MFA Bypass Techniques: How Hackers Steal Accounts #shorts
Show transcript [en]
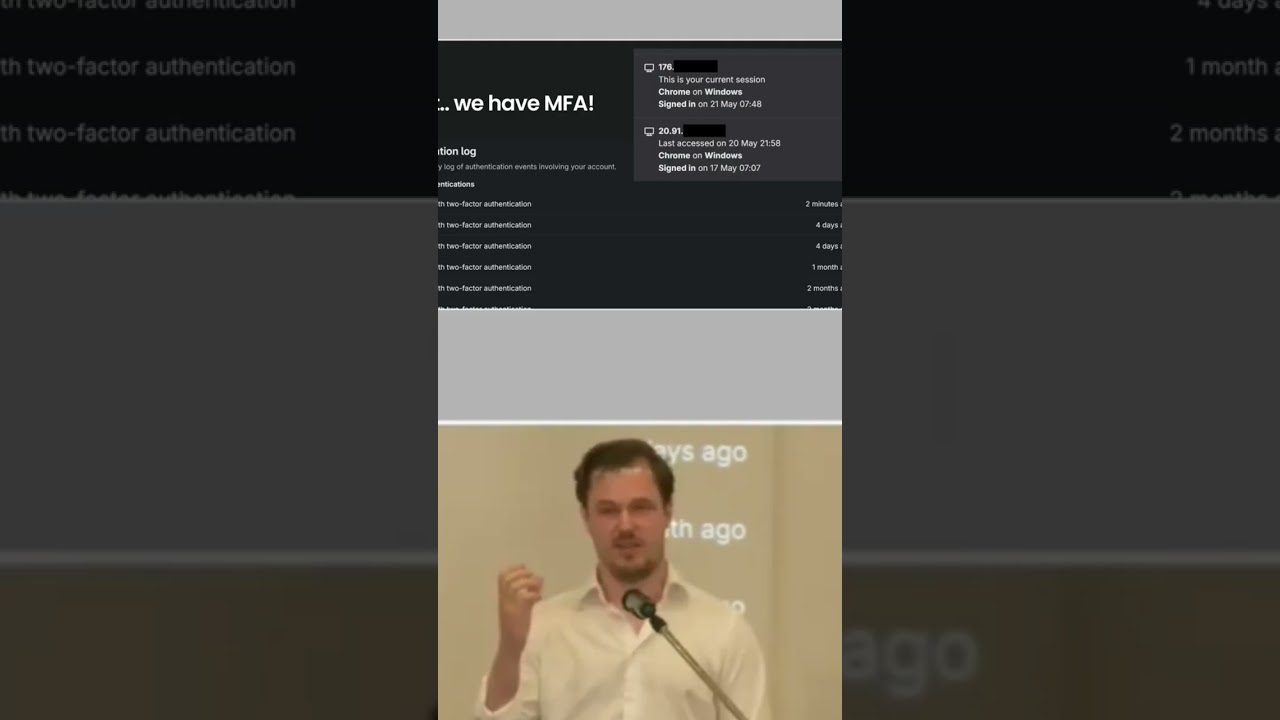
With that said, I guess we have one problem left, which is how did he get access to GitLab then? And the customer said, that's not possible because we have MFA. And yeah. I mean, there are many ways to bypass MFAs that we see today. MFA is great and it's something that everyone should use for obvious reasons. But I mean, well, threat actors have adapted, right? So, we have like an adversary in the middle is really common. So, like if you fish the username and password, why not just relay that to the back-end service, get the prompt, relay back the prompt to the user, make them enter the the MFA prompt as well, so they can
just, you know, do the entire flow. They just need to add one extra step in their fishing sites. And there are, of course, like evil engines and so on that does this at the have already implemented it. Um I think also speaking of MFA, um in a cloud context this becomes important, right? Because a lot of it about cloud security is about the identities that we're trying to protect. And I used to work as a red teamer and when I fished an account, uh it was usually for that person at the company who isn't that great with security, who's not really aware about security. So, if I then fish the username and password, then I call the person,
says, "Hi, I'm from internal whatever, and you know, there's a problem with your salary, but according to GDPR, you need to show me the uh code in that authenticator app, just so I know that you are you." And of course, they're going to just read it out to me because they don't care about security, otherwise they wouldn't have been fished in the first place. Right? So, I just call them up, ask for the MFA token, which I mean, it doesn't really matter what method that they use because I can trigger if I need to trigger a prompt or something. Where it's like, you know, if they have that you need to accept this login, then I
can do that login from my end and say that, "Yeah, you need to click okay to you know, solve this problem with your salary or whatever story you come up with." Um so, I think that it's it's a it's a weird like it's it's not a perfect solution because we're trying to protect people that don't want to be protected in a sense. And if they can't protect their password, why would they be able to protect their MFA token? Um so, there are better solutions for this. And we're going to get into that.





