Cybersecurity: User Info Exposed - What Hackers See! #shorts
About this talk
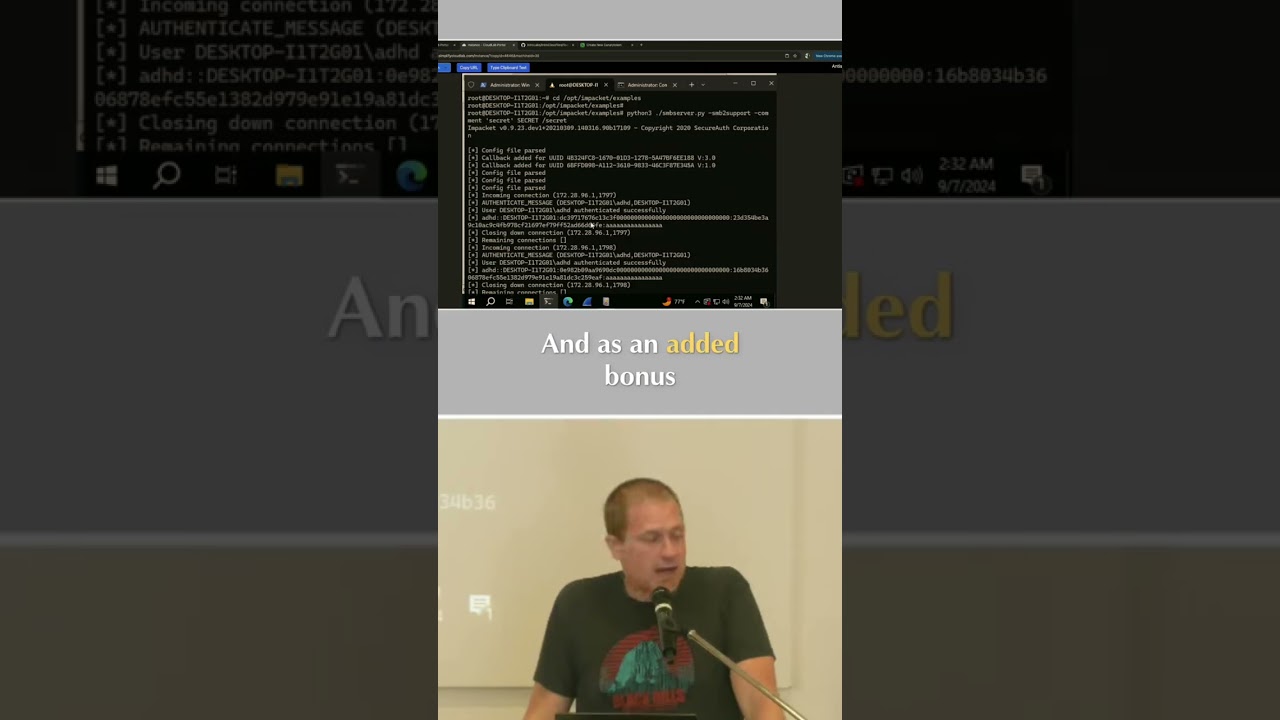
Gain immediate system identification post-exploitation by enumerating shares. Source IP, hostname, username, and even password hashes reveal critical system details. #Cybersecurity #PenetrationTesting #InfoSec #NetworkSecurity
Show transcript [en]
I have the source IP address. I have the host name. I have the name of the user. And as an added bonus, I also have their password hash. But this is enough information for you. If somebody post exploitation is trying to enumerate shares in your environment, you're going to be able to identify the system immediately.





