Jerry Chapman - Zero Trust
Show transcript [en]
All right. You want to use the wireless or I cannot stand here. Just make sure you clip that on somewhere because make weird noises if you don't. Oh, sorry.
All right. Does it work better on the outside or the inside? Fine either way. It's not that. No, that's fine. Yeah. Which one is for Where's the HDMI? This here is for video power. I don't know this for Oh, you have HBR right here. There it is. Got it. I don't need
power. There it is. Make sure this is working. Yeah. Perfect. All right. So, welcome back everyone for our first talk after lunch. We have Jerry Chapman with uh Chapman. Jerry Chapman with Optive with Zero Trust.
Can everyone hear me? Okay.
Test one. Test one. test. Test. There it is. All right. Yeah no worries. Well, good afternoon and um hope everyone had an enjoyable lunch. My name is uh Jerry Chapman. I work for Optive. Uh my goal here um as an employee of Octave. I'm I'm an engineering fellow with Optive. So, I get to do a lot of things around thought leadership, whatever that means in the industry. Um I am a uh well let me just go further a little bit. I am a co-author of a book called zero trust security um in an enterprise guide. So I've been this a little bit for a little bit of time. Um the the goal today really is to give
you an agnostic understanding of zero trust to hopefully as practitioners walk away from this and have a clear very precise understanding because I'll just say this I when I wrote my book we wrote a paragraph and a half to describe zero trust right and it's why because we had to fill pages, right? You have to fill pages when you're writing a book. So, we write a paragraph and a half just to define zero trust. Well, I'm going to tell you what zero trust is in three words. Just be very clear. Um, I'm going to talk about that. I'm going to talk about a journey. I'm going to talk about um uh uh what it looks like
and how to do zero trust. Um I'm and hopefully give you some strategies to walk away with. And then more importantly, what I find uh when I have this conversation is if if you take away the notion that I have very specific solutions, you being the practitioners, very specific solutions in my environment that can lead down the path of zero trust and you and you hear that and you're like, "Yeah, I get that." Then you're like, "Yeah, this the the the vendor conversations, those are great. Vendors talk about zero trust. They talk about it from their product which is fantastic. They do that. They do it very well. Um but if you look at it from a what do I have, where do I go
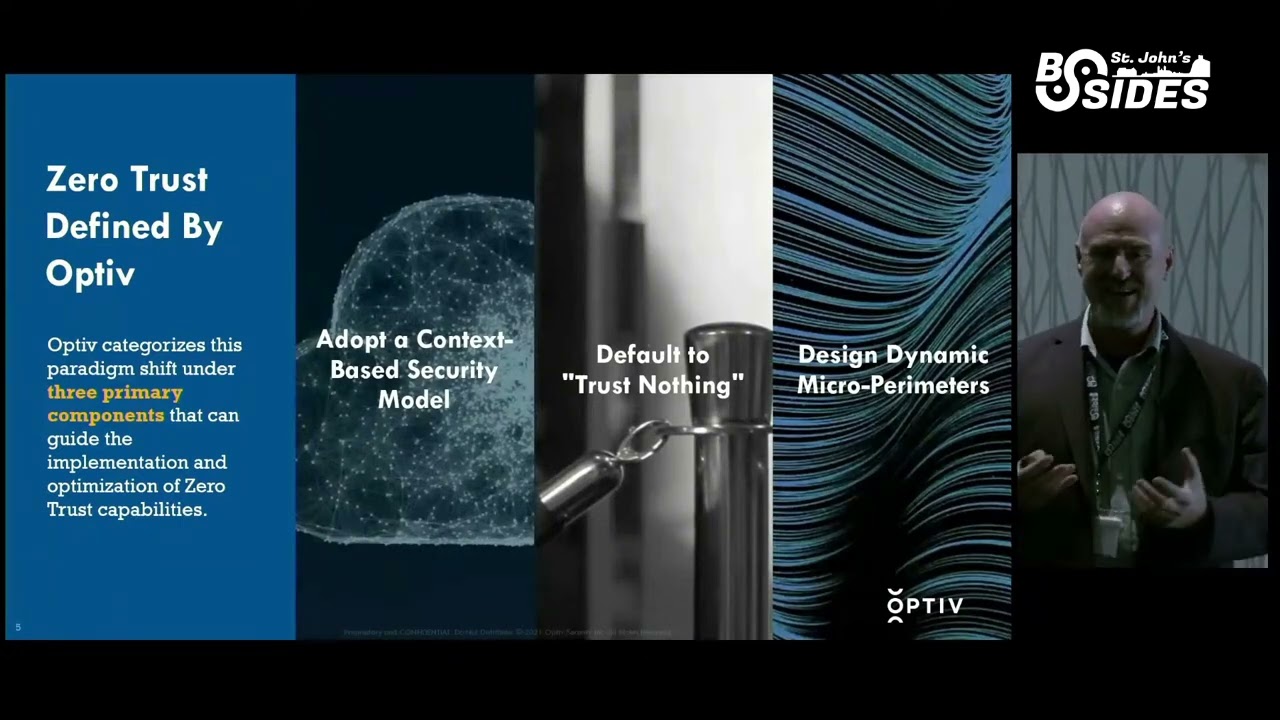
and how do I move forward? And then most importantly because about to say I'm an identity guy. I've been an identity guy for well over 20 years. I talk about identity all the time. We're going to lead security with identity. That's that's what I talk about. How do we lead security with identity? Right. So let's let's kind of get into this a little bit. So if I start to talk about zero trust, first off, I use my own USB device because I don't trust devices. Let's be very clear. Um the first thing I talk about is security. So if you're talking about contextbased security, that's a bunch of marketing terms. First off, understand that zero trust is more than marketer. I
call it marketer, but it is more than marketer. And then you see something like identity based security or I'm sorry contextbased security like well that's just more marketing terms Jerry you're absolutely right. Let me add to what that actually means. You take identity you take security controls and then you take risk. You bring those three things together you've got a contextbased security model. And I don't mean the identity providers that tell you, well, we do geoloccation services for step up authentication and those types of things. Yeah, they do. They've been doing that for five years. That's not what I'm talking about. I'm talking about bringing in external telemetry to drive riskbased decisions. That's how you get the
identity security and risk model to drive contextbased security. The second thing, you've heard this trust nothing, right? That's what everyone tells you what zero trust is. That's absolutely right. But if you don't want to impact the users and and in a lot of conversations in security is what is the user experience and there's this weight and measure between user experience and and uh security, right? What I tell you and what I can show you and prove to you and we're going to talk a little bit about this is how do I make the user experience better and how do I ultimately increase my security and security controls to support a zero trust framework. So while
it is default to trust nothing ultimately it becomes a earned trust conversation. You have to earn the trust that you have and if that something changes with that trust like I don't know I'm in I have never been here by the way it's beautiful area love the country it's awesome I have never been here but when I log on to my network there's no way I should just log on and say yeah MFA that's wonderful no Jerry where are you what are you doing why are you trying to do this you've never been there that is risk that is where earn trust and if I start coming up here regularly. Now, our our client manager here at Opti is going
to try to bring me up here as much as she can. Thank you, Kelsey, by the way. That will change because if I come up more regularly, it's like, "Oh, wait. Jerry's goes to that location and he's able to support it." And then that becomes earned trust. That's what the default to trust nothing really means. The third one here, the design dynamic micro perimeters. When people read that, they say, "Jerry, you're talking about micro segmentation. I hear that all the time." No, I'm not. Micro segmentation is a part of the conversation in a microparimeter conversation. Micro segmentation um is a way to support things like micro parameters. But if I'm talking about data and if I'm talking about more than
just um uh segmenting my PII data to some network data, that's fine. I can segment my PII data to some network. But what happens when I get through that network? Because I quote unquote have access to that data. What about all the data inside of there? That segmentation does nothing for that. So there's different technology to support that. Things like data protection that includes things like data classification, data governance. That has nothing to do with micro segmentation. That's why I call it micro perimeters. Then the question is why is it dynamic? Here's the truth. You've been we've been doing the principle of lease privilege for well over 20 years. the the the the the military has been used coined the
phrase defense and depth about 20 years ago. They've been doing it for 20 plus years in the IT industry. We've been doing it well over 20 years. So, what's different about zero trust? Because we're talking about defense and depth. We're talking about uh a principle of lease privilege. Jerry, everyone has said it before. What am I saying that's different in zero trust? What I'm saying is now we can do things like just in time access. Well, we've been talking about that in theory forever and forever. But what I'm going to tell you if in the last five years, the vendors, the industry has come to an integrated model where we're now we have standards where we can
integrate our technologies and integrate our solutions to drive just in time access. And I'm going to show you an example of that here in my in my presentation in a few minutes because I think it's important for you to understand what what do I mean by just in time access. Okay, simple definition, right? I spent 10 minutes on a slide. You're like, "Yeah, that's simple, Jerry. I get it." Identity, security, and risk. That's the three words you need to remember for zero trust. And what that means is every organization has some level of maturity around zero trust. Whether it's fundamental, by the way, if you look at this slide, you see fundamental, you see things you've been doing for 20 years.
Yeah. I'm doing network security. Yeah, I'm doing identity. Yeah, I'm doing data protection. Yeah, that's great. Have you integrated your identity solution with your security solution? That's what that next level is, the integrated model. And most organizations, quite frankly, stop there. Yeah, it's great. I can take my Active Directory users and groups. I can integrate them with my nextg firewalls. And when I integrate them with my nextg firewalls, I can do things like userbased routing. So a user gets access to a network segment because they're in some active directory group. What I would challenge you is do you have a governance solution associated with that identity to determine whether they should even have access to that network through that user
group in active directory. So that's what really what that may or may not get there. they get there with some level of of maturity or some level of integration because now they're bringing in things like uh your your SIM solutions that have a UBA ingrained in them. They're bringing in things like source solutions. So now your sock analyst or your sock solution is now saying, "Oh wait, I've got an incident. It's not a false positive. Let me forward that on to something and say we have a problem. We have an incident. Let's do something about this." And more importantly, this is where I t start talking about leading security with identity. If that source solution is
notifying my identity solution, my identity solution should be able to say, "Oh, wait. This is a change. Go change what's going on. Kill the authentication. Kill the access." Whatever that means. Terminate it. And that's where an adaptive model starts to drive your zero trust program. Okay, moving on. So, I told you what it is, right? pretty simple. I've told you kind of that maturity journey kind of where you bring identity security and risk together. Let's talk about how you do it. Now, there's a whole lot on this slide, so I apologize for that from the outset, but if you haven't read the NIST 800 207, it's a great conceptual guide to tell you what zero trust is. They did
a great job at defining what is zero trust, what are PDPs, what are peps. They've got all this stuff out in it. Go look up the NIST 800 207 if you haven't seen it yet. Fantastic document. What I've done and what we have done is said listen let's make this simple because to me it needs to be simple. How do I get to zero trust? So if I look at the first box and by the way the boxes across the top they are the uh they are the steps that I'm about to walk through quickly. The bottom tells how we align to the NIST 800 207 principles. So what this means is I'm not just making this
stuff up. This is not something I said oh let's just throw some stuff out here and figure it out. No, this is stuff that aligns to what the industry is saying that are good ways to do this. So the first one is define a micro perimeter. That's easy, right? No, there's three ways to do that. There's I'm just going to go buy a VPN solution. I talk a little bit about this in a few minutes about technology and so forth, but it's I just need to protect my castle and moat with my moat, right? I'm just going to keep doing that and I'm going to add I need to do something with my VPN. Maybe I've been doing VPN for
years. Maybe I'm going to augment it. Maybe if you're talking to some of the vendors out there and they're they're fine. Replace the VPN. I personally say replace it, but that's a different conversation because it's sometimes you can't just replace your VPN solution. It's not even an option. You've invested $10 million over the last 15 years into your VPN solution. Sometimes it's not optional. So maybe that's not the path. The real path to defining a micro parameter is defining and understanding critical business systems. What may I mean that that's that's a vague term too, right? I'm trying to drill down into some of these fake v vague terms. If you have a critical business system
that drives your business and more importantly if part of that system generates I don't know 50 60 70% of your revenue in your organization guess what that's a critical business system. And if you start to understand that critical business and when I say understand that means you understand what's going in and out of that first we'll start at OSI model 3 through seven right you start to understand the network layer you you know what's going on AC up the top all the way to the application layer you can get that that's pretty easy there's solutions that'll tell you that that's that's not hard but then you get into things like the application layer security that the network stuff is
not going to give you that the DTNA solutions that are fantastic are not going to give you. You have to figure that out. You have to figure out what is the user experience in that environment. So there's a whole lot of stuff I just said there, right? Understanding the business system, understanding at the at the high level, where do you get all the way down to the the attribute level if necessary in active directory to say, oh yeah, if you have this attribute, this is what your user experience looks like. There's a lot said there. Now take zero trust out of that conversation. That drives cyber resiliency. Think of that for a second. That drives your cyber resiliency
because now you understand what's going on in the organization that is your most threat. So some of the ransomware stuff we heard earlier today. You know how to protect that stuff. You know how to get past that. So if you understand that, here's what you start doing. You start drawing circles around those components in that business system and you say, "Oh, I can create a micro perimeter here. I can create it here. I can create it here." And it's going to be different for each one of those solutions or which each one of those circles. And that's okay because what you're doing now is you're protecting the business. And what you're moving towards, and this is the hard part, what
you're moving towards is implicit deny with explicit allow. And when I say that, people say, "Oh, Jerry, you're talking about whitelisting." Yeah, I am. Why? Because we're only giving you access if you should have access. Period. End of story. Conversation over. It's hard. Yes, I know. I'll talk about governance of that in a minute. The next thing you see up there is identity. Listen, if you can't define an identity, and I don't mean just a user identity, I mean a um a machine identity, a device identity, service accounts, all of those things drive identities. IoT, MIOT, that's a lot big conversation I'm having lately is around medical IoT and I'm completely separating it from just IoT just to be clear.
OT, right? All of those things are driving identities. So if you've got a micro perimeter and you've understand the identities, what you can now do is start say well I can define who and what can get in and out of that micro perimeter. That's the point of understanding identity. This goes back to let's lead security with identity. It's my favorite catchphrase these days. Okay. So, the third one that enhanced security. Now, I'm an identity guy and I talk about MFA all the time. MFA is not perfect. It's not. Sometimes we we we spend way too much time with with pushing buttons from the authenticator apps and and people get very tired of that conversation. They're like, "Yeah,
I'm just going to push a button." Right? I heard someone else say earlier this morning education absolutely education. MFA is one of those. Another one that I talk about a lot is dynamic PKI because let's face it, you're not doing interactive loginins with service accounts and you shouldn't be. I heard that earlier today, too. Don't do that. That's just wrong. But if I can do dynamic PKI now, I'm not doing interactive login. I'm doing one-time certificate authentications. And then there's technology today that I can support this without having a huge PKI infrastructure that has a CA and I got to manage the CRL and I got to do all those things that drives my certificate management.
No, there's ways to get past that. Better ways because now we're not relying on the human condition to support it. The last one, visibility. I can create all the micropameters I want. I can define all the identities. I can have MFA, dynamic PKI, whatever I want. If I I can have all of that and in perfectly inside a little cube, a little circle, whatever I however I want to define that. But it's at the end of the day, if you don't have visibility into that micro primter, guess what? Doesn't matter. Because when that ransomware gets in there, if you can't maintain what you have, if you can't monitor the environment, and then most importantly, if you can't
respond, what's the point? You've done nothing. you've changed nothing. So visibility sorry I get very passionate about this subject fish can't tell it's a lot of fun for me so keep those four things in mind when you start thinking about zero trust how do I create a microp perimeter how do I bring identity into the conversation what does enhanced security look like and quite frankly how do I have visibility into the environment those are important that's how you do it sorry excited all right moving on so let's talk about strategies By the way, I usually can talk about these things for hours, so sometimes I just have to check myself. So, let's talk about different strategies. The
NIST 800 207 has some great strategies. They talk about uh using enhanced identity governance. Now they talk about using enhanced identity governance but the the CISA within the NIST environment they tried this and what they came back to to to the environment or to the to the industry and said is our identity governance solutions aren't ready they can't do what I'm talking about they can't do enhanced identity governance with things like you know open network protocols with with you know portal modeling the the attribute-based stuff they're saying they can't do it now I'm going to argue that point in a minutes, but they're saying they can't do it. That's Jerry's opinion. It's what it is. But that's okay. We'll talk about
that in a second. I'll I'll show you I'll give you my support for that in a second. They're also talking about micro segmentation. Listen, we're doing this forever. Micro SegWits, uh uh NextG firewalls, all the stuff that I've already talked about. They're talking about what's the other one? SDP. SDP is my favorite topic when you start talking about softwaredefined parameter or when you start talking about ZTNA because quite frankly STP is based on the simple fact that you have to have an authentication header before you do anything. If you don't have an authentication header the packet gets dropped conversation over and you don't even get a response. So you just get the response timed out message if you try to
attack an environment or or talk to an environment you get it drops. So STP is a great technology. I encourage you to look into it. If you haven't, I encourage you to to to see what it looks like in your environment potentially because it's all about that authentication header. All right. So, if that's NIST, then Jerry obviously has something to say about it. I have a lot to say about a lot of things, but we'll keep it here for now. First thing is there are two ways in my mind to drive a zero trust approach or to to to encompass a strategy. First is technologydriven. I'm going what's that? Left to right from your perspective. Right to left.
Technologydriven VPN replacement. Easy conversation. All your ZTNA vendors are talking about it. Yes, you should do it. VPN is the number one attack vector. Period. Everyone knows about it. It's not hard. That's an easy conversation. The second thing here is data governance. Data governance is an easy conversation, too. If you really start thinking about it, you should understand your data. You should know who has access to your data. You should be able to classify that data. You can get a solution in here to drive it. Good way to drive zero trust. The third one up here, again, I'm an identity guy. SSO and MFA. Absolutely. If you're not doing SSO and multifactor authentication as a means to get to zero
trust, A, you're not increasing or enhancing the user experience and B, you're not even going to touch zero trust. Because if zero trust is about authentication and authorization and getting access to something, if you don't have a mechanism to automate that process, forget it. Conversation over move towards SSO and MFA. And quite frankly, you can't do the next step beyond SSO and MFA. And this is my favorite topic, one of my favorite topics, passwordless. Why should you do passwordless? Because if I am doing passwordless, my user experience has just increased. I'm not changing my password every 90 days, 180 days, whatever it is. Microsoft says you should do it every year. I I can explain
why they say that. That's the Windows Hello environment. The NIS framework says never change the password. Just create a very long password. Never change it. So the passwordless initiative or the password list is a step into zero trust. This is again a technology focused mechanis mechanism to implement zero trust. It gives you that first step because if I can do that the user experience is great. What is as an IT person, as a security person, if the user experience is wonderful, guess what? Now the security controls I put in place is not going to negatively impact the user because now I can start stepping up authentication and they're like, "Yeah, I'm okay with this because I'm just
clicking a button." You educate them. The fatigue of hitting the authenticator, you educate and guess what? The next step is, "Oh, I get it. If I'm not making the request, I don't hit the button. period. But if I'm doing passwordless, I now understand that because it's a normal part of my day. It's a normal part of my job and I'm not changing my password every 90 days and I'm not creating uh uh long calls or long, you know, long days where it's just trying to reset my password on all my devices because all my devices have passwords all across them. This is giving me access into my environment. I hate changing my password because now I'm on
my iPhone. and I'm on the Android device and all these things just to get into the environment. It's really a headache. Should not be have should not have to do that. And it just affects my experience which means I don't want my CISO implementing anything that's going to change what I do because it's a pain right now. We're security professionals. We're it. We don't care. We're like, "Yeah, of course I'll do that." Your user community does not want that. That's the truth. So that's where I talk about the technology driven. The second thing I talk about is a policy or outcomebased. Now I I list three here, but I want to talk about just one of
them because I again I typically go way over if I talk about all three, but I want to talk about network access control. What does that mean? Policy based control about policy or outcome based in a network access control environment. Well, first that means I got to have a policy. Well Jerry, what is that? That's you're very general. Now, I know this is very general and I appreciate that because it's going to be different for a lot of people, but a policy starts with a subject. Sorry. What's a subject? An identity. Whether it's a user, whether it's a machine, whether it's IoT, OT, MIOT, uh a service account, it's an identity. It is a subject. And then what are they going to
do? What should that subject do? Whatever that is, keep in mind I'm going from implicit deny and explicit allow. So implicit I'm going to sorry implicit deny with explicit allow. We've always been implicit allow with explicit deny. Unfortunately, that's a reality because it's easier. I'm flipping that on its head. Okay, so I have an action. I also have to have to have a target. What do I doing this to? And then ultimately, what's the condition? That's the risk stuff. So, let me just give you a sample policy. CIS admin. Well, probably a few CIS admins in here. Probably a few domain admins, whatever that looks like. Generically, let's go with CIS admin. Need access to a production
environment through very specific protocols so they can do their job. And I just name a production environment, whatever that looks like for you, right? Yeah. That that's not hard. That's the easy stuff. Here's the interesting thing. The condition, quite frankly, you're not getting to that system unless there's a ticket open in my ticket ITSM system. Period. I heard earlier and and he's not wrong. Um the have a have MFA if you're an exchange admin or whatever that looks like. You should have MFA to get into that system if it's 3:00 in the morning. I argue they said no, you should not get into that in system at 3:00 in the morning on a weekend. Unless there's a ticket
open, you should not have unfettered access into that environment unless there's a reason to be in that environment. And then let's give you that reason. Go do what you have to do. And as soon as that ticket is closed, I think I have a diagram here. I'll just build it out because I'm not going to walk through it. Unless that ticket is open and then ultimately closed, and there's multiple ways to close it, you don't have access. When it's open, you get in. When it's closed, access is removed. By the way, it's not on the slide. I apologize. I I I know this every time I show show the slide. I just haven't updated it. Remove that access. Now, here's what
I want you to take out of this conversation right here. This this is one of my favorite slides and one of my favorite things to talk about. Here's why. Every organization, every person in this room sitting in this room more than likely has Active Directory. Sorry, Microsoft gave us the drugs in the 2000s and we said, "Yeah, we're going to do it. Yay." Right. Yeah. Active Directory. We And now we are here we are 22 years later. I blame Bill Gates. Bill Gates in 2004 said at the RSA conference in 2004, "We need to go passwordless." I'm like, "Really, Bill? You've got Active Directory and everyone's using it and you won't you won't let me turn it off
until 2008." Then he said smart cards and blah blah. We can I can have that conversation. But everyone has Active Directory. More than likely, high probability. I I I'd bet on that. I'd bet those odds. Let's just say that you probably have some sort of firewall system. And I would guess you have some sort of nextgen firewalls because you're protecting your environments. So you're probably running the nextG firewalls whether they're Ciscos or Palpos or or or forets or whatever they happen to be. you're probably doing that, which is fantastic. They will support userbased routing. Integrate those firewalls with your active directory environment. If you haven't done that yet, and you'll be surprised how many people haven't, do
it. That's the first step to userbased routing is the first step to this. And then we can go to PAM solutions because I'm an identity guy. I can talk about privilege access management, putting jump boxes into place, using privilege session management, all kinds of things I can talk about, but more importantly, I want to integrate those things with my ticketing system. And most importantly, I want to integrate them with my identity governance solution that does life cycle management that drives whether I should have access not just oh it's a you know it's 3 in the morning and I should do MFA. It's great. You shouldn't be able to do it unless you have this access and
the solutions you have today I guarantee you will integrate and you can do it. That's what makes me most excited because my job is to help you understand what you have, how to bring it together to do this to drive zero trust principles. Okay, you see where I am? All right, still doing good. So, I've been talking a lot about this and I and and this is a passion, right? And I talk about let's lead security with identity and I talk about well identity and zero trust. This is a huge part of the conversation, right? How do I do identity in zero trust and before I build this out because I want to build this out a little slower because I think
there's impact but what what I'm about to show you think about what I said what the NIST or the CISA said within NIST that there is no identity governance engine that can do the things that I'm talking about. I argue that point say yes you can. I can do it with the current technologies that exist today. What it takes is a mindset change or a shift, a paradigm shift, a mindset, whatever you want to call it. It's a shift in thinking in how we use identity governance engines. An identity governance engine today. And and listen, I'm just as I'm I'm the blame. I I'll take I'll take the blame. I'm an identity guy. I've been
preaching arbback and role-based access control and application security for 20 years. I've been doing that. about five years ago I said seven years ago I said wait a minute this is not the answer because it's not that is not the answer if you properly deploy an identity governance engine into your environment that engine should have its tentacles and I am being very specific with that word tentacles because it should reach into everything in your infrastructure and if it's not you need to go back and think about what you're doing. It should be helping set policy in your firewalls. It should be helping set policy in your data protection solution and your data governance solution. It be it should be setting
policy across in your applications. One of my favorite questions is what about applications or legacy applications? Listen, I know it's hard. You can externalize access control in applications if you really want to. And there's solutions today that will make it easy for you. and you bring that into the data governance engine. Now, first off, I I know everyone's probably said, "Jerry, you're talking pie in the sky, pie in the sky type stuff." No, I'm really not. I promise you I'm not. I do these things every day with customers. This is what I do. And my goal is to get them to where they're thinking about their governance engine as a policy decision point that can drive policy across my environment.
Does that mean probably across their environment in their infrastructure in their cloud environments on their on prim environments in the in the uh hybrid environments they can drive all of those things where they properly deployed identity governance engine okay so h how do we make that happen so we've got identities right Identities drive all this and again identities is everything I've already talked about I'm not going to repeat that. But more importantly now we have to bring risk into that conver identity security risk right I'm I'm right back to the same things I started with how do I bring risk well listen these identity governance engines a lot of your risk engines your sims your source uh your
data protection solutions uh UBAS casbs all of these things have analytics as part of the conversation and there's no reason you can't bring that analytics into your environment. That's risk. You want to bring them in and then you can start initiating workflow or or sorry also intell I forgot the intelligence sorry that's thread intelligence right what are the vulnerabilities what are the things we need to know about because that impacts my policy and what I need to change potentially. So if I bring in my attributes, so that's the standard identity stuff, right? I'm bringing in HR and Active Directory and all these things that define who and what I am. And I bring in risk information,
telemetry data, things like um things like and I and I hate talking about vendors, but I I just have to say this. Microsoft is probably the biggest um uh uh are the largest attacked organization in the world. They're everywhere. Everyone wants to talk attack Microsoft and because why the attackers know that you have your email system. Most of you 90% of the world is on active directory and there's and if they're on active directory which means they were probably on exchange which means they probably migrated into the cloud. Now I'm playing percentages. Again these are percentages. These are I'm not a gambling man but I would bet on these percentages. The telemetry data that Microsoft has you can bring into your
environment. They call it identity protection. If you don't like Microsoft I get it. You don't have to micro like Microsoft. There are other partners out there that do things like compromise credentials. So they know they've been, you know, they search the web, the dark web. They get in there and they bring in these credentials. They know what credentials have been compromised. And if it's your organization, they can say, "Oh, wait. It's these domain names. Here's the names I'm searching for. Yep, here they are. Here's the compromised credentials." And if I have those, what do I do with that? Well, I need to do something about that in my identity solution. Now, some would say, "Well,
change a password." shouldn't have to change a password. Shouldn't even be on a password. Number one, what what does that mean? Well, that means the credentials are no longer valid, right? I put those dots together. Okay? And then finally, if I'm bringing in any kind of the thread intelligence and I'm bringing them into the entity that I'm managing and in my policy, I called it a subject. I'm bringing it into the subject and all of the environments and all of the conditions that drive how I gain access. And if I do that, what that's going to do is it's going to go across my infrastructure. It's going to apply policy across my infrastructure. It's going to apply policy against my data.
It's going to apply a policy against applications layer 3 to seven and up. I usually do eight, nine, and 10 and I make that up all the time. But if you do that and you bring your engine to support that, that's where you start to get that policy decision point that the NIST 800 207 talks about that the NIST CISA group says you can't do. Yeah, I think you can. And I do this I talk to customers about this all the time. This is not Jerry making stuff up. This is stuff I work actively with customers to do. And I think it's important that if you if you go back to your organization, you talk to your
CESOs or you talk to your directors or whomever and you start thinking about, huh, we have an identity governance engine, where's it deployed? And I think you start looking at it, here's what you're going to see. You're going to say, we're protecting applications. We're doing wall-based access control. That's what you're doing. Again, that's my fault. I own that. But I'm telling you, you need to change it. Here's the other thing you need to change. Birthright privileges. Oo, I'm an identity guy and I'm saying change birthright privileges, right? That's my fault, too. I'll own that. For 15 years, I told you go do Birthright because it's easy. It makes the user experience better. Wrong conversation. Identity guys hate me
right now. By the way, they they hear me. They're like, "Jerry, you need to stop talking." I had a VP in my own organization. I was presenting to a client. He was sitting in the room. I said what I just said, and he just gave me the look. And I've known this guy for 16 years. It's like, Jerry, what the heck are you telling these people? I'm telling them what they need to know so they can effectively deploy zero trust. Period. That's what I'm doing. Now, does that mean birthrights go away? No. You've got to get a laptop. You're going to get an active directory environment or an as a Azure AD environment, Office 365. Those are things that are that's
table stakes. You should have those things. Everything else, you need to earn it. You have to earn trust. You have to request it. I have a friend of mine who travels between Atlanta to Denver all the time. And when he first took on this job, he's like, "Jerry, this is such a pain because every time I get on my computer at home, I have to log in. I have to do MFA. I have to do step up authentication. I get on the plane from Atlanta to Denver, I do the same thing. I get into Denver. I'm doing the same thing. And then I come back." And but after about two weeks of traveling, guess what? He's like, "Jerry, this is
cool. I'm not entering anything in anymore. It knows where I am. It's driving risk analytics to tell me whether I should be doing more stuff." And I just met him. I I just saw him um three weeks ago. He was in Kansas City. He's like, "Yeah, I'd do it again, Jerry. I had to go to Kansas City." Yep. That's what should happen. That should be the experience. And if we're educating our users to understand that that is the experience, guess what they get? They they start to expect that. But they also expect it to be okay when they're not doing something abnormal. So there is a a ramp up time. There is the bell curve. You kind of go
up. Yeah, it's a little bit of painful, but after about a week and a half, two weeks, it goes back down unless you start doing something abnormal. So if if ransomware gets a hold of your identity and starts elevating privileges with some of these identities, guess what's going to happen? Conversation over, stopped. It's not going anywhere. There's no elevation of identities. If they're trying to send data out to some outside source, right? They're searching the data, they're in the environment, they got the environment, they're searching that, oh, I found some data. Send it out. That's not going to happen because they're not going to get out. Okay, I think that's my last slide. No, one more. Sorry. And then I'm
done. I p I promise I'm I'm almost done. Last piece of this is, you know, I talk about identity. I talk about leading security identity. Um, and I just want to just rehighlight some of the things I talk about with identity that emphasizes zero trust or emphasizes leading security with identity. Listen, if you don't want to ever say the word zero trust, because some CESOs are like, get out of my office. If you don't, fine. Don't don't talk about it from that perspective. Say, I'm gonna lead security with identity. Huh, what does that mean? That means I'm going to build a policy engine in my identity governance solution. I'm going to figure that out. I'm going to
make that happen. That's first on my road map. Secondly, I'm going to do identity governance. I'm going to drive an identity governance program where I understand where users are, what they do, what they should have access to. I am reertifying that they actually have access and require the access that they're actually they actually have. I was in a quick story. I was in a uh an organization. The organization was divesting from the the organization that owned them for 20 years. So they were completely separating. And I went in to do some life cycle management stuff. And the guy I was working with said, "Hey, I I told him I see I need access to the parent
company's active directory environment." Nobody he said first off he said well I haven't worked as an active domain director or active domain administrator in 15 years but let me give you my credentials because they still work. I said no. Number one, I said no. Let's call them and talk to them. But but that's the point. Without an identity governance solution, you're not going to have that. Not effectively. Third thing I talk about here is SSO, MFA, modern authentication. My favorite question is, what about legacy apps? I could talk about that for hours, too. I've been on that pedestal for pedestal for since 2002, right? We talk about getting rid of the main frame. Oh, no. We're never Let's talk
about that. I've been talking about that since 2002 and what that means. And then the last one, yes, start a passwordless initiative, right? Forget, don't forget, don't worry about the password change solution. Self-service password management. Again, that's my fault. Self-service password management. We've been talking about that forever. It's the same problem. Start a passwordless initiative. And listen, I'm not telling you to do that across the entire organization. What I'm going to tell you is do that in a small proof of concept way. Let your system admins test it just to show it and then bring in the business. Bring in one or two users from the business because now if you've got the business engaged, you can do
whatever you want. Okay, that was my last slide. Um, I appreciate the time. I'm really going to enjoy my weekend here this weekend because I brought my wife up and we're going to enjoy the weekend. So, I appreciate that. Um, I'll take any questions you have uh at this point. Yes sir.
So the question is what are my key points on measuring endpoint posture? I'm going to tell you I'm not an endpoint guy. I don't have agents. I don't work with agents. I have um uh I have a team around me when I talk about zero trust if when certain things come up like hey come with me or I talk to our vendors our partners say hey you know come with me because I'm not that expert I can talk about everything and anything identity won't have a problem there but when you start talking to the the metrics and the key metrics and and more importantly some of the algorithms and that that's not Jerry's not answering that question but I will bring
a person to answer that question for you so I I don't have a better. I wish I had a better way to answer that. Well, I guess the answer is there are there are yes there the the the integration of the technologies today is incredible. And if you're not taking advantage of that, then you're just buying stop gap solutions and then you get a bunch of shelfware. Anywhere else? Yes, sir.
So what do I mean by passwordless is is the question right? So first let's just be very clear when I say passwordless what I mean is you are removing the password from the attack surface period that's the end of the conversation. So depending on your identity provider let's let's use active directory because everyone loves active directory right in active directory the only way to remove the password from the attack surface is to check the box that says smart cart. Microsoft did it in 2008. I used to go around to Microsoft sites all the time in 2008. Everyone was on a smart card. Everyone had a smart card, a little smart card with the certificates and everything they needed. Back then it
was a little harder to manage. But today there are solutions that will do that for you and make your device your smart your a private certificate authority. So now the certificate is your authentication mechanism. That's number one. Now if I add to that you get things like ph2 and and web ain and all the things that ph2 has driven to say this is what password looks like password list looks like. Sometimes that removes the password from the authentication process. Sometimes it doesn't. It really is going to depend on the uh the identity provider you use to drive how they do p how they do authentication. Does that help? Yes sir.
still sending a text message or email or something like that magic link. Yeah. Yeah. Which you know by removing the password I mean if you already have MFA as one of those things you're removing the elements. So um is I guess do you have to be careful when you're talking about password list to make sure that it's as as you described some sort of hardware thing as opposed Yeah. So you you bring up a good point and and and the question is do you have to be careful around passwordless and what does it really mean and and and what is the impact and what is the the administration and the registration and all those things that all those use
cases. The answer is yes to give you the short answer. The answer is yes. You have to be careful with that. But let me give you the little bit longer answer. If you can create a passwordless experience for the user community, what you do in the backend becomes whatever you want to do, right? Because if you fix the user experience, so now whether they are actually using a password or think they're using a password, who cares? Because if you change the experience so that they are now passwordless and they're not entering a password, they're doing MFA, step up authentication, whatever it is, then on the back end, you can do whatever you have to do and that could be moving
towards a truly passwordless experience and migrating and navigate navigating those waters. I think I'm a little over. Am I? Am I a little over? All right, any other questions before I call it a day? I appreciate your time. Thank you for having me. [Applause]





