History of Video Game Console Hacking - Matthew Reaney

Show transcript [en]
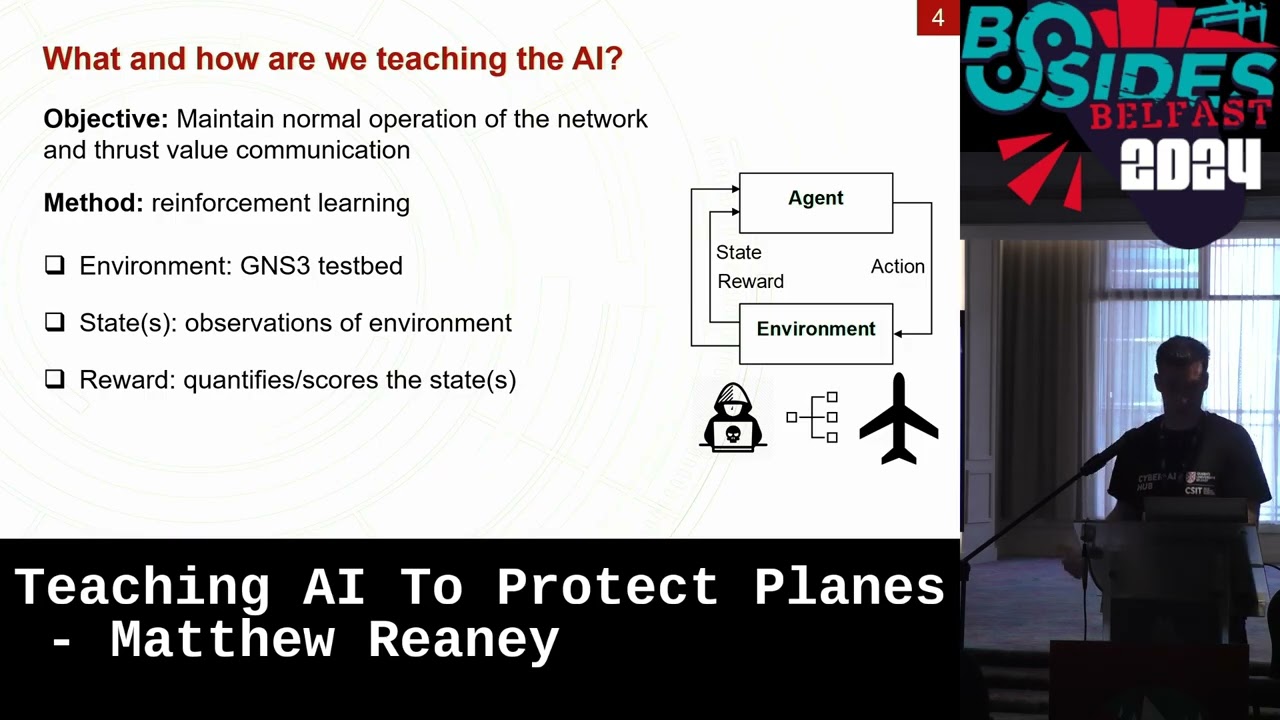
Um, thank you all for coming. Um, yes, today I will be talking about the history of uh, video game console hacking. Um, so a little bit about who I am and why I'm qualified to talk about this. Um, so I am about to be in my third year of my PhD um, as part of the cyberi hub in seat which is uh, the down in the Titanic quarter for Queens University Belfast. Um to summarize my research quickly, it is teaching AI to protect planes. If you think that sounds more interesting than this talk, you can leave now and find it on YouTube from last year. Um and there'll be links to that at the end. Um
uh and as you've noticed, like I'm a student, so that makes me very qualified to talk about video games because I have lots of time to play them still. [clears throat] and to save somebody in the audience from asking at the end, my favorite video game is XCOM 2. So, um, to show what I'll be talking about today, um, or more importantly, what I won't be talking about, um, sadly, Bides doesn't offer like a five hour slot for me to talk about every video game console. Um, and I won't be able to talk about handhelds either. Um, PC gaming is its own thing entirely. Um, and I won't touch on the the ethics or legality of this. Um, if you know,
consult um, if you do this to your own stuff, I would be very hesitant to put it online. The big companies will find you. Um, even if you're not doing anything techrelated, I'd be very careful. They're very protective. Um, there was a local um, pizza place near me called Mario's and it had a um, you know, a mustached um, mascot and it's been renamed. So, um I think you know potentially somebody could have intervened there. Um so if you definitely mock with their like uh their products themselves um that they're going to come after you. Um there's some great stories. I don't necessarily have them in here, but um there's one who hacked the original Xbox and he recorded
um thankfully the voicemail that he got from Xbox coming on to give him a cease and desist um um and take down the information he put online and it's quite just humorous to listen to this poor guy in the office who clearly pulled the short straw and it was like you have to ring him and tell him to take it down. So, um, speaking a little bit about the console generations first, um, to to go over their history, um, we start off, uh, in, um, the sort of '7s with the the Magnavox Odyssey, which was a console I hadn't heard of until I researched for this talk. Um, I and, uh, one of the the
key things um, at this stage is, um, they really had no idea what a controller was supposed to look like. Um, as you'll see, they just straight up put like number pads or strange like rotating dials and things. Um, very weird. I'm glad that we got over that. Um, uh, moving on a bit. Um, you'll see that some of these are uh, pre and post collapse. That's uh, really just talking about the the American centered sort of um, view of it and the rest of the world was pretty unaffected. um especially um Japan which really capitalized uh on this sort of uh period where they they sort of brought in um the the NES and
started to um sort of do really well and they're still around today. Um the same can't be said about Sega who are I think um barely able to survive at the moment. Um so um moving on to generation five and six. Um the most sort of um arguably important era for video game development um because of optical media. Um it made it far easier for developers to um put their code onto a disc and then load it into a um a test copy compared to having to build a new cartridge every time they wanted to test it on hardware. Um, so, um, it was pretty important. Um, generation 7, uh, is sort of what I
would call the the Goldilocks generation um for um console hacking. I think the main sort of reason why is they started to look sort of more like computers at this stage. Um there are computers at every stage, but um they started to have like internal storage and be able to um run apps and things on them like you had the the Wii channels. You could view the weather if you got bored of playing Mario Kart or something. Um so um yeah, and I'll I'll focus a lot on these later on. And then we have the the modern era um which is just a bit boring to be honest. Um and it's sort of cloud focused. Um,
ironically, they're now starting to remove the optical drives, um, which was, you know, something they, um, famously added a while ago. So, um, to get on to the history of the hacking, um, when did it all start? Um, I think this, you can, you know, argue about this, um, quite a bit. Um, one of the cases you can make, um, was like one of the first video games ever was sort of a hack in itself. um a PhD student who had a really cool name. Sadly, we don't all get those. Um he decided to basically modify a giant and very expensive looking calculator. Um and got it to run uh Exio's tic-tac-toe knots and crosses um whatever you want to call
it. Um but this is sort of, you know, this is like modifying a computer to run a game. It's not really hacking the cons like a games console. So you can move further on to products that were made to play games like like the arcade. And this is where sort of understandably people wanted to start to modify them because uh you got charged uh every time you wanted to play it. Um and that's sort of like weirdly come back in the form of mobile gaming. Um so um we then um move on to to thing like cheating devices. Um, so whenever like the household gaming market came around, um, some of the first stuff was like, um,
devices like the Action Replay, um, that added features like saving your game or pausing it that weren't, uh, available in every video game at the time. And a lot of these companies like like especially Action Replay, continued on for years. Um, this was actually a cartridge that I bought in a retail store when I was a child. And I was like, that seems wild that I was able to get a thing that basically just hacked a DS as a child. I was able to buy that. I was like, that's that seems strange to me. I I don't think they're around anymore. Um, but, you know, who knows? Um, so I think really the '9s was when
it all kicked off. Um [snorts] this was sort of the era when piracy um sort of became quite rampant. Um and this is an example of like one of the first um ways to copy or sort of crack video games. And this is for the Atari 2600. Um if you wanted to like basically play a game, you had to copy it onto a whole new microprocessor um and just have a whole load of these kicking around and use like a weird converter to plug it in. Um, so, um, this was also the advent of when bootlegs also became a thing. Um, that's basically companies making sort of unlicensed games. Um, a lot of the time they're they're fairly
like copyright infringing uh, as well. Um, so what did the games industry learn? Well, we should probably protect um, like this our our digital media and devices. And that's sort of where the term DRM came from. So moving on to like when it got popular. Um as I mentioned previously the optical media and the optical drive were massive for development and they were also massive for people trying to copy software because uh home like DVD writers um were very prevalent at this time. Um, so it made it quite easy for someone to take a real disc and then just rip it onto a copy and then you have two of the same thing um for the
price of one. Um, so Sony were like, "Right, we can't let that happen." So what did they do? Well, the reason it's copyable in the first place is they didn't bother to obscure any of the data on the disc. Um, which is a bit stupid, but they thought of an even better way to protect it, the wobble groove. Um, so what they did was put a really weird line at the start of the disc reading process and um, if it didn't find this, it would be like, "This is a fake. Don't run that on the PlayStation." So this wasn't a sort of shape that could easily be replicated by home copying machines for a while. Um, so um, how did hackers
get around this? Well, they only put the check at the beginning of the disc. So, what you could do was put a real one in and then quickly open the lid, take it out, put your fake one in, and it would have just done the check and said, "Yep, the thing that you're about to read is real." And then read the copy. Um, so you didn't really need to do any hacking. You just needed to have um good sort of hand eye coordination. Um, so what did uh the games industry learn? Maybe we should put protection on all of the disc and not just the first like three seconds. Um, so onto the PlayStation 2, sticking
with Sony here, um, they put product code throughout the disc which acted as one part of the encryption. The other part was an unburnable watermark logo. Um, this is an even harder to replicate wobble groove basically. Um, for those familiar with that concept. Um and um this basically ended up with a disk security that for argument's sake can't be you know broken. So what did hackers do to get around this? Well, they went after the thing that reads the disc and that's uh the meccaon or uh the the mechanical controller which doesn't sound as cool. Um and uh well what does the mechacon do? So it checks the the format of the media that you put into
your PlayStation 2 and it says this should be DVD ROM which is read only memory. So um it should be shouldn't have been a copy. Um a copy would require to be a piece of memory that is um writable or DVD R. Um so it said uh yeah only allow DVD ROMs. Um so how did they get around this? Well, someone came up with the the Messiah mod chip that required you to take um 20 wires and solder this chip on top of your uh PlayStation 2. Um and what this why this chip needs uh 20 wires, the way it works is by you can't just skip this check. You have to pass it. So, what it does is
add the DVDR format to the list of like whitelisted media formats. Um, so that that's why it's quite complicated. Um, requiring a lot of wires. So, what did the games industry learn from this? Um, well, we should probably also check the integrity of like the component hardware um that that's like running the the media. So, I'm going to move into um the aforementioned Goldilocks generation um starting this time with Microsoft rather than Sony um with the the Xbox 360. Um once again disk security that couldn't be reasonably broken. Um looking more at the console security. Um the components were encrypted with unique per device keys. Um so each one of these like disc drive and things had
its own uh signed code. Um and if it didn't match um it would say okay your disc drives been modified. We're not going to allow it to run. And the way it did this was um using a hypervisor to sort of protect the the core operating system. So because these keys are communicated um between the different devices, they can be sniffed. You can get your hands on them and that basically allows you to sign your own code and then modify um like the the firmware of the disc drive to say right don't do any of those checks to make sure that my disc isn't a fake. Um the way it did this is you you would
write onto the disc drive flash memory and it was fairly easy to do because the the memory was separate um so you could get it the the um serial peripheral interface um which was required to write um onto it. So what did the games industry learn? Um we should probably disable write privileges on our firmware storage and you know protect it. So, Xbox actually got a a bit lucky here. Um, they they had a chance to try again with the 360 because of the red ring of death. So, when the slim came along, um, they thought, right, you want access to this memory. What we're going to do is actually put it inside the controller to to thwart all of you so
you can't write to it anymore, and we're going to stack them on top of each other and uh, put them inside of the same um, you know, piece of plastic. So um you can see here this diagram points out uh this is the serial peripheral interface and it's basically getting tied to another wire that'll set it high. So it means it's always on like readon mode. So um the only way that we would be able to effectively write in the same way that we previously did was to like cut this wire in some way but it's encased inside of a component. Um so that that's not really possible. Um as you see it's sort of within this
uh chip this MediaTek chip. Um but um some people once they decapped it which became um how how they got photos like this from the inside they basically drew a diagram and said if you line all of these pins up you can sort of know where it is inside the chip.
What if we just drill into the chip from above and cut the wire? Um, so this is the the kamicazi hack and this was so I I loved this so much when I first saw it that it's why I did this talk. Um, so um yes, you would basically drill in using a vague idea of some lines and as you said there's two wires there, one on top of the other. You only need the top one. If you wreck the bottom one, whole Xbox broken. So, it's not just I'm drilling here. It's you need to just drill a bit. Um so, um yeah, quite um quite difficult, but they thought right, okay, if they can get the right privileges,
what we should maybe do instead is protect those keys so that they can't just write their own firmware. So, we move on to the to the Wii. Um, did they did they, you know, did they take all the previous information um into mind about disc drive security? Uh, no. Um, they they actually used the same disc drive as the GameCube, which had been out for ages, so it was very exploitable already. Um, so running your own games on on the Wii was actually quite easy. um like copied games. But you know for the sake of keeping this talk interesting um I thought what if we raise the bar from running our own games to running our own software on the Wii U
um for it to you know make use of its amazing computing power. Um this is typically known as homebrew uh within the sort of gaming community. Um I think maybe just software community in general. Um so if we want to write our own homebrew what do we need to get past in the ways of security? So we need a way to get the keys and we need a way to write similar to the Xbox. Um so this was a pretty difficult task um that we you know was pretty sensibly built to a degree and said right the memory instead of having keys for all the components we're going to keep the keys in the main
memory and we're going to say nothing has access to this memory whatsoever. So the minute it leaves uh it's written in the factory and that chip is sealed up, sent away, no one can ever get to it ever again. Um which you know it's it's quite a good idea. So as I said about the disc drive they included earlier, the reason they did this is because they included a GameCube mode where you could basically run GameCube games on your Wii backwards compatibility. Um, so what this actually did was essentially boot into a version of the GameCube operating system. Um, and as I previously said, the GameCube would have been out for a while. It was
very known, you know, exploitable. Did they bother to maybe update any of that stuff? No. So, um, any, you know, vulnerable custom code that you had for the original GameCube, you could exploit it here. Um, sensibly the Wii restricts the memory so that even if you do those exploits, you can't escape the the part of the memory allocated to the GameCube. Um, so you you'll see on this this diagram here is the the Wii memory, and you can see there's a key there. Um, and when you activate GameCube mode, this happens. And, uh, the Gamecube is confined to that part of the memory, and the keys aren't there. Um, you know, Nintendo thought this over. Um, so
what if we moved the GameCube memory? Um, that this, you know, is is, you know, in theory, software-wise, impossible. Um, and if we did move it, we could get those keys that we need to write our own software. So, Team Tweezers, spelled with Wii in the name, realized you could just slide the memory address that the the Gamecube mode could use using a pair of tweezers um up and were able to grab the keys. That's not the end of the story, though. We we have a bit of signed firmware that will run, but we now need a way to write it because the Wii memory is still protected. Um so, we can't write it while we're in GameCube mode because
that'll only write to the GameCube memory. And when we go back to the Wii mode, that'll get written over. So, we need a way to write uh in Wii mode. So, Team Tweezers came back, double bill, real menace for Nintendo. Um, they came back with the Twilight hack um to, you know, capitalize on their previous exploit. Um, how does this work? Um, so really, really long horse name. So, uh, within the game, you name your horse, which is normally, I think, a pona. Um, and you give it a ridiculously long name, uh, and what this does is causes a a buffer overflow. Um, and basically you can point to, um, the SD card memory addresses, and it'll run that code
instead. Uh, and, you know, you put your homebrew that you've signed with your keys on there. Uh, and then it runs. So, what did the the games industry learn here? um we should probably assess security of legacy modes if we intend to include them. So, going back to Sony, um we started there and we'll we'll end there. Um this one's um the most sort of complicated I'll go through, but when the PlayStation 3 came out, it was the most like a computer that a game console had ever seen. You could actually when it first released run other operating systems on the on the PlayStation. um supported uh sort of natively by Sony and they they advertised it as like you
could utilize the computing power of the the cell processor which I was told was really heavily marketed at the time um as like a new amazing thing but I don't think it caught on. Um it it didn't cut off Sean too much, but um unfortunately for Sony um because they sold their consoles at a loss, people did realize, oh, we can get a really good deal and sort of just put a whole load of these together and make a really powerful computer on the cheap. And that's exactly what the US Air Force did when they combined nearly 2,000 PlayStation 3s into a giant supercomput. And there was all these other wild cases of uh people proposing like preposterous
numbers of PlayStation 3s hooked up. Um I can I can only imagine if they did this nowadays like people are already annoyed at scalpers. Imagine being like didn't get a PlayStation didn't get a PlayStation 6. I'm raging and the US uh US Air Force comes along and like we've got 3,000 PlayStation 6s and you're getting none of them and we're going to build a new computer out of it. You you know you'd be very annoyed. Um, so one guy online basically theoretically came up with a way to break into the PlayStation mode from the Linux or other operating system mode. And his proposal online that he never even did was so terrifying that Sony just removed the whole feature. And this
cost them like millions in lawsuits cuz this was advertised as a thing that you'd be able to do and they basically had to remove it from all the PlayStations. Um this was to be fair a pretty good idea from Sony. I don't know if it was monetarily but from a hacking standpoint um it was it was quite a good idea. It took four years to break the the PlayStation 3 security. That's a really long time for console security. Um, most of the other ones it's either like weeks or months until they get broken. Um, so the USB was its eventual downfall though. Um, a team came along that named themselves PSBR and created this magical
USB stick um that you plugged in and then you also plugged in an external hard drive and boom, you could play all your games that you put onto the hard drive that you obtained somehow and got them on there. Um, but they charged 100 quid for this and this was like back in 2010. So that's like probably like 250 quid nowadays. Um, so yeah. Um, the hackers really didn't like this. There's kind of a an honor um like system of if you break it, you need to tell everybody how you broke it and sort of make that publicly available. So this actually caused infighting um and the hackers basically h bought this product, reverse engineered it and figured out
how to hack it themselves without having to to everybody to pay this other company. Um so how did the the PS jailbreak work? Um well it it used a number of things. Um it posed as a sixport USB hub and did funny things with this. Um, it utilized heap overflow exploits. Um, and also basically the the big one was faking credentials as the debug jig. Eventually people figured out if you named your uh USB device the correct name that was like PlayStation debug one two three or something. Uh, they just tried a whole lo of these. It would then put it into debug mode as long as your USB device was just named the correct thing. Um, so
what did the games industry learn? Um, maybe make your debugging mode harder to access. Um, but I'll actually explore I' I've done the we takeaway already, but I'm going to explain this in more detail, but it's quite complicated. So, I'm going to need I know it's near the end of the talk. You're getting tired, but I need you to perk up a wee bit and, you know, lock in for the this. Uh, so on the top we have um this is the same six port USB hub top and bottom. The top is what the PlayStation can see and the bottom is sort of what the PS jailbreak or or the exploiter um knows is going on
behind the scenes. So step one, we're going to insert the payload into the first port. And this payload basically points and the uh memory address for the disc drive instead to your external hard drive. So it'll run games from the hard drive as if it was a disc. Um it's quite clever. Um, so that goes in there. Um, but the the PlayStation won't like natively run that when you just plug it in. So we insert another drive into two. Doesn't really matter what this is. You'll see why later. Into three. We then um basically place a really big USB drive. Um, and the PlayStation thinks that it's just filling three, but it's so large that it
actually heat overflows and fills three and four. We're then going to unplug that device number two. Now, this is important because um, basically when the memory is full, if you're trying to write to it, it'll default to placing it in the nearest or first available location instead. Um, and that for us would be two now that um it's freed up. So, we insert the the shell code into four. And this shell code will um activate the payload. But because four is actually full, this gets shifted down to position two. Um, and the PlayStation doesn't think it's there. So, we then insert another heap exploit. And we also named this one the the debug jig um and put it into five. It's
actually five and six, but they're now full. So the the debug mode points to port two, which actually has the shell code in it. So this runs the shell code, which then detonates the payload, and um you can now play uh all your games off that hard drive. So um to close um the modern era uh it's become much more software focused uh as you can see even as we as we go on um it becomes more of a software challenge um than uh a hardware one. And the sort of big problem with this is a lot of these modern consoles you have to be on the latest update to have connectivity to play online games. So, it's a thing of
like you might hack the console, but it won't stay hacked for long because eventually it'll get patched. Um or you'll get banned or or something like that. Um so, um it it's I don't know if it's as popular. I can't really say. Do we still hack the old systems though to sort of gain more power and things um over them? I I don't know for sure if I'm sure people still do. Um, I've got some some people attached at the end who go back and and modify things, but I think now um a lot of people choose to use emulation instead. Um, and it's it's a whole other um like legal can of worms and that I won't get into. Um,
so to give some takeaways, uh, from the PlayStation one era, we learned protect your media. um don't rely on silly gimmicks um like the the wobble groove. Um PlayStation 2, let's um start checking the integrity of our firmware or you know our different controllers um on our device. The Xbox 360 um protect your keys for your encryption and preferably make them drillproof. Um the Wii, yeah, assess legacy of uh or assess security of legacy modes. uh if you're going to include something that's backwards compatible, make sure that it's now safe to do so um if it was vulnerable um at the time. Uh the PlayStation 3 make your debugging mode harder to access. Um and there's
probably some other, you know, port related things that you could learn about that that case. Arguably, the last two are the most important. And the first of which is um all of this advice is probably horribly out of date. Um, it's weird to say that the PlayStation 3 is about 15 years old or closing in on that. Um, which is terrifying. Uh, because I feel like it came out yesterday. Um, and lastly, gamers, I suppose hackers as well, they will find a way. So, that that's one thing um that they'll always get around um your security. Um, thank you very much. And I'll I'll take some questions. There's my socials and some sources as well to to check out
if you want to find out more.
Questions? One here. We've got two here.
Yeah. So, yeah. So, it's sort of saying like the Xbox um it hasn't it's not as said the security isn't on it, you I know it's not a great story behind it, but or well, sorry, it's not amazing. The story behind it definitely is good. If there's one of them I can recommend um going and watching a video about, it's the the Xbox One. It's the one that the voicemail is included. Um because yeah, he found he basically was a researcher and put all the the stuff online. I think he's got a book and everything that's free if you want to read how he did it. Um but yeah, it it's it's an interesting story at least. But
yeah, the security wasn't amazing on it either.
Yep.
Yeah. Yeah. So, a lot of people got fed up having to have quick hands. So, there was mod chips that would do that for you. And I said it some of it was maybe obscuring sensors or things um that were um preventing that. I know on the Gamecube they put a whole load of sensor. I think there was three they put in. So, whenever the lid of the GameCube came up, it was like, "Ah, you're trying to lift the disc out, aren't you?" Halfway through. We've got you. So yeah, they had to sometimes those uh different versions of the PlayStation song maybe included sensors to try and stop people doing swap tricks and things. Okay, I'm
going to this question. Did you have a question as well? Yeah, I I'll grab this one first and then I'll come back.
There you go. Yep. Yeah. So, yeah, there you go. The mod chip just input the the wobble signal regardless of the the disc and question here.
>> Yep.
>> Yeah. Yeah, I've seen that. Yeah. Um, yeah, as I said, Nintendo is not the one to muck with. There there's the questions about like, have you seen the the latest stuff with Switch 2? I said I don't follow this too closely and I've not tried any of it myself, but yeah, I've seen I've seen weird things happening to it where it like thinks someone's exploiting it and it's just bricked the console and and weird things happening. I think there was a lot that ended up being even like bricked on arrival because of maybe something happened with like the battery activating stuff. Yeah. Yeah. Yeah. >> Yeah. But I mean, you know, it's a pretty good security strategy if you
don't want somebody hacking your product. You just make sure it's bricked on arrival and then, you know. Any other questions? Oh, we've got two more. Two more. I'll take the the one in the front.
I I do think you're on something. I did hear something about the different color. I think potentially the reasons that some of them got like platinum editions might have been to give them better disc security. So there was um Spyro is a really good case of um it's very interesting to look into. It was um a trilogy of games on the PlayStation 1 and basically every game the Spyro crew got better and better at putting DRM in their own product. So, it didn't want to rely on the wobble groove and stuff. And there's really good cases of I think in Spyro 3, they basically implemented like uh if they detected you tampered with the the disc or anything or the console,
it would basically like just take your coins off of you constantly. So, you could play like the first hour of the game and then it would be like money bags or something. I don't know who he is. Guy with big money bags would just come and rob you. So, it was like you needed a 100 gems and he'd be like, "Thanks." and just take your gems off you and you could never get onto like the second level. Um, and yeah, it would like wherever the check came in, it would just like ruin someone's like they'd already invested enough time that you would get annoyed that it's then caught you later on. Um, there's some there's some weird uh I think PC games
as well at the time tried to add stuff like that where they would try and catch people. But yeah, I I I think it's maybe just those different colors or like different releases, but potentially. Um, and the question behind
So the question saying do I think the games industry is really good at security? Um and is there is there
I think I would actually say I think they're doing quite well. Um, this is like come it's a pretty unqualified opinion, but I think the the money that they put into it is it's surprisingly one of like they invest a lot in the security. it wouldn't be something I would necessarily think of is like who's putting a lot of money into cyber security but yeah games industry is is you know as we've seen they have definitely tried to to do a lot there and but I I don't think they would be the best but they seem very like as you say the customers or the the people wanting to do it are determined but I
think like there's a lot of money in the games industry so the those companies are very you know financially motivated as well to stop it so yeah it's Um just the we'll take the last one at the back there.
I so the questions about do I think there's more scrutiny if a game can cause exploits or or host exploits. I don't have much evidence other than I know that I think it's like one of the brain training games on one of the Nintendo products is like the easiest way to hack it and it is the best selling game on the eShop. So I I if that says anything like you know I I don't think they I think it's one of those things of like if it's old enough they maybe make a judgment call and go right are we really going to profit still like we aren't producing the cartridges anymore the sales on the
eShop have completely like maybe dried out or whatever like is it worth us chasing these things up or are they actually going to make more money by you know whatever you know maybe 10% cut they're taking of every person who buys the game to then exploit it that might actually make them more money. I have no idea. But yeah, um it's definitely an interesting one. But I feel like they would have a lot of scrutiny if there was anything causing like security breaches on like more modern stuff. But um for for sure if there was like they would definitely have that game pulled I feel like um from from the stores. Thanks