Escapades in DFIR, An Incident Responder's Reflections
Show transcript [en]
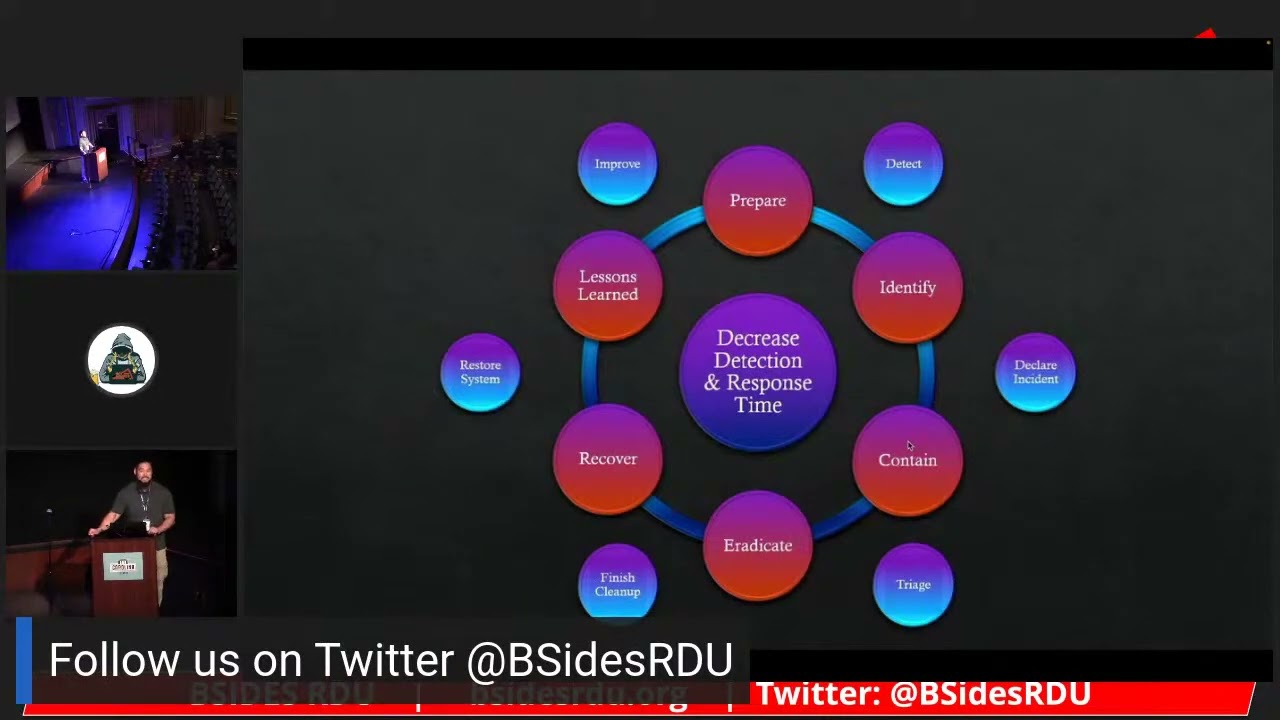
and up here 's H key mines we got an HTML Port there somewhere awesome okay so Mark I'm gonna do a quick bio here for for you so uh Mark is a US Army veteran he received his bachelor's degree from Campbell um for he's pursuing a master's degree at Sands right now and he's working as a cyber incident response manager he's constantly learning about digital forensics and incident response uh hey you also enjoy weight training obstacle courses in spending time with two dogs and I think there was something about tacos and beer that went in there as well in the original right yeah yeah you do all the training so you can eat the tacos in the beer right yes exactly so Mark uh welcome today and uh thanks for uh being our last Talk of the day it looks like thank you I wish I knew I had more you can actually right on right on so cool hi everyone um so I'd like to start by saying thank you to Patrick I don't know if you're in here right now but um Patrick helped coach me through the sole submission process of getting the the talk submitted and really provide some valuable feedback so I think that's not just a great reflection of his character but it's also a reflection of this community that we have here in Raleigh a lot of times we have people who want to get help but I think we also realize that there are so many people who want to help and I absolutely love that about this community so the talk that I want to give to you guys today um I want to highlight kind of where I came from what I do now and I do that because I want to show people that even if you don't know anything about computers you can still um you know really grow into this career field whether it's pen testing whether or not it's blue team threat hunt threat Intel you know whatever it is that you want to do there's just so many opportunities to do it here and with a supportive Community like this my faith in humanity increases a little bit every time so Chuck thanks for the bio um we talked a little bit about tacos and beer what's not written in the bio is not only do I I like to engage in the weight lifting I like to engage in the beer drinking so super excited for Pony Source guys um and just you know love to network love to meet new people um unknown fact about me I'm incredibly introverted so I'm secretly dying on the inside right now all right so I did get bachelor's degree from Campbell University go camels woo um so when I was I came to North Carolina in 2007 I was in the U.S army I was in a unit called psychological operations and basically what that is is just Nancy words for business marketing I did about eight and a half years there at the time all I knew a computer could do you could play video games and then one could download movies and put them onto external hard drives someone not me but someone uh shortly when I was transitioning out of the military I went to a school called New Horizons that was in um Durham probably real close to here actually and then it eventually became Carolina Career College and I just recently heard that it's not there anymore covid was not kind to everybody of course so I earned a couple of certifications namely a plus net plus SEC Plus once I got the SEC plus opportunities really started opening up for me especially on Fort Bragg for those of you that don't know I still live in Fayetteville so Fort Bragg's right next door and there's just a whole lot of job opportunity there so I took my first job and I decided to just go all in Let's Go full it and let's just see what happens I changed my degree plans to I.T security and so I was going to Campbell University full time Monday morning to Friday afternoon and then I was working Thursday night to Monday morning that was a pretty uh pretty uh rough six months of my life there I lost like 20 pounds and it wasn't the good weight that you want to lose so I spent about two years in a service desk Help Desk position uh fast forward a couple more years I got a couple more certifications one of them being the cissp transition to an auditing role so if all of you are familiar with secure configurations I think CIS controls I think DOD Stig controls I was auditing systems Network appliances software applications against those guidelines and then of course I was working with those system owners to either remediate them or come up with a plan and document the risk that was inherent there I then moved on to an incident handling role and that was my primary focus but because I was the only cyber security person as part of that sub organization everything came my way I did vulnerability management engineering architecture scanning all of it on managed 80 servers across the world if you're familiar with the tenable products that's what I was using there I was involved in the risk management framework I was introduced to Containers container security so I think open source tools like Encore Swift and gripe I think there's another one also called Claire so that was actually the last job that I had I was there for about three years and that's really where I got a lot of my experience where I started meeting a lot of new people and really getting a lot of perspective on the field [Music] so what do I do now um as we mentioned earlier I currently go to Sans technology Institute so all the GX certifications that's this college and I know there's at least four other of us in here I recently and there's five of us here total I got to meet um one of our other stance colleagues here we have a slack underground and he knew that we were here and so he uh Extended Stay so definitely appreciate you doing that very glad to have you here so I am also an active member of the Issa and they asked to say is another organization um to promote um the networking and the further mint of the profession so I want to give a Shameless plug here um first of many uh or warning there um so I'm the education director for Fayetteville Fort Bragg and I'm looking for speakers whatever you guys want to talk about I have all of 2023 open I'm looking for 20 to 30 speakers next year's if you want to do something Tech call something you're interested in a workshop please come find me I want to bring you on board and really get you some exposure and help to teach all the people in our community so I also like to work with open source projects and Technology because I'm in the digital forensics incident response field that's typically my area of Interest so if you guys are familiar with memory forensics I use volatility I use winp-mem for acquisition um I use Eric Zim miles and one really Major Tool which I'm going to talk about later called velociraptor um for digital forensics incident are standing to do a whole bunch of things and I've also got a side project going on if you're familiar with detection lab it comes pre-built it has Splunk uh Fleet with OS query Microsoft ATA Velociraptor domain controller and then you just start going to town with the labs and it's really pretty awesome so I kind of want to show some of the things that I do on a daily basis um I did my best to make the best memes for you guys and I'm so excited to share them I didn't like them at first but as I stared at them over a couple beers I was like nah nah these are good these are good I like them these will do so typically what we're about to see here is a Monday but it's also kind of every day so we start the day off we start you know um upgrading our privileges because we use that just in time model and then we start getting into our consoles so Microsoft Defender think silence think all these security products and we're going directly into the consoles to see hey what's waiting for us today foreign and I really love this meme because you could translate this in so many ways once we kind of get settled in and we kind of get our minds right we switch into this graphic up here which is our six phase uh incidents response life cycle um this is a pretty common life cycle and I um recommend that everyone just treat this as a framework this isn't something that absolutely has to be done and typically we'll go in a circle from prepare identify contain eradicate recover Lessons Learned and then back to prepare however there are times where you'll have to bounce back and forth between these phases and we use this as a framework to help direct our investigations so when we talk about the prepare phase we're setting up all of our detections we're using threat hunting we're using threat intelligence we're building out those good detections so that we know is there something that's evil is there something that's a false positive are we able to prevent that thing um automatically we're also looking at part of the preparation phase as are we getting the right logs do we have the right visibility do we have the right level of access to do the things that we're going to need to do the next phase is identify and a lot of people seem will think about this as all right we found evil let's declare an incident but I also submit to the group that it is not just declaring an incidence but part of the identification phase is to scope if you have one compromised endpoint we need to look at the blast radius there what other endpoints could that compromise endpoint have talked to you or a user what could they have done from the initial point of access and that is part of the identification phase typically we'll then move into contain now in a perfect world in a perfect Network and in perfect you know patched organization who here has that by the way I'm curious okay good I didn't I didn't think so all right I'm not alone [Laughter] but let's say that it was a very robust network with security architecture in mind one of the containment actions that we might consider would be to isolate a network segment um we discovered that hey the blast radius is within that Network contain all of it so that it can't touch anything else and we can consider that kind of as the start of the cleanup or the triage then we move into our eradicate phase let's make sure that everything that we just triaged is cleaned up if it was a compromised endpoint let's return it to a system of known good if it was a user do we need to reset their credentials do they need a whole new set of credentials how do we protect that user and let's fix their accounts now some of the times as you're in your containment and your eradication phase you'll find new indicators of compromise you'll find more users that were affected maybe you'll find more URLs that were clicked I have actually a running joke right now which was what's the worst security slogan you can come up with and mine was and I'm pretty sure I won was carthy DM click the link so no one submitted anything after that so I'll just take that as a win uh but we can really take this and with new findings like I mentioned earlier switch back into an identification phase let's rescope with new information new intelligence with what is relevant to our organization let's take another look at what we need to do to start triaging to really limit the blast radius and to prevent the spread of damage and then with our recovery phase we're finishing our cleanup we want to restore business processes we want to make sure the users are able to do their job successfully and in a safe manner with Lessons Learned personally I feel like this is the most important part after an incident has occurred and I've had listened to the talks today just so many good examples of incidents of ransomware a secure configurations vulnerabilities um when we talk about the Lessons Learned we might call them post-mortem reports if you're in the military after action reports um but we outline here what went well what went for what can we do to do better in the center I have decreased detection and response time now for those of you in the incident response field some of us might say that the primary goal of incident response is to identify the evil contain it and return the business back to a safe state so that it can Thrive make profits do whatever it is that its purpose is in doing I think it's more important that we focus on decreasing detection and response time I like to operate under assumed compromised I think that there's evil regardless of whether or not we have an alert I think we need to utilize threat hunting to move ourselves from automatically detected iocs like hashes IPS URLs let's get into tools let's get into tactics what kind of processes are they doing in sequence that could be evil a lot of the average there I've seen use binaries that exist on a system like cert util Powershell command prompt that being said my focus on decreasing detection response time is because of this there's only 10 types of people in this world those who have been hacked and those who will be hacked again the best thing that we can do is decrease that detection response time let's get that time down as low as we can prevention will fail it's not a matter of if it's just a matter of when not I mean unless of course you know you take your computer or smash it with a hammer bear it six feet under the ground along with the rest of your network and call it good um I think we some of us would all like that does anyone here keep a gun next to their printer so that like if it makes a funny sound they can shoot it in the face I see Hands I see Hands okay cool me too C4 Extreme and I like it the other things that I do on a daily basis are purple team activities um this is kind of a little bit nerdy so not sure if everyone here will get the references from a movie um but long story short we have this character who's about to eat the buffet and got all these scare characters on the right so and in our purple team and and the organization uh the red team's like all right we got authorization we got a Rules of Engagement let's go and us on the blue team like all right let's hope tools work let's hope the detections work and uh I would say that um a lot of times the tools don't work but that goes back to our preparation phase right do we have the right logs and if the detection the automatic alerts aren't working do we have the capability to manually hunt and investigate ourselves and not only that but as part of the preparation as part of purple team activities a lot of people will think that hey we need to validate security controls and that's true I also think it's important that it's not just about validating security controls it's about improving both teams when the red team does something and let's say blue team does not catch it there should be a collaboration where it says hey I did this here's how I did this and then blue team can go back and validate okay here's how we could have found it and it goes both ways if red team gets caught blue team go talk to them here's how we found you you cleared the logs it generate event 1102 and that's how I knew you were covering your tracks and because you did that I scope backwards five minutes to see what else you did and then I scope forward five minutes to see what other log sources I could look at to find out what you were doing and a lot of I think that it's so important to have that communication for continuous Improvement so that was kind of a blast through the first two parts of my talk and kind of the next piece that I want to talk about which is really important to me and this is where I really want to spend some time with I wanted to think about during this talk what is something that I could provide to all of you I know that there are a lot of different levels of seniority in here I know that there's a lot of different fields in here I wanted to figure out what I could provide to you that would be of immediate value after listening to my talk after me showing you the things what could you go home and do immediately I settled on six things three of them are some technical tools and resources and granted they're a little bit geared towards blue team but I think that red team can use it as well here's what we're looking for if you don't want to get caught try to avoid doing these things and then three of them are interpersonal I can't tell you how important it's been over the past several years for me to understand that talking with people taking care of yourself taking care of your mental and physical health has been so incredibly important and I want to share some of the lessons I've learned as well I like to also preface this section with if I say something that you guys like use it and if you don't like it just discard it fair enough fair enough the first piece this is the react framework it's based on miter attack it's not the same model organization they're called Atomic threat coverage and on this website if you just Google react framework it lists the six phases of incident response and it has lists of all the steps that you could do as an incident responder to do these things and this is a screenshot of it right if you visit their website you'll see in the preparation phase it's like three times as long as every other phase and some of those things are take training get access get logs and it's just so incredibly important I have a friend who actually showed this to me recently within the last several months and when I saw it I was like yo I literally spent the last three years studying this kind of stuff and now you tell me there's a website that I can just go to and it tells me how to do my job Okay cool so I hope that by sharing this with you not just incident responders but maybe managers maybe team leaders you can take this tool and say hey where are we today out of all these things for incident response what's included in our incident response plan what are we actively doing what could we be doing it's not pictured up here but Atomic threat coverage also has a tool for called react Navigator it does just about the same thing as attack Navigator which allows you to put an overlay on and say all right we did this thing turn it green we do this thing turn it green we do this thing turn it green you can generate score you can make a heat map just a really good visualization of where you are as far as your incident response maturity levels go foreign moving on this is also another resource that I wish that I knew about several years ago what this picture is is a website called uncoder.io and what this websites was called Sigma rules into other tool languages Sigma itself is an open format it's a generic language it's based on yaml and what this will do is it will Define exactly what will happen in an event log it'll tell you what processes that you should be looking for and it'll give you the logic and if not and or not so the example that I have up here is scheduled task creation and we can see that the product is going to be Windows the service which in here is going to be a log source is sysmon who here has cismon deployed in their environment limited number of hands oh well I hope it's just for lack of not raising hands if you don't have system on please deploy the system on for the logs look at the logs the three things of logging and then on the right side here I just used an example to translate this into the Splunk query language or SPL there are thousands and thousands and thousands of signal rules and they're all free they're all open source you can literally just Google Sigma HQ rules and I'll pop you right into their GitHub and it's labeled it's mapped to the miter attack framework so if you know for example that scheduled test creation is technique1053 you could just search t1053 or just search for schedule tasks and it'll pop it up I put this picture of encoder versus the picture of the GitHub because I thought this was a lot cooler and Velociraptor okay I could talk about this tool for hours it is absolutely Fantastical it's free it's open source I think they were just acquired by rapid 7 and the community is great there is a Disco





