Training The Human Firewall - Reanna Schultz
Show transcript [en]
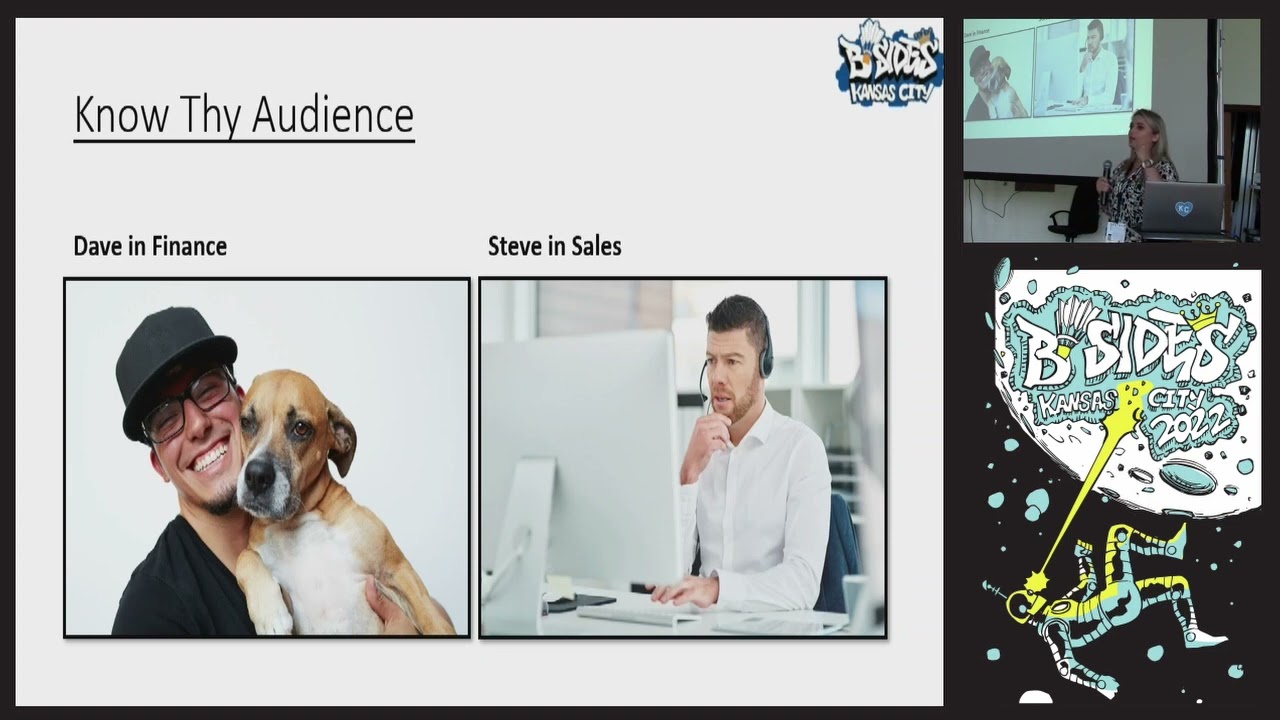
well hello everyone I just want to begin with by saying thank you to each and every one of you for not only attending these sites today but for coming to my speaking blog we're going to be discussing social engineering training the human harmful also known as our users and as a quick introduction my name is Brianna Schultz I am a University of Central Missouri alumni I graduated thank you I graduated in 2018 with my bachelor's of Science in cyber security secure software development I enjoyed school so much I decided to go back graduate again in 2020 with my Master's of Science and information assurance I have a huge extensive background in endpoint engineering network security engineering and as of right now I work on the security operations center I do a lot of volunteer work with women in stem and I'm a huge stem educator with Girl Scouts of America besides cyber security I love eating Chipotle and I enjoyed reading 1980s science fiction thank you so a few takeaways as we begin I would like each and every one of you to keep an open mind through this presentation we all come from different security backgrounds whether it's 10 years of experience maybe you are fresh out of college and you're sitting here or if you are a college student welcome to b-sides I really hope that you learn how to not only mature your security education fishing awareness program but if security education is a new topic for your business maybe your funding is a little low you can benefit from this talk as well so the previous slide sorry this keeps really sticking my keys the previous slide talked about historical knowledge about some of the topics we're discussing I did a lot of research prior to this talk in fact I took a pool of 100 users with the background of cyber security and computer science and I wanted to do a fishing assistant I want to understand the psychological reasoning as to why our users clicking fish regardless if security education is present or not so how did I fish up I took three different campaigns each campaign had a specific type of threat to be used fishing in a barrel spear fishing and spoofing I sent two different types of fish that mimic these types of threats and I made it into a measurable quantifiable data by creating my own algorithm by taking all of the fishing characteristics that these fish have I give it a severity rating this severity rating reflected the probability of the likelihood of how a user is going to spot a fish so the more characteristics a fish has the higher the score is the most likely a user will be able to spot a fish and for us to understand how to fish users fun fact we have to know our users there is a word called user architecture we know security and we perform security defenses by knowing Network defense architecture and security architecture and this identifies how our assets and how our defenses work on our Network on our business Network why are our users not part of these differences defense and death we talk about all of these different layers of Defense models our users are going to be that last defense model so we have to count as this being part of that architecture mindset for us to understand user architecture we have to know user mindset and user behaviors user mindset just go to really reflect how we do security security is also a type of mindset for example you might hear this frequently phishing education is important we per we provide leadership metric Maybe quarterly to show how our security assessment is working one to two percent of leadership might be like yeah our users are not interacting with their fishing program this means it's working but in reality we have a user and he knows for a fact that she happens the second week of the month and the company might provide incentives for reporting the fish such as such as providing swag items maybe the company sends out a huge email and has a wall of Honor for the users that reported fish six times in a row this year so this user understands there's initiatives and security so it's a fish out second week of the month this user received an email and then this user looks over to their co-worker who has also received this exact same email user goes cool this is my fish so they're going to report to security to get that notification that says congrats you reported a physician assessment so this user who is so friendly so great they're going to screenshot that email and blast it and slack or teams and let everyone else know in their Department that hey this is sufficient of the month you too can get swag for participating but what does leadership see that one to two percent click rate then we also have a different mindset we have annual education Refreshers are important yes we do provide fishing education but annual Refreshers such as videos might also be beneficial why because people learn different they educate themselves differently so some people are visual rather than Hands-On what's your day-to-day user going to do oh my gosh it's another video I have to watch that's mandated so they're gonna play this video in the background and they're going to continue on their day today what's our users learning here it's not pushing education it's how our environment Works how a business is working and environment so user architecture we have user mindset our users think what about Know Thy audience there is a saint in this industry it's called Know Thy Network know how assets work on your network um identify Rogue assets the netflow how the topologies work our users again are a different type of architecture Know Thy audience understanding how our users behave in an organization so we have Dave Dave works in finance Dave was a great guy great employee shows up to work nine to five every day um once in a while he's sick but we'll let Dave be Dave Dave has a lot of emails he specifically works with maybe 401K Services he might work with Benefits payroll then we have Steve Steve Works in sales Steve works with maybe account managers customers other vending vendors or third-party services David feed work at the same company and they got hit with a fishy made it through third email security because it's a new type of threat and this email security vendor hasn't provided MFA signatures yet so this email makes it down to Dave and Steve and the email content specifically say it's time for you to update your benefits you have a time frame to do this otherwise we're going to automatically unroll you when they click on that link it might be Prudential harvesting so Dave who works very frequently with benefits and 401K Services probably has a higher probability knowing that this is sufficient right Steve who works in sales and probably doesn't know much about benefits he's that day-to-day user that just enrolls and when he gets that email from HR then that's when he has a you know reminder throughout the year so what's the likelihood that Steve is going to be reporting this email so we have to understand how users behave we have to know how their email traffic looks because each user has a different Behavior with their organization so security education software it is expensive it is so expensive and I always make the joke you have to probably sell your plasma to be able to afford a good security education program in fact in 2020 improve point of release uh an article stating that it was eight dollars a user as a subscription for their security education platform I love Bitcoin it's a great but for a tool but if you are new to security education and security awareness you're probably coming at the bottom line of that budget totem pole which is sad because our users are part of a difference in your business so part of my research which was funded by UCM um I didn't go on money I couldn't afford these reputable vendors so what did I use went out to Google and I was looking for good open source tools I used a tool called go get fish go get fish is great I personally say this is something that you're looking to start and dip your toes in just to see how maybe security education looks in your environment and what I liked about it it had a lot of web hubs and API Integrations with good satp server Brands such as Gmail Yahoo Microsoft and what I liked about it even though it's open source the developers were very in tune with their community so they provided updates bug fixes and they let their Community know as well if you are interested more about this I do recommend uh skating the store code above just so you can learn more about it now this is how I used it I posted my go get pet server on a virtual Linux machine environment and that go get their server I was able to upload maybe email examples I also hard coded a few of my emails by using HTML CSS because I had a large participant full I bulk uploaded 100 plus user emails to this server and I was not manually gonna be putting one by one email link that's just I'm sorry no uh from there I created an authentication API took I created accounts on third-party SMTP such as Gmail Yahoo and Microsoft and I use that AP authentication token to talk from that go get fish server to that SMTP server that satp server to visit out all the emails what I like specifically about this go get fish is I could dynamically send my fishing campaigns meaning I set a time frame from a week to a month I scheduled my entire three campaigns I wanted and I sent it to all the users at a different time beautiful now this was one of the examples going back to the historical knowledge I used three different types of threats first threat was sufficient apparel and if a user did click on this they were redirected to a survey page and the survey page goes hey you had an oop scene I'm sorry um no worries but this is where you can learn about security education facts there's some common fishing characteristics I use all of these characteristics in my fishing campaign so I was essentially giving keys to the kingdom to my users of how can you not fall for my phishing emails so because I had an algorithm and I wanted to measure how difficult a fish could be my first fishing campaign had a high probability rate that industry speaking spot this in fact that first fish I sent I went through Google translate a good four or five times and they're reverted back to English and that's what my email was so I was really creative with it but what made this a very high probability about both of these um when hovering over those links there's a short URL there's generic Greenies you know really didn't make sense bad bad grammar badge structure all together I had people click on this and as a security professional specifically my audience being those in cyber security and computer science I said oh my gosh there was no way and we go back to the zero percent click rate why do they click on this they were curious um they didn't care in fact I have a few other participants State they had false trust that their anti-virus would prevent any threats happening on their computer this is why your users are your last layer of Defense so I said all right cool and in fact I have a couple that even know this was sufficient so I was happy they interacted they're learning that second fish I said there wasn't us me clicks and me being an actor in this situation instead of moms you know I like people clicking my question emails it's satisfying um but this did show security education is working with this type of threat now let's go to the second email I targeted Fear fishing I every participant was in University of Central Missouri student this was really fun I specifically targeted these students with factors that included their day-to-day um the first one I wanted to have a psychological scare with my users I said hey you violated in a browser policy you were looking up inappropriate content while on the University Network you have to go register for training there was a lot of clicks yeah fun fact there's no policy I used at UC um yeah and the feedback on this I had a couple of very angry messages from students and I was like look me in I don't care what you're doing on your computer but the second one wasn't as scary I wanted to have a false trust relationship with my participants in fact it's not uncommon especially since we have international students we have students at State students will work on Google Drive as a form of collaboration with homework and so I sent out a link and if you're a Futurama fan I use a couple of Pop Culture references such as Philip fry in this um again there's a lot of clicks but there wasn't that many and so we can see again educating on this type of threat is working so it's the last fish in my campaign are you spoofy if you do not have a decam dmarc policy on your email security filters I really recommend that you make a note of this you go home you research this spoofing is a threat and it is forever evolving it's forever maturing because our threat actors are getting smart as we are maturing our defense as well so I script my own University address and the header and all the participants knew this should be coming from my University address and I gave them a gift card as a form of gratitude thank you for participating had a lot of Clubs students love free money apparently um the second fish I sent I felt you know I was like oh yes hopefully I get a lot of clicks on this I had scraped the University of Central Missouri's office of Technology email I scrape their headers and in fact this is the format that they use for a lot of their emails I took that used it to my own leverage and I basically said hey your password is expiring you need to reset it from here there were a lot of clicks again so what can we learn from this well security education yeah it's great but what can we do at the same if I was in a corporate environment and I did this with all the users my organization leadership would say why was this high are our users silly and I'd be like no they are learning because this type of threat is clearly something our users are not educated on this is something we have to evolve our users with if you walk into the mindset of we constantly update our EDR we update our black listing we push patches to our systems to prevent vulnerabilities our users are a firewall we have to evolve our users so that way they get the same modification of Education that's coming out with new types of threads that way us as Security Professionals can have starting a false sense of trust with our users and zero percent click right unrealistic I'm sorry um all of the survey feedbacks either had a consistency of I was curious out of false trust that security was going to block this threat so having a low percent click rate doesn't necessarily mean a bad thing this shows that maybe hey you had a good starting point in your security education but now it's time to mature it one to two percent might be a low level for you but what about having a 10 or 15 so showing that your users are being challenged to grow and that's what we want as Security Professionals we are updating our user firewall so how do you mature your fishbowl well you do not have to be creative to have good fish in your pool work with your security operations center work with maybe your service or help desk these people are going to be your first size in the network these people are going to be your ears of your network in order to be seeing what is reported to them for instance if we're working in a sock and day from Finance started sending me a bunch of phishing emails and regarding benefits and I see nothing from Steve maybe I should have this in the pool because I want to train my other user behaviors to spot these types of threads as well how many it people actually report fish how can we target RIT people the ones with admin accounts and credentials another thing um read the news get on Twitter um follow some podcasts in fact Microsoft released two months ago and o365 fish that was targeting MFA tokens how many of you saw that and decided to put that on your fishing campaign but real world threats into your fishing campaign because again we are evolving our users to the type of threats that we receive day to day these are our last lines of Defense so this is my talk and like I said I hope you all came here with an open mind and maybe I motivated you to make a change in your security education maybe um this is a way for you to grow and evolve your user firewall as well I want to leave this up for a couple more minutes because we're going to have the feedback slide I have a question yeah what's your favorite fish that you've ever seen oh baby just because it shows maybe gaps and my security and something I can take back and work with my other security departments as well if there's any other questions let me know yes um how difficult is a supply pass like external email to things like password resets is using slack or teams or something like that an internal network notification better to avoid the addition details for an extra resources yep so each organization so the question was so regards to scooping um how difficult is it to bypass like external notifications for things such as email or I mean um password resets or things like that for internal appliances consoles like Office 365 or something like that and get those the teams or slacks so that you don't ever have to get a password reset through your email yeah and we go back to talking about defense and death layers so there's a few factors you can include to harden that security um you can use slack in Microsoft but we have seen how many times those have been hacked how many times those have get oh does well and you have the same recent events in the news um it's not uncommon so what we can do we can educate our users of what's an authoritative source of a password reset maybe it's a banner if you're using MFA as a secondary maybe you're using a portal to reset your admin passwords or reuse your passwords from there uh rather than something like an external website would like to answer it boldness awesome thank you so much [Applause]





