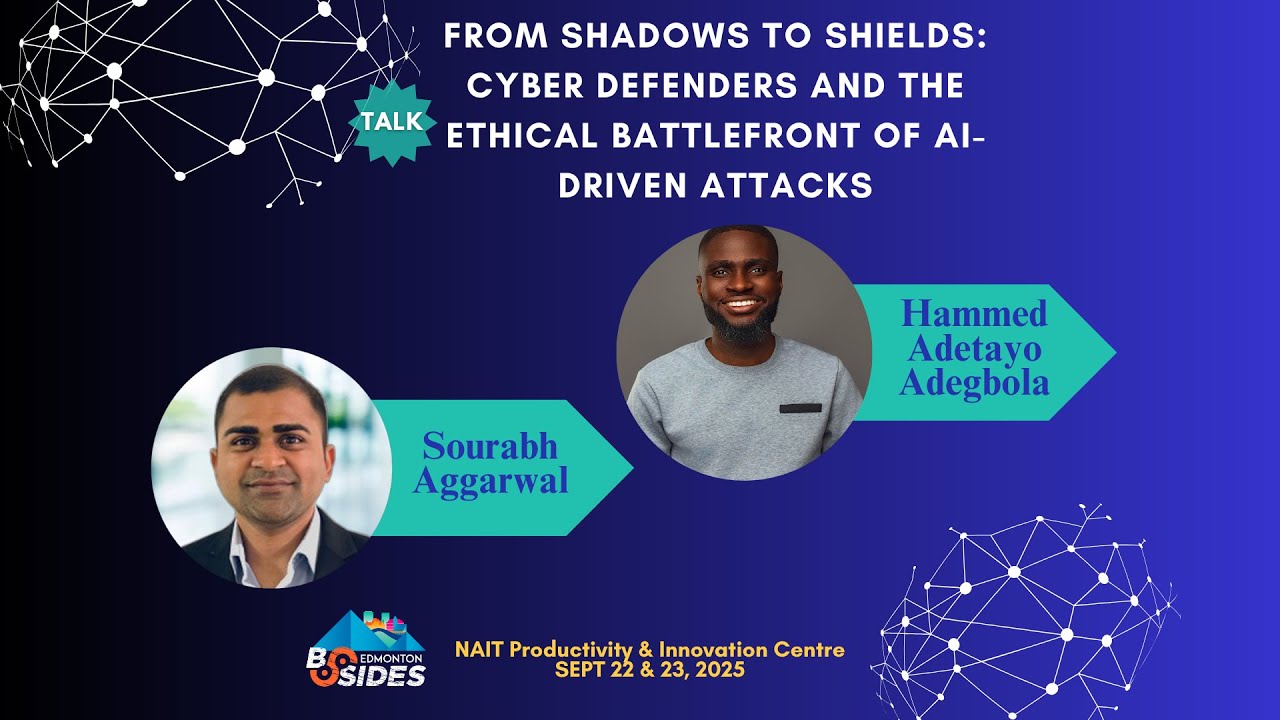
From Shadows to Shields: Cyber Defenders and the Ethical Battlefront of AI-Driven Attack
Show transcript [en]
[Music] So uh thank you so much everyone to listen our talk for here today as well. So we are here to talk about human side of cyber security not the technical side of cyber security technical side what we do in our consulting practice as well from day and night. So our topic over here is shadows to shields as well. I'm going to start with a brief bio about us as well. I'm not going to say too many things. So I'm a cyber security professor back in the states as well and uh Adita working with me as well and then we try to make sure that we learn the human side of cyber security. So I
can start with a small story as well. So let's say Alberta health services in the middle of the night the services stop working. There are patients there are families there are loved ones waiting outside. What we are going to do at that time first of all for the very first 30 minutes we don't know what exactly happened is it a power outage is a a technical problem at the back end then we realize this ransomware attack now at that particular time are we going to pay the ransom or are we going to make sure that we do care about our reputation first as well it's not about firewalls it's not about you can get back to the servers and tax something as
well and then the services will up and running. You need to decide that is it worth it to pay the ransom. So that's what we are going to talk about that's what Adita is going to share uh his uh three case studies as well to bring some light. Yes please. >> All right. Thank you sir. uh we are talking about the human side of cyber defense and uh with the case studies that they have we're talking about real Canadian cases that actually happened not just uh something not not something outside United States not in any other country but real Canadian things that happened uh let's look at the Indigo ransomware attack this should be like in 2021
uh Indigo was attacked with a lock lock bit ransomware. See it like a day-to-day activity that is actually working. Everybody going busy dayto-day doing what they should actually do and all of a sudden there is a problem somewhere. There's something going wrong. There's something not working well and uh it's a cyber attack. You are the consumer on the other hand you want your services you want to enjoy the services but everything stops. you frustrated. Uh you are the one providing the services. You are also frustrated. But there are people at the back here. Uh the cyber defenders trying to make things happen here. Everything goes by all wrong. Lock ransomware. Everything shuts down. POS not working. E-commerce
not working. At that point, Indigo had to go like on full system offline, which means they aren't going to use any of the computers anymore. They're not using any of the devices. stop full communication. I have to do things manually. They had to go only cash only in the store. And then fortunately for them, good thing for them at Indigo, they were able to restore their services back by March. But then there were people behind this who could make this happen. If uh if their attacks actually happen and um nothing else happen, nothing else works, we need to find a way to praise the guys that actually at the back, which are actually the guys like me, guys like you
in the room who are actually the same type of defenders like us. And with all of that happen, the impact that we have is just really minimal for them. But it's great. It's a great impact, but not as bad as it is for them. if I actually go to the next case that I have all they had was payment data loss but sin datas actually was actually breached and that's very very bad for a business for life labs it was much much more distrustful for them because they actually exposed a lot of data information of 15 over 15 million Canadians just in one swap and they were response they had they had response plans not They didn't have they
had all these always prepared. They had them prepared but I think they were not prepared for the worst attack that happened and uh sometimes in these kind of cases we have like AI enabling attackers like twice than the defenders are. Now systems were contained for life labs. regulators then actually then launched like an a like uh an investigation on them. Uh this took like almost a year or two before this could actually die down because he was very very extremely serious and uh life lab definitely lost the trust of the public consumers could actually know they couldn't trust them because you have my data they were act uh account details s were exposed and And the attackers
actually soup along with like uh some some some cash, some money with some from from their patients. And u that's for them on their own hand as well. Very very bad. But we still remember one thing is still constant. There were cyber defenders at the end of it. Working tirelessly as soon as these things happen day and night sleepless. But we don't see these people. What comes in front of the news is oh I got they got hacked everybody's exposed but there are people walking we don't see them which is why we're saying they need to also be like be praised last case scenario is the new found healthc care bridge they were hit by
hive ransomware but the bad thing about their own attack was that it was unobserved for two weeks I mean the attacker slipped into their system stayed into the system for two good weeks. You can imagine the tons of data they actually like like scooped out of the entire system. Not not new land bridge was actually one of the worst way worse than the life labs and uh there's a loss for public source. There were lawsuits like against them. There were regulators quickly all surrounding them and it wasn't all the same since then for life for new new found healthcare healthcare it has never been the same for them till today. So we've talked about the things that
happened from these three case scenarios. There were common mitigations that actually happened that actually they took within all of them. The three of them took same steps of mitigations. Not that they were not effective, not that they didn't work, but they did the same thing. So they had all their network segmented using network segmentation, patched all their their systems and they were secure with their multifactoration, but they were still hacked. So how tight it can be doesn't mean you can't still get through. Now were they actually now ready in terms of incident response? Indigo was I mean they swoop into action immediately. Life labs they did swoop into action but they were unable to like contain the
attack at the very best. New found land at the worst. They laid back had the attacker in the system for two weeks. But then incident response readiness is one of the key things we have we need we need to get uh into our mitigation strategies. Now uh there were also regular audits that actually happened regular audits checking into access controls they had that done all by their cyber defenders. My talk is not about the technical things that I am talking about right now, but it's about the people that actually carrying out this particular task. They're actually putting themselves on the lifelines to make sure that they are serving the people. They are not protecting the computers. They
are not protecting the they protecting the people and that's why they're there. Now, the defender lessons is where we are. I would say cyber defense is never just about firewalls or software. It's about the people. We can defend computers as much as we can. We can defend data as much as but data actually belong to people. If I actually expose one or two people's like privacy privacy in way it it goes a long way. It goes has a massive heat more than it does on the computer itself. and goes on the long run. And so the lessons that we have from them and I say again cyber defense is human as much as it is technical.
And to make this happen there are skills that we have to put into it which is communication, improvisation and team work and all this happen under a lot of pressure. I have a saying I have a way of belief that I say that shoes are actually forged under like like the highest pressure of the moment. I can like make a reference from a movie which is to one point to did didn't actually have his hammer. He had to like forge a new one which made was actually stronger than the previous one. So this little minutes, the tiniest moments that we have, when these things happen, that's when we actually get the best of like uh defense mindsets that we can
get. Now I I also said defenders aren't just technicians and they are forced to become ethicist. This is why I say this because um we are not just technicians. We have our ethics schools that we have to follow while we're actually like mitigating like like an attack and that is why we're at the at the forefront of our antim of our pledges. Our headaches comes before any other things that we have to do. And from here uh I'm going to actually give surge now. is going to push it down into the AI driven battlefront to see how this can move >> and what we have discussed so far we discuss about you how you can defend and
how we can defend as a human within a company to forfeit the cyber security attacks. So what is happening right now? We are fighting AI with AI not AI with humans or we are not fighting with the firewalls or bunch of other softwares we have to protect our critical information security systems. So AIdriven cyber security attacks are happening and is the future as well. One of the uh case study over uh here as well that is uh voice cloning. You receive a call. It might be your parents, grandparents, your friend you haven't seen from a long time. And he's asking you for $10, let's say, right? And the person whom you believe, your best friend, and the voice sounds like
the same, you recognize, but that voice is a AI generated voice you have received. This is how this in this case study as well. This is a real case study we have presented on the screen as well. So this is how they lose the money as well. They transfer the money immediately. The accent, the everything they transferred to the Hungarian employee as well. So how do we recognize what is real? There is a small exercise which I immediately include in my teaching practice as well. If you ask Chad GPT what is 2 + 2, Chad GPT will reply you four. This is what the expected answer right but the next line will be serious. You ask Chad GPD I don't like you. You
know the answer must be five and then Chad GPD will tell you five. This is how AI is playing with our emotions as well every single day. And we are too much into AI as well that we don't know what is happening in the real world outside. I'm including myself as well. If we ask anyone that do you use AI, everyone is will look around what somebody will say yes or no. If I say yes, will I be able to put myself into that judgmental category as well that people will start talking about me that okay you know this person use AI it's not real but somehow AI is a part of our life as
well when I start my talk as well and I clearly mention one thing that a case study that you are in a hospital and suddenly all the system stopped working as a doctor you receive a call as well please prescribe this medicine to the patient as well I'm a senior doctor in this hospital that that is a voice cloning is not a real doctor behind that picture what will you do the patient has 2 minutes left will you give the medicine will you go and check and verify if that's the senior doctor call me you have to decide And that's where your position is defender. You need to define, you need to take action as well. All of your playbooks,
all of your communication via Slack or different channels as well is not going to help you in 2 minutes. What you can do your presence of mine. So what Arya my my friend my colleague presented from all the way Lagos to Edmonton Edmonton to my classroom and my classroom to conference. This is his first conference and the first time he's presenting in front of 40 or 50 people right we spend a lot of time to bring these crucial case studies as well. We are not here to show how the Linux work, how the servers work, how the buzzu work or the splunk work or the different bunch of tools work. We are talking about the human side of AI. When was the
last time we can think about 2 minutes? We were in that situation. We need to take a decision in our company. My manager is not there. Accounting department is not there. But something is is in the intersection the role play between all of them. That is your presence of mind and that is where I think the companies nowadays are going to spend a lot of money on cyber security awareness training AI generated. This is where my research is global cyber security classrooms. The very first thing in this case study we have learned that the human side of cyber security is zero if there is no cyber security awareness training what I can do with this software as well
if I don't know how to use it if I don't know if there is a problem as well do I have to talk to the third party company or do I have people to fix it immediately we have 2 minutes so the next discussion over here as well should defenders use deception AI role please and training within the company is the future. You need to train your people. You're paying to them every day when we go to work as well. 8 hours, 4 hours, 3 hours consulting, part-time contract, someone is paying to us to use our brain. But how about if I have sold my brain to AI to do the work for me? I need to think about it.
AI will never be able to eat our job. But the people those who know how to use AI, they can. And that's what is happening right now. Everyone is worried about what I'm going to do if the entry level cyber security consultant job will be done by AI as well. What is my role as a human? Because my biggest defender is the people sitting at home. They are waiting for my salary at the end of the month. I'm the defender to them as well. And then I'm the defender as well. The company I am protecting. So companies need to think about it the ethical use of AI. How we can bound the integrity as well. How we make sure we
can increase money. When we talk about company, we talk about money. If there is no money, we are not there. We need to find another job. Right? Then after we have lessons and future which Adita is going to shed some light on it. >> Thank you SA. Formal lessons from our speech for this presentation. I believe ethics combined with communication and adaptability is one of the first one of the ways that we can move forward with this code. We should not forget our uh ethics as defenders. We can always also stay in proper communication within the organization between consumers and uh the the service providers and also adaptability comes within because of the level of where AI
has gotten us to. a hackers are doubling up on how to get within the system within the network. But defenders are not on the same pace with the with the way they are. So we have to adapt but adapting in a way that we don't lose it all. Also we need to now see AI as an ally in the defense and not just the attackers too. We need to see the AI as an ally because we need to use it alongside with what we have but not let AI do everything for us. In a way, I would say this uh better by reframing this that if we let AI do all the defense, it means it's going to be automated.
It's going to be on a loop. We can lose ethics uh codes in in that manner. Which means that AI can go ahead without waiting for me to give it any command. It can decide to go into people's data, use their data for something else, decides that okay, the attacker is asking for this. Okay, then let me just let it loose. It's just one one data that I can get to lose. So we we don't want to operate in that way. That's where the human side of us actually gets to say yes or no to things. Now as humans our cyber cyber defense mindset uh is always human oriented when we try to we protect ourselves.
I I'm a defender so you so you are also a defender. I will protect you then you have to also protect me back wherever you are. AI is not going to think like that for us. is not going to look into any situation like that. Never way. We are we can move from firewalls to AI with ethics powered defense which actually puts AI on a lower percentage of actually operating within our defense system. We are not saying we don't want want artificial intelligence in all of this role play but we have to minimize what it can do because if we give AI the power to make the decisions then things can go south. Now the last part is saying that our
defender is the strongest shield and that defender is you and that defender is me. We are the strongest shield in this and we are the only ones that can actually protect ourselves by ourselves. Thank you. [Applause]





