Chris Sanders - Using Honeypots for Network Security Monitoring

Show transcript [en]
good morning bides austa that was you do better good morning beid Augusta there you well done well done welcome to track two I got you so if you haven't already caught on to the uh The Motif here all of our tracks are James Brown song since James Brown lived in Augusta right we are the home of the Godfather of Soul so we're trying to picture you uh by naming our tracks and this is track to I got you so uh for those of you who don't know me I'm dou burs uh I do this little software project called Security on you may have heard it um any the security on con yesterday a few people did you have fun
pretty cool has anybody seen our lter table out there with L arcade did you did you play the arcade you got to okay before the day is out you got to get over there and play some okay so you have some giveway as well so and not just Solutions but we have lots of great sponsors uh so go and make sure that you stop by those vendor tables say hello um maybe even take a business card or something like that uh but let them know that you're thankful for those sponsoring besid guys are sponsor very important uh we do want to say a big thank you to Augusta University for providing these amazing facilities uh so up for Augusta
[Applause] University and lots and lots of other big sponsors so again make sure you stop by those V tables and say Hello uh so our first talk this morning uh is a very good friend of mine uh Mr Chris Sanders uh and you know last year at the security conference which is held about this time of year uh I had to rise sing Happy Birthday to because tomorrow right tomorrow is his birthday now he's specifically requested that we don't sing happy birthday to him but I'm not going to ask you to and and Chris wipes the sweat off his face but make sure that you say happy birthday to an individ so after the talk
you see throughout the day go give him a big old be hug and tell I'm keeping all these giveaways now by the way you're welcome uh so thanks Chris Sanders uh great guy very smart guy wrote several books with more books on the way uh and also does this great thing called the world technology fund which is also a sponsor of the sizea so thank you very much for that uh so ladies and Gentlemen please join me welcoming Mr Chris Sanders I also want to say a big thanks to Doug here I feel like every year only has the get to announce me and as
well now I got to say I'm really CH to be here I love my native georan so those you from not live in Georgia now socome to those from here and I got to say it's going to be something like
[Applause] but so uh I own the early morning talk um so we've got some stuff to give away here so I'm going to go and give something away uh early but since I think it was Happ you might still be a little bit of sleep and that's fine because coffee and whatnot uh so I've got this uh this tap here to give away graciously Don [Music] by I see want have first person tell me what year securitying was
officially I you uh [Music] 2009
answer is 2009 all right so I'm here today to talk about honey Poots uh if I were to subtitle this talk probably be called Chris gular so which I question we'll time talking myself called the technology fund we operate in Rural and low income areas donate scholarships to students puring class degrees donate lab equipment to classrooms so they expose students to information security at a much younger age so all thing the thing I'm most proud about along with that I wrot a couple books you're interested in the topic this talk monitoring has some things I also enjoy um so all the proceed all the world go toy so talk we have an agenda but I
really want to try to tell a story and today's talk is going to be to in the week techn too deep really the story I want try to tell in this talk is all about honey and why I think honey aren't used enough in the way I think they provide the most value particularly in terms of of placing inside the network for detection purpose now how many show have ever deployed a hone up now how many of you have deployed those inside your aew so that's we're talk a little bit about today frame that through the L of security ecomics there the only SL it's important here cover here to put a little College West
Kentucky muray State University the racers and I a really great Professor there I didn't a lot of told me said understand the world nature master physics understand man Master economics I didn't Master either one of them but I do know back in a realiz we're in a state in information security where we have a supply and demand in Balance the first rule first thing learn about economics supply and demand and we have a state where we have extremely low supply of expertise security Pacers and great demand for them and what that does is it more or less drives up the cost of everything security products Services you drives up theost and it makes it to where security is
affable folks with huge budg right compies or like that your little guys are really to fight game and as long as it's cheaper for attackers to be attacking we're going to have so I've got a few the little takeaways you're the little honey pot images here I want to say that I think it's not good enough for security to be good has being affordable to purchase operate and maintain that's security thing right there's a lot of technal innovation that happens that never sees a lot of not cost effective we've had people building electric cars for a really really long time they're just now coming into main can actually theage consumer we're getting we got space many many years we're just
now getting to the part now getting to a time where space travel has been brought down actually start so that's pretty NE now this is a slide lot people angry uh so NM is no different terc problem we Face we have a lot of different solutions out there for NSM so talk talk about the collection connection analysis of security events uh secure so techologies this grid up here I call this the grid of cost Effectiveness not so as you can see we have different squares here and we have Effectiveness it's part of the right more effective all the way to the left it's not very effective you have cost it's down low is not very costly it's up high is very
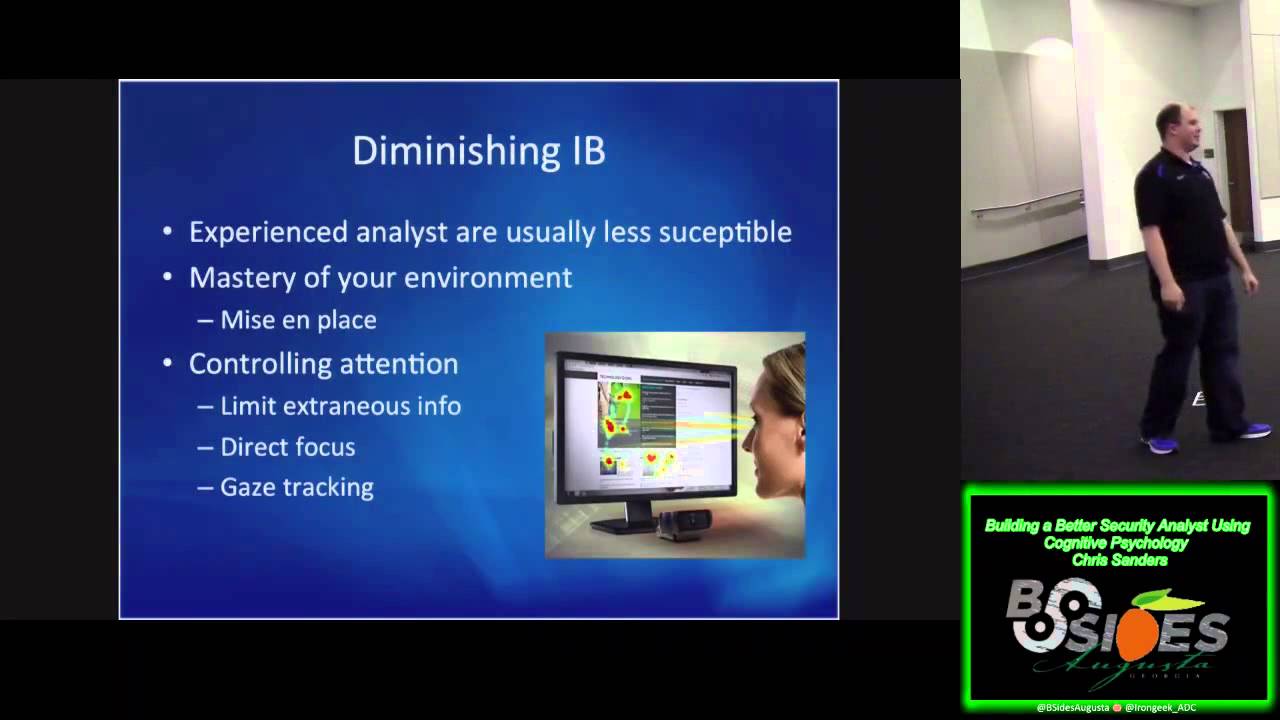
costly IDE worst scenario techologies out there so I said myself I said s where would you of the techologies out there now with the Assumption you're taking the time investing in them everything you need to make as effective as they probably can be place things this is just me um from friends and colle this is kind I things out there today how have things that exist in GRE Bo that's why that's most right and keep mind this is just the cost of software this is the cost of the expertise software so like out there people so down here it doesn't cost a lot but it's not near as effective certainly as it used to be um anal machine learning
is very kind of a new space has yet really itself out a square um I IPS can be kind of costly and effess kind VAR a whole lot so not a lot of in the SP now this probably beer at this point but I think any honey properly um can be le SL green you're approaching the right way right way we'll talk about that more Sol the economic challenges we face um with doing the detection now
around for years something ridiculous like that lot work on it have organizations acers read books here famous work here things all good stuff here project you're familiar with devel still comes out of that stuff people SU right now Hy was probably one of the big first really prolic huny software can deploy on your network now tradition very simple concept usually a piece of software or an operating system designed to be attack vulnerable and Prim used for specific research purposes a lot more of those research purposes existed um back in the day where we really like Sting worms things like thatall you see want tax it and you kind of use that engage how worms are across the network um so B were
short tra architecture really mostly look like this right so we have your internal Network outside it fly on the internet and ta tax that that's generally what traditional like I think one of the biggest problems with people thinking about a grasp too closely to the traditional notion of Hy High interaction things Etc so a lot of uh you know put some tweets out there leading this talk recently and you just need to rep this doesn't make sense all this bad stuff and so I got a few different um things that hand that right and these are to some what I call take a lot of time to maintain risk asor and four is are only for the most
secur organizations believe some of these very number four iot I said unless you are at the pinle of security you should not in my op sham on that as I'm to do more this myself and see others do it with great success not to say that you think you should but you don't have to be um working fora forar organizations or for able to do this successfully so to do again I leave behind your traditional concept what is and let's try knowledge what we think to be given the so abouty now system on your network it Serv no act purpose sobody is now right but system be who l in the wrong place something want to know about so talk about service
speciic honey a lot ofi in nobody ever Hy So to that I've already alluded to this place inside the network the goal is to mimic existing systems so if you have a bu of SE servers you have r almost always going to be low interaction honey BS they are not operating systems they're not fully blown in installations of various different tools and services they are uh software designed to look like them and one of the things here is well as as I something isn't that thing to figure out what it is [Music] and
and of course extensive Ander are going to be that so if you're say anytime somebody PES know that security theas uh so so that's basically what we talk about we talk about uh honey and the big number Hy put out there what you in Honey po you have something you're trying to specifically protect RK in your environment and I talking about risk is fun sexy but when you're do detection and collection planning risk is really framework you're going to use to decide where you're placing really heat those techologies especially Hy you knowy makes my my living with web servers databases and they're down for Millions dos [Music]
r that bridge my wife on count dri Georgia South atanta um yeah what say is they running into this bridge a little lower are so how can we how can we protect against this and came through that same um so the big here goed strategy should be integ component of your strategy and talking about what what are the threats I'm concerned about where's the risk lot what do I need to collect have visibility of those things and what speciic I need to detect from the data that I'm collecting now I can get through any talking about food thing I have so I like think about good strategy like a really really good cheap and making this is like a this is
like a not picture you think you know every a little different you have perf you have really nice
patties cheese lettuce sa sauce all that stuff lot bad ways to build a Cher you want to do this your strategy is really Cher and really compon that EXA place you don't put the Tomato on the bbody the same way you got it put in the right place the right way or else ruin everything else want you know what happens when you don't you don't belong [Applause] together
applications [Music] Doles of that so H in a lot of ways is essentially a deceptive tactic right we want attack system that not necessarily which may sound probably years with it now any human Network detction scenario there three categories into in terms of what I'm when right those are systems data and users most gener fall those I think focus exiv on systems and systems and um that's just generally how we uh how we bucke tize those things um we also forget about the data and the users which um I think are of equal importance now the process iay is generally so so first is is reality we have a system that example earlier that was your your
web servers and your servers res resarch organization it's your windows servers that all your resar on file something like that um maybe it's trand production systems that hold like credit card information and so on SS right so those systems such that from the outside to someone who already has access on your network and St H around whatever they look like system so after compromised workstation on your network and I stand around those things and I see this array of SSH ssh and there's of them ideally they all same I don't know that one of now at this point scn I don't SC on I don't know nowal SC process
[Music] theity first
that so reality taking a system making honey pot that looks like that system using software next part is interaction have to look the part some level of interaction um in some someone SC it so you get a from somewhere that's that's it's not enough to just say that they connected here we can say they connected here and they use this username that's helpful too there and they connect and use leg toy
in more interaction you cly better but this is under the of a low interaction model that you're not using actual operating system so your Se Hun is not actually a window server running SQL Server because we don't the realm of being leg [Music] compromised so we're C that interaction and we're generating some of these tools will do that for you um they gener some typ of alert in a database or some ofis message or something send whatever uher console you have other with something so you have SSH example and take to it maybe somewhere else whatever detecting that it doesn't really matter but functionality even if it's not okay that functionality elsewhere Cally pH go so look at a couple examples here
we'll start with systems um that's generally easi so in this case we we have window syst running R and that's all Serv all this so window system make person connecting to the r look like Windows now there's a lot of different tool do that I about tools a lot here I'm going to give a big page list tools this share slid every have that we play Hy
Hy minutes they commercial which is is pretty nice um and Bas those things look like RP system scanning [Music] them so that's reality there in this case both of these tools will actually
set service somebody so that's probably one of the more simple examples of how to use honey pots uh to uh generate detection [Music] systems this is often forgotten really most of business are Data Systems um most of our companies for that matter are in the business of creating data on the indry in uh we also research company we're actually um to protect the data let's say we have of HR data and spreadsheets that's Prett General thing that
syet that's where we are so this casy honey also know honey token essentially a document is sitting amongst all the other documents got really name like your social security numbers here payroll dat employee data something that get in there start here Packers open
stra you do which home way to do that was essenti like like reference back server so you're Ling that point access so if they pull back to the network they open it hackers have that offset which is is very us um and that conect back ability to see where that's coming from and just nature using file access monitoring so just someone accessing that file that doing anything to it raming it um deleting it whatever notifications for that so that's that's another way of course generating different way that's for taking it out to me this is one of the simplest things anyone can do right now to start using honey po it's not speak this is the thing you can do
Services I think they come ear they also onl service you go create for you that way we talk
about users we think users credentials access most of the time um so there was a greatech came outk
onot cral
so can generate user accounts that are more user accounts withs who don't have access to anything that are all your points and some uh there of their credentials you look for that called Secor tool and we see that you some on that creative soltions looking forward get set up um that point you're taking us looking for those cred to be done not really is a honey user so to speak giv you that ability toate so uh we'll get close to uh to wrapping up here um decently okay on top um called the action so really my goal here I didn't get too deep in the we this is what I was trying to do here
there more deep myths use I personally use these seeing these in action they be very very effective as an analy I'm a lot anal at this point you know ratio is not a fun job not job overloads way you a lot of AC work was really to and as an analyst analy that's kind my time investigating things that matter things that don't so this is the part where I brought over later so in this case I a Believer now this years ago that your innoc is complete you're not Levering hone uh hone infrastructure for detection in some way or another again doesn't mean you start there doesn't mean that has to be the Super Elite of what you're doing
everybody usey some way examp ideas how you do that the uh effective and provid better in so challenges and I think I have challenges here for everyone if you're an in the room start looking for implementation opportunities one of the biggest things that's going to drive accept of more people tell other people to have successful that's why here todayful this eom problem now that all change wherever it comes from so uh managers even you're not technical uh ensure that your animals are aware of the technique and embrace don't get afraid I've had a long career asking people
Tooney you know it's very interesting when you go from from my military work to commercial work I a lot of time working for the Army when I was working for the Army contractor I said uh I went to when I was working for contract I saidy they were little like all right you can deploy them you can't call Honey anywhere I honey okay that's something a more AC of that people looking for solution well some managers ensure vendors I work for a vendor I told this time you looking way to developable Solutions people are already doing this right iot the chapter on honey I them honey called do only do I doing but there there coming out there
bu solutions that a lot of them are prob very sheet like hot yourwork somewhere with really configuration it's like a 5 minute set of thing you got your making reality your interaction alerts all in one and that's super cool super accessible and for a lot of people about open source have open sources here open organizations cultur not they need solutions to drive that Innovation the NASCAR innovation mod Drive NASCARs all the cars you drive are in safety because the NASCAR teams buod share out for use by rest right so the same thing things thaty will spread open source will clean on to more solutions and drive Innovation up to all us to drive that ination
Source that's pretty important so I add some software recommendations here um just just a few things that I use personally really [Music] enjoy fusy some own some notar there most of this youly on security open sourcing and you don't have waste time there for you few minutes this one of things we deploy a whole lot of honey all over the network um man you configuration management is a real problem good work very dead people learn lot from them work dead those fors you learn a lot doing these things things like and oper all that so makes lot a lot easier um and really good ide to um a lot of other stuff out there not
all these um there's a really good list there um this GI of
themed popular here SL but there's a lot of different options if you want to get started withy all interaction Purpose Driven stuff um that's pretty much it
question invting we it's fascinating you go into that um
ccces like your regular work computer put a web in it's opened on this machine anywhere else work pretty well [Music] I a pretty simple one hly theol
aot Jason Smith nice words question you're you have a pretty large interest in like anal psychology and things like that and you work with a lot of pretty mature people as far as that industry so a lot of them will accept the answers that okay you know we can get over you know the old hat kind of ideas that not safe and things like this they can safely set them up but they still kind of fight back follow like whole Twitter that kind of happened when when people still arguing that you're never mature enough to even consider honey pots you have other things to worry about why do you think from a psychology point of view these people never like they
don't really have the full reasoning out there so you had reason um well first of all
question so I'm not psychologist PhD Psychology in the middle of that
[Music] the mind what it expects to see and that kind across everything we do so mindsets very quick to form but very resistant to change so many especially know formed you heard know that story by people Point incorrectly and that things happening because of that people have healthy fear say probably healthy fear like but at the end of the day talk interaction stuff it's UL just software and we all know how to deploy software on our networks may all we should know how toy software networ keep maintain keep secure and software is no different than any other sofware interaction does some things with it some things out right this do make special like it those on your own think it's a matter
pry notion abouts um mindset being quick form to resistance change people seeing and hearing and Hing things as they would expect to inter them that answer the question yes hey Chris all right so Ry I was in involved in the Twitter debacle with you so yeah I'm going to crackly made a statement but word it like a question um so I appreciate I'm huge maners in general and all this is stuff that I would teach my students it's stuff that that I plan to use like to record a video for sure so I agree with everything you're saying up until the point on the it's just a bias perspective some facilities aren't well suited for it and I don't think it's a
bias perspective it's an understanding priorities so specifically working in the industrial control system space there's no way that I would ever encourage an industrial control facility doing Power electric water Etc deploying out a Honeypot in their environment so I think just for a aspect on we didn't get to have a full conversation off of Twitter Now sort of now and we have each other in person what are your thoughts on certain industries not being able to do it for safety reasons not so much cognitive reasons sure yeah that's a good question I that from Psych perspective but what I also learn psychology is that before you understand most of all the time and they to keep things
running as it is security mention fantastic talk talking about their number one goals of operations and when more are squirel ATT so you know security just really just now expen people visibility I wouldn't expect them to be brings I do think honey can be a good idea in environment with folks places but I respect the fact that there certain industries that have different priorities than what a lot of us are used to because of that they they're struggling to do some of the other things right and they got Focus
there hey Chris Brian G when it comes to how many people in the organization need to know about the Honeypot versus how many you think they need to know um have you come across the topic of opsac or operational security and had some of those barriers or perspectives maybe Asset Management folks or people that maybe aren't under they don't have that compartmentalization mindset and have you seen resistance to the idea that only three people need to know about this um I'm not sure yeah absolutely so my perspective is if you're deploying a deception platform um that we we probably don't want to put a lot of documentation out there that might proliferate around a large organization uh so that you know
that itself could be footprinted so I was just wondering if you come across that obsc Concept in this and whether you find okay yeah absolutely now yeah that's certainly the thing you don't want Hy out there you don't want every employe Tre be hidden the crowd do that now I don't think it's too much concern in the sense that the first time you have an employ AC opens and they the pretty much that they done wrong and that's kind the best feature to some degree concern with stuff again most these Cas once the attacker does anything in relation to you like you're already should be a little bit so the thought having to much isn't as much
concern hey um as far as ISC honey pots they actually do have ISC honey it's called compot and I thought was interesting that okay just want to make sure no it's it's there and they do deploy it um in the Honeypot conference I was in this this year as one of the big discussions with ISC and honeypots I thought I saw Rob there yeah I spoke there um it was about research honey Poots though not deploying them internal to the ICS environment so I don't want we can talk about it
after um I noticed up on the list there's probably a little over a half dozen commercial vendors now that are setion Market space I didn't see them up on the list and a lot of customers are clamoring for high interaction capability even though they're probably not well equipped to deal with the information they'll pull out of that what what are your thoughts on the commercial venders coming out and where they're going with technology I'm not Asar with the commercial I a lot of organizations was like think of the like I really high
bring a whole different story actual fun operating system actual function applications I know lock those things down but that point you're managing operating system you ask yourself you trust to manage an operating system your [Music] networ system interaction problem
anybody I'm not sure to talk a little bit about what is the state of thee art today and a couple of questions that were asked you know use the word deception a lot more is the terminology changing in this field to away from honey more broader app other track things do sure I me I think I think I wish loaded term that I'm also kind of against like the creation of doing so as far as sa the art um I guess on how you
whatever is very simple Findation simp IDE to solve quality with as little effort as possible soever allows you to do that what I would consider sophisticated right now um there's a lot [Music]
oface I think the Silicon Valley Bas anything that we have a lot of different
options I think um I think we're long let me do this last giveaway real quick and then we'll call it a big day and if you have other questions just grab me after the fact of this question isurity question first he it who count who was the first coach University of Kentucky no I saw there that's right [Applause]
off every ch