Hardware-based Security: Gimmick Or Game-Changer? - Mantas Stadnik
Show transcript [en]
thank you thank you thank you I wor with actually recent startup start few years ago got into many areas today I'm speaking about public security and we got a chance to actually work on one of the interesting projects so question is is it a gimmick or is it a game changer on the agenda um I will be talking by the hardware based security project called digal security by Design um I know that there's quite a few other Hardware based security projects but in particular this the one that I'll be talking about today and I'm going to mention the organizations and the Enterprises that are involved within this project there's quite a few big names out there so it was IM I'm going
to talk about the ACT problems that Hardware based securitys to tackle and I also going to talk about the new technology that actually has been uced and developed throughout this project um how does Hardware based security actually tackle today security vulnerabilities and issues and in addition pment which is company that for on our PR concept project um and finally I will also uh talk about the feasibility of Hardware U Bas security is it really necessary what are the Alternatives um and is actually worthwhile looking into so who is involved um start and Vis security by Design which I will refer to as BBD a lot quicker and a lot easier and what to do is
fundamentally change the Computing infastructure by by creating new more secure Hardware as well as software um tsdb is a joint research uh project by University of Cambridge and the SRI International and for anyone who doesn't know about s International it's an American Research Institute they're the trustees of Stanford University and have done doing this project with United States Department of Defense Department of Education on the the healthcare Institute as well so this is this project is also directly sponsored by the UK government which not a finding there um and ultimately it tries to bring together the world leading a research base with Britain's best businesses just for a safer future and in terms of funding it brought together
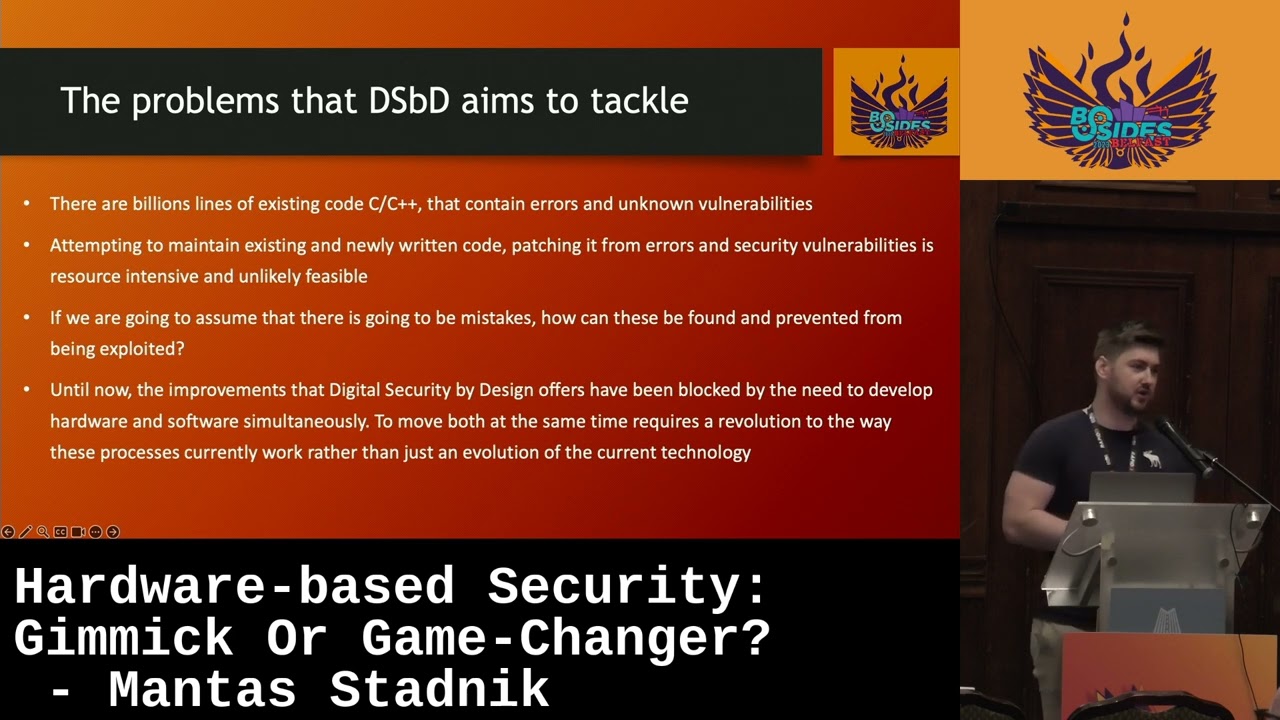
about 70 million pounds worth of government funding which was then marched by 117 million pounds worth of Industry investment as you can see there's quite a few big names there on Microsoft the department of science H points course so what are the actual problems with theb first thing first there billions lines of existing C on they and unknown vulnerabilities now because ultimately people who write software are human beings human beings are inherently making mistakes these erors will continue to happen and in particular I'm talking about is the memory um in addition people are constantly been pushed for deadlines meaning that it is often preferred to reuse existing code and through the ReUse of existing code forther
vulnerabilities be introduced now a lot of time and we don't see the one will leased immediately and it takes quite a bit of time for that exp to p through that to be taken advantage of and particular where soft has been 1980 1990s more these recently and which was particularly seen in the 2017 NHS ROM attack and I'm sure everybody already heard of it but I thought it was a not worthy mention um so what happened was bunch of devices under the NHS framework was attacked devices were taken down meaning that a lot of data was lost and productivity as I remember there was about 19,000 appointments over Council about 72 million PS worth um of
taxpayers money was used to actually bring these systems back up and U get the data back um but the most um interesting thing that I found was that the vulnerability and was caused and was inly rooted in Windows SMD s now interestingly it was developed back in 1984 which is the first place and it was so interesting to see because a vulnerability back in 1984 caused such a massive such massive amount of damage that for on in7 and in addition to that what was really interesting to see was that a month prior to attack Microsoft actually were B aware of this vulnerability and they actually released as an emergency security po um I'm not sure about the
inner details of the HS but actually fail to deploy P either they were unable to due to Resource constraints or else this they just will not well but just because even if you do find a fix for the S and in the exist software the difficulties also actually deploying these CES on um so attempting to maintain the existing and newly WR code and passion for and vulnerabilities is extremely useless and passive um and ultimately if we are going to always assume that there's going to be mistakes being made in the new existing code the existing code or the new code how can these be find and prevented if you can't fix software ultimately your next that is the and is
exactly what pbds to and until now their per by Visual Studio Design offers have been blocked by the need to develop the hardware on sof and there's quite a few good reasons for that right developing brand new hardware is very resource enhan and expansive um also trying to convince organizations Enterprises and individuals to take their existing um Hardware that they pay for that that they familiar with and to exchange it for a brand new hardware that they have to purchase and and learn how to use is a rather difficult task um so to move a both hardware and software at the same time really requires a revolution to the way these process currently work but just an
evolution of the current technology which is PR because it's much harder to simply just make the current technology better with software plus what lot of the focus so um problems is the 70% of software vulnerabilities are generally acknowledged to be Memory safety issues this statistic that have been referenced by BBD has been asked by US National Security is also very interesting to me to hear that the two talks that this morning won by CEO of the British national security Center as well as the Microsoft researcher they both actually mention these um statistics so languages like C and C++ provide a high degree flexibility and efficiency in Family Management for with the honors on programmer to do how we
letting programmer have all control whenever it comes to memory management and in her there's always going to be because why there so many vulnerabilities on and increase vulnerabilities andity so BS can Le to issues such as proper overflow or unattach accessing objects of the long type which can be by so the Revolution and Hardware based security technology I going to mention all the new technology that's been introduced through this project which aims to complet L memory and safy issues first one and it is Cher the new instruction set architecture and it is based on the existent risk and but it's Curr and based on the risk existing stion and unjust can enhanced who I like to call
it is an a new instruction set arure which has been P St um so risk is a wellknown um concept now has been wiely the field AMD consumer G and indust G M processors have been using it for many years in addition arm has also developed extensions based on this uh architecture for their own new mobile micro processor such as Dragon so what Cherry is do is to provide a memory protection model by a capabilities a capabilities is of extreme importance but I will cover them in the next slide because it just deserves a lot more detail in addition to the new instruction set arm came on board and simply because arm recognize the potential in this new and capability
architecture and specifically in deterring certain key security creatures that it can prevent they decided to take part in this project um by producing a morelo evaluation work which implemented this new architecture and in addition to the new hardware we um this project also implemented this new Cherry PSD operting system and it's solely based on the existing pre PSD which is UNIX like operting system and the only changes made that is to actually Implement these new and memory protection um features called and because this new Eco system has been developed from the hardware up and applications will now then be um compiled specifically for this new architecture and utilize these new uh features so um introducing the actual Cherry
concept right like how what is the difference between the traditional approach on why this it actually model so men computer systems are insecure in large part because of combination of theal Hardware architecture in addition to the C and C languages which provide only course GRE memory profection now whenever you give whenever you give full control to the developer and when it comes to accessing Al and theoc memory errors will always occur and and because of these coding erors exploitable security mobilities are introduced so chering architecture revises this Hardware software architectural interface with Hardware support for unable durabilities which are used for fine gr and reproduction and compartmentation and one of the interesting quot which was wred by Paul Waller was
that dbd challenge aims to ease the burden on velers of ensuring that the products are hard dis and this is exactly what the project needs to do is to completely eradicate these memory safety issues that C+ C and C++ introduces so I mentioned these Char really S three times now so what actually are them so on the the left here we have this classic approach pretty simple we got a pointer with an address and reference which points directly to an addressable memory while on the right we have this new dsbd approach now to the addition of the dress gra we have mad data through the use of this new Mad data it provides us much much more control over the
traditional approach the combination of the dress reference and the matter data we now call this capability and due to this new capability we are able to extract these new validations that we can enforce when accessing memory one of them P validity and integrity so what we're can do is we can ensure that the capability is valid and of no Provence Provence so any case where process is trying to access memory that's but doesn't actually even exist an aggress memory we know that a exist um another thing is BS we can significantly limit the area of memory that can be accessed so du to these uh new mattera instead of the process have access to the entire addressable memory
so in case exploit we able to um access anything they want and with the dbd approach we're actually set hard limits on what the process can actually access in terms of memory and in an explo you cannot go beyond these limits we also have these new commissions U constraining the set of operations that can be performed essentially if a process request right Andre um permissions we can grant them and but whenever it comes to let's say they no longer need right permissions only need read permissions what we can do we can decrease this these permissions and those will be the permissions that they use if they want to allocate M then there's no permissions at all and in
addition we have micity which is binds and permissions can not be increased so whenever comes to the binds the process will receive certain amount of addressable memory and they'll be hard limited they be they will never be able to get more memory and therefore limiting this address space they can access in addition permissions can also no longer be increased so in a case where a process wants to read and write memory um and then they're no longer needed let's say the the allocated entirely and those permissions will be gone forever and they will not be able to treat them [Music] again and through the use of these new capabilities what we can then achieve is
compartmentalization uh which really just provides us with fine green com compation of memory so that mises can be sign reduced so as we can see last SL during the classic approach in in a in an exploit whenever there's a breach of memory which could be anything such as and proper overflow um the attacker can actually exploit any piece ofas memory but whenever it comes to this new dspd approach because we have these capabilities and set limits um even in a case where the exploiter can reach the process they will only be able to access a very small limited am of dat meaning that the damage they can actually induce sign and simple exploit will not provide
full access to the entire adjustable memory and more U more often than not whenever it comes to these cases and exploits whenever an attacker does g ADV access to the limited area often times there will no there will be no valuable U addressable memory on the contents of it will uh not be of interest to the attacker therefore you cannot achieve anything valuable so I going to just talk about actually and everything was just um so we pan we had a chance to contribute to the dsbd project and work on an actual proof of concept um it's all well and good whenever we have the H but we also need to ensure that this can
actually be implemented in real time which is exactly what we wanted to do and in Autumn 2020 you can research Innovation r a competition to find a range of projects that work to enrich and expand these software now you can imagine that we have this new hardware we have this brand new instuction set that nobody has ever used we have specialized CPU we have this new OP system so we need to develop everything else to support it and which is what we call the software e system so us we applied for this competition and we actually were one of the 10 UK white winners of the 2021 Vis per by Design and which software a
system competition and we were allowed to go ahead and inform about the software and actually made a positive contribution to uh BBD so the project that we specifically focused on was Secure high performance packet processing one of the fundamentals so packet processing is a core network uh networking concept widely used in powerwalls network monitoring storage backup packets receive from Network and for classification filtering or other processing now this packet processing um is usually divided into two separate approaches distributor approach which mainly focus on the security um there is also the model approach who is quite the opposite it focuses on performance right the way the distributor approach achieves it security is by using the inter process communication what
essentially does is the processes such as the plugin and the rest of processing within the network stack are completely they have their own shared address cases which they cannot um access Now by using this um enter process uh communication mechanism and running these process in separate um address basis the problem is that this introduces a massive problem performance because you need that overhead to share so just a pack commiss whenever it comes to the model iic approach they have sign improv in performance by using this new data name development kit and what it really does is gets rid of this overhead that this distributor approach and introduces by running all the processes within so the
plugin part plugin for example and the network St processes under the exact shared memory address and dpdk the data pain essentially is just a set libraries and that focuses on receiving and sending packets within the minimal number of CPU Cycles because of their approach of running multiple processes under the exact same shared memory this uh introduces a lot of risk M abilities security risks so as I was doing some research um over this new um approach s perform approach and recognizing there so many any um security risk been introduced um I want to know if there's any know inabilities this introduced very well documented um through my research find there was actually 16 vulnerabilities um and seven of them in
particular CAU now the reason why is because they were actually caused by Auto BS M reading rights um buffer overflows and lack of points checking and permission Claws and the reason why it was so me because this is exactly what the dbd project tries to eradicate entirely so no one and this approach and and this security Lis that it introduces we had an idea of why not combining both approaches with a monolitic approach and the dbd approach the dbd approach and introducing security through the capabilities um and the monic approach which is the more perform approach so we had this idea and want to test it because what if we can actually achieve the best we can achieve performance and
security at the same time so once we came with the approach we put it work and particular work with theb to show the CH abilities could be used for performance cure packet processing and the way we did that was by receiving the moral aard that was developed by arm which enabl charer abilities and we actually received it and in person and actually run it in real time we also used Cherry PSD system has devel developed and and we installed it we then ported the data P development kit which is seen in the model approach to achieve performance it was ported over to the moral board and on this new architecture simply for packet process performance
Improvement now there was also um a new application that was developed in house you can see and it was called L and and we aimed to prove that the charry capabilities could in fact secure the natur packets and the way that did we did that was actually try to modify the packets directly and we ensure make sure that we can not read outside of theil ones we can notot write to read only theil and buffer cannot be illegally reused so this application was Sol as a third party plugin we attempted to do was we consume the packets as we only permission and we try to monify these packets directly once we actually had this implementation running and implemented
uh we decided to compare against a distributor approach which uses the enter process communication with the performance problem the new dsbd approach run the application and the plugins under the same process meaning that it was run under the same shared address this just like the monolithic approach but because of these new capabilities we could enforce safy specifically memory3 through Hardware means the particular performance Matrix that we looked into was packet processing latency and CP utilization and we measure those against various packet points and various packet sizes specifically packet sizes 52 bytes right up to 8,000 B and then in terms of the packet we have numerous testes 20,000
pack, once we actually measure those measure the two approaches very as you can see here to the left the latency versus the packet size of the BBD approach buring it's St consistent comparing this to the traditional approach that is widely um implemented through the entire world um the enter process approach like the lat increase which is even on Mon DD and whenever it came to CP utilization we can see thatd approach also utili a less CPU resources and I think it's funny to see that the worst case of BBD was the actual bestest um we also got a quite a bit of positive feedback from John gaker um and he's just happy to see that we can
actually use this new dbd um approach and combin it with form approaches and achievable security EX in conclusion the theor charties were implemented and should be working successfully in real time and it combined the new hardware the new instruction set the new OP system and new oblation together for the dbd approach showed that using M of chies required sign significantly less resources provided lower leny and was a while the same being completely proving dbd on Superior skillable and performant M pack processing approach which I believe is step one and providing improving that this new approach can be broadly app applied eradicate the memory in off is Sy specifically for C now do we really need this new
hardware my Hardware is hard to it's so expensive so let's look at the alternative options specifically softer cheaper alternative options rust be enough I know that previous talkers also mention to um and I do agree it is a really good per it is an alternative to C and C++ but with new Concepts that improve memory saing which is exactly what hardw B really and they achieved this new M Cy the use of ownership borrowing and essentially ownership h p loer And1 time as well as borrowing m p code can have access to memory in addition there's few other features which are notably mentioned resizable data structures as well as IND types including overflow through these new Concepts and
features memory related bus like no pointers use and both overflows are but what about the exist there billions and billions assistance so how do we go about fixing that one answer is let be about exist but whenever we have such a copious am code is not useful and require estimate am resources so some of the hurdles that can be faced Hardware Bas Security in terms of and implementation which is migration cloud computing migration cloud computing is ever go um and without the on start centers companies no longer need uh to consider such as space considerations power requirements and purchase of expansive equipment and the maintenance of this equipment and now of course as a consumer all you care about is here's my
application here are the for the application just go it out rest and ultimately as a consumer Computing you really should avoid the hardware that your application from but I understand I understand the argument I'm sure and as a consumer you don't really need to worry about that because it's up the provider but the end of the day the provider should be the one because it is their responsibility to release secure hardware and make sure that is being kept up um and even AWS themselves said they have over 300 available cyber security tools consumers to use so the C providers actually do there um the biggest hle of the all is the requirement of new hardware and software
and we have new board with a specializ CPU we have a new instru set architecture a new OP system and all the exis applications to make a compatible for this new architecture set must be have so that is a amount of effort we put in and and one of the biggest phots is actually convincing companies to give up their existing um hard the platform the p is working and replace with this new um and yeah it's really hard to argue against that but I do have one solution po use let me introduce tested by pbd console even though you may not have the hardware and Hardware will not be available and you may not have to
purchase it what you can do is you can build your application for cherry and architecture meaning that but even if your application is going to be for a different architecture entirely what you can still do is build and compile your application specifically for the Char architecture now you're not going to get the real time memory safe capabilities but you will be met with a lot of compilers in the case where there are memory safety vulnerabilities by using by compiling you can detect these mul abilities and early which you would not get from typical um compiler for different architecture um and you can utilize these Cherry compiler checks without having any of the hardware or the
software and all you need is the compiler schable do it and ultimately I think the best solution for it and whenever it comes to testing pipelines is you have a pipeline that and compiles your application on test test on it and specifically for your targeted architecture on the other hand you have this Cherry architecture and you simply just check for comp compilation um and having this implemented with your testing pipelines you can have a pro confidence level when delivering EIC changes such as every time you push a up and you want these get the benefit of the ch so hardw B security is it a gck or a game changer I will I was with thank you for invited
[Music] [Applause]
attention Okay we have time for a few questions and uh maybe you're all getting hungry and waiting for lunch downstairs but but certainly floor is yours folks if you want to ask a few questions [Music] on yep so the development as you mention they support ACC architecture this support arm architecture as well right because so arm architecture is based on the risk bis risk architecture um on Cherry extends the risk architecture so all we have to do was actually considered new extensions that were added to the original risk architecture so it was just extra CPU instructions we have to be [Music] very it seems that this is fairly good at protecting processes from other processes with have a lot of extra
coding effort but does it protect a process from say code injection into that
process by Design but what it aims to do is limit the damage that availity Avil that can be made right um because you have these hard limits on the Dr SP you will be sely limited on PR you can
do yes but it's extremely [Music]
limited yep so we if you have two processes right uh one process gets an allocated um area of buod I mean sorry of memory and another process it gets allocated memory as well and they're sharing the exact same memory right they will never overlap the bonds will never allow for one process to cross into the realm of
another
well the main game that you get is that any SS R within the code specifically memory safety Earths canot be
exploited
so recompiling the existing code off
the yeah you will get all the BS yeah you will get B this iMed because these new capabilities right are s by Hardware right they're enforced by hardware and they cannot be overwritten through software does that answer your [Music] question I I think this is something that could have to have a deep dive technical session on its own I think there's a lot more discussion in this one but um feel free to right any further questions question ands y okay one [Music]
last no um so it really is just an evaluation board um specifically the mor board that implements this new Cherry architecture what it really is is just proof of concept that we can actually achieve this um so in the near future yes it may be possible um if you were part of the the very first talks as the C from the British national cyber security Center he actually mentioned that this is a 20e project but we're going to actually see if this is something that we really really need and if it's really useful um the results so far proved that this is absolutely necessary and this is incredible um one of the other interesting talkers was the
Microsoft researcher who was dealing with family safe issues every single day right and she actually cursed C++ because that is all she sees and in one of the particular examples whenever I had a chat to her after the talk she said that even a couple days ago what she saw was that it was a vulnerability that was due to the mem safety issue that Windows which was written in 19 1989 or so so she's so so surprised that this Oneil has existed this entire time theil is actually all Earth U but yeah I get to the point is yeah this is more of a proven concept at the moment but there is definitely potential to roll this out
in the broader Market okay I think that's us uh launch is downstairs folks and uh we'll be back later on thank you thank Applause





