Terry D . Smith II - Threat Hunting and Hacking Questions which Get Increasingly Harder
Show transcript [en]
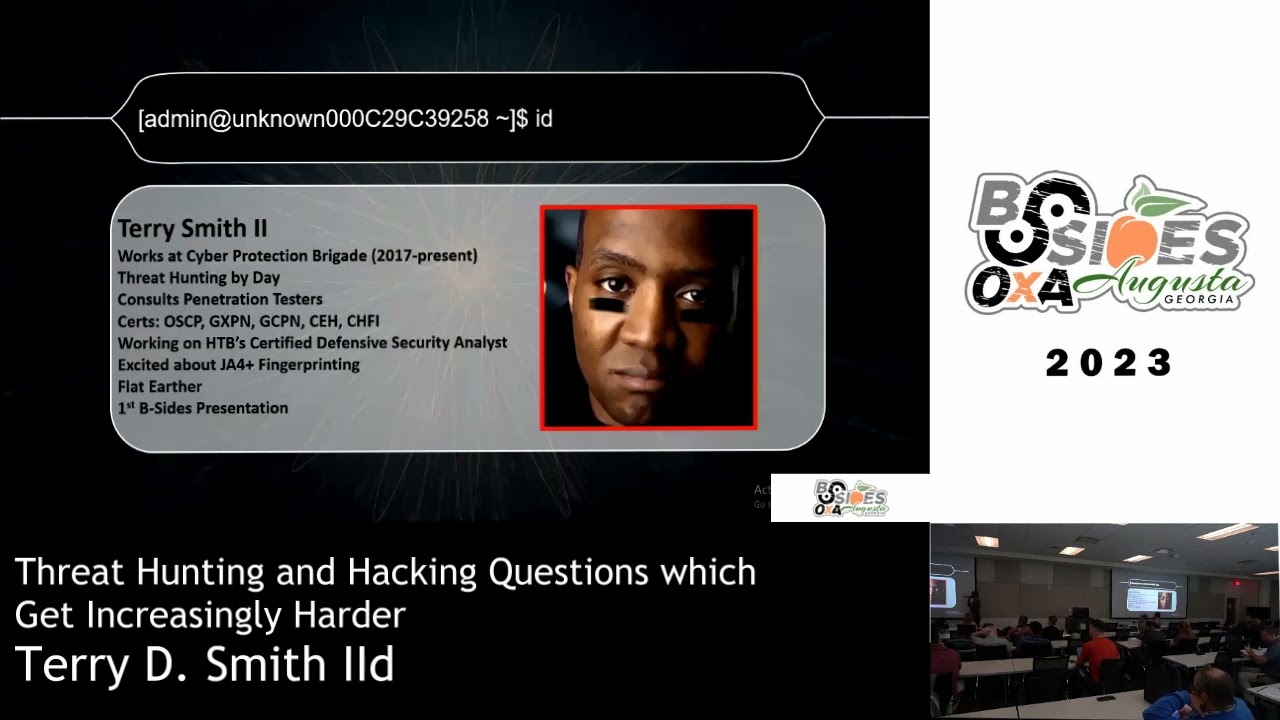
I'm going to start right off by asking for the windows experts in the have any no experts okay how about intermediate okay stand up sir yes sir would you like to take a jab at this question for me please sir and feel free to use a Lifeline if you want I always say more when I see something okay thank you sir so he's going with the anyone else um to me it looks a little weird to see the IPv6 and the ip4 together so I don't know if that's a normal query or not okay I'm kind of leing towards impossible I think the Gent over the corner have it say again sir on making DNS that's exactly correct so you have wind log on doing some pretty funky stuff there and the only reason why I know this is malicious is it it comes from a forensic report on the D through report on the website this is a really good report and after my talk you should probably check it out one of the silly things about that report that that I found pretty hilarious is the attackers before they ran their ransomware they alerted the entire domain and told them that um the entire domain was infected with copal strike which will'll go over what I believe the reason was in a few minutes where my pin testers my red teamers do I have any not all right would anybody like to take a step at this question feel free to use Chad GPT Google or anything cuz my two gentlemen I'm giving them away two prizes and they got participation points my Gentleman here actually got the 25 points for the first question oh s hey I got got an A over here I get a I'm just guessing D because it seems something to happen Okay D so D is actually was that you well he somebody over there said it first okay so um I'll tell you how the points work in a minute slipper is one of my favorite is probably the favorite uh my favorite C2 you have two others that people normally mention cobal strike in uh brute retail and I found it really hilarious that it warns you in such a way and this is the actual screenshot from that it U as actually asks you are you an adult and of course you put yes the funny thing is if you put no here exit the shell and come back it'll say no you're not and adult so it's just a hilarious thing about sliver it's a it's open source if you want to test it out in your home Labs legally so before I introduce myself I want to ask the audience can bad attack or offset ever be a good thing for the adversary probably not right yes I hear yes yes can you stand open explain why sir you were there so I plan to write a full article or podcast or audio book or something on this but these are the reasons why I think attackers can sometimes want to be loud one of my favorite ones is sometimes that bad obset can just drive your anal to Crazy decisions availability bias one of my favorite ones because as you begin to see something more and more you focus on that more or let me take that back as you are more familiar with certain artifacts those become priority when there may be a more Insidious one so I encourage any analysts any pentesters to please look up biases fallacies CU we all fall victim even the experts okay so they told me the speakers didn't work so I don't know there's a who wants to be a million million re I'm going to let it I'm going let it play last question before I introduce myself though anyone want to take a step at this one for 25 points this was should be easily googleable Twitter is all good s so yeah so if you did I lose okay okay so with questions like this um the first thing I want to say is Twitter or X is a good source for any current cyber threat Intel secondly I want to say all of these are somewhat relevant minus maybe stuck that but the the key thing to to take away from this is ICD trickbot and Zeus All Families of malware they all began before 2010 but they're still relevant so if you ask Chad gbt it's going to tell you none of these are relevant just keeping that in mind it hallucinates some time and so this is just a screenshot of uh what I like to do I like to go on Twitter and pretty much just steal people's work me um I'll blink the uh the name out in the face obviously and so this is me so I uh before I introduce myself I want to introduce my son Terry Smith III I want to introduce my wife in the back and my best friend and then uh my uh pride and joy little tanley Smith they're all here so about me Cyber protection Brigade you can read I don't want to really read to you too much um I use a uh Mr Robot approach when it comes to learning and stuff so I 3 hun in a day and at night I either work with pin testers or I do hack the box and things like that I also have a side of not a side hustle it's probably not appropriate to say of a home business where I consult pin testers and it's uh it's pretty awesome to to to see some of the pitfalls and the things that they deal with it's it's pretty pretty awesome if you want to ask me more about that offline we could we could talk about that after the um presentation here I'm working on hack the Box's new cdsa I don't know if anyone's heard of it no okay well they're putting out a blue team c u certification which is going to be my first actually and then I'm excited about J four plus fingerprinting which will go over that more uh flat earther if uh you want to ask me more about that you can ask me out after the uh presentation here this is my first presentation and I wanted to do something different I've been coming here for six years or so and I wanted to do something that uh Engage The Audience so hope you everyone is having fun one of the most inspiring things to me if you don't know what this is this is the thread hunting maturity model and I just love model model I love when people in the field take their time to create a a model so that organizations can gauge where they are gauge where their analysts are and it inspired me so much that I put it on an individual level where I could tell my analyst hey you can only respond to alerts you're level zero or you're so good you could probably build a carbon black or a a a end game you're you're that good and that's basically my blue team maturity and the questions that I'm asking the audience today are a part of the the threat hunting maturity exam that I give my Analyst at work so and then this is red team maturity I guess we don't have any red teamers in here today which guess I didn't get any feedback on that but it this is U I'm pretty proud of this I am and um I think it's it's a good way to just gauge where people are and I think everyone just really wants to know where they are in in the field I know when I first started I I didn't know who to talk to or who to gauge my skills off of and that threat hunting maturity model just hit U hit the nail on the head for me so a few notes of how I want the rest of this to run I was going to split the audience into blue and red team but it doesn't seem like that's going to work today so we're going to work off the honor code if you answer answer the question correctly just please note somewhere in your phone how many points you got for that question and then we'll tally up the points on your own and then the top two winners will get my prizes here does that sound good yeah sweet all right um if you are a Learner in here this is your first time if you're just getting into the field I highly encourage chat TPT just open up a chat and just start typing things in there and as you you mature in the field just go back to that chat and start asking it more questions I mean um it's it'll it'll really help um and just have fun it's the end of the day I know these uh presentations are really really difficult to uh it's it's difficult to stay here all day just honestly so I'm I'm glad you're with me and loosen up and have fun I know it's a pretty it's not formal but it's a pretty stuffy event on time so just want have some fun here the next one for my blue teamers for my sism fish andad during an incident response your team wants to use sisan to monitor host notice that the points here have uh went up a little bit might want to take a stab at this for lovely prize of here to compete for that we have a be yeah I think it's you think it's yeah only when we have time well if it's an incident response the organization should suspect some domain adment stuff going on some some root privilege stuff going on and in that case with with with exceptions you have a config file that's pretty exposed there are ways to secure that config file but not many people know it so most of the time it's going to DB some of these are debatable so if we have a little bit of time to debate these if you would like but this is going to be B for this [Music] one not do that all right you attempted to as roast as rep roast my service account and I CAU you how did I catch you this is really good if you are uh if you work with active direct a lot I just learned this like last week this one is going to be a little bit harder I heard a b heard that b well have you chose B you're not correct sorry so with a is it's this is pretty interesting because in 2008 Microsoft released I believe this is around the time where Server 2008 came out and before then your ticket granting ticket was encrypted with rc4 if you don't know rc4 is outdated and we jumped to as as 256 what some attackers don't know is their script Kitty tool use still use rc4 so we catch them a lot there are other ways but that's the one that I'm going to uh give about today so next question he ran an map scan external to the Target Network and got no results I ran an inmap scan and got results with one key change see SE over here hear B I have B's here B is correct so this one is another one that I learned pretty recently um that a lot of uh pentesters and a lot of red teamers just don't know um I I am aware that if you have a do a DNS server you can drop any packet that you're not expecting so there's an IP address that doesn't look right you could drop that but generally speaking if you're scanning from the outside if you TX Source Port 53 onto your MF scan that's going to be a best practice so I don't know why this one is 500 I didn't this should be more but your analy sees the following ioc insists mod event ID what and immediately reports it there's a pattern here for ioc's I give you 30 more seconds to Google I hear C's anyone want care to explain why that would this would be saon C2 server it looks like it's doing Discovery to me like trying to go from Network The Local Host yeah I'm hearing things but that one is a redirect so it's putting the output to that local file so so let's for for our group that that have that have a little bit of experience can let's go back to our Network admins for a minute and think of how they would normally run a pain would it be like this no that's all you need to know this is malicious and minimum is going to become an event and um it's just the nature of the Beast is as far as just understanding that and an ad doesn't have time to nwork am doesn't have time to come up with these crazy things just to do simple things like peeing and just for everyone's just to take something away from this if you ever see a slash C you should investigate it anyone know why calling another uh like another shell script yes so with a slash C you could your 80 to 90% 80 to 90% of the time that's going to be run from a script or something that's pre um like an executable or something like that and they can find you a lot of good wins for the blue team so as a break from our questions I want to share something else that I'm really excited about most of us know about the miter attack and it's access all the way to impact I recently discovered the UniFi heel chain which describes how hackers how adversaries interact with the the the network in a much more accurate fashion once you get an initial foothold maybe you have a PHP webshell you have to do all these things before you make it into the network and then I would argue you'd have to do all of that again to come here I don't want to dig into this too long I just want to show you something that could really help you understand an attacker's mind frame from the I guess from the mind of an attacker and just understand that nothing is linear like the minor attack majri for for the leaders in the room a lot of times you want your reports in a linear fashion like minor attack just keep it in just keep in mind that things are more like the unified kill chain next question do do I have any forensics experts in the room forensics mare analysis I mean analyst sorry analyst in room anyone want to take a stab of this one just randomly hearing two answers from gentlemen nowhere in the corner got to commit let's get I show have hands for C what about did I hear B this one will really throw you off it's going to be D so if you that deer report that I referenced earlier a part of that TT the TT people that attack her is they took Beacon dll and they moved it to another box and then they activated the dll it's crazy but you you just got to I guess got to keep up with the current current things and it's tough I know it's tough It's really tough but I think what a lot of you just failed for with this question is availability bias you saw a beacon D and it went right straight to beaconing activity it happens it does and I assure you that the adversary they know about our our biases the next one I wanted to put brute retel in here just to give you some exposure to all three of I I call them the big three c2s um we're going to we're going to make this one quick what we got b b no Del Delta for everyone Del [Music] nice so I mean it's just a matter of just I guess watching YouTube videos and at minimum just understanding I would say understand an artifact from each major C2 and I think you you have a you'd have a decent foothold on what attackers are doing I I kept the same graphic there so this one is a elk related elk stack related question we've gotten away from hacking a little bit where are my master Gunners in the room have any Master Gunners anybody know that is D hear are you all be you're correct you guys are awesome you are so went too fast too far so this is basically elk stack I don't want to go over too much it's something that you can Google definitely but um it's pretty awesome and we we lay on this pretty heavily um during our analysis at work and not only us but pretty much this is this is the way to go when you have big data and if you are interested in hacking it this is the Box on hack the Box where you can learn about the elk stack a quick story about this I was in Miami and um anyone know A-Rod or Alberto Rodriguez bche so he told me hey man you really you want to do this you want to do this box and just do it and I spent maybe two days or two weeks something like that um but it it taught me a lot about it it taught me faster about the elk stack than just reading about it it taught me exactly how log stash looks and the filters and the things and the configurations and such and I would recommend if you are new to hacking do with the walk through nobody's judging El redk I'm sorry red if you haven't heard of of this is the red team in the adversaries mentation of rip out stack and I want to turn your attention to this big red circle so with many of us the way that we operate when we find a suspicious hash or suspicious IP address or suspicious domain what do we do to confirm whether or not it's malicious anyone got anything virus total my man virus total exactly what we do is that the right answer no no and this is why as you if you if you notice this little arrow here this constantly queries to see if the red team's ioc is in virus total so if the red team little old red team little old Joe that works uh in room three can download this and run guess who else can do this Adar adversaries thread actors APS so it's always best practices to download your entire virus total database I know that sounds ridiculous but if we really want to get after our adversaries we have to do ridiculous things sometimes help is another implementation of elk stack it's pretty awesome if you notice some of the stuff up there it's going to do all the things for you I think that's pretty much it for the things that use El anyone recognize this yeah I call this the OG of the elk stack so security onion is awesome if you haven't messed with it please do please do it is awesome and I owe a l to security onion and the the the good folks here um and I I think my organization does as well all right back to the questions so this one is uh a little bit harder so stay true to the the title there they get increasingly harder anyone want to take a step at this one and don't fall victim to availability bias because it is up there D I hear a d anyone else Charlie make sure you're keeping track of your points please I have not B and B and D seem like same thing right you masquerade in order to Pivot yes there's one more correct answer there's one more correct there's a there's a uh there's a answer that's more correct another one yeah they're time for questions so think of it like this if I am an attacker and I place commands or any artifact or anything on the box there's a point to it right there's an objective to do a thing that's I heard a few D's and you're correct if you chose D so yes you can masate your traffic because essentially what this command does is it turns your Linux box into a router and this became pretty important especially with the Advent of cloud because you had adversaries just pivoting through Cloud providers n works so this one is pretty Insidious and it's pretty shocking how many people don't know about this one because it's it um if it's active if all of these commands are active and running it's it's pretty effective for the attacker all right now I will tell you I will give you a warning my uh my team at work they absolutely hated this question but I assure you if there's a method to the manness here I'll explain it all what we got all the above the Deltas got anything else got a Del Bravo I got brav I got did I hear a or not a you are correct sir so this one is a little bit frustrating but I will explain why it is not b and why it is not D so with B you have a bunch of vulnerable end points but if I have an objective as an attacker what do I care when they don't involve my actual endpoint my the one that I'm targeting and as far as C goes AC directory is pretty much a mess it it it does its own thing when it comes to where it wants you to access and what it wants you to access to where bring protocols become almost I going to say irrelevant but and they step down a bit because again as long as you have that access and that right User it's going to find a way to get you access to whatever you need so I wanted to go over a few remediations I was hoping we have more red teamers in here and I wanted to just put this one on the slide by itself because it's so important when attackers laterally move they should be given a reason or or a path to move from workstation to workstation it's not necessary for business operations it's not necessary for communication and it's just not necessary so just block it at the DP level uhoh go far I want for all of my windows experts and all of my active directory experts in here can you tell me a reason other than convenience why you must have a domain administrator account but you can have laps instead if you want to Google that you can do as well it's bonus points on the board but you have to tell me in a sentence a letter hear answer you can't see it by default otherwise right you have to goif permiss after okay so the brake glass we good go ahead sir brake glass breake glass for lapse yeah okay maybe I need to re re uh so let's just say I go to going into an environment and they have domain admins everywhere and they're not using labs and I say hey stop using do admins and use laps am I correct on that what





