Dungeons And Datacentres: Dilemmas And Thoughts In Social Engineering - Tom H
Show transcript [en]
she is for coming I realized that there's a whole bunch of you know talks activities other things you could be doing people could be chatting to so I really appreciate your kind of turning up to see my talk is dungeons and datacenters which is kind of covering some of my thoughts and violence that I've had with sort of experiences social engineering recently so so so Who am I my name is Tom I've done way too long 15 years in InfoSec so I consider myself kind of long-term listener first-time caller as far as this sauce was concerned it's my first talk hence why I'm kind of bracketed as being a rookie the ridiculously long combination of
letters there means that I'm a senior subject matter expert for advanced intrusion testing at Lloyds Banking Group which is the repeated three-letter acronym way of saying that I kind of manage scope and design and perform read team testing for Lloyds Banking Group I'm a avid gamer of pretty much any type so you know from computer games through to board games through to card games if basically gave me a tennis ball and said throw this at a wall and you'll score some points I'll probably sit there for a few hours a massive psychology language and systems nerd so any of that stuff I absolutely love it it takes up a bunch of time I'll read anything about it kind
of dig deeper and kind of look at outsource stuff and then also I must kind of social engineering junkie so it's one more special isms that I fall under the subject matter expert bit of my job title I kind of started digging into it probably six or seven years ago and then since I've been doing red teaming in the last sort of three or four it's become kind of a lot more focused and I sort of decent part of what I do day to day so what I'm gonna do is kind of go down the rabbit hole go through red teaming what it is a little bit social engineering how that fits in and then
we're going to go into the bits of social engineering that I want to talk about the bits that I think are interesting and there's some stuff that we can kind of learn about how to deal with people and how to you know appropriately social engineer them that sort of thing so I've interest who works in a Red Team offensive security or that type of thing or for a company that has got that cool so for you guys I hope I don't teach you how to much how to suck eggs for the start of it and in the last part of it you'll get some sort of useful information out of it so that quote there is the in theory water red
themers you know it's a independent group that challenges an organization etc etc etc sounds really cool you know is really appealing and probably one of the more more interesting bits of InfoSec in my opinion in actual fact it's it's isn't hacking it's hack it's really really heavily bureaucratic and regulated hacking with like 80 percent reporting and that isn't any different when you work for a bank it's probably if anything a little bit worse so scoping red team engagements and that sort of thing and what you include and what you don't is a real art particularly when you're dealing with sort of a large organization they don't want you to go everything's in scope even though the ideal for a red team if
you can approve anything is that yes everything's in scope so as a whole bunch of those arguments that go on on a day-to-day to their life but hopefully going to talk about some of the more interesting bits so social engineering within red teaming so red team is meant to be a holistic way of testing you meant to test kind of everything in the entire environment allowed people break stuff down into being PPT I use kind of pppt I always have to check that I've said there are around peas so yes so covering people process physical and Technology whenever we do tests so when people talk about social engineering they tend to go this is the bit we're
interested in you know this is the bit where people talk about the humans being an organisation's biggest weakness or there's no patch for human stupidity and all that solve really really bad phrases that don't encourage good behaviors in your user base in actual fact or I tend to find that the really interesting bits tend to come when we look at the kind of intersection between people process technology and physical and how like the people monitor those controls how they use them that sort of thing so you find a lot of vulnerabilities in in the way that the people interact with them and in a case of kind of the blue team which is the only kind of blue thing I'll
probably discuss for this talk like the defense's you can put in place there are still some and if you look at Defense's in terms of technology or process controls or physical controls to stop people doing the wrong thing then that does actually prevent a quite a few social engineering attacks so from breaking down social engineering I break it down into kind of four main sections so ocean stroke recon which is a massive subject in its own and is the foundation of pretty much any social engineering you do if you want to do good social engineering you need good ocean a recon fortunately I haven't got as long in this talk as I'd like to kind of dig
really deep into how to do ocean recon that sort of thing but you know it's an essential thing you can find a whole ton of stuff out there online on it so then we've got fishing which is you know the most well known you know really high volume stuff and you know I think the figure is 65% of breaches start with a phishing email that sort of thing then we go up fishing which is phone social engineering and doing over the phone and then the bit I'm always good to that there isn't a word that starts with itching or ends in itching is impersonation which is the in-person physical part they see where you go in
talk to people and actually get them to do what you want in person so I'm going to cover these two areas mainly cause fishings kind of a thing all of its own and phishing impersonation cover a lot the same type of skills a lot of the you know dealing with people dealing with individuals conversation rapport that sort stuff so if you break down phishing an impersonation so it starts off with the ocean recon phase right the start as I said it's a whole whole world of interest and details then we go on to kind of pretext development this is where you're developing the person that you're going to be when you are social engineering someone when you're going in
when you're calling them you know this is how you define what it is that you're going to do then you go for what is the bump or initial approach with phishing this is really really simple so this is the bit where you know they pick up the phone when you're doing impersonation a bit more complicated it's the bit where you stop being a stranger to them so you answer put your questions as you approach them in order to kind of put my ease stop them questioning you too much then we go into building trust and rapport which is what normal people would call a conversation but when you say when you do social engineering there's a whole bunch of
other factors that you're trying to do at the same time as having that conversation and then achieving your objective so trying to get someone to do something they may or may not want to do in order to help your attack or or progress what it is you're doing so as we go to kind of further down the rabbit hole these the bits that I'm probably gonna focus on that bumps or approach stuff is it's kind of fairly low-key and not something I'm gonna go to detail on but they're the kind of protects development how you work out what you're going to be how you gonna be approached it and the building trust and rapport section the bit that are kind of the
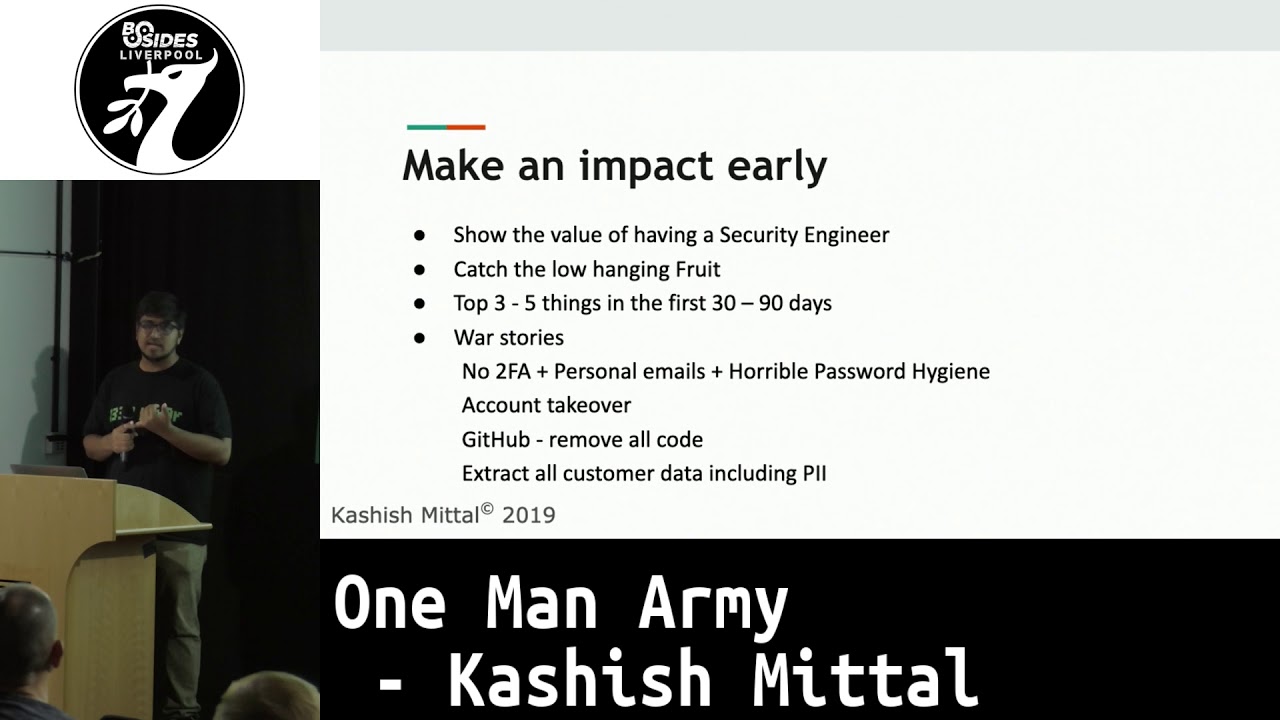
main meat of your social engineering engagement cool so I'm gonna go over some of the stuff that I use as kind of weapons at my disposal so as I said I've done a bunch of social engineering research but a bunch of reading about it as well as a couple of different training courses that sort of thing I'm a social engineering pentest professional and master's level social engineering expert from social engineer dog but on top of that there's some extra elements that I've sort of used in order to help me with these dilemmas and problems so psychology and sociology huge subject whereas social engineering as an idea has been around for like 10-15 years obviously psychology and
sociology have been around for hundreds so there's a whole bunch of tools a whole bunch of stuff that lets you dissect how people work what they think that sort of thing and it is where a ton of my research time goes is into thinking into this so another thing which is kind of quite awkward for most techies and that sort thing improv acting so the really really similar part of social engineering applies this is kind of the the impersonation section you know when you're there when you talk to someone you kind of want to be able to come up with ideas discuss new things and kind of edit what you're how you're behaving and what you're talking about
in order to apply better to the target it's also the bit that at least I find is the big fear of social engineering is that part of going oh my god and we stood there and I'm gonna choke I'm not going to know what to say I'm going to panic actually The Improv acting stuff really helps with that because you're put on the spot like twenty times and every time you do it and then kind of the the big nerd influence and what influence the title the talk I think it puts me second on the nerd hierarchy on the geek hierarchy slightly below furries um I've been doing kind of D&D tabletop stuff for like 15 years I've been a larper for
like well over half my life in the last few years I've run seven or eight different events for people where we've built entire immersive worlds we've kind of you know developed characters for them things to interact with done like 20 different pretext generations which we define as you know roles for them to interact with that sort of thing and it's a really really good opportunity to study human behavior human interaction in kind of weird settings so like very very difficult in real life to watch someone who's scared for their life but I get to do it like 20 times every event which is great you know and and going if I give a person X Y Zed information
what will they then do with it which is something you just can't do without well occasionally associated new you get to do that but as I've kind of done it I've seen the parallels between the two quite a lot so dioramas and thoughts which is kind of the main focal point of this talk which is kind of issues or problems I've experienced whilst doing social engineering and the tools or ideas that I've used in order to help kind of fix them so the ptex development part as I said realized really heavily on ocean and recon that little diagram is one bit that's really important assess what you can and can't do so like I would fail
miserably to impersonate an Olympic athlete a pregnant woman or a brain surgeon and like you kind of have to accept that but that being said in some situations you can go I'm going to impersonate a brain surgeon because I need to do it for five minutes to this one guy before I leave him away and never get asked questions about it again so it is kind of possible to learn some things very very quickly I crammed at one point to be an interior designer in the space of two and a half hours and managed to carry off a relatively successfully for like an hour and a half in a discussion with people kind of you
have to understand what it is you your pretext needs so what you're trying to accomplish with this social engineering engagement and then look at who you are and what you think you can be within the timeframes you've got so sorry just checking back on that so a couple of dilemmas that I face when doing this is what preparations should I do because that's a really kind of hard thing to decide there's a whole whole world of preparation you could be doing you then what's useful what's not and then there's a thing about how perfect is too perfect for your pretext you know if you're approaching someone exactly how detailed you want to make it and
what you want to talk about so one of the things of course want a spontaneity versus preparedness style Emma so you've got a temptation to write a full autobiography you know you've got you know you're going in you pretending to be a certain person and you want to write all the details you want to prepare everything if you like me you want to kind of design everything put it all down make sure you've got it all embedded in your mind that sort of stuff but if you lock yourself down too hard you lose the ability to kind of improvise when you need to when you're talking to someone so if you approach someone and they're you know kid is does
football then you want to be able to switch your pretext to going yeah Mike it also does football you establish yourself as part of a tribe with them you build a link with them you start building trust and rapport and you can then leverage that further on to get what you want so being prepared is great as much as you can remember it all like that's one of things I tend to find as well is that you get to a point where you've gone I'm not gonna remember all the details of this I'll just remember certain key things and then kind of be spontaneous spontaneous with the rest but even like spontaneity requires a basic amount of background knowledge for
you to leverage in order to know what to do with it so I use this which is Whitney Maxwell's kind of breakdown of digital footprints I'll turn it on his head and go okay like different categories of stuff so core intermediate peripheral information so things like personal preferences likes and hobbies really good things to be spontaneous with really good thing to connect with people on and talk about a little bit you need to do a little bit of research on anything that you're going to be spontaneous about that you're going to bring up so you can at least cover it the kind of I've heard it termed as being the related songs man so knowing a
little bit about everything so you can use that to better leverage your pretext when you're talking about the kind of intermediate stuff so categories like you hometown employer religion you want to do make sure that's consistent research you know in the facts that you can come across as someone who works for company acts or who lives in town X you don't beat them going all whereabouts in you know whereabouts in least you live and you're going all by the car park is you know absolutely dreadful so you want to make sure you know enough details that you can say that if you are questioned in normal conversation about it you can still come up with the right
ideas and then kind of peripheral stuff which is the end of an individual facts about you that's tough you need to know it because everyone knows their individual individual facts about them but it doesn't need to necessarily be researched or linked into anything or anything like that as long as you're consistent with it and you're not giving you know you know introducing yourself as Bob to person one and then Kyle to person two you should measure the time to find so the other aspect the too good to be true dilemma so this is something I've seen a couple of times whilst doing social engineering people are naturally suspicious of anything that's too perfect so you do eurosam
you find out everything about this person that you're gonna be targeting and you're like right I'm gonna write the perfect pretext he's into photography his kids do football he's wife's a chef so you show up with you know your cooking book under one hand your phone your camera onto the other one and start talking about how great your kids football was and he's gonna look at you and go that feels wrong because that's too close to me and normally there's more differentiation between you and strangers you mean unless this is gonna be you know unless you you pretext this that that guys are gonna meet your soulmate you probably don't want to be going to that level of
detail so what I find is that there's a kind of a role play game technique that's really useful here so sit down and go write that list of what I am or what I could be and what pretext needs build out list it out in a big page and then go I'm going to choose one of those at random rather than necessarily I'm gonna go straight for this first one that I've made that's absolutely perfect so take all the elements split them out and then use a kind of random generator to go yeah I'll be this because then it's not going to be precisely spot on and perfect cool so this is a something that comes
from 1730 when they started defining the properties of actors in plays and that sort of thing but it's something that I find really useful so my brain naturally works and approaches stuff and I'll go here's the details here's the facts that saw stuff this sort of thing is the thing that I never really think about unless I'm kind of forced to so I won't go through them all but a few of them like you know the dramatic need of what you're trying to accomplish kind of the attitude of the character that you're trying to portray the pretext at you developed that saw stuff and then like weaknesses and mannerisms are good ways to kind of differentiate yourself break
away from being the same thing every time you do it and kind of also help you load better into what I consider to be kind of different brain VM in that you are then that thing and you're that person so as caring pretext generation so I'm going to go on to kind of developing trust and rapport so this is the foundation of every social engineering attack really really heavily leverages body language and and that sort of thing I'm not going to go into detail on that because there's a lot of people who covered it books by you know Ian man Paul Ekman Joe Navarro as well as talks by Chris Hutton Aggie shark Ian man a whole bunch of other people so
sociology kind of defines a breakdown of conversations into form and content so you cannot kind of analyze them independently of each other and an aspect of the form of conversations is a thing called flow which was defined in 2014 research paper by Guttenberg post MERS an owl so there is defined as being the way a conversation is experienced as being smooth efficient and mutually engaging and as a social engineer I read that description and went holy crap I want that in every single social engineering conversation I have if you've got those three elements then that conversation is going to be going well you're gonna find it really easy to develop trust and rapport and that
person's gonna be a lot more compliant when it comes to it so talking about the form part of it there's the classic social engineering advice you know you match you match the tone pitch speed and volume of the person you're talking to you've got a bear in mind that when you've developed that pretext before you've L this character that you're going to be whilst you're doing your social engineering but if you try and do this stuff too hard because sometimes break that so that's a conscious decision you need to make as to whether to you know if your planks if you want to be someone who's nervous or apprehensive or you know excited then you might be talking a lot quicker than
normal you might be kind of like putting more herbs and and pauses into your conversation so you don't necessarily want to match all those if you still want to come across as the same kind of aspects one of the things yeah never try and do accents like unless you've got an accent that you know 100% you can pass for that person if you're put into that city then don't don't even try and do it learn from Sean Connery you know stick to whatever your traditional accent is and the other thing that I've found that isn't included in that se advice I don't whether it's a positive UK thing because you know we shift around kind of accents
and formality and different places so much but changing varying your formality so abbreviating words not using words that are too long or doing the opposite and being really formal with something can really help to kind of put across your needs what you're trying to do what you're trying to accomplish that sort of thing so one of the other things I found is that a lot of traditional social engineering advice is you dealing with an individual you know you approaching that one person and getting them to do what you want and it's really really rare that well it's pretty often that you'll find that that person's in a group of people and that's a very very
different situation to approach so what I'll try to do a lot of time is when you first enter a group conversation look at positions of body blading and feet so like where your hips shoulders head pointing and where your feet are pointing that can help show kind of how the authority and flow of that conversation goes who's important who you like who that sort of thing and then you can kind of match that to some extent to make sure you fit in now another one of things that that kind of traditional social engineering advice comes along with is being kind of synchronous being similar to the people talking about same things you know agreeing on every sub
that sort of thing and matching them in a whole bunch of ways actually sometimes you'll find especially positioning group conversations that you want to be what they call alternating or complementary so this means that you have a value to add to the conversation you're not being the same as what they're saying you're adding something new but you need to make sure it's not a conflicting thing so add something new that kind of couples on to what they've been saying and then listening out for common grounding noises so this was defined by someone called Kasim or a researcher called Kashima which is the noises we make during a conversation when we're not the one talking that confirm that
we're still part of that conversation so they're yep's aha that sort of thing listen for those and see what the ones that are that are used in that social context and try and mimic those when you're agreeing to stuff it's really good like it's like psychology wise it establishes you as being part of their tribe even though that tribe is just people in this conversation it establishes being part of that and instantly kind of connects you to people so onto flow it's as I said it's really a ephemeral concept measuring how well a conversation is going it's kind of key on the prompts for transfer of focus just to be able to kind of assess how
well it's going so if you listen to two people who've got really good flow they'll be hardly any gap between one of them finishing on the other one starting and people won't talk over each other they won't interrupt as much like he'll naturally kind of bounce between people and they'll pass the different amounts of focus so that focus transfer is normally less than 200 milliseconds in a good conversation so if you're thinking for more than a fifth of a second about what you're gonna say then it can make it seem like you're not really part of the conversation and like the conversations going awkwardly flow comes really easy for people who talk a lot so
these days especially you know your text your email you'll slack or whatever I've started trying to force myself to actually call people on the phone and talk to them because like exercising those muscles is super important and and if you're not doing that then you kind of start falling out over the way to make good conversation so there's a really good improv accounting game for when you're doing social engineering with a group of you or a pair of you you want to make sure the flow between you is kind of really strong and you're not going to you know talk over each other you're not gonna interrupt which is a really simple game involving counting so the concept being the
between you you need to count to 20 you're not going to just take it in turns you're gonna say whichever number you feel like saying and then you after about four or five times of doing it and talking over each other way you both say to at the same time or you both so for eventually get to the stage where you're naturally picking up on that person's kind of body language and cues that they're about to speak and you'll stop talking over them so much and being able to fill up that with whoever your social engineering with means that when you end up with your target you not likely to kind of enter in that same situation and
they'll find it a lot easier to enter into the flow of your conversation and then the other one which is really really good for active listening so if you're talking to people then a lot of the time you'll be sat there thinking about what you're going to say next rather than what they're actually saying so there's an improv game which involves starting your sentence with the last letter with the last person sentence that's really really good and is really good for forcing you to listen right to the very end of a sentence before you start the next one if you can do that with that same lack of talk too much of a gap then you become a really good
active listener people really start to kind of engage with you and talk to you about stuff and that's really good you can do it deliberately if you go to someone and go hey let's you know do that game whilst we're talking you can have a regular conversation whilst applying that and likewise you can apply it to people who aren't really paying attention so if they do even if they don't know that you're playing that improv game you can do it and kind of just force yourself to wait till the end of a sentence before you think about what you're going to say so content so content is what you're actually gonna say to you target you know is this it's
the things you're gonna deliver the things you're gonna discuss so you always want to let them lead and kind of use the work that you put into your pretext earlier to let to help kind of shape and and direct the conversation and make sure you've got stuff to add you want to try and break bring people into helping you so people don't want to back out after commit to doing something people will find that if they've started doing something for you they'll carry on doing that something for you all go carry on doing something else for you you know really kind of get those stuff in early to know what you're kind of framing to get them because you're pull
for what you want to do later so having another person to shift and blame - for any kind of effort or rule breaking the need is really really useful so going oh god my boss is asking me to do this or you know or my wife wants me to do this because she'll be really upset if I don't people can empathize with having a you know potentially grumpy partner or a pain-in-the-ass boss and so they'll instantly kind of put that puts you into one of their tribes as well and then also if they're feeling if there's sort of negative feeling or they don't want to do what is you're asking then they're not directing that
you they're directing that at some guy who's off in the background here they never meet and then they'd be aware of the need to pivot so pivoting is one of the things that gets discussed quite often so it's a situation where the target is either intentionally or not is changing your pretext or kind of the frame of your attack so situations where it feels like they're putting you into a situation where either they're correct or you're correct so if you come in and go hi I'm Dave from IT and they go well I know everyone from IT then this is the point where you need to kind of pivot and go or actually I'm a contractor or I
only started last week or basically find a third option in order to be able to give them something that makes them feel like they're still correct you haven't lied to them and they can carry on about their business so roleplay games are kind of discuss this is being an option three traditional difference between kind of tabletop role-playing games and that sort of thing versus computer games is that they'll always be kind of an option three because you're in the real world and you've got everything to work with this under the Sun so there's a really good improv cornerstone for this which is the yes and game so someone make something up the next person goes
yes and so you basically confirm what the person said and then add something to it now when you're doing social engineering you end up a situation where you need to pivot that's because they've said no book to you which is a really really hard thing and tends to break down in profit improvise those who improvisation so there's a few role-playing games and saw tabletop games that are really really good for practicing this so there's one called The Adventures of Baron von Munchausen which is a one set of being a like late 1800s kind of adventuring Baron where you go this is the easy story I made up and then someone challenges you and you need to come up
with some idea going yes you're right but this is why that's right and I'm still right so kind of learning those things to do in order to be able to kind of still confirm that they are correct and that the challenges is valid but answer it and move on so this is something again super easy to practice with friends you know I play a game called well terms with a friend of mine and I'll say something that's that is nonsense always you know a lie that's made up they'll call and go that's because of this and then your immediate response to that needs to be yeah but this is actually why it's still true and and you kind of
have a vague argument where you're not actually arguing really easy to practice with friends a really good thing to kind of develop and kind of work from there so that's kind of getting towards a conclusion a talk I think I covered the key stuff I wanted to thanks for listening so the takeaways whilst social engineering engagements even working in part of a red team and it being actually part my job is it's something that doesn't happen all the time actually finding Talent ways to practice is really easy so games like that type of thing like one of my things recently has been trying to start a conversation with three strangers every day which is really really difficult especially if
you're in London on the tube you get looked at like an absolutely crazy person but trying to find ways to you know use words at the very least and then a bit of conscious effort and kind of research and a bit of planning can change your in bonus to a Christmas bonus so people who are way of TMZ and stuff will understand so going from taking your intelligence and kind of an analytical mindset and that sort of thing and using it towards conversations and discussions can mean that you actually come across as being really charismatic when actually just substituting it for a whole bunch of stuff you've learned and practiced and then whilst the humans are the last line
of defense and all that sort of thing they can actually be sometimes helped by process and technology controls and physical controls to stop and doing things that they really really shouldn't be so if you want to contact me and talk to me about any of this stuff afterwards or my contact stuff down there Twitter Gmail I hang around on the many hats Club discord and in the SEO and Red Team channels so always happy to chat there yeah cool any questions so I struggle to give direct examples as part of the fact so I work I work for a large bank and they've gone I can't talk about any actual details of stuff like that
but so if stuff when social engineering stuff goes wrong especially if it's kind of a really key pivotal moment tend to find that it can massively skew things it raises suspicions in people that's all things so a lot of the time it's one of those things where if it starts to go wrong you can't really remediate and fix it unless you can pivot well and kind of transfer it off at the time then you end up in a situation where you're going right we just have to avoid that person that subjects that that protects these ballots because you don't want to kind of carry on pushing something if people start to get suspicions it's a real real
slippery slippery slope so yeah so there is some degree of kind of going here's my get-out-of-jail-free card I'm going to walk away ideally just leaving and going we're just going to leave that and let it be someone who's vaguely suspicious and hasn't reported it and hopefully doesn't so we tend to try and feed it back so we don't do it to individuals is one of the kind of cardinal rules because for social engineering anyone can trip up anyone can make those mistakes and you don't want any organization kind of persecuting the individual for having made the mistake that anyone can make but yeah we do kind of go this is the type of thing you need to be looking at
but a lot of the time it's just talking about like awareness of the fact that this is a type of attack and then kind of encouraging critical thinking so people actually go is this really what's going on rather than just naturally assuming yes it is cool well I'm gonna be looking around here in probably outside smoking for the rest of the next half hour and then I'm about for the rest of the day so feel free to catch up then cheers thank you very much [Applause]