article uh I don't remember if I have it also on my GitHub but it's on my in in my medium article this this one any any other question yes what what popped up
okay I I thought yeah yeah yes uh and here we didn't do the uh the post exploitation but here you see the the shell is still active so it didn't catch it didn't cut the connection after some time it can stay there for days hours months so it's pretty it's pretty persistent and we didn't do any migrate to another process we have mimikes there we have the metal printer there and we were talking about five ten minutes and it's still there so sorry uh no it doesn't have that persistas it's just a process it's a threat actually it's a thread so any other questions or we can discuss after the presentation we may have a chat yeah okay thank you
very much





