MX has a story to tell: Hacking MX records for fun, profit and data
Show transcript [en]
Hello. Hello. Hello. >> So, I'm Dylan. I'm going to be giving a talk on Tempest and what that means um for LCD monitors because a lot of the research is not on LCDs. Um, cool. So, that's a rough breakdown of who I am a little bit more in depth. I've taught before. I've ran CTFs. I've analyzed and written ransomware, etc. Um, I've done most things on the offensive side. I don't know much about Blue. If you ask me about Blue, I will make something up. Um, these days I hack web apps, databases primarily, but I really do work all things offensive. I'm from LA. I've lived all over and now I'm in Seattle. And in my personal life, I
produce music, I travel, and I write. I'm not really big on PowerPoints, so these are mostly reference slides. Uh there's a fair bit of info. Take pictures if you want, and questions are welcome throughout, but there will be time for them. So, in a single sentence, this talk can be summed up that EM fields can transmit meaningful data and air gapping is not actually all that secure. Okay. And that's the that's the main thing here. We also want to acknowledge that Morse code is really slow and there are ways to improve this. This was a research demo, not a fullyfledged attack framework tool. So we have a couple important things to go through first if you haven't heard of
any of these. First off, air gap networks are just a network of computers. They have no inbound or outbound means of communication. So no public internet, no email, etc. Um, if they're better, then it's harder to actually connect things into them physically. And that's well, we'll get to that a little bit later. C2s are the backbone of modern ransomware and malware. Um, LCDs are, at least at the time of writing this, the market leader in desktop monitors, and that is our attack surface. Contrary to CRTs, which the entire monitor was the attack surface, in this case, we're going to be targeting specifically the HDMI and DVI ports because those are the leaky uh parts. And we're going to be working primarily
with AM radio and the intensity of the waves is modulated instead of the frequency. That's the primary difference. So, we need a very base level understanding of EM fields. It's not entirely required, but it's helpful. Essentially, um, everything creates waves. If it has electricity running through it, it will create waves that are listenable. And that goes for all devices. The waves we care about are transverse waves. And I could try and explain what they are, but I think this makes a little bit more sense if we see this animated GIF. Um, so the big takeaway here is that the red is our electricity, the blue is our magnetism, and all of that is transferring data. It carries energy and
momentum, but it does not carry mass. That's roughly what a wave is. And then according to the NSA um that bottom image is their representation of of an electromagnetic field. So let's talk about hacking just a little bit. Um modern hacking I would argue began in 1971 with freaking Kevin Mitnik kind of made it popular. It's the world's most famous hacker. Um, in 1985, this is a little bit lesser known, but a Dutch researcher drops a paper called electromagnetic radiation from video display units, an easing risk. Um, which got the attention of the international community, primarily because most governments were already aware of this and considered it far too complicated for the average person to
do. Unfortunately, he proved that it was not that difficult to do at all. Um, and that was the first unclassified paper. The NSA created Tempest as a response. Bringing that up to now, it's only fair to talk about stuckset. And I couldn't have planned the day better if I tried. Um, so yeah, air gap networks. The most famous hack on an air gap network was Iran's test Iran's centrifuges for their nuclear program. Um, and the way that we did that and actually target an air gap to network is, and this is heavily theorized, uh, that the US and Israel work together to disseminate infected USBs at conferences nearby with the hope that one of them would be plugged in.
Um, this was an incredibly comp or complicated piece of malware. If you haven't, if suckset is new to you, go look it up. It's pretty interesting. Um, but its best characteristic is that it wormed through everything and only targeted what it was going for. And that's kind of similar to what we want to do because this is a relatively noisy attack. If we go through and infect every computer that we come across and say, "Cool, transmit data." that is going to be really really obvious and I'll show you in a demo why. So to make this attack actually work we do have to think about it and there is another talk that I would rank just
about equal in difficulty. It's the barcode talk from one of the Defcons many many years ago. Essentially a guy came up with a toolkit to make fake barcodes that were programmable. It's well worth a watch. Roughly, that's the difficulty level that you're going for here. You can set this up in a week. You can be up and running, but this is not I just want to launch a tool and have my attack done for me. There is a fair amount of recon. So, the first thing that you need to figure out when you're doing this recon is how am I actually infecting this computer? Air gap systems are usually behind physical security as well. Um,
social engineering is the best way because it doesn't go back to you ideally. Um, onetime physical access is totally fine and if you get bored, you can just throw USBs at them. It worked for the US. It will probably work for you. Um, and of course some policy has changed. Um, really really secure air gap networks are going to disallow HID connections. So you do need to have an approach in mind before going through with this. Next up is the technical side of it. Not just how are we going to access it, but what do we actually need to know. So the main things that matter is what kind of monitor it is and the refresh rate. And
the refresh rate matters because we're going to be looking at frequency harmonics. you don't know exactly where you're going to find the strongest transmission. Knowing what the refresh rate is makes finding that a lot faster so you're not sitting in a bank parking lot for two hours trying to find the right frequency. Um, by the way, if you're going to sit in a bank parking lot for two hours, have a car about it. So, yeah, broken down, this is roughly the questions we need to answer to complete our full attack. Um, we need to write a program that can control leaked EM fields. So that's modulating pixels on Windows. That's really, really trivial. We need to have some kind of listening
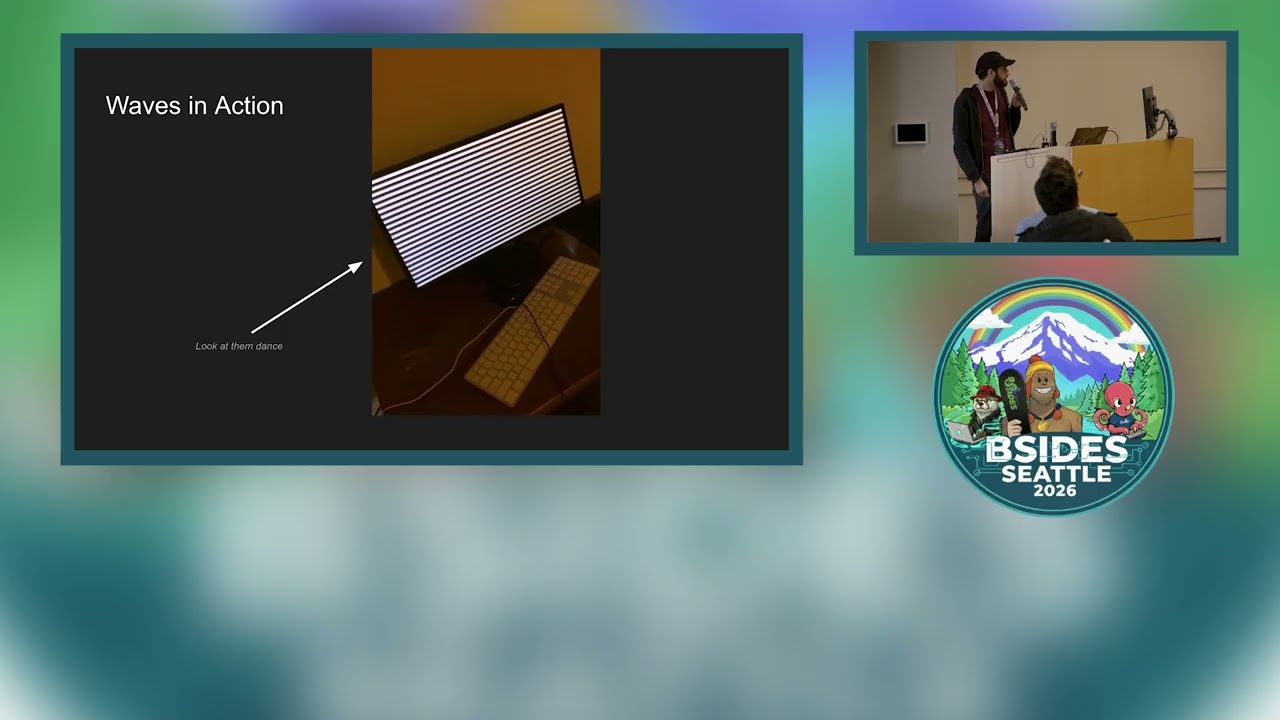
station unless you have a very, very powerful antenna andor way to broadcast and also way to dodge the FCC. Um, or we need to be close enough to listen and we need to retrieve our recordings and do the decoding. So that is also not a super trivial process but let's just assume that we have one-time physical access and can listen because otherwise this talk is not so interesting. Um here we have an active transmission of some waves. What is actually happening is we're maximizing the leakage from the field with this pattern and we are transmitting beeps that can be picked up with our receiver. This is relatively strong. We can transmit, at least from what I've
tested, through three walls, multiple mirrors, and 20 ft of building. It the transmission goes, you'll you'll get something if you're on the right source. Um, and the primary source for the EM leakage is the DVI cable connector. So, for a while it was thought that LCDs weren't really leaky in the way that CRTs are, and they're not, but they are leaky. And I want to talk about why that misconception exists. So, Marcus [ __ ] is a German researcher who's done a lot of CRT research on this topic, and his papers are excellent if you want to go deeper. A a lot of this is from him, his papers, his work. But the high frequency
Variations of light emitted by CRTs contain enough information about the video signal to reconstruct readable text under low background illumination. This is practical even with the background noise from nearby surfaces. And LCDs are not immune to this or they're not vulnerable to this because their pixels react slower than CRT. They don't essentially have a pixel gun blasting each one in a line on the screen. Max energy. um LCDs update the entire pixels in a row all at once and that makes it not so simple to separate um the individual contribution of pixels over time. So basically flat panel displays lack deflection coils that makes them low radiation devices. Unfortunately, um that doesn't really matter because
the device itself is not the only source. Um it has the data has to feed into it and out of it. And unless you have shielded cables, in this case a DVI, um that actual port is where we're going to get plenty of data. So this is what I actually did. If you want to recreate the attack, this is the gear you need. Any monitor will do. You need any softwaredefined radio. And I found the cheapest um antenna I could on Amazon. Putting all of that together, we get a proof of concept. So the proof of concept code that uh Ben Hutchinson started for Tempest testing, it's a reference to um a program called Tempest Test for Eliza or Eliza. There's
some very old YouTube videos on it where somebody makes classical music using this technique because you can actually control the pitch of the uh of the transmitted noise and we'll we'll hear that as well later. So this is what an actual captured wave looks like. So when we after we receive the data transmission from our LCD and we capture it with an antenna, this is the data we're actually analyzing. This is the decoding that's going to happen. So I know it's on the screen, but I'm just going to say it. Every vertical line is one frame. This mapping has over a million frames. This is not something that's particularly trivial to uh to decode just by hand. You need some kind
of algorithmic way to do this. And uh this actually says tasty food seven. So that's all we transmitted. All of this data, all those million frames to transmit tasty food seven. No space, no caps. This is a slow transmission vector. Our malware should be specific. If we're trying to extract passwords, we need to have the key logger and all of that looking specifically for passwords and only transmit this data. Um, and I want to talk about some of the ways that we can transmit data. So, this is a low bandwidth transmission. Um, the negative amplitude peaks are what we're really interested in. So, the negative amplitude peaks are everything below, in this case, 9,000. and we're looking at whether they are
short peaks or long peaks. We use three of them together to construct one letter. I will show the uh the mapping a little bit later. And then we use a couple filters and some clever Python to decode this. So, the hardest part about automating this is figuring out where your good filter is because you don't want to cut off your peaks, but you also need all of the data. Well, you you need all the data below zero. You don't need anything above zero. Um, the hardest thing about that is just how much data you need. Lowering the bandwidth as a general rule brings the amplitude, distance, and signal noise a little bit closer, but that also
makes filtering harder. So that makes analysis easy because you wind up with really pretty waves, but all of your data is in line with um with the noise and automated analysis is not trivial. So the second trans the second issue that that's just the analysis the bit rate is really really slow and all of that on the screen explains it but this is why we need to be picky about what we're going to transmit. There's not a great way to speed up the transmission. You can um but then your code and filter needs to be a lot tighter. One thing that I think is an interesting area to explore for this going forward is using
some kind of image analysis as AI has gotten a lot better. Visually, visually the data is not difficult to analyze even though programmatically it is difficult to analyze. Next up, finding the right frequency is tough. You really do want to know what your um refresh rate is. Knowing the monitor is really important because you can scan through a wide wide range of stuff and not find it and also not even know if you're transmitting. So, let's say you do find the right frequency um and you just came when it's not transmitting, that's the end of your attack. Um you want to test this stuff beforehand. So, if you're actually out on an engagement, you should probably
know what monitors they have before you even get there, and you should have one in your bedroom already configured with this type of attack. Okay, let me see if I can get a demo going really quick even though. Cool data. Okay, so this is what that actual waves file looks like. If you were wondering why it might be difficult to analyze um by hand or programmatically, this file is the same as this file. And this goes on well, it's frozen. That's how far it goes on. I also want to show what it looks like as we capture this and what it sounds like.
Yes. >> Maybe here.
>> Can you hear it? Oh, okay. >> No, it's not speakers. >> Oh. Uh, no. This is my output. These are the like system sounds. >> Oh, >> you're good. >> Okay. Well, that worked earlier. I'm sorry. >> All good. Here, I'll uh I'll recreate the noises. We can kind of see them. So, right now we're getting beep beep beep beep beep. Okay. So, as we broaden that, um, now it's going to sound a little bit fuzzier, but also cleaner. this kind of as you pan through a radio. It's like, right, you guys get the idea.
Um, but okay, we can see I'm panning a little bit and we can see all of those positive peaks, all those really tall lines, those are our harmonics. We want to find one and really narrow in on it. um that's where you're going to get the best capture and that's why I'm nerding out about low bandwidth captures, high bandwidth, and how to analyze the data after the fact. Um if anyone plans to do this, feel free to talk to me in the hallway. I'll show you a little bit more. Okay, so this is the code I wrote. Um I think this is enough to convince you I'm not a software engineer. I I hack for a living. But I did want to
show the mapping just so you had a an idea of how we're actually reconstructing this. Um, and yeah, there's definitely a better way to do this, but with the constraints that were given, I think this is the fast way to transmit. Um, the only real way I would update this is I would take the most frequent characters in English and move them to the shorter beep section, order it that way. But that's really being pedantic. Couple things to look at. Um, how can we make it go faster? The transmission rate is really the biggest technical challenge to overcome. The rest of it you can do with NDAs and white boxing. Um, or figure it out yourself.
But th this is the main constraint. There's also something really weird you can do with it that I want to take just a second to mention. Um, this is an instrument. So, I make music generally electronic, but my first album I recorded, all of the melodies are just this like these waves doing stuff. Feed it to an arp or a MIDI transcriber and you have almost a song. Well, electricity's idea of a song. That is most of what I wanted to get through. Um, I know I breezed through some of it, but please questions are welcome.
You mentioned a shielded HDMI cable. Did that actually block the signal and save you or how deep do I need to dig my bunker? >> If you really really want to dig the bunker, look into a red block separation and fully hardened machines. Um, one shielded cable is not enough. You need to shield the entire machine. Uh so do I understand that you're uh essentially mapping asy characters to morse code and then looking for that um after it's transmitted? >> That's exactly the attack. >> How do you um how do you uh do you do any redundancy methods? So if you don't get the correct Morse code to begin with, you have another opportunity to
get it back. And how much overhead does that create? And uh yeah, I can only imagine >> we don't do that at all. Just get it right.
>> Yeah, of course. >> Yeah, it's actually the content on the screen. Um so Whim Van proved that was possible with a regular television if you knew a broadcast code, which was a security feature. There are open source tools on GitHub that attempt to do this for generic uh monitors. It's not all that functional, but it does exist. >> So that it's not just for CRTs. >> No, it's not just for CRTs. >> The second question I had was you mentioned that only the required.
>> Yeah. Uh so this is just where our transmission range came through. Um I guess if our peaks appeared up here, then we would be analyzing the upper levels. All of this data, the vast majority of this data, in fact, up to about where my mouse is, we can cut everything above this line. We only care about the stuff down here. That is a good question. So this is a direct recording. um from cubic str. So if you tell it to capture a certain um period of time, this is the graph that comes out um after you run it through a python program, a mattplot lib library. I don't recall the exact one. >> What's the bit rate of the input uh that
cubic str? the bit rate of the input that cubic sr >> the thing that generated the graph like how many bits per second is that >> in terms of like if you were to digitize it >> uh that's a good question I don't know I haven't digitized this >> I wanted to ask where we could find your music >> um >> yeah come talk to me after the after the track >> so uh thank you I forgetting my first microphone. >> We have one minute left. Try and take a look at >> Oh, >> um uh so you you mentioned that uh the the the leakage from an LCD monitor uh like primarily you're looking at the the
leak for the the cables because the uh the like the pixels on the monitor themselves are not being like uh individually controlled. So there's like I assume there's like too much like interference that way. Can you can you cause significance leakage from an LCD monitor by just flashing the whole screen like altering black and whites and then using that as essentially one giant pixel? >> That's a really interesting question. Um, the issue with LCDs and flat panels specifically is the way that they put pixels on the screen. It's not really a matter of having enough pixels. It's a matter of having enough power. Um, CRTs literally like blast a pixel onto the screen. Like the term pixel gun is not
unfair. Um, LCDs don't really do that. They just update in a row and at lower energy. I will also be in the hallway if anyone has more questions. Thank you so much.





