Ross Wolf - The Hunter Games: How to find the adversary with EQL

Show transcript [en]
and if your help and if you're not here for Ross you should say anyway cuz it's a cool talk yeah so I'm Ross wolf this is the hunter games we're gonna talk about how you can find the adversary in your network using eql so bought myself Ross wolf RW access on Twitter you want to follow me you know I don't calendar I think I'm a threat researcher end game so I do a lot of work with our events so like when I say events I mean like endpoint telemetry processfile network activity that sort of thing I'm so I try to take those events and say how can we turn this into a detection how can we um
create new frameworks for for detecting things and so as part of that created the event core language which we open-source last year and a lot of like this entire ecosystem around it and I have a background like before in game I was at mitre I did a lot like a red and blue teaming there so I'm kind of coming from that mindset of them if I'm red just like that usual Purple's test of like if I'm the red teamer what am I going to do to evade the blue team that were usual at cat-and-mouse game of them how can you actually find something and oh what's this an email bad wolf report are we compromised like never mind we'll
get back to this unless oh there's an update all right so this whatever is happening right now I should probably pause let's look into this report what are we okay bad wolf execution flow tiny graphic but I'll just give you the high level starting from like drive-by download through like lateral movement eventually gaining privileges moving across and there's some like dis decryption going on or encryption sorry I've been interesting but like if you get a report I don't know if anyone's ever had like an email like here's this new report here's this latest threat actor do we have them in our network can we find them what do we what do we even right how do I search this I'm sorry I
want to take that question and give you an answer to that how can you find that and as I want to answer that what's the knob what okay we have a report now what do we do about it and how do we get ahead of the next one so overall I kind of want to talk about like how can we take all the adversary behavior in general and use the attack framework to organize it and organize and orient our approach to writing detection z' i also want to go through event crate language and give you just basics of how to write your own queries and then i want to follow like what a real threat actor does going
along the way and staying like okay if their next step is this how would we write a detection for that and then there's also the question of well what if I don't have a report I have nothing to go off of how can I find something either suspicious or find something that feels wrong for your environment and then finally like one thing that this is like why we're all here it's like we want like contribute to the community how can we take all these new detection s we're gonna write how could we share them with other people and express them in a way that's easily tractable and what like what are we doing an end game to try to give back so
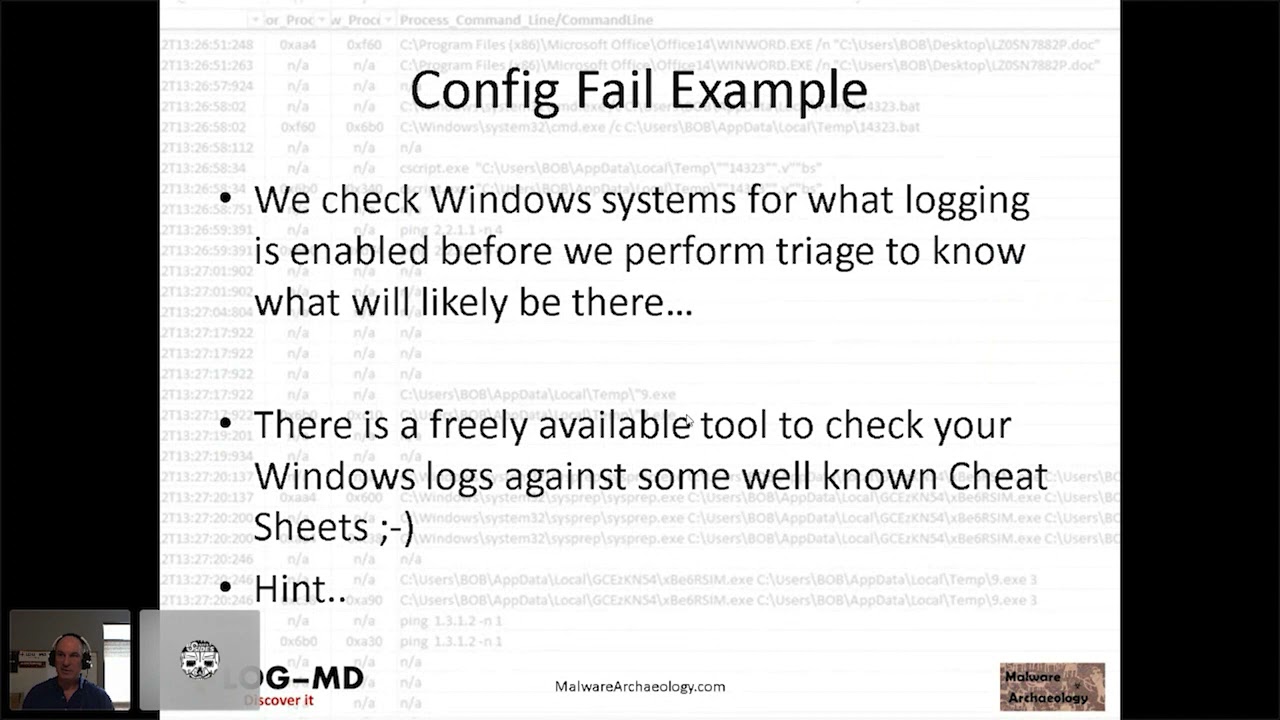
start with like threat based detection like what's our what's our general approach and process so this is loosely based off of um paper from my past life at mitre but in general is like okay how do you start with attack start with your understanding of the threat landscape and instead of just thinking like alright we have these iOS es do we have this hash it's like well that's great but that's going to answer one question as soon as something changes like it's useless so like how can you zoom out just a little bit I want to go through like what the attacker does and in your network like maybe you don't have you don't have like full event data maybe
you don't have file events because maybe they're just too expensive to collect so like understanding what makes sense for your environment and what data you have what can you work with this really important because I'm how can you write anything if you can't even if you don't have the data your queries will just never match anything and then the next part for writing writing your own detection is thinking my platform is maybe some sim and what's its query language what capabilities does it have like can it can it do like aggregations or something and if you can't do that maybe you're not going to write detection is based off of that understanding of what those capabilities
are what logic you can express how you can like join your data and then finally one of the last things is like well yeah okay you took a report you wrote a detections like does it actually do what it's supposed to do and part of that process is is red teaming essentially or having having these unit tests so atomic red team is a testing framework that red canary released from mitre has called era and game released red team automation and there's there's a handful more that you can use but the point is like you should be you should be testing the stuff that you have there's a lot of these things they're essentially a red team in a can a small
little script that does like one behavior so it's a bit out of context but if you want to like say okay well how do we guess something that's real not just like this one technique but how do we detect how do we detect someone that's like operating and using the specifics of my environment against me so like human red team's are also very important and it's also it's also okay to be willing to say that when you write detections they can be wrong I have we've had a lot of guesses like this will never fire in Windows and then it does and I just like ask myself why and you see software doing the strangest
things and a lot of the noise that I run into is like automated software which means that it's on every endpoint so if when you make like a a mistake and you're trying to tune something you're often doing a like a scale like every time so being able to think that like is this is the entire hypothesis I had just wrong do I need to rethink that and that's like I think that's a good healthy process to do and sometimes like if like if you run like your searches on a schedule or something like that's like CPU cycles you can also get back so there's also very practical reasons to up to retire things that are producing
fruit so that's kind of a high low of like how do we write detections what what's the mindset that I'm taking as blue a but like as a red team what was going through like my head as I'm trying to compromise the network cuz it's often like the same same goals that an adversary has right they want to like eventually find your crown jewels like steal your files or like maybe it's like some ransom or thing or something but also when there's some goal and it's there it's on your environment so the first thing is like I need to get into your environment so that's gonna be like some spearfishing err most of the time it's gonna be
spearfishing and then it's like okay I have code that landed but is am I in the right place and so there's the next step is like as a red team or like I'm on the right host run a hostname command and then if it's not if it's on the right place actually having some code to persist so like when the system reboots once the user logs off you're not just screwed and don't have to resend the email again or hope for someone to double-click on something then from there it's like okay you have code it's running it's persistent now you want to actually take control over it because you actually need to do the part of your
mission that's that's your mission so I'm taking over had like a network connection back and then from there gaining credentials privileges moving around the network between hosts ultimately like collecting and exfiltrating information or sometimes you actually like like in trucks in that case like you have a very significant impact you want to make and that's also like a good part of like attacks like what was the maybe the objective wasn't steal data but it was like to really like make you ineffective at your mission and so like all of these things is going through the adversaries heads so one question is like how can we write something like each step of the way and create this layered approach to writing
detections oh right I forgot one and on all these things we're trying to do while trying to evade the products you have super thing about that like what are the things are gonna do to try to evade and how can I turn that against them be like okay are trying to hide here it's like I'm gonna look there and all this is like looking at the attack framework so all these steps were taken might organize them and to attack essentially if you've got columns which are tactics they're like the high-level objectives that I was going through individual cells here are the techniques like what are the individual methods to achieve that goal and there's like so
many threat reports in here and every technique has like what the technique looks like how you could detect it how you could mitigate it what data is useful and some real-world examples of it but there's not like here's a query run this so I want to kind of get from how do you go from here until under all this knowledge into something that's like operational and the next thing is like okay you know what the threat looks like you got to do their mindset like what's my data in this exam this slide I'm gonna use system on it's like free open source pretty easy to use and they're datasets pretty rich you often have to tune it down because
there's so much data and one example of an event is like it looks like this at the bottom command line process names users pidz peep it so you can even like rebuild a process tree with it so there's ends up being a lot here that's kind of like one example of data and this is might look different for you or maybe you don't even have endpoint to and you're looking at network telemetry but understanding that is also very useful so we have the data does maybe you don't have equal but what what your query capabilities are just pretend that this is those or just read all these as pseudocode that works too so we wrote it
we try to be concise try to be simple when writing it it's not tied to any particular schema so even though like we use it an end game we don't it doesn't only work there and I'll get into more some like demo of using it and it's also oriented around like a real time approach so even though you could use it for searching you could also take this and like run data through this pipe and get things that are matching as it happens another thing about this is I know that a lot of these behaviors that you're trying to detect are like you see a process that drops a file that then executes it makes a network connection
like it's kind of complicated and saying like give me just a network connections that look like blank like you can't really anticipate that so visually important to make sure that we could support things spend multiple events find an easy way to connect them without having to deal with the sequel inner outer join I honestly never remember so I try to avoid that exact problem and then instead of like having like crazy syntax like contain starts with everything we just have like a function notation that's just our design choice so at the very basic level we're looking at like comparing fields two strings wild cards quarry might look like this and equal it's like the simplest form
and probably see one so this is just looking at process events so uh I think I got a laser I can do too it's looking at like process names this is a field on our schema that matches SVC host and either the command-line argument doesn't have - K which as we see oh so it should or it comes from or doesn't come from services this is one thing like find weird SVC hosts boom here's like easy for you want to go so this is like at the start of like this is what like a simple equal query would look like but we can also do sequences so maybe have multiple events in a row how would you write that and so
the thought is you can say sequence with a max span of five minutes so within these brackets here you have a standalone query like from the last slide so this file where file name is star dot exe well that's the first event grab the user and file path and then match that to a process event but the file path now like became the process path so that might be kind of confusing to say like out loud but essentially these fields that you're joining on have to match all the way across and it's not like some crazy complicated sequel joint it's always like exact matching there's also unordered sequences or joins so like tell me if these two things
happened so I could say that was there a file to this location was there registry modification to this path if there was both you get a match if there was only one you wouldn't you could also again like add this by for um sing are there three incoming could network connections to these three ports between these two houses so that's another thing you could do with join another thing with equal is like yeah it's nice to describe something you know what you're looking for but if you have a lot of data or sifting through it I want to make that easy as well so we have pipes it's like unix-like or if you know Splunk this should translate pretty
pretty easily so looking at like here's one like looking at process events and then removing duplicate like command lines and then from there if you count how many things there are per process you know how many unique command lines there were for process so the thought would be here it's like could you figure out things that are have command lines that are very predictable and if they have less than like five command that's normally maybe you could watch for deviations this is just like one example of something you could do with a couple pipes another cool thing one of my favorites is that we can track process lineage so if your events have pin and peep it we
can just chain those together looking at creations and deletions or terminations so we could write a thing that's like look for network from PowerShell processes but not ones that came from Explorer dot exe and so we could watch the whole chain and be like okay then this checks back this does or doesn't track back to Explorer and then we could use like event of and child of as well if you just wanted to like little smaller ways like if you do child of child of child of child of you can nest them as much as you want if you want to validate like an entire tree checks out so that's like just of what equal looks like let's actually turn
this into code something we can actually act on and take those bad wolf reports and make it useful so how do we detect behaviors that we already know it exists we already talked about how to what the adversary does what their mindset is mindset is and a little bit of attack of what specific techniques are but we're gonna go let's go through some more some more specific techniques and say how would I write detection for this so first technique is that initial access your spear phishing email how would you detect spear phishing email one thought is a lot of the time you're gonna see malicious macros and those are gonna run like in the context of an office product
and then those macros often will run PowerShell or some scripting host or run act like a batch file or something so you could look for a parent process relationship did a PowerShell come from word and something as simple as like that actually does really well not there's not many legitimate use cases for having office like VBA running PowerShell and if there are talk to me after cuz I'm really curious to what you're trying to do another option would be like maybe you don't have power cell running but it's a script that drops the file and runs it so you can say okay within like a five minute span look for exe files dropped by Word Excel our
PowerPoint like this could also be like in attachment but hopefully you have filter setup so your exe files are not directly in the middle of emails so looking at like word creating them and then I'm running within like five minutes like well why and a lot of times it's trying to break out a VBA so that's one thing you could do another step is like okay access has gained now privileges need to be need to be gained like it's escalating a system persisting so that way you're not kicked off with the reboot so one thought here is and this actually happens so that bad bad wolf report was actually just bad rabbit but renamed so bad rabbit one
thing they did was actually take scheduled tasks run the mess system but the user that's creating the task wasn't system it's like this is really weird to me cuz I have to ask like why would why would any normal user even at admin it's also weird why they need to run code a system why is it administrator not enough so looking at looking at like that deviance here like the user on system the command line contains system there that's for me to test detect Purvis quit scheduled tasks another attack technique where things get hairy is like command and control so as far as there go in an attack it's just saying like it's almost like they took all the
network connections and just pulled out the metadata of it like was the port common or not is the protocol common or not and it's the combinations that make that interesting but if you just want to say like I'm looking for uncommon ports in my network you're gonna have a long query like I didn't even make it to like four four three so there's not even SSL in here so this could go on for a long list and even then you're gonna run into false positives like between hosts RPC you'll end up creating like dynamic like high ports or or maybe there's some a new protocol that something else has and you're just gonna run into like alerts
and alerts alerts and more alerts and you're gonna have a really bad time if you try to do that so a different approach that we try to say it's like well instead of thinking like what's weird about the connection is maybe what's weird about where this network connection is coming from so what processes are really weird to be making network connections so there's a wall bins or delivers words like you never say out loud you've read it but I don't know or Lal buzz the living off the land binaries and scripts it's like tools that are built into Windows you don't normally use but they allow you to gain code execution by like dropping like some interesting like what
is it the XSL file for the MSX SL I just I have a point around yeah so that's one so looking at these programs and saying should these be making network connections and then cool thing about turning us into like an equal sequence is now you have the process creation of it tied to the network event and so you can look at the command line and the destination address at the same time it's like oh that's interesting this was outbound and it has some weird weird like that are you and the command lansing that's interesting another tactic moving on down through the lifecycle like blending in so where was the file actually placed one thing
that you'll see and it's I think it still happens is thinking of programs that look just like normal windows processes so there's like core Windows programs that are running if you look at task manager it's never empty right there's all this built-in things but they always run out of the same place they're always signed by Microsoft so their names are common targets like or else asks a common was like what once a star else asked with two S's so there's another thing you could look for words like mismatches but look at these in the wrong place so there's one example I'll show later with is like see windows system32 slash INF slash alsace so even
getting this part of the query where you're looking at it's in system32 but not in a subdirectory is one way to anchor this until we'd out like and to get it like just precise enough so you don't accidentally whitus the whole directory recursively another approach for finding things that are kind of weird maybe you've got some injection detection but maybe you don't if you don't want a way to try to infer it is think of programs that were like looking for like process howling like it starts a child then it puts code in it is looking for programs that ran from the wrong parent it's like built-in when Windows boots up it runs things like in
an order and that's it that's the only time Alsace runs so if you have like to Alice asses and your task manager you should check you might have accidentally down with some Stuxnet malware or whatever else so looking for processed creations looking for extra versions of those running with from the wrong parent is one approach for looking for looking for like masquerading and process injection another another command you could go like the Mimi Katz approach and try to find access this tell SAS or you could say it was anyone like grepping through four passwords I know it's is this one like why is this query taking up such a small part of the screen because it actually
has worked for us I don't know why but Red Team is actually running through here like you should be doing your grepping like client side but we've actually seen like red team's from this one as well it's just I thought I thought when this was created it was a joke but it's worked another one looking for discoveries like recon commands that have been kind of tricky because there's so many different ways you could do it you could say like five in us in two seconds or something else but I just created a couple buckets of commands it said was there something from each bucket because you might see 10 different IP commands in a row IP config
commands which I've done but how often do i do IP config and look at processes and look at what users are installed not very in the sort window that's suspicious so that's one approach looking for lateral movements like you could look for a remote powershell looking went over when RM so seeing an incoming network connection followed by that power saw provider host and then since you've got both of those nice thing is you you know where it came from you've got the incoming source address and you have like the user that the process ran ask so you know who's running from real powershell as well another ones looking for exfil a lot of actors will bring WinRAR themselves I
don't my guess is that it's not open sourced and they can't compile it in so let's bring the signed version and just drop it on run like the HP flag for encrypting and then it creates a rar file they grab it back so looking for that this one is a little bit cheating because it is oriented around a specific tool but collection is hard kind of hard otherwise because otherwise you're looking at like every file read event and that's that's tough on the last one for the is like impact so what what ways was the environment negatively impacted one command for cleaning up tracks is deleting volume shadow copies would be like a couple of built-in when those
processes or clearing ones the nut logs and here's just some some commands you could use and I could search for them so that's all that's all nice but all of those I knew what I was looking for so what about when we don't know what we're looking for what what are some general approaches we can have to hunt and this is where it goes from like how do you how do you detect for known things versus how do you hunt for this known unknown so one way I kind of think about it is like all right I don't have a threat report yet I don't know who the actor is I don't know what they did I don't know why they're here
but maybe they are so someday someone's gonna write about this so eventually you'll see a report that looks like that but today the info you know is very little answer like well I'm on a look it's like can anyone help me out and that's kind of how that feels it's like nice later but I'm not gonna do that to you I'll give you some approaches for what threat hunting is and to make the talk a little less dry I've got some memes sprinkled throughout so how do we how do we proactively look for an adversary it's like well we know how they think let's use that against them we without looking for particular techniques think
of like what evidence does a tradecraft leave and specifically what makes that weird in my environment so what things are happening it's like prevalence by that I mean what things are happening on just a few end points out of a lot what things are just happened within the past couple days we're like what patterns do you see like every night at 9 p.m. there's a network connection going here what's that about so those are just some general approaches for like sifting through your data for threat hunting so one question you could ask is what parent-child processes have like wonder what child process relationships are new or rare in my environment so you could look at
process creations this is kind of like the other one where had that long hard coded query but you could say look for a lot of these and find what's rare and then sort those ok sorry there's the unique count pipe so this is going to take all the uniques remove the duplicates but add a field back saying how many duplicates there were so of those now you have 100 most recent processes that were seen for the first time of though it's like take the top 10 rarest one so there's just a way of getting that rare and recent question which are kind of hard to mix so I've got some data in here too one of these
there's some benign activity that you'll find the first one is like a random parent process name and then the one at the end is also like a random random child process name I think so those will always be noisy because they were the because the names are random but there's still things that show up in here and let me get the pointer back quick now one thing is looking for like what are new parents and children of power cell like there's power saw running this running run dll 32 with the dot file with a random name and then some entry point that we don't know so that actually brings up an interesting point is like maybe we could target this a
little bit better and say what our new parent and child processes of PowerShell and now you get all sudden all that noise kind of went away and you got this thing that sticks out because this PowerShell had never spawned this before another question you could ask is a what a I'm in what recently first scene processes have made network connections so they saw the process you've never seen it before and it made a network connection a question I would usually want to ask is why and a lot of the time you'll find like installers that are like to stage it's just a tiny little download file it's like oh cool it's not like 500 makes and then it that'd be a
lot like 500 kilobytes and they're like oh it's got down like 50 Meg's it's like okay that explains the network connection so you'll see like if you try this hunt in your environment you'll probably see like setup files but might like reach back like here's some that we that I've seen but also can find this living off the land binaries from earlier like install util maybe it normally it never ran before and the first time it did it made a network connection there's another thing there like that install util one is you could look for things that have have run before in your environment but every time they have they never made a network connection but they did now so why why
the change why the sudden change in behavior so one question you could ask is like are yeah what can happen what have I seen before like this date but the first time made a network connection was after another date that's kind of what's going on this query why is wise hide the paint Herald suddenly on the phone so another one is looking for a privileged escalation so files that were dropped by an on system user but they somehow made their way up to system in the short time so how do they escalate that quickly that's a good question that I would want to have answered but there's there's still some noise in there that sometimes
we're like you'll run a program and it escalates itself I don't know why that's always necessary but sometimes software does that like zoom as one example I've seen but then this this INF SVC host one from earlier up top is some example of legitimate that's PI small legitimate activity they're not legitimate sorry that would also be very suspicious to look at that because now you're looking at two different things that it would have triggered another one to think of is looking for recon commands so we have the whole approach of looking for things and buckets and trying to do some fancy foo but one thought is a what programs are being are making outgoing network
connections and then asking for information about the system that's kind of a weird combo what's going on there and you might find some noise in here maybe you'll find some admins doing something that's generally the trend of noise but that's one one more thing you could look for another one is looking for a brute-force activity so seeing a lot of log on incoming logon failures so this is looking at Windows Event log so switching from ik processes files networks to looking at Windows log activity so that Windows has like 46 24 for logon events that's the event ID and four to 625 for failures so the thought for this one is what if you see five failures
before you see a success and you eventually do see a success and then until part of the sequence is saying if I do see a success before I see four or five just ignore it reset the counter for that for that IP and so this would find cases the cool thing about this is this one it just find people brute forcing a single user but doing like a password spray so like okay I got a bunch of crash passwords I don't know what works on this host I'm just gonna throw them all at it some of them or fail some of them well but if they like fail too many times before they success not like now they tip their hand
to you and one last one is a have more than one more looking for WMI so w is kind of an interesting beast in coming WMI process events so like the w my lets you remotely spawn and manage other hosts so one thing for this is if you have an incoming if you have a process that was created by a network connection mm I will give it a brand new token be like alright here you go you're coming for a remote thing you don't exist on this used on this host here's a new token that ties with your logon session here you go and run the process but one thing that's cool about this equal
approach is when you do a unique you always get the first thing that matches so for every token what's the first process that did and then you can check you can say was the first process that used this token WMI or a childhood of mine if it was then you know it's creative remotely or created by another user locally both of those are weird cases and here's some example of noise that I've seen before some necess that I'm guessing has like RT log ons logging information to testing whatever and and then also some Lazarus group actual like what that looked like with the IP changed that was basically right out of the report on the
last one is looking for a suspicious lateral movement between hosts so this won't work on a workstation or on a server sorry you run this on a server you're just gonna blow up everywhere you'll find what all your endpoints are in your environment fast so the thought is what about incoming to a workstation or maybe a different type of server so all on a host looking at what look at incoming SMB and RPC sometimes you'll see incoming SMB like connecting to windows file shares dropping a file and then using RPC to execute it or to do something else so you kind of have the like the copy and the execute sometimes you can find it this so that's kind of
some techniques I've got for hunting with hunting for things you know hunting for things you don't so what can great now how do I actually use any of this so we've since we've open-sourced equal you can just install it it's a Python package you just pip install equal there's a CLI you can run equal query but that's fun let's actually like do something so I've got a as of this morning a demo why all right cool let me switch over to this quick right on all right so we've got this equal shell that we've got CLI that we use so there's no like UI here with some fun tab complete too much time spent on the
tab complete so I could load this data file so like let's load we since we a 10-game have released like several data sets here's some you can use so you've got this data set here normalized RTA there's 31,000 event so we looked at them the cool thing is since I've looked at all those events just then I figure out what the schema is so like network events have the have process pits and those pidz are numbers there yeah network and file in process I'm looking at different than we figure out like what you can do so now you could actually perform a search and I could search for like maybe I just want to count of all of all the different event
types like how many process events how many Network events how many file events like okay that's kind of cool you get some JSON results you can see that most of the data is actually registry so maybe that needs some tuning so you could then like render this as a table like okay that's a little easier to read another thing you could do is looking for has anyone heard of squiggly-doo so there's this technique called squiggly-doo that I think it's a Casey Smith thing and one thing for one thing this one did is it was like register read server 32 so I'm gonna try to type and talk and see how this goes but it's a process
event coming from reg server 32 and it's a sense it's a creation I want to get process creations the next thing is like okay we with the scribbly to attack it would also load this dll so I could look for that image load where the image name equals scrub dll and then finally so that it executed it loaded this dll and then I made a network connection I don't really care where it went so I'll just say ik we're true cool you can still see that and that's that's it for that query so we got three results my table messed them up so if we saw a table we could actually say okay well here's the
process event a ran as Alice the parent was Python and this was our TA running and then I load the DLL and made the network connection so you can play around with your data ask all kinds of questions in here to make it a little bit more tangible those kind of one what hope of all this it sounds a bit of like what you can do with equal what it actually feels like we also have this analytics library have you posted it's called like the equal equal Lib and we've gone through like attack so far if we created 45 or so analytics and read Canaries contribute a handful as well there are there's also some data sets I
just want to play around and ask those hunting questions just like I did yeah we've got sort of data sets you can use it looks kind of like this we've got attack essentially annotated with all of our detection so if you're trying to orient your approach from approach around miters attack we've got a way to like kind of build your coverage out now and you know if you have a different data set there's also ways that you can take a query that we wrote and equal against that schema and convert it so you can you could take a query looking for the MSHDA with a certain command line is this one here but we can actually convert it to map to
your data so as long as you say how to how to go from one to the other and there's mappings in there for a system on and for one or two other ones we can even even convert things we're like maybe you don't have a processing but you have the full path let me know the name part of the path it's like that's something that we did here so yeah so over the next couple weeks we hope to update equal as well get this that CLI that I demoed probably over the next day or so get that public adding a Python API that we have so if you have other projects in Python you want to just you
say okay this CLI doesn't really work for me but I do have a real-time stream of events that I want to like build my own if you have some intrusion detection system you're trying to write or something it's all streamable so you could stream data through and get it straight out and then we're also working on the 75 maybe 100 more analytics map to attack if you're trying to increase your coverage and get more that we plan on sharing and if you want to follow equal you can around Twitter and get er which is like a chat let's kind of slack like a couple thing about it though is that you can use your existing like
github or Twitter account so if you have one you can even lurk so you don't have to let us know that you're there you can just watch even though there's not like two comments and they're so far and they're both me there's also like an email if you're like super old-school and do that thing it's equal equal endgame comm and if you want like resources we've got several blog posts this is all and read the docs so there are stocks to read and there's get repos you can clone there's also a guide oh there you are yeah Paul and uh Devon from any game wrote on just a general guide to threat hunting it's not equal
base at all but just some of these same general techniques like how do you find weird registry rights we've had like there's an e-book on there you can download and that's yeah that's uh that's it for me do I have any questions sure there it is I just said we did the attentative announcement elastics in the process of hopefully acquiring endgame sir plans that like integrate some of this stuff into like the Cabana front end for elastic databases and love urges against their schema or a great question I can say basically nothing but there's a great blog post that you can read that's corporate and official on I think the elastic and the endgame side so if you do want to follow
more basically that automatic I can't / - sure any other questions alright great thank you [Applause]