Cloud Persistence: Unmasking Hybrid Setup Attack Techniques #shorts
Show transcript [en]
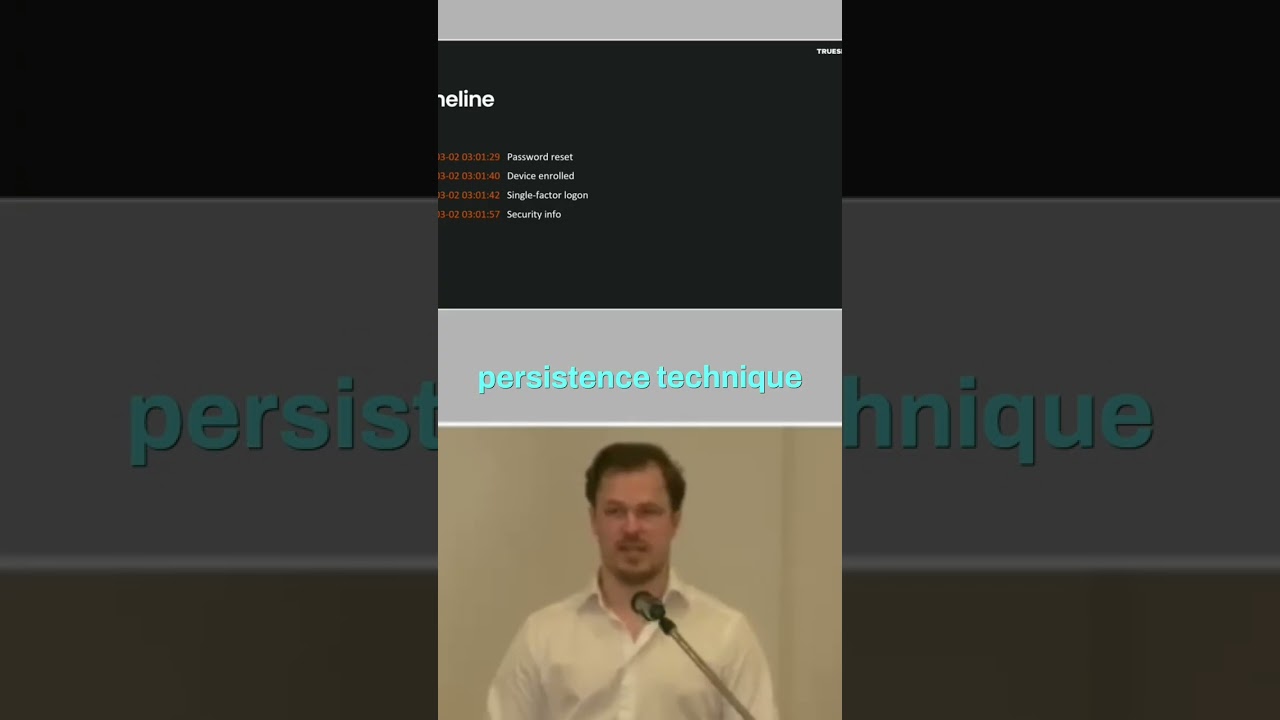
We don't really see any alerts aside from one alert which doesn't seem relevant and so on. We see that the customer have changed password for the user, so I guess case closed, right? Uh the enforced MFA and then reinstall the PC just to be thorough, so I guess everything is good, right? Of course not. Uh the thing that we forgot to add here, which is what me I work as a forensic consultant, so I do forensic investigations. What I like the most is timestamps. So, if we add timestamps to those events that we saw, it's another story because we see that it starts with a password reset and then a device is enrolled and after that you have a single factor log
on. So, that's a completely different story, right? So, obviously it's not the customer resetting that password and we also say security info here, which we didn't really cover with a print screen, but that is a I think under appreciated persistence technique in the cloud, which is, you know, you have this self-service password reset functionality and usually you have to have like different factors to do that and it can be like an alternative email, a phone number and so on. Um for persistence, the threat actor can update that and when they want to get back into the account, maybe the investigator forgot to see that those are updated, so they still have control over the account, right? Because they
can just reset the password. So, let's look into that password reset because that's the first event that we know of right now, right? And we see that the password is changed by an account called sync_something and that points us to a hybrid setup and there are three types of hybrid setups and I'm going to go through them now because we kind of need to understand how they work to be able to figure out what happened here.





