Where in the world are Carmen's cyber attacks: The game show that wonders why things aren't worse
Show original YouTube description
Show transcript [en]
all right well thank you everyone for joining us for this afternoon's besides 10th anniversary programming brought to you live from our common ground studio here in Tuscany Las Vegas we'd like to remind you that these talks are streaming so please turn off your cell phones and if you'd like to ask a question raise your hand and I will bring you a microphone besides tenth anniversary is brought to you today by our inner circle sponsors critical stack and Balam they're our stellar sponsors Microsoft silence and our friends at the National Security Agency as well as viewers like you we kick off this afternoon's programming with where in the world are Carmen's dollar adjective cyberattacks so please welcome our host Alan Friedman
thank you thank you by the way there's applause thank you we are so excited we have a great show for you this afternoon there's been a lot of discussion about how we make things better this afternoon we're going to wonder why on earth things aren't actually worse cyberattacks come from all points all sorts of approaches but most of what we're worried about are similar to why we rob banks where the money is at so today we're going to look at the attacks that aren't financially motivated and say why aren't more of them why aren't there more we have a great panel for you now a lesser panel would have just been ordinary Talking Heads having a standard policy
panel but our panel today is going to give you a fence fantastic and fun game show where there are great prizes and the points don't mean anything and we all wonder when we're going to die in a giant cyber fire so I'm going to introduce our panel and I have a request which is when one of our panelists shows up at a dead run I would like everyone to stand up and give him a standing ovation as he comes I think that is the appropriate call-out for someone who is coming late but the folks who actually made it here on time we have a truly stellar panel for you today our panel kicks off with Liz Wharton was the VP of
opsin strategy she is over a decade of experience as a lawyer working with hackers and she is someone who you should not trifle with either in a dark alley or in a competition based on where your next meal is coming from so Liz you've been doing a lot of work in security in this how are you informed how's your work inform you to wonder when we're all going to blot dye in a cyber refire well considering half the time I'm trying to keep the people from causing the fire and then the other half the time I'm hoping that the folks that I work with are the ones that haven't burned my stuff down just for the lulz
I'd say over a decade keeping these folks out of trouble and working with policy makers that's unqualified fantastic thank you and our second panelist today is Chris kubecka who's the CEO and founder of hypo sec she's a cyber conflict expert and consultant which she thinks of has a slightly more lucrative career than her past gig as a carny that's true actually asked her to do some stunts for you later just not all of them are currently legal in Nevada so be careful Chris you've thought a lot about cyber conflict why are you here today I like to discuss how to use technology to kill people it's one of my favorite topics and that's why I'm here
excellent so true to form with our game shows our buzzers have not arrived in time so we're going to be asking each panelist to make their own buzzing noise so for at least the beginning of the game Chris is gonna sound like and liz is going to sound like oh no no hey hey we talked about this no threats of bodily harm [Applause]
you're wrong our last panelist in a man who only showed up late because he really wanted to make a flashy entrance is Bryson bort Bryson is the CEO and founder of grim and scythe and has a mysterious dark past that he occasionally alludes to and is also makes one hell of a cocktail so Bryson how has your work both in the secret squirrel world and in the private sector informed your understanding of attacks that aren't private that aren't a profit motivated well just like everybody else I don't know anything but I pretend I do technically that's my job I thought we had this conversation alright so we're going to start off today with a key question the abstract
we use the analogy of the Drake Equation and your first question contestants what is the Drake Equation Liz I'm not sure but the solution is the numbers to my cell phone I I don't think that my cell phone is the right answer do we have another answer what is the Drake Equation price a calculation needed for the optimal ships to raid the Spanish Main and defeat the Spanish Armada but I I was not expecting a 16th century military strategic reference but that's what you get from West Point ok I'm sorry that's still not correct does anyone have the correct answer and condition depending on certain types of technology fantastic and I'm gonna ask the panel to
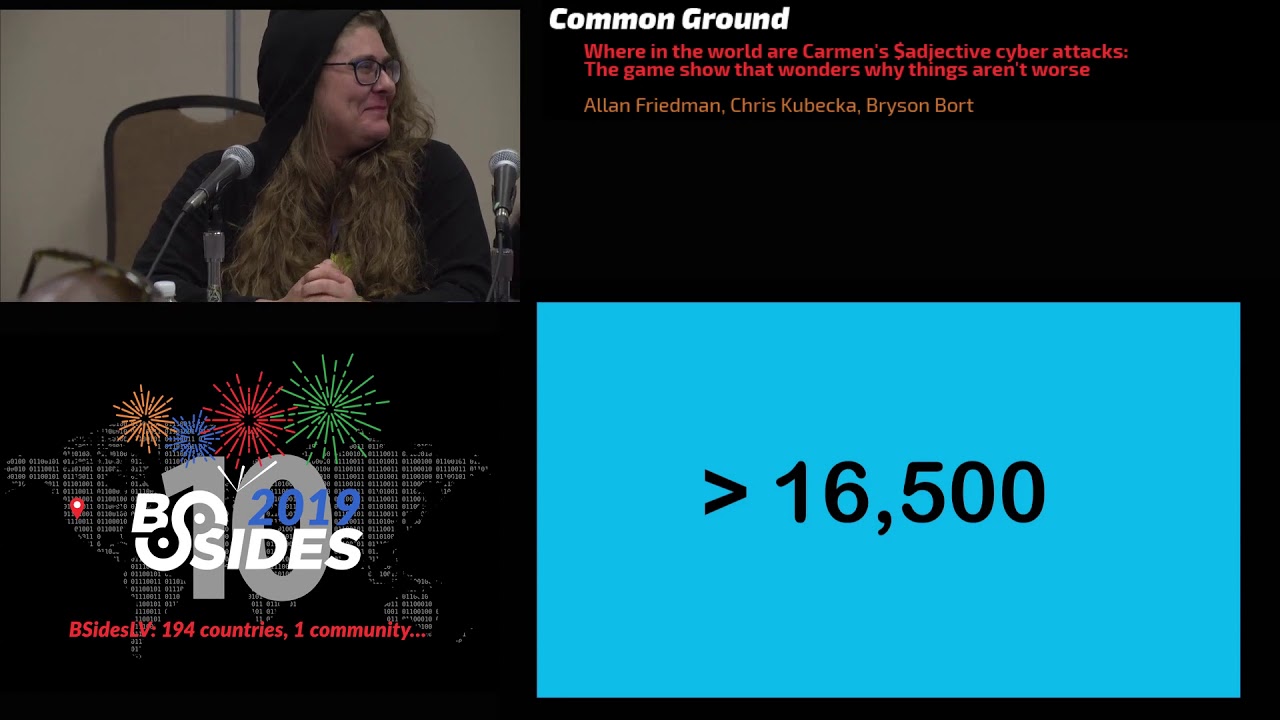
move the mics just a little closer themselves so you start off with a bunch of very small probabilities but if you multiply them all times a very large number say the number of people stars in the sky for intelligent life or the number of people on the planet it still means that there should be a nonzero risk of either intelligent life or not so intelligent cyber lifing so your next question we're gonna play a game I like to call if this is the answer what is the question so panel if the answer is more than one than 16,500 what is the question it is that is there is a real risk Liz yes that's the number of arrows
I would need to take down a wide area network that I would feel like we should actually measure that I think you might even be able make it and fewer than that but that's impressive that's not do we have another answer what is it price the number of new entries in the national vulnerability database so there are lots and lots of vulnerabilities out there so let's let's talk about a couple of them panel what do you think was the most important security news from last week that's John McAfee yeah it's true he's no longer Jill I think that's no I think that's important security news but I was looking for something a little Liz um yes
the better question is who's in your wallet because apparently hundreds of millions of credit card numbers have lots of people now in their wallet Capital One but I think that certainly dominated the headlines but I'm gonna disagree I think there was one more story that from a cybersecurity perspective was even more important as anyone know what it is it's Bryson the 11 vulnerabilities announced in wind rivers VxWorks real-time operating system that it's true that is I strongly believe that if you're not familiar with this VX vxworks is a real-time operating system made by the company Wind River there's a disclosure of eleven serious vulnerabilities many of which will be there forever not everyone knows exactly
what their real-time operating system is this is technology that is used in satellite uplinks in digital controllers and factories in medical devices all over the world and not all of it is easily patchable so this is a real concern it's a shame that the headlines were dominated by the Capital One or the John McAfee so here's a chance that redeem yourselves because still the points are well they're made up so I'm not gonna read the score yet for the muggles in the audience do you each have a favorite vulnerability that you really like to talk about to frighten people Liz printers because just as soon as you get the sucker working you find out someone's using it to steal all your
data and information that's a scary one Chris billion devices and that really it is and it's always asking for an update to which probably means there's some bad stuff in cars yeah all right Bretton what is your favorite vulnerability to scare people with if you have a computer we can't find you alright I'm now terrified that's alright so as we've talked about the majority of attacks that we see today whether they're targeted against companies whether they're ransomware where they're going after you know little old ladies computers they're financially motivated it's the classic line why do you go after banks it's where the money is up but there's a lot more risk outside of just the cybercrime world so we're gonna
play lightning round I'd like the panel to go down the list and please whoever can give us the most risks that we should be focus on that aren't built around direct profit so let's start Liz oops my bad so accidental risk accidental risk is key squirrels squirrels Bryson insider threats ooh so we just had one out in the news today there was a Pakistani man who was arrested for using $1,000,000 to bribe AT&T officials for the record no one bribes Commerce Department officials that's because we look for results all right so for these sort of non-financial related attacks what are some of the threat actors that we should be worried about well the good news is I don't see
anyone with a hoodie on or an old-timey mask so I think these are good hackers are there any other threat actors that you think we should be trying to worry about well yeah you have to break it down you have to look at the criminals those just looking to cause chaos and then again the oops my bad the clueless who don't realize what they're doing and the effect it will have whether they're a panda or a kitten or whatever [ __ ] name we're gonna come up with because we're running out of animals the latest one on the horizon is now Vietnam Vietnam has started to actively hack everything in their countries so just following the rules the way the
rest of us do it so that gets us to a question of thinking about motive so is it easy to tell the motive of you know for someone who wants money pretty easy they want the money for these other types of attacks is this something that's easy to figure out well sometimes people want you to know why they did it if they're doing it for chaos or the lulz they'll tell you whether they're lying another story that's true sometimes people claim credit for things they haven't done as a white man I'm very familiar that phenomenon the sorry plan that I do it not that I'm victimized all right that was awkward no but I think your point which is that
there are lots of times that we want people to know that we did it right I drink your milkshake do we always have that not always I like to say anytime the Israelis are on your system because they're so good you never know their motivation well that's the question isn't it Israeli vendor or is it the Israeli government so Liz you you talked about chaos should we fear the anarchists the people who just want to break stuff well going back to capital one I mean doing it because you can according to court documents is in exposing that kind of risk I would have to say yes I'll take that answer for 100 points that's true unfortunately the
points have been ransom weird so yeah sorry about that but yes according to the court documents the suspect told another twitter user I basically strapped myself with a bomb vest effing dropped Capital One's Docs and admitting it which is not a great thing to be on the record for the FBI are there other sort of a nursing that was a while we said that wasn't the most important thing there's a big deal are there other reasons why we might want to worry about the people who just want to break stuff from my experience they tend not to do as much harm they tend to get the low-hanging fruit but there's still a lot of low-hanging fruit out there all
right so now it's time to take a quick break and get a quick note from our sponsors in addition to the lovely b-side sponsors Jays game show is brought to you by bolt on security bolt on security because sometimes you don't want to be asked to actually build it properly yourself bolt on security why worry bit now when you can worry about it later we are also brought to you by the miracle hangover cure hydration hydration it's what's going to keep your pee clear while you're in Las Vegas hydration so meanwhile back here we are after all a game show that is nominally themed after Carmen Sandiego so I'll have a carbon Xenia again Carmencita your question Carmen Sandiego
is known for using henchmen and hench women so for the panel your question is what does henching involve Liz a TPS report filed in triplicate with the top copy printed on yellow paper oh my okay that sounds frightening do we have another guess from the panel well to be honest a lady doesn't really describe it a little too much is is there a perhaps even even better answer for what henching involves yes Bryson so it is related to the old English for hen guess or stallion it's true a henchman was a term for the person who worked that for your horse and so it was a groom in the eight days of yore when you know your
Knights had lots of people to help them and so your henchman was sort of the person who did the dirty work while you got to ride off into glory similarly why I get to wear this fancy jacket while the henchmen on the panel and hand Truman on the panel do all of the work for this panel so let's talk politics everyone loves politics it's always great in this conversation people do crazy stuff over political disagreements there's discussion about parties people countries is politically motivated hacking is that still something that we need to be thinking about yes Chris yes there is a bunch of very interesting Russian patriotic hackers I've been told it turns out that yes moving statues has
has caused the problem panels any other answer guys Bryson I think you're well there used to be a lot more in the US but then they all grew up and had kids and now they just do real things at DEFCON yes except for the few that got rolled up in the anon crackdown but yeah that's I think a really important point that you can now get paid to do a lot of that stuff and I think that has soaking up some of the market in the US Liz yes well and for as much as cities and other folks are getting held by ransomware to say it's politically motivated is probably not as much the case more
likely than not a lot of it is just purely accidental or realizing that you're following the lowest hanging fruit the weakest link yep that's that's a fine answer so is hacktivism gone are there any regions where we still see lots of hacked ism in the world well India and Pakistan when even cricket is not sacred I mean cricket might be sacred I certainly don't understand it so I think it's ineffable so yes did you hack an entire schools website because people were celebrating their team's win that's a cool story are there any other areas there we should be concerned about Bulgaria and Romania because they're pulled apart by Western Europe Russia and Turkey when you're at the Nexus of
not just two powers but three powers things get a little sloppy exactly anything else that we're seeing today Bryson so of course I'm gonna pick on China now I also throw a Russian there as well I mean there's this fine line between what they are independently doing versus what a state-sponsored but I guess if you follow their party line then it counts as hacktivism all right no I like it and we're gonna get to the state stuff in just a minute but I want to ask before we dive in there we're slowly ramping up the scariness so we've talked about people doing thing for the lulz we've talked about some political stuff now I want to talk about
cyber terrorism is that a real thing who's got the right answer here [Music] yes I'd like to take the first shot because well Kaos clueless can cause almost as much damage as a cyber terrorist that knowing the motivation helps whether it's a real threat the end result may be the same anyone have a firmer answer yes or no bricen absolutely not second shot fire so short of two facing websites most of these groups don't actually have the capabilities so when we're looking at these kinds of things it's now a group effort it turns out defense actually did get better go I am the cavalry you don't know who I am it's too late and so when they're looking
around that we have now more of a group effort we're in the you know 20 years ago an individual hacker could get up really far now it's more of a team-based thing and it's a lot harder to organize that way and a lot of these folks are could be taking the contract alright so we have a maybe we have a hard no tomorrow I'm going to be doing a talk on cyber terrorism because an insider hacked the Saudi Arabian embassy and was very friendly with Isis and another nation-state and held hostage the entire city of The Hague in 2014 so if you'd like to know more but come to my talk at 10 a.m. tomorrow morning right here and
about their lovely 50 million dollar extortion attempt or they would kill over 400 dignitaries that I would watch that movie by the way I don't know about the rest of you I think that sounds so we're in addition to your talk we're looking for to the screenplay as well so and we've talked about terror so let's let's break this down single actors right is this the sort of thing how easy is it for one person a lone wolf maybe they're not part of the broader it was easy for one person to do some real damage I'd like the fact that we get to listen to that every time there's a question well from having worked for the world's
busiest airport as the technology attorney I can tell you that with the latest Mirai variant attacking LG screens in almost every airport in the world not just in the US using some form of LG screen as their signage that one misplaced thing and suddenly nobody has signs you've created the chaos but then you also look at the fact that one company Aero data does the load balancing software for all of the major airlines and is prone to glitches and one glitch back in April shut down seven different airlines in one fell swoop for several hours so knowing where'd you go you one person can just have a bad software update be it a person or a squirrel alright so
we've got a case that yes one can mate panel any other answers Chris so one of the things we can look at is the bug bounty programs there are some really good people out there like Crissy back there and there are lots and lots and lots of more mediocre people who are just following a well-known playbook wait there playbooks I just a mediocre without the playbook all right so any other answers on can one person make a difference in this world by breaking things buzz president so unless you're Brian Krebs nobody's [ __ ] with your website is that because things have gotten better or because the actors have changed I don't know it doesn't say
anything about that mr. fantastic so it's time now to play another game of if this is the answer what is the question the answer is three what's the question Chris the number of furry propositions I might accept okay I mean that's a pretty good defense rate from sixteen thousand to three faz yes Bryson my actual emotional maturity age can confirm this the number of bitcoins that some city somewhere has refused to pay to unlock their systems and do we applaud that or do we think that is the wrong decision it depends you know it's really hard to get this fair point and a profit motivated attack do we have so a do we have another answer for what three might
be Chris so the number of people that were killed in a German steel mill attack it was the first known instance of cyber used to kill people in 2013 do we know anything else about that incident today uhm the German BND will not release any other information other than one paragraph about it just that does the audience have other known mechanisms of a cyber attack leading directly to death I'm going to take the mic to you I jammed poorab CSO online I had a very reliable source tell me in 1998 that in the mid 90s a New Zealand hacker hacked a test nuclear reactor in Pakistan causing a mini meltdown and the death of 80 engineers I've never been
able to prove it I am glad that we have put that unsupported allegations on the internet that is a fascinating story and and hopefully hopefully we've inspired someone to do a little more digging of it's fascinating hey we stand behind our 5i partners okay but that leads to the real question here like the big actors now which is nation-states do countries currently have the capability to and let's see if I'm pronouncing this technical term right F things up panel yes absolutely any other answer yeah right close the door yeah all right now we're skiff yes Liz do you have an older man sir uh yeah really just by asking the question I think we're gonna
deduct some of your points oh thank you thank you I'm in the audience back over to myself all right well if we know this is happening let's actually dive into some of the really scary stuff are we seeing attacks against critical infrastructure Liz exactly but you wouldn't been able to listen to that if you're living in the Ukraine on December 23rd 2015 we're 30 substations 230,000 people pause 230,000 people were without power for one to six hours that sounds pretty scary do we have other examples of you know people getting all up in the cyber and breaking things in a way that would make us not sleep that well so in the summer of 2014
there was a raft of production ICS related attacks all across the country of Germany it affected the pharmaceutical industry the steel industry the lumber industry every type of industry and it nearly shut down their production that sounds pretty frightening Bryson you're the scariest person in the room mainly just because Ming left who's gonna be here for DEFCON who's coming to my talk where I'm going to be breaking down all the critical infrastructure attacks we saw in 2018 in detail put up your [ __ ] hands [Laughter] see you think that you can't be educational entertaining and self-promotional all at once but this panel has really demonstrated well so let's talk about what we can do about
this then so if countries and maybe even the occasional individual or well-resourced group can do something really bad what options do we have can we you know try to stave them off can we convince the bad guys not to attack us buz Brice there are two kinds of influence in the world there's the one where I put a gun in your face hi Tyrone and you do what I say as long it's there the second so I put a bullet in your head and you permanently do it well that gut Grimm should put that up for my nickname yeah so one approach is just we have lots and lots of force on the other side so if
someone comes and attacks us we make it clear that we're going to do this do we have those red lines today well so red lines I think are more of a policy and academic thing sounds like the kind of thing Department of Commerce would be you know coronate with NIST about we just take action and then we think about it I like that are there other things that we know about how to you know deter organizations or countries Chris well after some of the EU NATO cyber warfare exercises and Brussels and convincing perhaps influencing unduly my group of countries to use the nuclear option to create an EMP over the attacking country we've now been building a diplomatic
toolkit so that they can actually talk to each other before they launch a weapon you see brezin not everything involves guns smash Chris sorry Liz as you say okay but it's an interdependence creating the interdependence where if you break our system you've also broken yours if you break our travel that you will inevitably take out some of your own citizens or disrupt your own industry and your own systems I think that helps as well I like that so see again sometimes we can get newer and fancier guns that we all have to use together so that one China yes I don't like that part well so let's let's continue talking about sort of some of this new
and emerging tech so you know a lot of us are engineers we like new and shiny things is the evolution as things evolve is that going to make things better or worse for you know these attacks that aren't just crime that are these attacks that are meant to hurt you know is AI going to save us as IOT and by the way if anyone mentions blockchains you lose can I leave the panel if I do you've already ran some weird my points anyway so I've got nothing to lose well now I'm going to actually make you tell a story about how blockchain can help fight okay if not if not blockchain water some of the other emerging texts
that we should pay attention to Chris there's a few different types of emerging text I'm currently advising the EU Parliament on how to use different types of artificial intelligence for warfare but also we're concerned at the University of Oxford and De Montfort University with quantum computing and how that will actually affect the current encryption and what it will look like hacking in a post quantum world I like it can we get a contract for that too well if I've already been ransom weird I might as well talk about that place I worked that part of it avoided the ransomware and at the airport being able to use the Smart City or the IOT connected technology but also unmanned
systems and as long as you weren't using a certain Chinese manufacturers aircraft in which case you knew your data was going to be exploited and taken somewhere else and etc etc but being able to then take that technology and that interconnectivity and do get better data on a runway for example inspection then you could using unmanned systems you can get the twenty minutes thirty minutes of flight shutting down the runway what would previously take hours much less clear data can get to the granular level that the unmanned systems and the different sensors on those good no I think the rise of unmanned systems both scary but also potentially useful potentially and also if you're trying to
get supplies into war-torn areas where someone may not want to be able to go you can do humanitarian airdrops and stuff so you hear that bricen things coming from aircraft paradise I don't know humanitarian is you didn't shoot down Oh nation-building Wow I mean we're liberating them so I got one buzz please so it goes both ways all too often we look at technology as the savior to overcome the fact that it turns out people do things people use computers the greatest surface area in any organization is people regular people not IT professionals not folks who are like I actually know what a computer is these are the folks that think the cd-rom ten years ago was where you put
your coffee these are the folks that we're still learning if I turn it off and on again it works and so as we add additional complexity that's called from an offensive site increased surface area you've now given me more of a target to go for defensive products our target just like anything else the more defense you have also the largest your surface area for me to attack all right now I think so basically we should have smaller organizations and less tech yeah I think we should just go back a few you know decades centuries just let's keep it simple well you know I call it my trebuchet plan yeah so one possible explanation as to why we haven't seen more people
exploiting all of these vulnerabilities that we talked about of the beginning of the game is that they are but maybe they're not telling anyone about it so what's the possible motivation there Buzz Bryson nobody likes to look weak well I mean with Chris around with her guns the rest of the panel well all right I've never had an arrow brandished at me before you don't know the right people then are there other reasons we may want to not actually disclose successful or potential attacks hey Chris like this morning and nobody really wants to be told that their baby's ugly some of us still get told rectly it's still not listen I tell a lot of companies that their babies are
ugly and attribution ain't easy I mean if someone's gonna take credit for it or if you're going to point the finger at another country nation state actor you better make sure that you are correct and that they haven't perhaps fabricated evidence to the contrary no I think that's a great point hard to attribute so audience have our contestants who are currently all tied have they successfully answered your concerns about why we're not all being pwned left and right by arbitrary bad actors does anyone have any questions this is the time for audience participation you can also participate forcefully you made eye contact you have a question yeah you yeah no that doesn't blocking blocking the eye contact doesn't stop it what's
your question unless you're talking about a retinal scanner in which case that may work temporarily but you still won't get in the door my cybernetics aren't that advanced yet yes do you foresee anything worse happening in the near future yes definitely yes so I might disagree I think that I don't think we're gonna see the digital Pearl Harbor I think instead what we're gonna have is the death by a thousand paper cuts and we're going to continue to see little slices of things as our adversaries because it's not just about cyber right this is not a game where it's just computers and that's the only part of the playing field it turns out we have other assets that are helping
protect us and those are very much part of the equation of any other nation state that's doing something to us which is why we haven't seen anything say in critical infrastructure crossing that proverbial red line because they know the result is not going to be that we're gonna deface their website we're gonna come and bomb the [ __ ] out of you I feel that should also have been your nickname as well yes I have to look at it to what what's the motivation because if you completely [ __ ] something someone they become useless and if you're just trying to cause chaos and disruption then you can do almost as much damage as one criminal
attack or one clueless stack I mean it's what are you trying to accomplish what is your motivation and the outcome or desired outcome yeah if I can tag on to that that's one of the big challenges we have in critical infrastructure particularly things like election systems I don't have to technically compromise an election system to undermine the public trust in the democratic process and so a lot of these things really are looking at the human psychology of what's the impact of what it looks like I'm doing or the perception of what I'm doing which still has the end result okay hi Chrissy a question for Bryson really you said that you don't think cyber terrorists have
got the capabilities to do much why is it then you think that governments are actually taking out hackers with airstrikes so for example Israel and also the America did it a few years back as well so the Israeli air strike actually didn't take out anybody they bombed a building and there's a lot of discussion about what actually happened on the ground which I won't go into but that story might not be as cut-and-dry as it as it looked like I think the better way to look at it is hackers are a capability like any other capability to establish effect whether that's psyops spying actual kinetic strikes and so they're just now part of the battlefield like anything else any other
comments in the panel oh no [Music] Plus how bad does this situation in us have to become for the Russian meddling in the last election to become considered a slowly creeping cyber Pearl Harbor what if in a few years maybe five six years from now we have still a racists in charge in the US and shootings happening every single day and democracy failing would you then go back and see 2016 as a cyber Pearl hopper to the whole panel so I was I had an interview with CNN this morning and the primary discussion was around that concept what was that self-promotional oh wait airs at five I blindly appropriate responses no but seriously because he
didn't want to talk about the cyber impact he wanted to talk about the people aspect and he wanted to go what can we do about it and while I do not have a lot of domestic law enforcement experience most of my experiences minnow CONUS a lot of what I discussed there was solutions through community engagement to solve the radicalization piece but going to your question about the Pearl Harbor aspect of 2016 to a degree that's I think that's more of a judgment call because I think Pearl Harbor was such a stark event that really shifted world history and you could argue perhaps the 2016 election did it well but more importantly is in 2018 we did something about it
and you can see where US Cyber Command went over and said hi and they did it in two phases going back to my comment about influence the first thing they did was all of the Russian agents or motivated Patriots at the IRA in Leningrad received messages pop up on the screen that said hey we know you're doing this hello now that only goes so far because you know the GRU officer was standing right behind me like yeah continue so that didn't work but then what we did do is we completely took them offline and at that point I always have the a hacker can't hack what they can't touch and the IRAs capabilities were degraded to the point that they couldn't
touch anything so something there was a response again segregating what is the national security response versus you know perhaps domestic policy pieces I can only answer part of that Chris thoughts well I'll be writing a paper with a German think-tank SNP to present at the German Marshall Fund and October for the EU u.s. joint response for malicious cyber activities this year and so some of the things that we're going to be addressing is not something to deal with perhaps directly the administration but the actual response on say between the EU and US Cyber Command and so forth and I think one of the things that is important to oh I'm sorry Chris oh no I
am NOT wedding writing a white paper with a pink this year instead focusing on the third-party risk and the appliance so hardening other systems to make it harder and so that you know what you're you know who you're dancing with and what's coming your way so that companies and individuals can make better decisions on how to allocate their resources but there are no international folks paying me to write should we go around the room and see who is getting paid to write international think tank the and I think it's important to acknowledge the distinction between an information operation and what we might call a CNE like you'd be remember exploitation and rice and point out that often they are going to be on
the same landscape but for this we tried to sort of leave aside the info ops and focus on the fact that if everything is broken why aren't more people smashing why is it just Bryson that's smashing that's not attributed yes attribution ain't easy I didn't do it was it me I think we've got the make up for a pretty good song if it doesn't return further questions yes you got a mic okay so are we seeing any trends in nation states using a kind of third-party contracted hackers from other countries or are we seeing more staying internal within their own home country so it's been more internal and a lot of that has to do with control now that being said
there's there's a fine line between from an outside perspective what looks like an independent party that's where I was teasing about the the activists and the motivated patriot searches doing this versus they're actually on the payroll but I do think we're going to see more of that I think as the as we see additional activities I think we're going to see a lot more introduction of those kinds of third parties in the next five years particularly as we look at the continued democratization of offensive techniques that are being leaked all right I'm going to now ask the panel one final question which is you know here in front of God hackers and a video camera what should we be
focusing on if we're worried about this growing risk mentioned of sort of people not just going after a quick buck but actually breaking things and harming other people and systems what do you think we should be focusing on from a technical perspective or policy perspective you know I've now given you hopefully enough time to formulate an answer what do you think well is he on some level it doesn't matter to me who was trying to do what if the end result is the same and you know whether the keep talking about the clueless the criminal the chaotic if the end result is a system isn't working or the you know I can't turn on my lights as an end
user then and knowing exactly what the impact is but just knowing the risk landscape knowing what you're doing the companies the different things that are playing into your environment and having a good feel for that and knowing what you can do on your end because you can't always control the actions of others I would like to see more countries adopt the Dutch model for requirements for coordinated and responsible disclosure from every company and vendor without that you have fears of litigation censorship or just not having any sort of program being able to acknowledge somebody handing you a vulnerability or exploitation information and I would really like to see that much more also in draft UK IOT regulations and other
areas that are growing around the animals there are certain parts of US government that have been actively promoting coordinated vulnerability disclosure for four and a half years now you can take credit for that there well the US government yes it's the the rest of us just aren't doing anything yeah speaking of which Bryson what should we be focusing on so my biggest concern is the promise of the internet that we were all given is that this was a way that one we were going to find data would be set free I remember when that was a thing remember that it would be easy for all of us to find truth and information would all be level
and what we've seen instead is the world is starting to balkanize and it's really bifurcating into those who believe in an open Internet and repressive regimes who have now seen the ability to control their populace and they're starting to close themselves off in these enclaves China has already done it Russia is already looking at doing it and I don't think that's gonna stop I mean those are not countries that we can influence enough to prevent them from doing that but that doesn't mean that the promise the Internet is not something we can still see as the standard in the international order now that's not something we can dictate as much as we have a lead as the United States it's
something which is the opposite of everything I've been half joking and half saying throughout this and part of this is this was scripted what I say so don't take everything I said with face value this is the only part where I'm actually allowed to go off-script that say something is de taught we actually need to be building de taunts with all of those countries to be able to continue to establish a free and open Internet against where these repressive regimes are going to continue to just carve out their piece and let's hope that they can't force other regional players into that and create their own internet alright that is an actually a note of hope of saying let's keep the
internet as awesome as it has been I hope you'll join me in thanking our great contestants they've each won a pair of the socks that are floating around as freebies that didn't end up in the bag stuff so well done everyone also travel assistance today was brought to you by weather delays weather delays it means you won't get a free hotel room weather delays so I hope you will all follow these brilliant people on Twitter they are both erudite and educational and I hope you will all join me in giving them a round of applause thank you everyone [Applause]