Malware Bypasses Antivirus with Avast Driver #shorts
Show transcript [en]
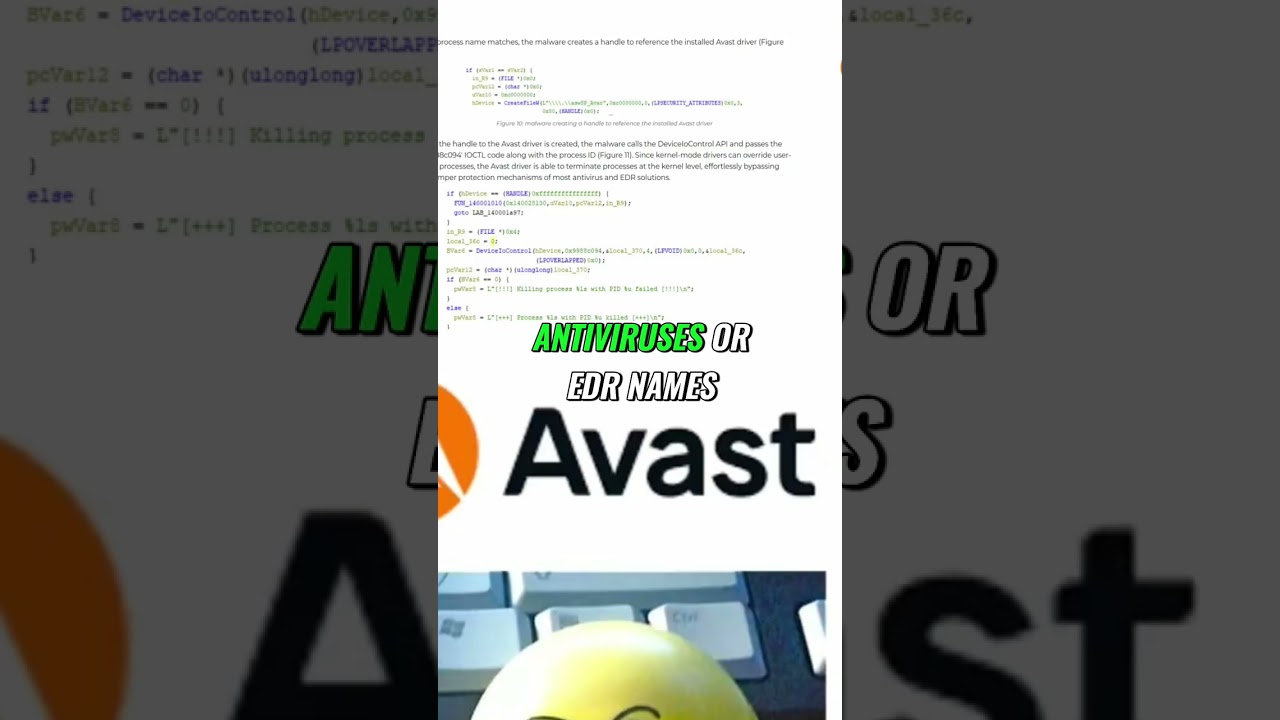
is uh the list. Here's choose a a a snippet of the list, but it the list cover all the antiviruses. So, it's going to load that and it's going to it's going to do that. And here's a a quick uh screenshot from the from the code of the of the ABS driver itself. If the process name matches, the malware creates a handle to reference this solid ABS driver. As as as you can see, that's the name. create file then create a creates a creates a handle with it and then once the handle of the bad driver is created the malware calls the dispatcher that I mentioned device IO control and then it's going to call that
IOCTL with the process ID that I already got. So first it goes through a list of uh uh uh antiviruses or edr names. So cross strike AG uh macafei all of them and then if there is a match it's going to get the P I and it's going to kill it using the driver from a busast. Yeah. All right. And this var is able to terminate the process at the kernel level for release by passing the tamper protection mechanisms of most antivirus and EDR solutions. All right, enough of





