Hybrid Identity Explained: ADFS vs. Entra ID Federation #shorts
Show transcript [en]
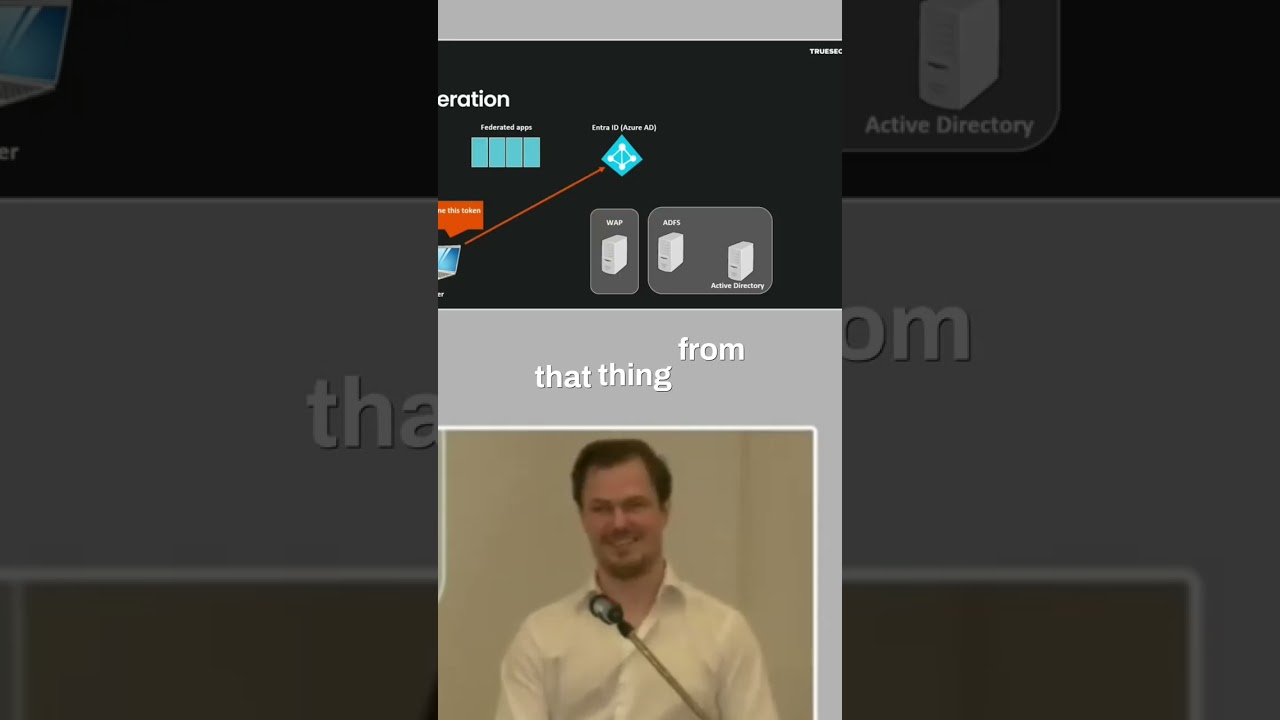
we see that the password is changed by an account called sync_something. And that points us to a hybrid setup. And there are three types of hybrid setups. And I'm going to go through them now because we kind of need to understand how they work to be able to figure out what happened here. So, we have the first one which is federation. Uh usually it's federation with ADFS, but it can be like there's many other uh solutions that you can use as well. And it works something like this. So, the user goes to a federated app and says that I want access. And it says that no, you need to go to Azure Active Directory, which I guess is called Entra
ID nowadays. They change names for things all the time. Uh and I guess while it still says Azure AD in documentations and some like XE X files and stuff are named that still. I'm still also going to mix it up uh if they can't keep the one name. But anyways, um yes, they need to go to Entra ID. And Entra ID uh says that no, you need to go to ADFS. So, you go to ADFS and ADFS checks with Active Directory. And uh if the credential is valid, then the ADFS server will sign it with their uh secret. And then you have that secret well which is well like you have the package which is signed. So, you can go
to ADFS to uh sorry, to Entra ID with that thing from ADFS. And they will give you then an application-specific token, which you can then present finally to the federated app. And finally, you're in. So, that's the flow. And what we saw there was this chain of trust, right? So, the federated app trusts Azure AD and Azure AD trusts ADFS and ADFS trusts Active Directory. So, what could possibly go wrong here? If you think of a compromised company, well, one way, which we saw in like the SolarWinds attack for example, was that if the ADFS server is compromised, you don't need to be domain admin. You just need to be local admin on the ADFS
server. Then you can dump the token signing certificate and the related private keys and secrets. And with that, you can just sign your own uh tokens. Which means that yeah, it's not a bad good situation, right? Because then you sort of just fly your way into whatever you want to fly into because yeah, you sign your own tokens as a threat actor. But this is not what we saw in this specific attack, right? We saw a password reset. That's what we're looking for. This would not be a password reset. It would just be someone who's magically authenticated.





