Cloud Attack Exposed: Threat Actor's Machine Caught! #shorts
Show transcript [en]
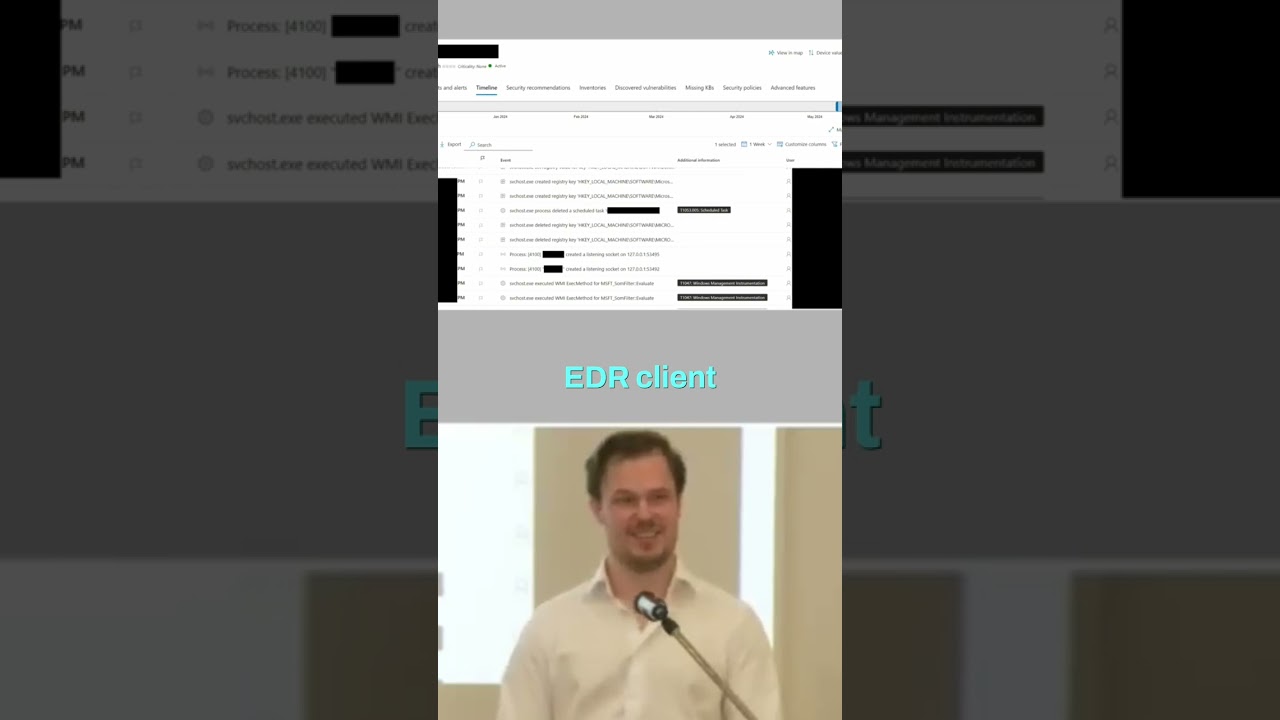
We also get a log for when that user that they just created is now in the global admins group. And I guess that's the explain some of it, but still the the device that they logged in from was enrolled in the EDR, right? It's a bit weird. And it actually turns out that the threat actor thought it would be stealthy to log on from a compliant device. So, they enroll it in Intune. What they didn't know was that the customer would then push out automatically an EDR client through the threat actor's machine. So, what we see here is actually the threat actor's machine. Uh and my my colleague Hassan has a complete talk where he just talks about
everything we can see on this threat actor's machine because it's sent to the EDR, right? And of course, they use that machine to attack multiple different uh customers. Um but yeah, uh we'll get back to that. Uh so, let's start draw like drawing that kind of graph that we saw in the beginning right of the classic on-premises attack now that we're in the cloud. So, the first thing we know is that they dumped secrets on the AD con server. They then used that to take over an enterprise application. Um they then generated credentials to be able to act as that enterprise application, made themselves global admin, enrolled a device, logged in, added some persistence, and so on. And then
finally, the seventh step here which we haven't really gone through, but that would be like, you know, syncing uh data and so on. Uh yeah, to exfiltrate high-value target data.





