Act and Think like an Epidemiologist to Combat Digital Diseases
Show transcript [en]
the b-sides DC 2016 videos are brought to you by clear jobs net and cyber sex calm tools for your next career move and Antietam technologies focusing on advanced cyber detection analysis and mitigation good afternoon my name is Ethan Ortiz and thanks for showing up to act and think like an epidemiologist um you can't can't hear me okay you hear me now oh man and you hear can you
this is CNN testing one two testing one two testing one two testing one two should I just yell then okay okay testing one two testing no testing guys testing can you hear me in the back if not you move up please
nothing anything nothing can't hear anything out into the room that's because none of these are up so you got to have these dials up all right so glad i can edit this part out thank you all right okay with that my name is Ethan Ortiz uh is the only time i'll mention that i've been with symantec 14 years mostly as a systems engineer and the last two years I've changed into a different role working with our innovation team and this is one of the wonderful things I get to do is present just these type of thought leadership type stuff and trying to convince you to you to convince others to think a little bit differently about the cyber
situation so I'm gonna tell you a story and then I'm gonna show you a tool and then I'm give you some tips that you can take back to the office so it all starts with a with a visit to the doctor so go to my doctor this is like five or six years ago now and yeah that's me on the left and after I got my annual checkup my doctor asked me so even your smart guy she assumed a lot but she's the you guys are doing security are pretty smart you have come your company has a lot of smart people researching all this antivirus stuff so why do i keep getting viruses in my computer right this is
like six six years ago now and it hit me like wow this is very smart lady she's been a doctor for a really long time and she asked me this question so I immediately just said dr. you're a very smart doctor and I'm sure there's a lot of medical practitioners researching you know Ebola and stuff so why do I keep keep getting sick why do I keep getting sick and that that kind of spawned the an idea that because I was able to educate a highly educated person on and I made a bridge right I connected that bridge from her way of thinking too I'm cyber anybody has a drink drink and then she said oh I get it so I started
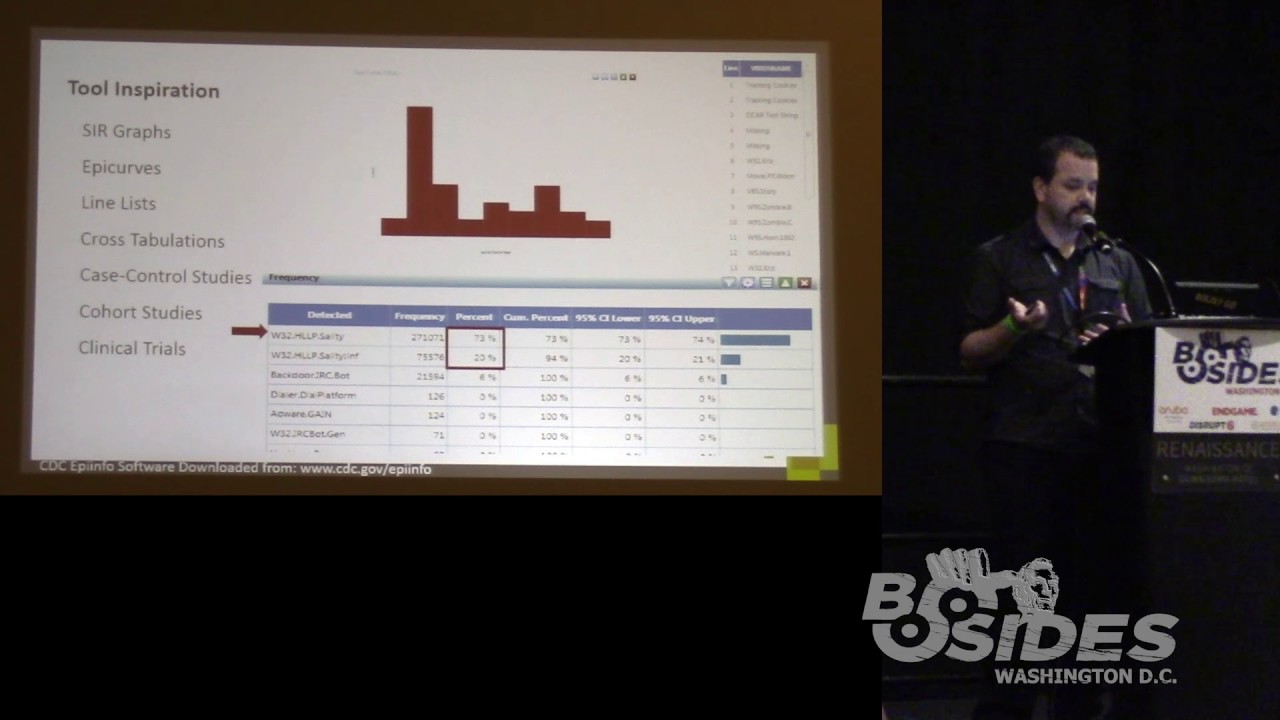
researching and I had the friends who are nurses and they gave me all these books on epidemiology basically level six viruses and stuff like that this is before the whole thing in Africa happened and one of the books mentioned the tool called epi info so i guess none of you know what epi info is it's a tool developed at the Centers for Disease Control that's provided to epidemiologist so when they go out in the field to study malaria or you know smoking Ebola whatever they enter the data into this tool and then they run statistically statistical wits that would either predict where people are getting sick why they're getting sick and so on so I started playing with the
tool just because I'm curious that way and I I ran some old data this is from 1854 it's a very famous epidemic in London and this is called an aberration detection chart this is a you can see the little reference in the bottom it's the epi info software and I'm like oh that's cool what other stuff is in there all they have these two by two widgets these little things you can run that you ask it oh no why did somebody get sick well we don't know so let's just find out you know what what did they eat at the picnic where somebody people got infected so some people a bacon some people a butter some people ate turkey
and so on and they did these things called two by two tables the laser is not as good these two by two tables so out of the three hundred and fifty nine people that were at this massive picnic 118 of them had eat that were exposed to the cook bacon and got sick 34 did not get sick all right bear with me this is going somewhere ok Bacon's good so it wasn't the bacon it was the butter that got everybody sick so um so they found out that you know that there was a larger proportion eighty-two percent almost 83 that if you had had the butter you would have become sick alright so that's that's one tool um that's just
the numbers okay and then like I had one of those midnight explosions in my mind like oh my god this tool has a sequel connector I wonder what happens if i plug it into the cement database its sequel and I would I just click on the widgets give me a frequency analysis for the alerts that are coming in and which machines are getting infected and why and then I saw this mic on most of the detections are not being detected with the antivirus is being detected with this practice stuff that's interesting again remember this is a CDC epi info a tool for researching biological viruses right and then I did it had a paretto button and I'm not a
statistician I just hit the little peretta button and most of the events were left alone like oh wow that's a lot of left the loans okay and then they have something called an epi curve which is cakes a count of the number of infections that have occurred over time and then and this is something that was used has been used for decades to look for a burst of infections okay and so what happened that day so that's a question so I've tried this tool with many other products not just semantics and it raises a lot of questions doesn't really answer many questions but it makes you ask what happened that day to cause that right okay then had other
stuff that I could run so frequency on the what policies reflect the most which viruses the word of the most prevalent you get the idea so those on the bottom there are behavioral policies they're like no people plug-in and USB sticks and and the like and then I asked for frequency analysis on what was detected I found that like ninety percent of the infections in the environment we're basically attributed to salary so what so this is now this is the epidemiologist thinking what about my environment makes me exposed it's dis ality alright so instead of trying to write a virus definition or write another IPS signature what is it about my environment that I could change to
make it less susceptible to that all right so I started I kept reading reading and reading about a PD me ology and I found these other things yeah you know cross regulations case control studies cohort studies and clinical trials and I'm going to talk about those some of those later but I showed you the EPI curves that's an epic curve on the top so on that day something happen so maybe I should look you know narrow if you're using splunk narrow your search to those two to those days a few days before few days after you whatever sin you're using all right so then I looked at the history of Epidemiology and how the United States
invests its money in health care in a public health and I saw a link with the digital so before 1979 there was something called sickness management all right so I'm going to go compare it to our digital world today so sickness management is basically dealing with the effects of the disease after the fact so let's take a look at it in a digital in the digital world so we install some technology because we love to buy technology we install it on our end points or gateways whatever and then we wait for the security vendor to provide us or vaccines and so on and then I don't know you know not you guys of course but most security guys just sit
back and wait for the alerts right you wait for the alert and when the alert pops up you do your job you check your console on Monday Tuesday Wednesday Thursday Friday everything's cool because it says I detected a virus and I removed it I detected a you know a call to a command and control and I stopped it and then one day something happens and all you know you call your favorite I our team to come in and do their job and then you do the investigation and remediation and then it's done and then you go back to waiting for the alert and then it happens again and it happens again so it's like a i call it the
hamster wheel of death you just kind of do it over and over so in epidemiological circles there's three types of prevention this would be called secondary prevention where you wait for the thing to have to get diseased and then you try to alleviate the symptoms right this is crazy then after 1979 the NIH published this this huge document that changed everything into like wellness management and I'll go into more detail on that but let me just illustrate it here for for you guys on the Digital side and then I'll go back so wellness if you if we were to apply wellness management to our same routine that big line on the bottom is the new thing right so you actively
study your environment so our people you know what are the logs telling me not just the I detected something definitely bad but what's probably bad possibly bad alright this is a preventive security thinking okay so you study who's getting infected or who's running a certain application that's not signed what are they doing when are they doing it where are they doing it I have to be very careful my kids are in the audience oh I can't use certain words though there was a joke right there clinical on case control studies you got you guys got it so you studied you know did epidemiologist study like where did people drink water from where did they eat what did they eat who were they with
right and then you you run some statistical analysis on it and you get possibly infected probably infected or confirmed those are the three things that they look for whereas management wants to know you know there definitely is a breach or we're definitely clean it's like a zero or one hundred percent epidemiologist take a different approach you know you're you could be sort of sick right you got Ebola on Monday but you're not going to show symptoms for like seven days but if you're exhibiting the symptoms initial symptoms then if you start reacting towards the beginning you have a better chance of containing that thing right alright so walnuts management requires that you Institute controls and I think everybody in here
has instituted controls but an epidemiology do it a little bit differently I think then most people I see where instead of just deploying that IPS policy or that firewall policy or AV or whatever DLP policy they would deploy their wish policy like what policy but you love to deploy in log mode right so management won't allow you to install you know to block USB they want to allow you to block certain applications for ever being blocked so why don't you turn on your wish list then after a few weeks or months whatever you decide how long your study your clinical study should be then you have evidence okay this is what the very famous epidemiologist did where
he he tried to convince management to institute a control and they said no you don't have enough evidence he collected the evidence and when he presented it they had no choice because now they're liable okay so we need to do the similar thing okay but we need to create those those are wish policies so what ends up happening I think is that you your your number of incidents should go down right and I'll go into some studies that we've done later but um but instead of just chillin back okay now I've done such a great job now I can watch netflix at work how about go do more not that anybody does that but do more studies
okay just do study your environment more view if you're sick of endpoint security go to the LP or or your network ideas whatever study them over a long period of time and I want to say that this is very different than your IR guy or forensics guy your reimaging guy because we still need those people this is the kind of I tend to say it's boring but it's exciting because you're going to look at the long-term you're not going to discover the apt you're going to discover the behavior people do that exposes them to vote up to infection so like I said if it's USB prison as if it's the browser's not getting patched fast enough if the plugins are in game
patch enough now you have evidence that you can send up to suggest our patching of operating system is not enough maybe patching Adobe Acrobat is more important than patching the OS based on the statistics you've collected I don't know you know your neighborhood better than me right all right so this is the healthy people document that i copied quite a bit from so this is the 1979 paper by nih you can download it enormous but here's a kind of what it was basic saying before 1979 the United States invested most of its budget for health on fighting the pathogen okay so that's the cholera malaria you can see them there so that's antivirus alright fighting the pathogens okay after 1979
after the CDC and NIH studied all this stuff they realized wait a minute we could save more people's lives and have people live longer not by focusing on preventing malaria cholera the flu and e.coli and so on but just have them stop eating so many burgers all right have them stop you know we're driving without a seat belt you know stop smoking right they found that these behaviors that in the document they're called lifestyle choices made them die sooner so how do we apply that to the digital well first let's look at the controls that they put in place for the past and and 44 post past and post 1979 so before they no vaccines you had sewage treatment plans
you had you know the little signs that say wash your hands and then the you know all these controls to prevent i like spanish flu from spreading you know put the the face masks on and after 1979 eat well right this is these are preventive controls you know exercise don't sit on the sofa that's what the sofa meant by the way seatbelts were mandated and thousands of people were saved the very next year okay little tiny controls and no smoking so instead of focusing on oh I found the apt or I found this let me write this IOC this is awesome it is excited it's exciting right this is not the kind of work that's court that's great that this kind
of work is kind of the look boring drawn-out work that could have a huge impact because you're having people put on your seatbelt all right stop smoking so let's compare it in the digital so this is before viruses worms Trojans apts backdoors all the cool stuff that we like to hunt so how about if we just educate our users observe our users what are they doing are they bit touring that a real word bit turning at work are they touring are they running like a gazillion browsers that the corporation is not patching you know and are they click addicts I don't know if that's a thing but I know like if that's a word but I you know who I'm talking about if
it if it has a hyperlink I want to click it right people is there something we can do to kind of alter that behavior or if we can't convince them to do it put a control in place and if you can't prevent it monitor it so you can convince upper management to allow you to control it because if you disable certain features if the masses are going to write it right so you're going to have to give management buy-in and the only way you're going to get is with evidence you need evidence driven security so what kind of controls to be put in place for all that that the viruses map the Trojans the pts and
stuff oh we anti-malware network ID s is endpoint IPS is firewalls we bought all this stuff and then we just we try I don't know exactly when it started but then we started using certificates and you know containerization and we stopped focusing so much on the antivirus and studies shifting over to policies checklists patching security awareness programs and so on but I don't think we're not we're not doing that enough we need to focus a lot on this side because buying five extra network IDs isn't isn't going to do it all right we have to get the users to learn to cover their mouths when they cough if you will and and don't eat that sandwich off the
floor just you know you wouldn't pick up a sandwich and eat it off the floor so why would you do it to a USB stick on your computer all right all right and another thing I usually this is the first time when I say this stuff in front of my kids but I've been teaching our kids to do this know when you cough okay we didn't teach them that in our one our yearly security compliance or health compliance training we had to do that repeatedly over and over and too often companies just do it once a year or worse at the employee boot camp when they first get hired and that's it and then every year they
just have to sign a piece of paper says they're aware of the security policies now we have to kind of repeat it over and over and they're pretty good now the irony somebody pointed this out to me there any about the coughing into your arm is that it will not make you healthier it makes the other person healthier it's a weird thing is one of those altruistic things that we do as humans we teach our kids to take care of others only ask them to cover their mouths and we hope that everybody else does it we need that kind of mentality that kind of reinforcement at work don't click on that you know document from
from a random person not as much to protect you but to protect the entire corporation right otherwise you're sneezing over the entire company or coughing all right I made this slide to kind of show that more parallels then I'm telling a lot of stories so you can take some of these nuggets and share them when you're out there so in both biological and digital space you have simple threats the common cold or adware you have complex threats Ebola Stuxnet you have the sharing of stuff so when we share water we have the possibility of getting an illness from it when we share nazareth's we have a possibility of getting an illness when we share needles
which you try and do I don't care what you do on the weekends just don't share the needles and then the USBs when you share USB so a similar type of thing as part of the human condition and socially and in the social digital space we have to share but you don't have to be reckless and then both in biology and digital that the bad stuff seems to find a way around whatever we implement so no matter what technology you put in place the bad stuff still going to get in all right so let's stop assuming that we can buy the golden pill you know that's going to solve everything and then I kind of like this one too it's a since
the dawn of life there's been diseases since the dawn of the digital age has been digital diseases right so I'm telling a lot of these stories this way a lot of these on little snippets so that you can share those with people so that they can click you can have that aha so now let's get them into more thinking like an epidemiologist when an epidemiologist goes out to another usually another country but we have a number of epidemics here to still today like the ice cream one we just had a few weather last year they do not they cannot afford to cure everything or to put a control everywhere so what they go in with these these three little circles
in mind where can I take my little resources they only have so much money where can I apply my budget to stop the disease and what that triad illustrates is that the disease can only occur in this case an infectious disease if you have all three so if you can invest a little bit of money here this is antique Lee this is the pathogen that's the thing that's actually getting people to get sick if you can do something to prevent that great like like a vaccine if you can't afford a vaccine or you don't have one is there something you can do to the host to protect it if you can't do that is there something you can
do to the environment so in the biological space that would be environmental controls might be like the netting over the bed for malaria okay in the digital space you have websites you have you know blue coats and all this stuff to control the environment coming to the host and on the host we do all kinds of crazy stuff signing of applications we containerized applications we're going really crazy with all this stuff trying to isolate everything we're trying to put everything in its own little like biohazard containment unit that you know if you can think of it that way so how how can you convince management to give you everything you want you can so pick
pick where you're going to focus your energies for the particular types of problems you're having okay so don't try to get everything focus unfortunately that requires studies so oh it's a question
so thank you so is the host of people or the computer
ok can you come up cuz you got competition pruning the people ah yeah I wish we could do that no um so I've been in many dinners where people say exactly that and I don't think we can go that far just yet maybe in the military they can do that or something but what I've seen done like what happens in my company we get fished on internally and if you ax if you're dumb enough to click on it we get the little rat that says guess what you're going to security training so it's kind of a punishment right you're not getting fired but if you click the link you're going to have to go to security awareness training so
firing people will not be great maybe on the third strike but yeah how many of us would be out of a job right now yeah all right so this is another i mean i'm shamelessly stealing from the Centers for Disease Control this is something called it SI our graph it's a susceptibility and flexibility and recoverability say that five times so it shows you that if you can see it from back there the red marks are when you were susceptible or exposed to something the longevity of the line is how long you were exposed to that thing and then if you have a black anchor you're dead so you basically died okay so that's that's one of the ways they plot out
okay when somebody was exposed this is how they determine things like the incubation period and if if you go more than 21 days without symptoms and you're not going to get Ebola right because they did they saw that the longest time was 21 days so what you're looking at here is my first prototype about two years ago and on the y-axis our user names for computers instead of people's names and on the x-axis is time and then the background colors pretty bad account you can see the colors but is the group's so the logical groupings in the corporation so this is this is this was the crew for concept and then a buddy of mine
his websites right that his github is right there we got together and built this tool I'm totally ripping off the CDC so we have again x axis is time y axes are the host we change the host names to numbers so we can actually so I can show you this but all we did this isn't this is a two-year-old slide and we'll work up to the more recent stuff but the gray dots are updates content updates the blue dots are check-in times and the red dots are infections and again since i since most of these presentations people can see them i'll highlight them for you those are the infections so what we decided to do is
use that s ir idea to kind of just show the data visually and let the human correlation kick in so it's one of the one of the proof of concepts we developed so we just we spotted patterns so that's the same computer getting infected almost every other day ok but here's here's the crazy part if you log into the console it said i detected something and i cleaned it the next day i detected something and i cleaned it so when you look at it's like going to the doctor and they go oh oh yeah you were sick but I you're fixed now and then they go to a different doctor and another one and another one and another
one but they don't see the big picture that they've been getting infected / and / or bo they're getting ill for some reason over and over and I forget which one of these it was because there were different reasons for this happening but one of them is a downloader so the downloader was did we did not have a signature for it but when it downloaded components the AV detector didn't cleaned it okay but when you look at a console know regardless of what it is you're just seeing that point in time versus time lining it this way all right and then you know oh by the way the word disease I thought it meant something you
caught it's not it doesn't mean that it means the abnormal function of an organism okay so and that's impolite now because we spotted other diseases that were non-pathogenic right so like we saw these white lines I don't know if you can look like you can't see them from there but basically we saw a pattern of when people are turning off their computers right we didn't expect to see that on a visualization we didn't program it to do that we just visualize times two events over time of color like huh some people are not turning off their computers and they have little red dots in the middle of the night who's sitting on that computer at two o'clock in the morning
then we spotted other things like this one here where my laser eiga this is getting more updates by a lot compared to the other ones why we had a group of machines that were checking into their manager like almost non-stop saturating the LAN links okay so I forgive it's this one or the next slide but they tended to be the drives are full so that's when a hard drive is full and it tries to download content when it tries to decompress it it can't so I fails and then it waits for the nest chat next check-in time and it downloads it again and it can't install it shuts it you know turns the dog turn it off next 15
minutes check in does it again so that was a abnormal function of an organism and after check after seeing it this way just go check check the policy and change it oh look at that the hard drives fall let's let's pick this remediated at but those machines were now susceptible because they weren't getting their updates you know and then this is another one where you had an entire office drop off and they stop they just stopped checking in okay yeah so on a console when you're looking at thousands of machines for hundreds of machines whatever your organization is as you're scrolling down if you see a big black Blanc block that that would be a problem all right but if you looked at
it just for the day it looks fine then we looked at another product so we took the same another product the console this interface is something we worked on but this is a different product we collected their logs and do it again okay here we go there's the there's the same type of stuff different company and those two bottom ones were the first high priority ones the laser pointers not working so these two let's investigate those what's going on there look at me this is very troubling these guys this entire group is checking in but never getting updates it's not even trying to download up anymore so again these are not infectious diseases it's just that the
hosts are not functioning correctly and we're able to see that go change the policy and now it works it functions correctly so the probability of them getting infected is lowered because yeah they're actually working the way they're supposed to this making sense and these are machines that the other machines work is pretty consistent and being turned off at night these were not so they were violating policy you're supposed to turn these off so go change for some to get turned off then one more this is a later revision this is back in like april 2015 this one we added application device control so like what processes are executing when they're executing our USB sticks getting plugged
and all that stuff and that's shown as green so quickly you can see that two machines are very green there's a lot of activity on those machines or violating a lot of policy so why then we my buddy made it so that when you click yeah what I ended up calling the patient report came up there it is so now it shows in color it breaks out the firewall IPS what files they downloaded what maybe what AV signatures were triggered an application device control and very quickly can maybe quickly you can see that the firewall is getting hammered something's up it's either communicating out or somebody something scanning and so then we added another button oops to
get even more details so he can hover over that one event and see what what's causing it so um this was my buddy doing work on his customers I ended up using this at one of mine and the moment we lit it up on his data we found dual nics servers so one nix on the inside one nix on the outside bypassing other security and all we saw was black lines across showing heartbleed just hitting the company but the product was blocking heartbleed right so the eight and the IPS was actually saying I detected heartbleed and I stopped it I detected hard plate and I stopped it but it at least let them know that you have an abnormal
functioning of an organism here it was not supposed to have to nix plugged in one to the outside and one on the inside that way so again I'm not focusing on discovering the apt and focusing on looking at the long picture and making the hosts healthier like making them work correctly then I used other tools this is a key be the part of the elk Ithaca offshoot of Cabana to do a these are scans AV scans so I saw saw machines that were taking too long and I believe this is the one that was a nas scan from an endpoint a very cheap customer setting up an endpoint to scan a nas drive which would take forever bad idea
and then policy detections by time fire alerts by OS and stuff like that and then this is a very old slide and you can see my awesome graphics this is just the illustrate kind of the mentality change from today to the EPI digit ologist right ok so that that guy right there is your everyday I information security guy you know he's a firefighter right he's saving all these machines all these hosts he rips them out of the network reimage 'as them and they're healthy again they go off to their merry way you introduced this new guy get my graphics are terrible but did you introduce this epi digit ologist guy and he's going to come in and you know the
legacy guys going to say where you going help me save these people I am going to help I'm gonna find out why they're getting sick in the first place that's a whole different you know differently from way of thinking all right it feels good to save somebody's computer to get them back into production and so on this boring work somebody needs to do it right and when they find out oh it's it was the Nazarite so let's put a rule 2 or less installs a scan engine on that thing and now you'll have less people to deal with less laptops to reimage right because you're preventing you're lowering the amount of P that are getting sick yeah it's not the
water's polluted all right and then folks started asking me so where do we get these people you know these you get you information security guys are expensive you know there's a skills shortage and so on and so forth and then I started basically arguing that the helpdesk would be a great rapport a repo of people to the higher so you don't an epi digit ologist doesn't have to be a you know static analysis ninja or dynamic analysis ninja they just need to have a logical mind be analytical and have a lot of patience but um help desk folks if they have enough years in the job they know where your exchange servers are they know where your
sharepoint servers are they know the neighborhood right so what better person to put in front of a dashboard to look at statistics like when they see an outlier like on some of those graphs like the customer I have we saw oh that their dual nicked they're not supposed to be I didn't know that I will couldn't possibly know that he knows his neighborhood better than me and that's where I think helpdesk hiring up internally and who doesn't want to be in security at sexy right this may not be the sexiest entry entry way but it's it so it's a way in and I believe and I mean my my son my ten-year-old here has seen my tool at work at home anyone he's
pointed out oh that looks like this and that looks like that my ten-year-old can figure it out huh yeah um and then I so I put a slide up for clinical trials okay okay cool perfect almost done so this goes back to what I touched on earlier survey your environment analyzed as many laws as you can then you create that awesome control you wish you could put in place right test the control now it's very important that you test randomly okay too many times when I talk to customers and like yeah we tested that product and it's terrible self-censorship it's terrible like where'd you tested Oh we tested it on the IT guys we will hold
on can you pick somebody from HR somebody from finance somebody from sorry okay so you know basically randomly select so I wrote a little Python script that just goes into the semantic database and just picks machines at random and then I can apply a policy that the wishful policy on just those machines and now as you know we're polling when you poll randomly it tends to represent the rest of the population better versus polling bias Lee okay let me just pull everybody that like in the famous telephone survey back in the nineteen like 30s where they surveyed who would vote for the president but they only called people who had a phone people who had money it wasn't a truly
random sampling so I would suggest test the control on a truly random sample then measure the effect is effectiveness of the control after a period of time you decide whether it's a week a month maybe you do checkpoints and if it was terrible start over if you didn't if your control was terrible rewrite it and start again if it was awesome deploy it to everybody else right just like the biological space just like the pharmaceuticals do just like epidemiologist do you do the placebo type thing and the real one okay almost look at like nine minutes left so changing how users think of digital threats so think digital diseases so just you know tell you tell the users
malware's just another type of infection all right just that just like you get the cold you're inevitably going to get a cold so they're part of the human condition you've really there's no product this is for management there's no product you can buy that's going to prevent your machine from getting sick if a vendor says I just invented the magic the magic pill they're lying and then this one tends to get a good laugh and I have to censor myself but just because we invented antibiotics doesn't mean you go crazy and you're not you guys from the 70s know what I'm talking about so you know it should be a somebody me you got it it you should just because
then a lot of users do this all i have norton so i should be protected i can click on whatever I want no so we have to change that mindset okay that's like my ten-year-old pointed out that a people who use helmets tend to take more risks because they feel though I have the helmet on so I'll be safer no it's supposed to be the last line of defense don't take more risk because you have the helmet and then study continually study and I'm guilty of this and I hope you agree with me our desk slide manner has been terrible alright we tell our users behind their back their stupid right they don't understand anything so
why would they listen to our prescriptions to better themselves when we belittle them alright so our bet our desk side manner needs to improve and and and just I'm sure you've experienced this with your doctor when your doctor is a has good bedside manner you tend to listen to them when they don't you ignore them alright so when you make when you prescribe a certain action if you do it nicely they'll actually think about it when they get that email that asks them to click ok so what what to do when you get back to your offices get to know well but maybe not you but get somebody whether in turn or somebody from the helpdesk well maybe you do it
but get to know your assets you need to know your neighborhood who lives in your neighborhood where's the exchange server right where's the sharepoint server and so on visualize your data I mean I was shocked to see the stuff that we saw totally unexpected results by just visualizing the data you can use the tool that we provided but there's plenty of other stuff out there that elastic logstash gabbana excuse me tableau there's plenty of tool that you can start to visualize your data and then use those visualizations to communicate to management they love crayon pictures leverage and then leverage a new insights to insta to create new clinical trials create if you see certain things and you
want to enrich that data then create the trial and deploy it in law only mode and then a few weeks later you can actually make an informed decision and basically make it evidence-based and I think I'm right on the money is there any questions
herd immunity so not not community um so when you have a customer that has the firewall and the IPS on some of their machines I wouldn't call it hurt immunity but I would call it like alerts like they become like the neighborhood gossip so if you were watching I feel like I have many customers who don't have the IPS or firewall turned on unfortunately so when we tell them turn it on on a random set of machines they become the you know the canary okay so it's not herd immunity but at least you get as long as it's random because if you just turn it on is then so you have the canary to alert you but you have to
be looking and not looking in that one day console you got to look at it over time question about
hmm
yep
yeah so when you write on man you're installing all these applications what dll's came with those applications right that introduced vulnerabilities and if they installed it you probably have no purview into them so you're not going to patch it anymore for i'll use an example anaconda is holier than Swiss cheese right so somebody installs it because they need to write their little scripts not knowing that they just opened up that machine to a ton of vulnerabilities right so yeah when you install too many applications it's somebody eating too many different things or take actually taking many different medicines you don't know what the interactions will be anybody else all right well thank you for coming





