CTF Introduction

Show transcript [en]
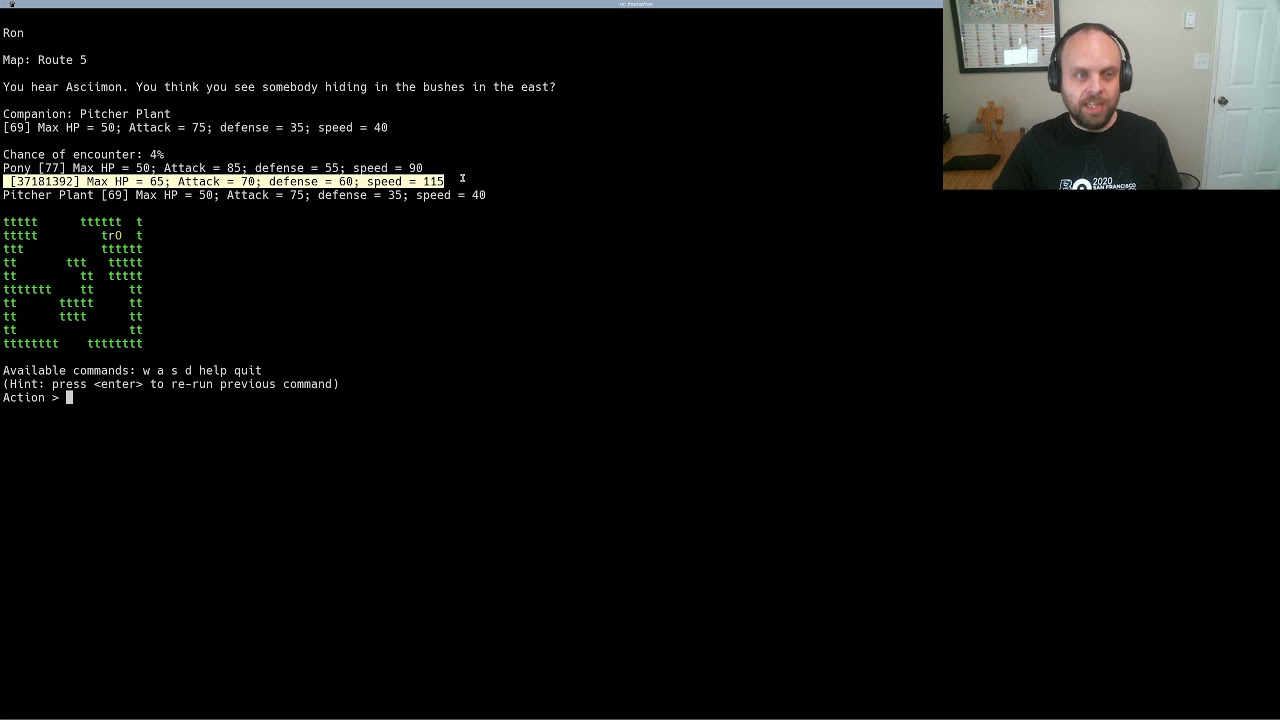
hi my name is ron boze on behalf of the b-side san francisco capture the flag team which is brandon david nero and myself i just want to welcome you to b-sides and to invite you to play the capture flight challenge this year this is our i believe fifth time running to capture the flag and every year we have a great time and lots of easy medium and hard challenges if you're interested in playing click on the ctf link on the b-sides homepage then click on the scoreboard link here and that will take you to our scoreboard where you can register an account you can play by yourself you can play with friends you can find a team on
slack just join the b-side slack and find the ctf channel and feel free to find people to play with to ask for help do whatever you like i'll give a very very quick walkthrough of a challenge called run me run me is what's called a shellcoin challenge where you write shell code which is basically machine code and you send it to us and we run it so i have a little example here that i provide if you paste that into your terminal what you should see is hello world what you'll actually see is hello world because i made some sort of mistake if you're interested in figuring out what mistake i made that might be fun to
do because i honestly don't know what i did wrong there now if you actually want to try this challenge you can either play against our server using netcat right here or you can run it locally using the run me binary so you can see i've already got the runway here so i'll just overwrite it we're going to uh make it executable first now obviously remember if you're downloading code off the internet you probably should run it on your actual machine you should use a virtual machine or a sandbox environment of some sort but if you do run it what you're going to see is send me x before i'm going to type in code and this is
going to crash because it turns out asdf asdf asdf is not valid assembly code what is file assembly code however is a streaming xcc um if we disassemble xcc you can see it's a one byte instruction int 3 which is short for debug breakpoint if we actually run that we're going to see a debug breakpoint this is the first thing i always do in writing an exploit because i want to make sure it's actually running if you're also running a debugger at the same time this will pass control to the debugger and let you see the environment the other thing i like doing is e b e b f e which is short for jump zero that means
jump to yourself jump to yourself just yourself this is an infinite loop if you run that it gets from me you're gonna see it's gnu in value and take up 100 cpu for 10 seconds at which point that almost killed please don't run this envelope against our infrastructure because that's going to waste 10 seconds of our cpu time and that makes google cloud sad probably also makes our sponsors sad all right so to actual useful stuff you're getting what's called a syscall this i found by google thing linux is called x64 these are all the things you can do read write open close et cetera and what we're interested in is this is called number which goes into rax which
is a variable essentially and our di which is the first argument we're going to find this is called 60 which is also known as cis exit and rdi will be the error code so let's just do that now we're going to remove the old halo arrow we're going to start a new payload it's a 64-bit application we're going to move rax to 60 that's this is called none rdi would be 1337 that's the exit code and then performance is called if we compile that using nasm which is short for the n assembler i don't know what the n stands for we can assemble it and we'll see this assembles to about 12 bytes of shell code if we run run me
[Music] with that code we're going to see nothing obviously happens because you just face it s trace or system trace tells you all assess calls being made including the exit so this does the exit with one three three seven which is the error code that we chose now if we wanna do a real exploit we're gonna do more than just exit we're gonna need to do a open to open the flag file read and write i've already written an exploit for that called xflight.asm explain asm as you can see doesn't open a read i write and then exchanges to be polite so we're going to compile or assemble that and run that and we're going to see
that that doesn't deepen the real flag if we s trace this we're going to see it opens because file handle 3 it reads and it writes that's all if this doesn't work for you make sure the file actually exists and have a great day