Hacking Secure Coding into Highschool Education
Show transcript [en]
hi everyone hello thank you so much for staying until almost the end thank you I hope that the suffering in Israel will soon come to an end and the hostages will come back to their families and without further Ado welcome to aking secure cording into high school education my name is OAR I was a developer for many years almost 10 years ago I switched my career path into cyber security my drug of choice is snowy mountains hi everyone my name is yariv tal I'm a season developer um I lectured in universities I mentored in boot camps and a couple of years ago I became an absc researcher my drug of choice is roller coasters so why do we
care why hacking secure cording into high school education why sorry 2024 and God is still insecure the same vulnerabilities appear again and again y are we still talking about SQ injection amazingly enough or we still are and SQL injection was first discussed in 1998 it became a part of the oasp top 10 in 2007 number one in oasp in 2013 2023 we still saw SQL injection in the move it attack 2024 cesa in the FBI issue an alert they refus to see any more SQL injection in code good luck to them refreshing isn't it and the same goes for accesses file upload malicious fire upload and more and more so what are the current ways of
dealing with it one way to deal with it is hiring an absc professional a Wonder Woman she has to deal with tools in integration configuration interpretation she also has to deal with teaching secure coding sometimes she's also the security Compass of the company as to um to say her word in a discussion about the product a Wonder Woman isn't it another way to deal with it is to use tools tools like SASS and dast and SCA tools that produce millions of findings some of them are true positiv many of them are false positiv and then you have to dig to find what is relevant and what is not relevant and this is only if you are
lacky and your or your organization has budget for all these tools another way is the security awareness and training and Me Myself and I sometimes the organization invite me to a full 60 Minutes of awareness but to be honest I'm not so sure that immediately after the talk the developers run through their computers and fix all the vulnerabilities some sometimes I'm lucky they invite me for a workshop sorry I like to move um they invite me for a workshop and then I have five or six hours and then I have two option one option is to build a tailor made Workshop something that respond to the H to the set of Technology is of the
organization and then as my colleagues from other firms can confirm it's not profitable the other option is to give them something that is more or less what they need for example if they develop angular I can give them a workshop with VJs I can promise you if you do it it will build it will be the last time that the developers will attend a security Workshop from their own will so what can we do well there is some good news um and the past couple of years we've seen new languages that try to handle uh secure coding as part of the language everybody here I'm assuming has heard of rust trying to get rid of
memory management security vulnerabilities um um other languages also try to address security issues for example cotlin has some secure default um there are actually extensions to Java that add security features and we have better apis we have better apis that come with secure defaults uh we have security embedded within platforms uh for example jot originally by the standard you can use uh uh instead of signing cryptographically you can choose to use no signing but every library that I've been working with for the past couple of years just won't let you do that so that's the good news but the real question is why do we need this huge ecosystem to handle all of these vulnerabilities why can't we just ask
coders to write secure code why doesn't it work and to get to give you an idea my son is in high school somewhere in Israel and he's been learning internet programming otherwise known as web programming and they have a login form and this is what their teacher told them how to do the sequel to authenticate so who sees one vulnerability here okay come on participate raise your hands you can raise your hand more than once two vulnerabilities three vulnerabilities not a lot of hands there well this actually has at least three vulnerabilities that we could find okay so the first one who wants to shout it shout SQL injection yes everybody knows SQL injection right well we're supposed
to know it but it has SQL injection second vulnerability clear text passwords yes third vulnerability there's authentication bypass here because it's like yes you can you can pass percent as a password it will match anything so students that learn programming aren't taught to code they're not taught to write code they're taught to write vulnerable code This Is How They are taught to do it now you can say okay we'll teach them how to address this later but we all know how hard it is to improve on bad habits it's really really hard so it's no surprise that they write vulnerable code this is what they are taught so even before this confirmation we realized that we have to shift all the
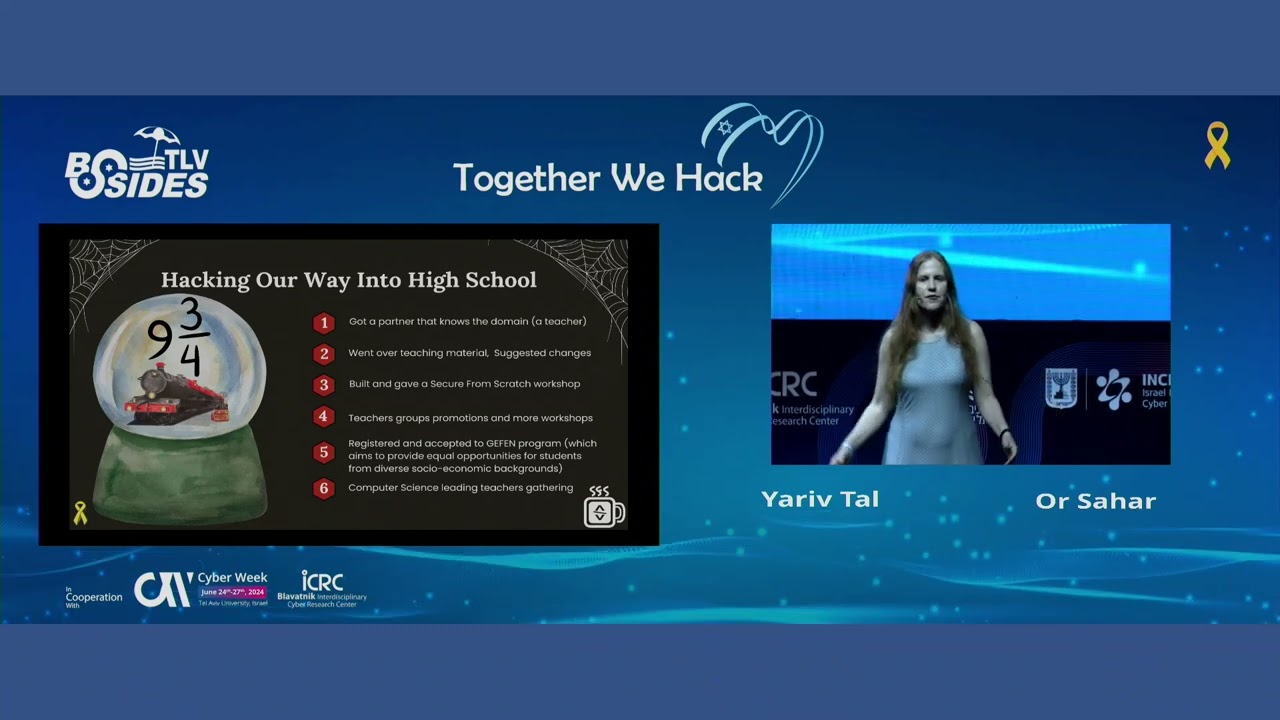
way to the left to the beginning of time before the developer became a developer so how did we hack secure coding into high school first of all we got a partner a friend of us who knows the domain perfectly and a teacher he gave us gave us an access to his Google Drive 300 uh teachers computer science teachers enjoy this drive uh when preparing for their class and then we decided to change the materials we decided to H we we try to add the security concept into the current lessons but we didn't Advance very quickly we also worked for our living so at one point our friend gu Ram the teacher the great great teacher
told us come to my high school please gave give Workshop to my students and that's what we did we prepared a skeleton for his students they coded they hacked to their solution not something that we created they hacked to their solution they they fixed their solution and they were very happy and also the teachers were very happy they were so happy they they they start to spread the world about secure from scratch everywhere in the WhatsApp in the WhatsApp groups of teachers and teachers from all over Israel started to invite us to their school it was great because it was after uh October 7 and we felt very good that we can do something for a
living more or less but also give something to our country so they told us about also they told us about the Gein program which AMS to provide equal opportunities from students from all over the country uh we registered to the program and uh something like a week ago uh and they accepted us so next year it will be much more easier uh to teachers to invite us to their school and we also H joined their uh Gathering they had a gathering uh the computer science uh teachers they had the Gathering in Jerusalem this week so we gave the workshop to the leading teachers we got a lot of feedback a lot of good advice how to reach our goal
that right now is in the sky which is change the education material and to add the security concept to every computer science book every programming book so before we continue there's a QR code here for a poll we are running on LinkedIn um do developers need to know about or top 10 uh we'd be happy if you could scan the code and give your opinion on this poll we'll publish the results on Friday that's tomorrow right yeah um I have my own personal opinion you'll probably understand what it is on the next slide but I'm going to talk about how do we build workshops that high schoolers like and high schoolers are very much like developers and that they
want us to cut to the chase they don't want a lot of theory they don't want buz buzzword they don't want acronyms they don't want to hear about all the types of vulnerabilities they want to work on the computer as much as possible in be interactive as much as possible so the first thing we do in our workshops is we focus on coding we don't focus on analyzing the code we don't focus on teaching them bad H find the vulnerabilities or things like that we focus on coding I have to remember this yeah okay so so the second thing is um in order to save time we H look for a simple yet real world scenario for example we take
a trivia uh program like cahoot simplify it uh because they're high schoolers we might even simplify to a level where there's no networking and create give them something that it's like a trivia program they can easily understand the domain they can easily understand the code we also give an initial skeleton code that they can immediately compile and execute H this allows them to start working immediately they don't have to start from scratch they don't have to write a lot of code before they can see the results if uh if our goal is for them to implement a feature will give them the a mockup of the feature so they can execute it see that it always returns
the same hardcoded output and then implement the feature by themselves if our goal is to let them uh have some experience in finding in hacking they can execute the program try to enter invalid input see that they manage to hack or they manage to hack the program they don't have to wait with that um then what we do is we make this in phases each phase we highlight the security problems they suggest suggest uh solutions they go and implement the solutions again we highlight the security problems in those Solutions you usually because they're high schoolers all of them will give uh insecure solutions to the problems by the way with professional developers it's not much better 11 out of 12 developers will
give an insecure Solution that's our own statistics um so again we suggest we let them suggest Solutions eventually we show them a secure uh coding alternative we explain why the secure coding alternative is better what's the mentality that makes it better and then we finally we suggest infrastructure turning this secure code into infrastructure so they don't copy paste it every time instead they can write a function a Class A Singleton H the problem is there's a lot of material about secure coding we can only give them the tip of the iceberg so what we also do is we tried to condense the principles behind secure coding into a seven-letter acronym we call it prevent so
prevent P is for P is for priority permissions and privacy 2024 we have to put security as a first priority R for reporting and logging we have to think what we want to log what details we should include in the log and what we shouldn't and what we choose to report and what we want we don't want to report e for easy to use securely easy to use safely sta this morning mentioned the file upload in every programming language we have the file open method and this method is vulnerable by Design what if I want to create an infrastructure that is easy to use safely then I'll create a file open with a directory parameter and then
I'll make sure in my infrastructure that the the file that the user want to open belongs to this specific directory verify refers to maybe stock overflow rip now it's generative AI so we have gini and GPT and a CO pilot and believe me I try I have a full Workshop about generative Ai and if it's secure or not what do you think who think it's secure nobody okay thank you thank you refreshing error ah verify also with refers to code review I believe that most of the developers conduct code reviews just add the secure part to this process and errors we have to deal with errors and exceptions sometimes just to save the resources and to protect ourselves from
denial of service sometimes other vulnerabilities we have to log the exception for sure nit nit code security by Clarity I think that nobody thinks that spaghetti code will protect us from hackers also the generative a high can help us with this as hackers we can give the generative a high old this spaghetti Cod that we don't don't understand and it'll help us with that but if our code our own code is Getti code we will never be able to spot the vulnerabilities so security by Clarity t for trust trust boundaries whenever remove data or control between entities with different trust level we have to take proactive actions it could be sanitizing verifying um do something maybe thring
an exception yeah so these the principles they sound very basic but surprisingly not many developers are aware of them you'd be surprised how many developers are not aware of logging for example but oh can we also help existing professional developers do workshops yeah I believe we can but as I said before if you if we are the Security Professionals create a tailor made workshop for for every customer and customer will not be able to make living from the other end I don't want to give the developer something that I don't like so that's why we created a g up repository in this G up repository there are workshops Labs skeleton for labs for high school students but also
Pro for professional developers and I hope that all the security professional would join us and develop together a repository that can help us to give the best experience that we can give to our clients so what can you do you can share an idea for a scenario you can develop a lab you can also conduct a code review you can create work through it could be recording it could be textual and also if you don't have time and believe me I know we don't have a lot of time if you use a lab please share your feedback it could be very very useful so and the most important thing spread the word about secure from
scratch tell your friends tell Educators tell your mother okay so let's summarize 2024 and it's not surprising that we see the same vulnerabilities again and again developers are taught to write vulnerable code it's not just in high schools I've seen the materials in universities I've seen the materials in courses I've seen the materials in in boot camps they are taught to write vulnerable code this is what they are taught so it's not surprising that this is what happens um we need to shift all the way to the left okay we need to start start with that material and make it secure hopefully we we will be able to do that in high schools and everywhere else but
we also need to help existing developers and you can help us there you can join us in the open source because like or said it takes a lot of work to develop workshops we can't develop workshops for all Technologies for all interests we need help questions yeah go
ahead great question yeah we'll repeat okay so it was a long question but the gist of it is how can we make sure that the workshops we create are secure you want to answer it I'll I okay so first of all we can't okay but we bring our experience we bring uh what we've read what we've learned and we write code using secure principles the problem is no one can be sure that once you write a code using secure principles it will be secure because you can never anticipate what kind of a hack will be found zero day maybe you're using a library that you think is very secure or an algorithm that you think is very secure and some
and 10 years from now you find out it's not secure we have no idea um so we hope that it's we know that it's more secure we know that it's at least with secure principles you can never be sure I will add to that that we talk about welcome list and block list and the the best attitude we believe is welcome list and if we teach the students what we want to achieve what we want to build is much more it's much better than the current attitude which is to tell them how not to develop because most of the product they ask the developers to hack something and then okay don't do that and don't do that we
want to teach them something else we want to tell them what to do not what what we don't want them to do yes and I'll add to that even though so that would mean we don't have time for another question uh we don't teach anti patterns we try not to they usually have the an patterns already we try to teach directly the correct way for example we think it's wrong that you taught in high school to use random because random is not secure and why not use secure random or Secrets if you're using python go for it I mean okay you have efficiency problems efficiency can be measured you can find out that it's not efficient you
cannot measure that it's not secure so it's better to to start with students teaching them only the secure stuff if there's an alternative go for the secure it if if they have an efficiency problem they'll Google it and find that there's an alternative but it's not secure but it's more efficient fine but go and teach only the secure stuff that would be much better like with the SQL don't teach that you can concatenate string go for directly for parameter query and time's up time up so thank you so much