Crazy Sexy Hacking

Show transcript [en]
okay
so of course i'd like to welcome the uh blue keepers back into the room thanks for joining us um i'd like to thank everyone for hanging out for five hours uh you had a good time today
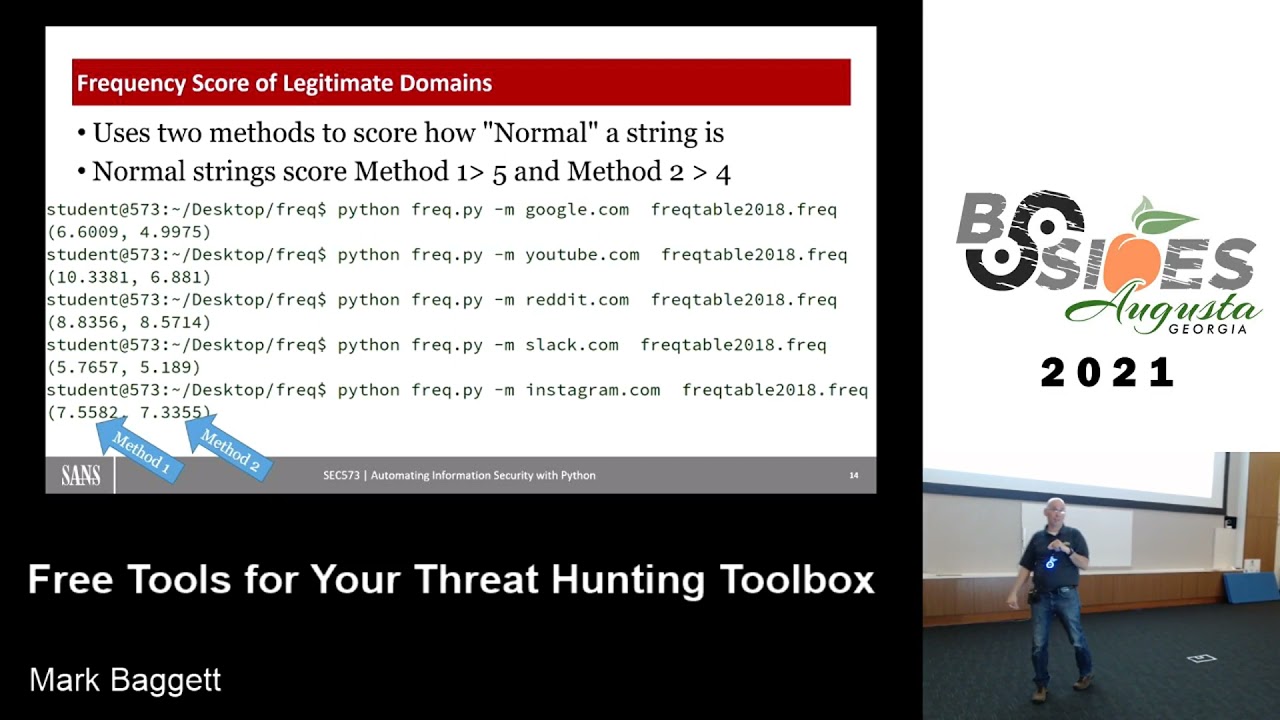
my name is my honor to uh give you the last talk of the day today uh last half of the day um it's mostly a collection of uh interesting research that that uh scares me um i'm calling this my uh my crazy uh crazy sexy hacking my career ending tin foil hat talk as you can see there when i'm doing all of my computing at home i've got my tinfoil hat on to keep the uh the nsa from reading my brain waves um you know i know that i'm within that critical distance that they can read those brainwaves so um my name is mark baggett uh it's my twitter handle i'm the owner of in-depth
defense which is a private consulting company i do penetration testing ends in response i also teach for sams i teach their offensive uh classes 504 and 560. um i also teach uh the python class i'm the course author for the python penetration testers course so um there's been a lot of great talks about python and other things if you're interested you want to learn some python lots of great opportunities for you to do that so uh if you've seen any of my stuff posted on the web it's probably been at the internet storm center or at paul.com which is now security weekly that's where most of my vlogs but i also do some vlogging on sam's pen testing
the website as well so yeah like i said this talk is a collection of kind of research techniques that have come out over the last year that that i find to be very interesting i think some of them got got some press it's not not heartbleed type um press but you know it's got some uh some press attention but it's just kind of things that just i just wonder where we can go with this uh most of this isn't complete research it's uh it's just my uh imagining where we could go with some of these research and some of the things we could do with it so why why do i call it my career ending talk
well because this is this is the first talk that i'm gonna give it's gonna publicly reveal for the first time you know that the depth of of my paranoia right exactly how paranoid am i about these things and you guys can uh look at this and you can you can let me know whether or not my fears are rational so first piece of interesting research that i wanted to talk about is this stealing private keys based upon sound do you guys see this paper when it's posted this year this was amazing so the guys that did the research uh daniel uh jenkins shamir and aaron trummer with uh you can see the url you can download this
what they discovered was that they could use a mobile device and if it was within 30 centimeters of the exhaust port of your laptop then they could use the software on a mobile device to record the sounds of your fan and the tweaks and the twerps and all the noises coming from your computer and if you were decrypting a file that they sent you they could they could derive your rsa private key from just the sounds that they had on your computer now of course the mobile device within 30 centimeters is is is the best case scenario but they've also figured out that they could do it within 4 meters if they had parabolic microphones
or if they had those laser vibrometers where they could just measure the the sound waves inside of them they could go for a much greater distance they also released a version of this where it was you go to a web page the web page turns on the microphone in your laptop and records the audio and since you're going to their webpage the web base can also deliver the file that they need you to download so you visit a webpage start decrypting the file while they're recording the audio and they can figure out your private key associated with your encryption i thought wow this is this is pretty amazing stuff but but that's not the worst but that's not the scary one right
that's it so the scary part here is yeah that's the s in rsa right so i shamir created rsa right we've been using rsa for all this time and then he comes out and says oh by the way i can decrypt your private keys using your microphone on your laptop to me this is a pretty good indication that ishmir
another piece of research that i found to be very very interesting uh is by bunny and exops right obviously their parents love them when they give that thank you but bunny benny they published this interesting research on backdooring sd memory right and so what they did is they took all these sd cards right any type of sd memory and they uh they applied acetone and things like that they opened them up and all of them have these these microchips that are built into the sd memory and you know they go and explain in their research that um sd memory is actually a very volatile um form of storage uh that when we store things in memory
that the bits inside of sd memory go bad the chip is constantly having to move memory around uh you know you might write bits to one part of sd memory one time and then when you go to read it the next time it writes it back somewhere else so they actually have these really complex algorithms that they use to read and write to sd memory and if you buy like a one gigabyte sd card there's actually probably like 10 to 20 gigabytes of memory on that thing and you're actually only using a small percentage there they're constantly moving around it they actually have to have a small operating system that is written and runs on these chips
that's on these sd cards in order to handle the complex moving around math and where does calculations they went as far as to say that when you are reading from an sd memory card that you're not actually reading your data you are reading a probabilistic representation of your data when you read from these things now where do we have sd memory cards well we've got sd memory cards in our cameras and our our phones our laptops this this is becoming the memory that we use in everything and for each of these things there's this little chip that controls everything that's being read from and written to our hard drives our phones our everything so they said hmm i wonder if we could
rewrite that operating system and do other things with that little chip so they did some experimentation with that and they were able to basically create a little hello world application that they were able to compile and get on this thing so what is this thing here yeah this is the only known compiler for uh sd card operating systems um it is up on a chinese website and so you have to go and write the operating system um in inside and see and then you can run this thing you can compile it and then you use this to load your operating system onto these things so there's there's one website and it's got chinese uh applications now if you're here you work
for the nsa and you haven't already replaced this application with uh your own then i would like some of my taxpayer dollars think about this right you're going to replace the operating system that controls everything that's read and written to the hard drives of every laptop every mobile device this is kind of scary to me so what kind of things can you do well you can't go you can only um affect what's read read from the hard drive or written to the uh hard drive you can't access the memory of the computer or anything from the operating system but who cares right that's all you need right you want to go and run an executable from the hard drive
well they can control which executables you're going to actually run they can modify those executables when you go to run those things you want to read information from the disk they're going to control what is red they presented an interesting scenario in their research which was uh so they're going to drop usbs in the parking lot at microsoft right where they modify the operating system on the usb devices to look for a specific file so if some piece of source code that's critical to microsoft's operating system like just say the the ndis driver right for network cars when that piece of source code is ever written to the usb device well it's going to modify that source code to
create a buffer overflow condition or some back door so that when you have two developers in microsoft that move that file from one machine to another they copy it onto the usb device they backdoor the usb um that piece of software as it's moving from one computer to the next and then copy it on the other computer and they inserted back doors um into the computers as they do things around them so this is this is pretty scary stuff in my opinion that you know our our um our phones our laptops we don't necessarily know right how are you going to detect this right your anti-virus software scanning your hard drive no it's going to be very difficult to
detect this so i thought about this and i thought oh my gosh is it possible is it possible that this has already been done to us right is our phone spying on us and i think just based upon anecdotal evidence that is pretty clear that our phones are secretly taking
framework as well right not going to fail right you're using that exactly yeah so joshua pitt uh created i think that's where i heard about this versus reading your tweets about joshua pitt's code case he created this awesome tool called uh back door factory right and what it does is it finds areas inside of executables that have lots of zeros right pieces of executable code that just have large sections that contain no portion of the executables just null bytes inside and he's going to write his malware inside of the legitimate executables so i mean we've been we've been putting malware inside of backdoors for a long time we've kind of been doing it this way right where we take we take an
existing back door and we append to into a new section in that executable the malicious code and then in you go back and you modify the original program so that it jumps out it executes your code at the end of it and then when your code is done it jumps back into the textual but his he's writing it actually into the original programs so there isn't a new section making it much more difficult to detect this type of activity so here you can see an example of a code block right a code cave where it's just got large sections of null bytes inside an x cube why why does our x why do our x cubes
have large section of move bytes oh jake's going to look at me he's considering well you've got page sections of memory and there's code alignment for optimization of oh yeah right jake right jake i know the truth has the convenience of being true but you know he says it's true i know the truth adolf hitler adolf hitler is writing compilers for the purposes of creating code case inside our executables so that people can place malware inside of them why else would such evil exist but it's not just those executables right there's all kinds of codecades out there you guys remember this the department of homeland security warns against people using microsoft internet explorer because of
huge security vulnerabilities now in this particular case of the security vulnerability it was a vulnerability that a foreign nation state was using to break into some department of defense computers right and uh i don't think would a foreign nation state who was bringing department of defense computers released that code publicly so that other people could use it against people in their homes but anyway uh there was this internet explorer vulnerability was a critical vulnerability and it was in dgx.dll right pgs.dll ptx.dll is a deal that's used to render vml files right bml and anybody who uh here do you do any active development in vml i do now yeah right so it's been around uh since 1988
it was replaced in 1998 by svg and so there really shouldn't be a whole lot of web pages out there that are actively using vml but internet explorer still has a dll that is still automatically loaded into memory to process bml files it's just never used right this is old functionality we have a dll large sections of code and it's just not used that is a right you're going to replace the entire function that was inside of there with your new backdoor code right and then when you want your back door to run you just have to visit a web page that has some vll vml on it right they went this is the web page it loads up the vm
vtx.dll executes the back door on your system you come in with your memory for instance you say all right i need to get a list of all the dlls that are loaded inside of internet explorer and i want to compare this infected machine to a known good system right well a known good system lowspeed bmx. dll the list of dlls are going to be exactly the same between the infected one and the non-infected one as a matter of fact if you go through and break down even further you say which apis are being called by this dll well guess what the infected version is going to have the same api calls as the legitimate version it's going to make
reverse engineering this or figuring out what you've been own is going to come down to all right not only do i have to figure out which apis are being called but you also have to actually look at the code that's being executed and see what's happening inside of that executable okay now it's there's a couple of problems right if i'm going to replace vgx.dll well microsoft typically signs those dlls so you can't just go and write stuff into the middle of the dll because that's going to be a problem right if we go and write stuff in there we're going to break that digital signature so how do we get around this well we could you could um load it into the
dll after the digital signature checks have been have occurred or we could find some way to defeat digital signatures right but that would be that would be really hard because think about it digital signatures we rely on those for everything and that's how we sign our emails that's how we sign our applications if you have executables that are digitally signed hey antivirus software says this thing's good to go right so digital signatures if we can break that that would be really really bad all right let me just do a little command prompt demonstration here so here i've got a windows directory okay first of all let's do this d-i-r-e-x-p-l-o-r-aster dot after you have two files
two files in the direct enter directory with the same file name space what's going on here i know you guys have seen this as i demonstrated in a python class i was doing recently what's going on here got a space i got a space after one of these so these aren't this isn't explore.ixe it's explored well a lot of it is explored the other is copy of putty and it's named explorer.dsc space right but it's very difficult for us as human beings to tell the difference that it looks like two explorer.exe is there right well how difficult is it for the operating system to tell the difference between the two so i'm gonna run up here a tool called
tools sync check all right sig check which checks digital signatures thank you slash sig check um e-x-p-l-o pastry.mastery all right so according to microsoft both explorer.exe and explore.exe space and you can tell the second one you can see the space before the colon there both of them are digitally signed by microsoft now i just told you explore that aac space is a copy of putting okay what's this uh i can also tell a c check to um give me dump the hashes what's the half of each of these files i should help you out okay so explorer.exe and explorer.exe space have the exact same digital signature right what's going on here well there is a vulnerability in the
operating system right that when you go to access a file that has a space at the end of it right the operating system trims the trailing space so in any application such as sync check such as insert antivirus software file integrity checking any type of software that's going to rely on digital signatures goes to open up explorer.exe space the operating system actually gives it a copy of explorer.esd okay us vulnerabilities existed for quite some time and it will continue to exist for quite some time i think i don't know this was anonymously reported to the internet storm center when i was a handler on duty about a year and a half ago and i started working with
microsoft let him know that this vulnerability exists existed i didn't talk about it publicly until about four months ago although matt grave or chris campbell because chris pamela here my favorite chris campbell um i'm good i'll talk about it now they they uh they did a blog post on this about three months after after it came onto the internet storm center so this is a vulnerability this is a bypass of digital signatures so not that we could necessarily use it in that same way but it's it is interesting that you can do that i've got one word how about bypassing it or shimmying those dlls after the executable has been uploaded let me give you a demonstration of
something that we can do to modify executables after uh it's been loaded yes sir would that defeat uh application white listing that's like built into windows via gpa um excellent question so will is the application white listing um on the built-in windows um this does not defeat app locker and so app locker uh that's but as far as i know every other um uh digital signature check based software with the exception of crowd strikes um incident response uh application and uh doug you know redline's been patched now don't ask me i don't work for that company okay i know he was working on a patch that's gonna address this for uh basically anything process hacker
process explorer anything that's checking digital signatures uh that's not app walker and crowdstrike that i know of is alarming okay thanks for the question um and you wear an extra large yeah there you go
nice uh all right so the other option is to get my stuff loaded into the executable after the security checks have already happened so let me demonstrate a way that we could possibly do that so um you guys know see if your cmd.ac if i would take cmd.exe and i um run it and uh here i'll do color f0 you can see this if i do it who am i so i have creative on this you can see that if i just run a command prompt i don't have very many privileges on my machine even though i am an administrator on my computer the privileges that i have under my account here are limited right
why well because i didn't right click on my command prompt and do run as administrator microsoft was friendly enough to strip all administrator permissions from any process you have on a machine unless you right-click and say run as an administrator this is a really good thing for us right because we didn't as security professionals we couldn't convince the executives that they didn't need administrative access to their computers so this is a really good thing but when they did it right you've got all kinds of things on the machine that need to have administrative permissions on their computer to operate and this uac prompt comes up vista comes out and everybody's like oh don't use vista because you've got these constant
pop-ups and all these other things that are constantly going up your machine so you've got this usc prompt which drove people crazy right so i'm going to click yes my uic prompt and here i do a cover of bureau so you can see it i'm going to do a who am i slash priv you see all right now i've got all these permissions that are on the system right but those pop-ups on the machines those drove people crazy you've got all kinds of computer processes on your on your machine that run as administrator but a uac prompt doesn't come up for example there's this one all right start cli config this is the uh sql uh client configuration utility
that machine there that command prompt or that box there is running as an administrator on my computer with full privileges didn't stripping its permit admin permissions but no uac prompts no uic prompt right i'll prove it in a second right but it came up no uac prompt why did that happen well if we go back to uh our see um zoom in a little bit we can see this dr cli can fix it in this directory yes it is all right i'm going to run tools save check minus m i'm going to dump the manifest file associated with cli config if we look inside the manifest file manifest file um it's got some configuration information used by microsoft has
permissions things like that i can look at this manifest bottle you can see that it's got this auto elevate is set to true see that line down there in the bottom this one's a little too short if it actually uh see it you guys see that line that line inside the manifest file tells microsoft hey uh don't do that oh uac thing when this process this particular process launches on the computer so what i really like to do is i would really like to run a different execute i'd like to have microsoft do all his security checks right look and read that manifest file that's embedded within cli config.exe and then after it's done all that stuff
redirect to a different process okay um you guys so uh besides last year i did a talk on um the application compatibility root kit i mean the application we've had early toolkit microsoft released you guys if you haven't seen that i'm not gonna i'm not gonna repeat all of that stuff but i'm gonna use the application compatibility toolkit here to create a little configuration file so here i'll go into let's see application compatibility administrator oh yes i don't know um all right i'm gonna open this one that i've already configured here's my application compatibility toolkit my patching cli config let me right click and edit this fix you can see i'm patching cli config and i don't have a compatibility mode
here's all of the ways that i can tell application bad loads we'll get the lives of this executable i'm just going to tell it to show the ones that i've got i've got redirect exe in here so i'm going to click redirect uc the parameters and in here i told this thing to redirect the execution of cli config to cmd.exe all right okay cancel let's go ahead and install this thing all right so let's see cls i'm going to do sdb install time tools slash elevate shell by running cli config okay so it says it's installed so now let's run see how i can fit exec click
okay so we've got full administration on here administrator box did i click the uic prompt no i did not click the uac prompt so what that means is it read the configuration for cli config right it applied the manifest that's associated with cli config then after those security checks had been done it redirected to command prompt i have a command prompt so it's a uac bypass yes sir uh does installing the ship required does installing the shim sdb install um require administrative images yes it does um uh from a uh from a uac prompt let's say sdb install also has auto elevate set to true within the uh within its manifest file okay so after the checks were done then
it loaded did the redirection of the executable so i imagine and i could i just say imagine uh that similar techniques could be used to load dlls and things like that after security checks have been done to actually get those code case into legitimate executables on the system okay so i did that talk with that on uh on application data bully toolkit and shortly after that i got an email from john erickson all right um anybody recognize the name john erickson yeah it's not that joke so there's getting john erickson he wrote this book and um took an email said hey my name is john erickson and uh i want to can i get a
copy of slides from your uh application toolkit i'm like of course you can you're awesome i read your book she's like i'm not the generation but as it turns out anybody named john erickson must be a complete genius because this guy what he did is he took the research that i had initially done and he went much much further and i need john erickson because he did it better than me so what he figured out he reverse engineered the uh the sdb uh process and he figured out that these sdd files have a section in them called patch bits right what patch bits is is if you guys ever seen microsoft fix ups you can download a microsoft fix up and
apply it to your machine and somehow it magically makes vulnerabilities in our computers go away how does it do that they don't replace the executables on our machine how do they do that well turns out that patch bits inside of that sdb file can modify executables in memory after they've been loaded and security checks have been done all right so what he can do is he created a patch fence bits up using a patchfit's sdb file that modified explorer.exe so that it contained explorer.exe plus additional payloads right so explore.exe which is a digitally signed portion of the operating system distributed by microsoft right you have the most secure environment the entire world you only allow explorer.exe to run
in your environment right but these apply to patch up a security sdp patch up to your system so that not only does explored aac run but it contains an additional payload that modifies the executable so he was able to modify digitally signed executables and modified executables to do whatever it was that he wanted is that interesting that's scary just keep you up at night i was i was a little worried about it right i was a little worried about it with when john initially released this information uh the more i looked into it i look obviously bigfoot is using explorer.exe to control all our minds and bigfoot lives inside the code cave as a matter of fact
i am pretty sure that all that stuff we can't find locust monster jimmy hoffa the where all of them exist inside of coke this is one of those this is one of those things that you're supposed to be able to stare at it and it's like something comes out i can never see those things right i'm sure that it has something to do with code case
i did this other thing i was playing with uh pmap when pmount is a really awesome memory forensics tool it's a driver that installs and then you can use python to interface with this driver and extract memory components and i downloaded windpmim and i've installed it on my machine and when you first run one team it says hey you now have your you have got this memory acquisition mode where you can read from memory it gives you these memory ranges and it says read memory from that location to that location that location that location don't extract your memory from these three locations and i thought what are you silly right i don't want just those
portions of my memory i want all of my memory why don't i just get those if i just get parts of my memory bless you that's not gonna be a forensically sound memory capture i have to get all of memory so me knowing more than the people who wrote my payment i started dumping all of my memory from the beginning of memory all the way to the end of memory and volatility wouldn't read it and redline wouldn't read it and none of those memory forensics utilities were smart enough to understand how to read all of my memory when i dumped all of my memory from the beginning of memory to the end of memory and i said what's up
of this and i fought with this thing for hours and then i read the name
and as it turns out there's all kinds of things that are actually into it's interfacing with the chips on our computer and actually dumping memory from beginning to end but turns out that your operating system doesn't actually use all of the memory in your computer it's just in ranges of memory inside of your computer and there's sections of your memory that don't have that don't have operating system memory right but if i read from that memory i get stuff and i was like what is this stuff right okay this has something to do with pci and isa and pci intel and i don't know right well so once again i went back and i read the
manual right and it turns out that oh yeah so we've got like shared video memory shared video memory is memory that's in your computer and the video card right takes its operating system and it writes it into your ram in your hard drive so when i was dumping all that other stuff i was dumping video memory and pci resource memory and stuff that is associated with other hardware on my computers so with a device driver i can read to and write from that memory and let's see when right so i've got my user mode applications they interface with the kernel mode applications interface with the device drivers and those device device drivers then access the memory
but that memory is shared with pci vta and other things i could potentially take malware and write it into memory and portions of right into memory that the operating system itself never sees that hardware video cards memory cards are going to see right which means it's never going to be accessed by the processor or my computer but it's going to be accessed by a processor it's going to be accessed by a cpu right that cpu is going to execute code i thought this is really interesting what's really interesting is these root kit hunters these memory forensics tools and everything else that's scanning an operating system from memory it's not going to be scanning the memory
that's associated with pci buses and things like that so i don't know anything about this right um this isn't full research here but this scares me right so i just thought i'd go out there okay so basically i look at i look at these the way that we've had stored memory out there the things that we have root kits all of the technology that we rely on um that has the potential to be compromised in very interesting ways in my opinion and i think to myself you know the internet the internet is like one of the pinnacles of human achievement it's one of the greatest things that we've ever done right the compute modern operating
systems are our laptops this is this is like really awesome stuff for our species but yet it's so horribly flawed i have to ask myself you know what um did we really put somebody on the moon i think it's pretty obvious that there's no way it actually did this all right so on a serious note right i think that there are lots of interesting things going out there i am always impressed by how far researchers in our field are pushing the lines with uh interesting things so some of the talks that we've seen today are really interesting things that have given me a lot of cool ideas that i want to go back and play with
the challenge to defend our networks is incredible it's going to be very difficult for us to do this and the more research comes out i think i i think it empowers us as we begin to understand potential flaws and ways that people can break into our networks and then we can come up with new interesting and new innovative ways that we can do this i hope that you were as inspired by some of the talks and some of the information that you saw today that you will take talks you'll go and build on them from there that we'll see lots of new research come up out of the the talks you saw today that next year
when you guys um have come up with these incredible discoveries that you'll bring them back here to augusta besides 2015 um which i i hope that we'll be doing again next year i want to take this as an opportunity to thank all you guys for for coming out here to augusta b-sides uh and uh like to thank all the speakers who took the time to come out here and just we'll see you back here next year