Here We Go Again: A Pentester's Year in Review

Show transcript [en]
what's up guys who in here was that Reggie's talking you guys all thought it was that so [ __ ] right good all right so uh yeah I'll tell her rights unless so it's good Safari started damn it I love that he says who are you and why should I care all right so I'm Tyler right son on the founder of lead cybersecurity we're based out of Albany New York all we do is penetration testing offensive security that's it nothing else we don't remediate issues I've written two books alone on wireless network security one on offensive security in which I propose that a specific individual can acquire the skills necessary in a very short period
of time to be able to hack into any organization and I stand by that and I think soon put my money where my mouth is and trained somebody from scratch but anyway you know why you want to listen to me is because I eat sleep and breathe security it really is what I love and you know even if I retired tomorrow I would still do this we have an awesome team at elite this is actually a picture of our team and we have a growing team as well so if any of you guys you know are looking for full-time work or even the contracted work reach out to me because we are looking for anyone seen in my talks
before no one your own loss so I despise interaction if anyone speaks out at all I will stab you alright no joke I actually like the exact opposite you're here you know I mean you can you can watch videos online and so you should take advantage of the fact that you are here and if you have any questions comments like to rebut anything feel free to just shout out don't raise your hand to shout it out that's what I prefer and I have an awesome announcement to make so any common which is a sponsor of b-sides work we founded it this year this is the first year of the conference it's in Albany New York June 16th
through the 18th Dave Kennedy is keynote speaking iron geeks gonna be there you got a huge hardware hacking village and awesome capture-the-flag competition in which we're testing every area of skills so come join us it's gonna be a great time and I'm actually giving away two free tickets during this talk as well as the CTF winners here are getting a free tickets to the con so pay attention because I'm gonna couple things and also we've got cool cool people sponsor we got like free stuff from no starch press south orders is donating lockpicks and things like that so it's really just a conference to have fun and you know grow the community in the Northeast we still
need speakers so if any of you guys I want to speak you get a free ticket to the con and you know really want you guys there how we hold a security meet up in Albany called side beer security it's free and formal but if you guys are find yourselves in Albany let me know you can join us so finally why are we here why are you in this specific talk so ultimately I want to share some cool war stories with you guys I've always loved war story related talks to just hear how other pen testers have experienced different challenges and cool finders that they have you know just share some cool stories and hopefully I give you some new techniques
I recently released some tools that I spoke about previously things like LDAP or dan which is a command line based LDAP reconnaissance tool once you have credentials or if it allows anonymous connections to enumerate a lot of really good things you can use an append test from an Active Directory other things like authenticating to OWA for for phishing campaigns and some other stuff bait after this talk once once I'm done with one of the engagements because one of the games I'm going to talk about I'm actually still in the middle of so on Monday morning and we're going to continue on with it so you'll see where we're at right now what I hope to
release a couple of the tools that we created as well as hopefully a white paper Ethan so you can check out my page there so before we dive into the war stories I'm always like to also talk about the interesting things that I've learned in the recent past so I'm still reading this book and I highly recommend this book it is so awesome you know we're big in the whole samurai martial arts kind of thing and some of the the specific things in here really stood out to me one of them is a story that I wish I had heard before I wrote the last book because I would have included it and it is so the book is the sort of the mine
it's all about you know swordsmanship and mastering and sword and so one of the best stories in this book is about a master swordsman who's walking along through a village and there is a boy being held hostage in a in a barn and so the master swordsman stops he looks into the barn and you guys got the sword to the little kids net and so this master swordsman borrows a costume or you know the outfit from from a Buddhist monk and he approaches the door and he says you know it's it's been a few hours you're in there with the kid you both must be very hungry and the guys saying you know don't take another step in here if you
do me to cut this kid's throw any guy says fair enough I just want you guys to be to be able to eat I know you've been in there for a long time and so he rolls up to rice balls and again he approached the door and says I have these two rice balls for you and the guy says if you come inside I'm gonna cut this kid's throat until the guy says yes I won't I will not come in and he throws him the the rice ball and he the the guy lets go of the kid he's holding it catches it and then the guy throws the other rice ball he drops his sword and catches it
and so he runs in tackles the guy and supposedly this is a real story and from that point on he was like you know considered one of the top Buddhist swords masters the sorry no actually I don't know if it is this does reference life-giving sword in some of it I have not read that book yet but I cannot wait to read that book so yeah I thought that was a really awesome story and if you really stop and think about it like what they're what they're really talking about is once you reach that upper echelon of understanding and mastery of your weapon you can completely discard and that's one of the number one things
that they talk about in this book is that to become the ultimate swordsman you need to learn to the bend yourself against someone with a sword with no sword it's really a cool concept so again I really like that awesome story again another story in the book was about a master swordsman who was basically challenging people while he was on horseback and you know he said no one can can defeat him while he's on horseback he's the best you know mounted sword and so sure enough there's you know all these guys that are challenging him in this one master swordsman they kept challenging him to face this guy and said no no it's not worth it and so finally they
convinced him and and he rides up to the guy on on horseback gives the nose of the the nose of the horse of his opponent's horse a little tap the horse starts reeling and the guy has no control over the horse and so sure enough you just you know knocks him off his horse that's really cool again way of looking at outside of the box thinking and then there's two really important concepts within this book that I thought weren't awesome and one of them is about obtaining knowledge and mastery of anything and so I'll run through this really quickly I want to read a quick passage from the book but it says to reach a house you must first
enter the gate the gate is a pathway leading to the house after passing through the gate you went to the house and meet its master learning is the gate to reach reaching the way because learning is the gate don't think that the books you read are the way books are a gate before reaching the way and so this is like a good example of how pithy but meaningful a lot of like these Asian texts could be I just love that that the act of learning is just part of the process and to get to that point where you have real with wisdom you can essentially you know you need to shape those two things and so one of the other
really awesome things in here is a this concept of exhausting all knowledge and so I want to read this really quick and so it says the great learning says exhaust all knowledge and master everything exhausting all knowledge means knowing everything that is generally known in society and the principle of everything that exists leaving nothing unknown so I feel like I've gotten to that point so so so this is a really really interesting point says well you don't know about something you have doubts about it because you are doubtful that something does not leave your mind if the principle of that something becomes clear nothing will remain in your mind this is what is meant by exhausting all
knowledge and mastering everything and so to skip like three paragraphs and get to the bottom it says that is the ultimate end of all disciplines the final state of any discipline is where you forget what you have learned discard your mind did accomplish whatever you set out to do without being aware of it yourself you begin by learning you reach the point where learning does not exist that's friggin awesome and so in previous presentations I quoted a master you know Grandmaster chess player and I wish I could find him cuz I cannot find this quote I remember it from reading about chess when I was really young and he says that to get to his level it was
always like learning individual tactics and techniques and steps was like climbing lungs on rungs on a ladder and that once he reaches a new level a new plateau he was able to kick away the ladder because all those specific things that he learned were meaningless and they didn't necessarily apply to him anymore as I felt like this was another really elegant way to talk about how in the beginning when you're learning things and again this applied this applies really well in my opinion towards hacking that you know it's a very concerted thing and you're learning about very specific things but then you get to a specific point and it all just becomes clear and ended you stop
worrying about that kind of stuff so anyway I thought that was awesome on a final point from this book is something that I'm still I think it greatly really think it greatly relates to that last point about exhausting all knowledge when they talk about this mind that never carries or this mind that doesn't rest on anything in particular and ideas so in the examples they use to me are a little bit confusing they talk about like touching a gourd or something like that but but it goes perfectly in line with that that once once you have a mastery over something your mind does not stick with that thing and it's free to roam in that it's that roaming
process that allows you to continue to be a master it's again it's a very pithy but awesome component so anyway read that book it's freaking awesome and then you know ping me on twit Twitter or something and let me know how you like it alright so what so let's get to the meat of this these are my war stories me and my team my team has grown pretty large since the last conversation or the last uh talk I've presented so this is me and my team if you hear anyone else telling very similar stories let me know so I can hunt them down and kill them so we're gonna go over four specific tests that we were on one was physical
infiltration at a health care organization two was an external hybrid because we're using offensive skills but was in a very like staccato way it was like okay test this okay what did you find you know ask the client for approval okay go ahead keep going and it was part of a very very large encompassing all-encompassing test and I cannot talk about the even the type of place because it won't give away what's he who they who they are and what they do but let's just say they have giant stockpiles of money now we're gonna talk about we're going to talk about an external pen test that was completely open scope against a software company and a really interesting one was
it this is the one that we're currently doing right now what which is breaking the client application alright so the first one physical pen test at a healthcare organization some of the talks are given previously we've broken into extremely secure environments you know basically power plant monitors where we came up with the whole pretext and disguise ourselves as FedEx and broke in and you know brought a huge pallet that was to simulate a bomb this is not that situation this is the exact opposite in that spectrum so when we do tests we always want to gear it towards the specific client and the value that they can get out of it and so the way we
do that is that we simulate the threats that that organization is likely to face so sure maybe someday this specific healthcare organization will have somebody go through the entire hassle of setting up a pretext you know FedEx delivering a thing yeah but they're very very unlikely to face that what they are likely to face is somebody off the street doing something stupid you know maybe they have some technical skills but probably not it's probably just somebody mulling around looking for pharmaceuticals or easy money or walk away with a laptop something like that so we were wanted to stimulate that and so we decided to break it up into two groups two groups of two people to simulate to subtly
different pretext one is people dressed kind of nice you know like consultants tie sports jacket whatever and the other one was to simulate truly two idiots walking up the street jeans t-shirt baseball cap I mean see how far they can get and so we basically kind of drew straws me and and you know one of my guys drew a better one we got the easier one right so we dressed as consultants which again if anyone in gear has ever done any consulting most visible security practices go out the window when they see somebody walking around in a tie and oh you don't need to check in going through so anyway we went in we entered through a side entrance we did
very very minimal recon online normally it's a big convoluted process but again we wanted to demonstrate what somebody with very limited knowledge but would do so all we did was identify the major entrances we entered through the side entrance went up Oh everything was so beautifully labeled in this you know staircases and all this tough east-west staircase so we entered the staircase went to the second floor where there was a sensitive Department of the business go to open it and it's locked start walking I think we're even headed down at that point and the door swings open and this guy goes you guys we go nope we're good and we walked past him and and that was it it was literally no
no other uh contacting the guy so we were in the sensitive area because he just opened the door cuz he heard somebody jingling the handle so that was like a really good start of what was about to happen so we're walking around through departments a couple people's people asked us if we needed help but basically said I continued on we made it to the elevators which were all had hit RFID cards to go anywhere so hit some buttons nothing nothing happens but in true adversary form we tried every single button in there and so sure enough there was one labeled 7r which is the rear of the elevator and it turns out you know at the end of the day they kind of knew
about it that that for some reason could not have key cards to access that that location and so we get up to the seventh floor the rear of the elevator opens up and we get out it's like this very small area and so we're trying to see if it leads anywhere and I mean like super small it's like you know this why that may be that long and that's it in the front of the elevator opens and the guy goes you guys lost him we go yeah I definitely think we're lost it he's like we're trying get through so then we take some floor he's like oh yeah you got to go around that so it's
like a little door over here because like or you can come through this way alright great thanks so we made it to the seventh floor was like a very restricted area walking around so that was basically our experience you know we actually smaller up sensitive areas but but that was it and so for us the real test was what will these you know people that look like any Joe Schmo off the street what will their what will their experience be and we gave them one so I call them legitimacy triggers we gave them one prop that they could use I'll let you guys guess in a second what it was but basically they had more success than we
did and they were addressed I wish I had pictures of them because it was literally like t-shirt and jeans one guy got a Yankees hat on and one gotta have like a beanie on and they're just they're just walking around and they gained access to way more than we did we literally had timed it so that we could all sit down with the client and kind of review the physical security findings that we identified right then and there and they were gone for the entire meeting cuz they were having too much fun like trying to hit every single room in this building so anyone want to guess what BIA with the prof was yes that's
exactly what it was so see me afterwards the free text at econo as long as you can make it otherwise you think you may get June June 16th cycle free ticket so yeah it's fine but that's literally all it takes in a lot of cases if something is stupid and trivial as that sometimes it's a printed shirt with something says someone like security sometimes it's a clipboard sometimes it's a thing that looks like their badges that has nothing on it but that's all it takes and so they got the same exact questions you know are you guys lost or what are you here for they answered with one thing and then they were good so the unique
thing about that again is that we worked trying to be sophisticated we wanted to know how their people their processes their security guards their controls would hold up against an unsophisticated threat because that's what they were likely to face so yeah that was uh that was a good one
okay so Lotus is not the company this was to jog my memory in case I forgot which one I want to talk about so this was that it was actually external and internal and all these other components for this specific client but we found something very interesting when we did the external piece so like always our research on this organization starts with with very in-depth reconnaissance and so we have a very specific methodology defined about everything that we do every single time to make sure that we hit as much for constant state as possible one of those includes looking at breach data anyone ever do that as part of a fantastic look at all the breaches I mean there's tongs now
Ashley Madison Yahoo there's tons of these smaller ones too so we stockpile them and we search for the target organizations name and especially their email address so anyone familiar with the Adobe breach in 2013 yeah I could cope seen a couple head nods so ultimately it was roughly ten gigabytes I think that was the hot bit of the uncompressed size and roughly you know originally they come out with numbers ever like way lower it was like a couple million 33 million then 150 million accounts as part of this breach and there are some other really really interesting components to this breach and I highly recommend that all of you research that breach afterwards for a
dozen reasons but just go read about it and you'll find some cool stuff anyone know what the particularly unique thing about the passwords and the Adobe breach I don't know what the deal was with those nope not that they were insulted yeah they were encrypted yeah so huge snap but anyone know why that's such a bad thing to do to [ __ ] passwords there you go exactly that's why we use hashing because it's not reversible sure you can brute-force it but that it's dependent on the password encryption if I had the encryption key I just decrypt all of the passwords so on that note it's interesting because there was a lot of research done on what the actual
encryption algorithm could be the key the the mode all that and as far as I understand no one actually ever figured out the encryption algorithm but because from a few stupid choices they made as well we can infer more information about the passwords and even more important than the encrypted form the password was there was another component as part of this leak anyone when I guess what that was who said yes the password hint so I highly recommend you go download this and look at some of the hints it is eye-opening so basically we found roughly a hundred and fifty users now we're at this organization that were a part of this breach and so we looked at
all of their password hints and because all these are encrypted and not salted so again two different technologies but if there were a hash insulted this would not apply but because it were encrypted all of the users that had this encrypted password had the same that use the same password had the same encrypted text so all we have to do is say okay this user has this encrypted password show me every one with that encrypted password and let's look at all of those hints together and you would be really surprised at the number that we can just basically reverse engineer slash guess based on the password hints so a lot of the things were like password is
password or it would be you know dog's name plus one and then it would be funny plus number it's like okay so maybe it's the dog's name is buddy the number is one we tried that so the interesting thing is that out of that hundred and forty we found seven users and this was mind you the end of 2015 beginning of 2016 that had not changed their passwords in three years to this Lotus email system so now we had access to seven users email in Gmail and passwords to log in and start getting sensitive data that way well because it's a Lotus system we also checked forward yes know what the deal is with this see something
laughing yes it's a directory of all the accounts in that Lotus email system do you know if there were any other vulnerabilities that were ever in this yes it does so now we have the entire directory and all of the hashed passwords for everyone in this organization based on breach data from 2013 so this was a big big headache I at the time I think it might have been brought in to half cat at this point but at the time that specific hashing algorithm was only available in John the Ripper and so it took a lot of mucking around because it's also like I was a specific patch that was only by default utilizing a specific version of jtr so I
will probably post this somewhere at some point just to save somebody some some headaches but we were able to basically brute force a passwords all again stemming from from that brief data so why was this unique we've utilized other breaches before this was the one that I think was very kind of like you know head on the head on your your forehead kind of thing cuz I was like you had three years to just force your users to change their password once and this might not be an issue at all so we thought that was a that was pretty unique help how bad that was so any other questions relate that one go all right so this is external pen
test at a software company where they said that they had they said that they get annual penetration tests done as required by Google because they develop software for Google and when I asked him what types of results they got from previous pen tests and I hear BS answers like oh you know the typical like you know certain issues an SSL issues and I'm like like I'm like we're gonna wreck this company if that because clearly what that was was a company scanning them with a vulnerability scanner printing it out saying there you go we weren't able to do anything and so this is one of those things that really helped highlight the difference in in my
mind and in the clients mind the difference between a vulnerability assessment the penetration test
so as usual starts with reconnaissance enumerated as much of the technical infrastructure as well as the human infrastructure for this organization as part of that we identified some web applications that they hosted that were exposed to the Internet we could register for accounts generic user accounts on those applications and gain access to them without any type of manual authorization so we did that or poking around we identified only one system that had sequel injection vulnerability we were able to dump the entire database including the user table so we saw a bunch of users at this target organization that had credentials in the system so okay let's go about trying to crack those we have a pretty awesome
password cracking rig it's six GPUs I think right on 9600 or something like that so it's ridiculous speed we were able to crack all potential there was md5 they were unsalted and we were able to exhaust the eight character upper/lower special key space within I think like two or three days we're at that point we cracked about half of the people at the target organization and a couple of them were were mentioned online as administrators and marked in here as like a so we took that we said okay let's see if they reuse these passwords anywhere and so they had Google hosted email so we log in their email poking around looking for keywords like VPN remote password we found a
bunch of interesting stuff but not as much as we usually do some of the most interesting stuff we found which isn't typical is that we found a lot of SSH related key data so it wasn't necessarily private keys but it was information about authenticated SSH on some of the servers they hosted but they were not accessible to us so we said okay let's uh let's take these credentials along into other of their web related assets and see if that gets us anywhere and so we logged into one system which we had also created a user account on but now that we logged in with an admin it gave us new functionality and so again without
giving too much information away you're able to run jobs against data and there was a it was built into the into the web interface but I'm not necessarily displayed by default which allowed them to essentially debug that job which was run in Python or another language which is very own comments I'm not going to say so anyone see any issues with no one Python from a web interface or never exploit that alright see you have a head nod all right cool well that great it's super easy and so basically we say okay looks like this admin account can execute arbitrary Python code let's see if that's the case so the first thing we did was just tell it to
run hang against a server that that we host and we watched for the DNS lookup and so sure enough we see a DNS lookup it's like we should have arbitrary Python code execution and so Metasploit actually has a module for delivering a meterpreter payload the Python so we're just used that spawning up on our external VPS server through the payload at this guy and sure enough we got some interpreter so we were on what appeared to be an internal server not necessarily on what looked like a DMZ because we had we can see a lot of stuff so one of the first things that we did was just run TCP dump fought for everything that was
not destined for for that for that host so we get a little bit of good recon information about that internal network and so one of the things that that we specifically look forward to help identify the domain related information was DHCP know like what we might be able to see in DHCP to key things so we get name servers and we get the net BIOS version of the domain so if it's like company XCOM then they're then they're NetBIOS name might be like CP x you know it's a shortened version so we needed that information to identify where the domain shows might be something can target those specifically so this was a particularly interesting one so we used
that to laro LDAP or Dan we enumerate via Active Directory all the user accounts and you need a valid set of credentials to query LDAP but any credentials within the domain will work so we tried all the credentials that we had from the sequel dump from the web application and sure enough not only did the ones we use to compromise that web application via Python they worked but we actually had a domain admins password that was the same as that web application sequel dump for Active Directory so we were able to immediately authenticate as a domain admin so at that point it was basically game over we pilfered a bunch of interesting data their source code large government
contracts and data with marked as confidential and yadda yadda the interesting thing was that the client had no idea that that component of the web application which ran the Python code was even attached their internal network he's like oh yeah that shouldn't be the case yeah I should know it's not supposed to be within the case so that was an eye-opener but for me this is one of those stories that helps really solidify the difference between a vulnerability assessment and a penetration test and again I don't care at the end of the day what you call it you know depending on the specific scope and methods that we'll use it's everything from a pen test to a Red Team engagement but you
know offensive services so if you look at what would happen in a typical vulnerability assessment they won't have gone to the point where they said hey we got identified a sequel injection vulnerability you need to fix that and that would have been it might be the end of the story okay well what's the real risk to our organization and they might even base it solely on what's in that application and say oh you know what this has public test data it's meaningless if oh if a hacker were able to gain access to everything that sequel database we really don't care and they might not tell you don't maybe they'll patch him and they don't but it doesn't
necessarily change these other practices that we can't identify unless we continue to do the same exact things that a real-world attacker would do like crack the passwords and see where else those passwords are being utilized so again we never would have identified that they have very poor password practices if we didn't take that information and continue on with it and that to me is the again the number one difference beyond the the quintessential answer of you know in a Pentax you exploit vulnerabilities and then a vulnerability you don't this really drives on that point that it's far beyond that it's far beyond yeah depending on the engagement I'm not saying that you wouldn't use a
vulnerability scanner or anything like that I'm saying is that in a vulnerability assessment it's exactly yeah their ultimate their ultimate goal is to just identify as many more boys as possible but you don't understand the real risk and what an attacker would really do if those vulnerabilities remain open so again this highlights that that organization might continue to develop software or SQL injection vulnerabilities but now they understand that it can be greatly exacerbated if they don't have unique passwords for each of those systems so again we're driving home things that we might not otherwise be able to identify and so again you take it a step further you say during a vulnerability assessment maybe you did even uncover that and you said
oh you know what make sure you instruct all of your people to not reuse passwords and so fair enough maybe that does even have some impact at that organization but we demonstrate the real impact and we do change attitudes because we have conversations with all those admins afterwards we say this is why it's so bad this one little vulnerability here web application leads me to everything you care about and so that behavior needs to change and so sure enough not only did that change but some other seriously
so rather than man you want just go right down that rabbit hole don't you yeah so let's come back to that because if there's so much of that but I would say the short answer is it comes down to two things one compensating controls and defensive death so if you can do multi-factor authentication then clear you should be doing that but to it more importantly is using SSO in related applications seems fine the problem here was it was an external web application with junk data so why ever have the same authentication capabilities as something that you really care about like your internal servers that control the domain and have access to all your data all
your data that's the big thing so but if you want you come back to it because it's awful we had the conversation yeah all right so the next slide is our Daily Double first person to tell me what this is from gets a free ticket well who said it yes all right that's nothing to do with anything you know from our free ticket do you think you can make it in in June if not you can always like sell it or give it away but cool awesome please do them alright so any other questions about that software company external cool okay so the final one we did and I think you guys might like this there's some cool
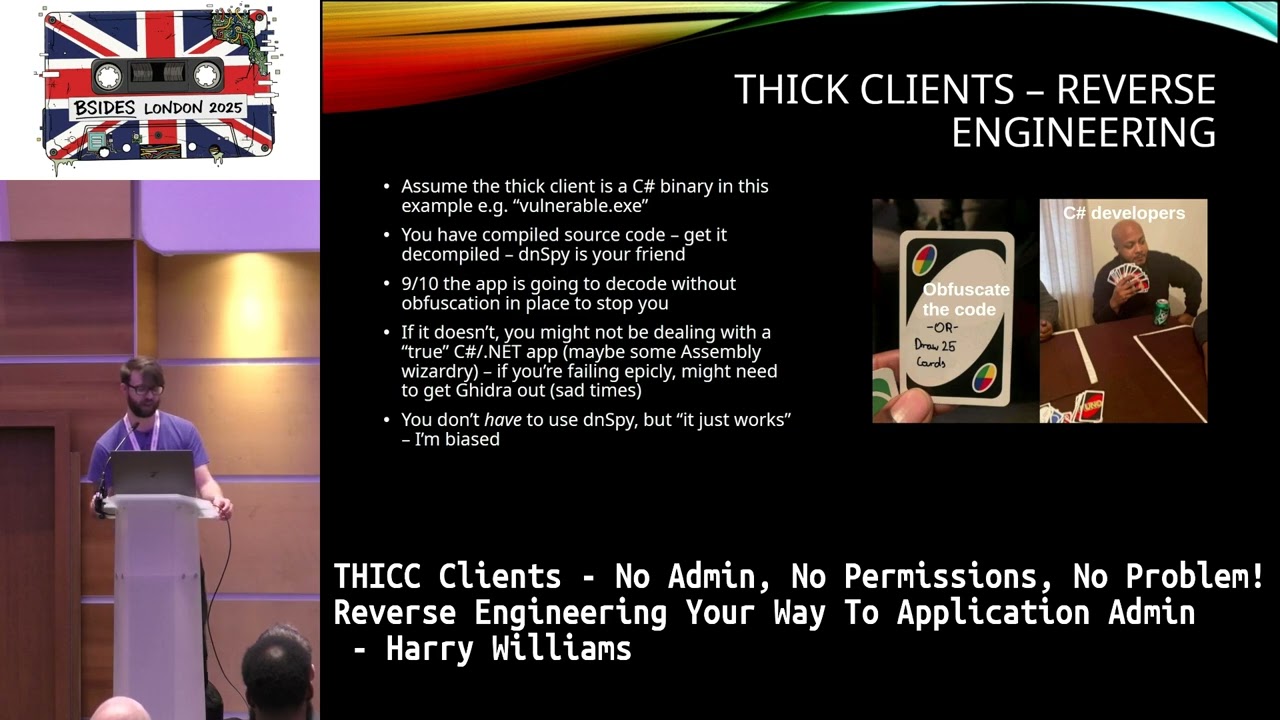
similarities what you guys are talking about um is that we were contracted and again this is ongoing Monday morning when I get back to the office we're going to take what we hope to be the final step in an exploitation of this guy but so the first step for us was to go I've never done at the client before we've done plenty of web applications we do a ton and I've played with stuff related to client-side software but I've never specifically been contracted to target a very specialized thick client and so you know this was a great learning experience for us and so honestly one of the things I love most about testing is that literally a test does
not go by where I don't learn something new you know I mean I met them I've been doing this for professionally I think almost 18 years more as a hobby I still every single time so anyway this was a whole new world it was like okay cool we're gonna get to do a windows-based thick client application did some research on it initially to see what other folks had done and there isn't a lot out there it seemed like there was maybe one or two decent papers but it was all the obvious stuff about debugging and compiling of Brookes engineering and all that stuff and and it didn't get into what I hope to be you
know a little more specific things to testing thick line applications so we started with the obvious stuff mapping the application discovered a tool that was new to me API monitor which was an awesome tool allows you look at all the different API calls made from that application and you can narrow it down based on specific categories like crypto encryption hashing compression other areas and so clearly we started with things like authentication and crypto but any one I digress and so we mapped it it's a very very basic application it actually doesn't it does a very very small number of things very quickly very well and it's all related to gigantic stockpiles of data and so the
interesting thing is that it's a read-only application though so I only asked the server for information displaces the user and that's it and so that attack service seems relatively limited to us so one of the first things we wanted to do was look at this network protocol and see if it used some sort of standard so the first thing we learned after grabbing the the network traffic was that exchanges RSA keys so it exchanges public keys from the server from the client and then excuse me then after that everything was in clear ducts so it literally only cared about utilizing that to authenticate the user and so we identified early on there was an md5
hash with a with a assault unfortunately all the interesting things was that the application handled that internally it did not use an external dia yeah well so I made it kind of not just to find quickly but we were able to identify early on based on the day that it's sent to the Crypt encrypt function which is part of the windows API what looked like a hash and the way we did that was we authenticated as user and I grabbed that via API monitor it said okay this is the whole call to cryptic crypt this is what gets encrypted and set over the network and then we tried a password that only had a one character difference and we've
noticed the blob that changed maps the length requirement of an md5 hash so that's how we quickly identified okay that's probably gonna be five is probably doing it internally to the application and not via DLL because it's not making any calls to to to an API that we're watching oh so anyway that was interesting we clearly alerted the client right away you know we have a ongoing we alert them to issues as we find them Hey so just get feedback and say does this jive with what you guys believe to be the case you know so we're not wasting time spinning our wheels so gets gets worse they said oh yeah yeah we're aware of that because
we have encryption turned off right now on the network side because we typically force users to go home or VPN we basically rely on that we have the capabilities within the application to encrypt network traffic let us turn that on you guys can focus on that so they turned it on and facepalm across across different user sessions it uses the same session key anyone see any issues with that can anyone explain what the issue is yes short answer encryption is completely moot so if I can decrypt any traffic from any other user because we all share the same session key what are you talking about that's not encryption so we identified that early on and then
also identify this part of that process that they use the same IP anyone know what the IV stands for one does all right you all know that one yeah initialization vector and so not only did they use the same IV across all sessions guess what it was well zeros so so five times I'll tell you the most hilarious story after this but but yeah so those two design decisions were something that we never ever would have expected it's like this is the most basic thing like give your users unique session keys yeah anyway I digress break it okay so then so we know that there was issues about the encryption they're still working on figuring out that issue
patching it but we wanted to understand the actual content of the package so we know we can read it and clear text but we've got to understand it because it ultimately looks a lot like binary data with some ASCII text in there and it's hard to really understand what's happening between the client server so the first thing I did years and years ago I'll wrote a bunch of programs using lib pcap and C to sniff traffic so don't set off the cobwebs on that stuff wrote a quick easy thing to basically read in a pcap print out the relevant components of that of the TCP data and that allowed us to create AC structure to say you know what
these four bytes look like they're related to this and we'll print it out in this way these bytes look like this and it was actually a really quick process for us to identify the inner workings of this protocol and so frankly one of the people I was working with on this C super-smart he picked up on some stuff really quick and we noticed a header that was consistent across all communication between these the client the server so it's really obvious which packets we care about so there was always like this this magic header and then after that like the first eight or ten bytes he got into chunks that would you know cycle through all these
different values but by creating that program and printing out the areas we cared about was we were able to very very quickly see the patterns in those and so the patterns that we saw were things like okay the the client requests a data by filling in these fields and it has these other fields set to zeros and then when the server responds it fills in those fields with its values but it's the clients values match and so we're able to quickly identify things like and I think control commands so where the where the the client was making a decision I want this thing this blob of data and this is the control number for it and so most of that was in two bytes
and so it would be simple things like you know number seven number eight and it would go through a series while authenticated cycling through these different what we thought were commands we also quickly identified that in addition to the TCP sequence and acknowledging acknowledgement numbers it had its own internal component for that so the client will go through and for each unique request it makes it just basically increments this to byte word by one and so we're getting a good good idea of what this what this communication pattern looks like I request this data my client-side sequence number is 20 I request the data from the server it tells me it's sequence number which is 423 and then
okay when I get that back I respond against okay now my sugu son one and so we can see this really easy exchange happening and so we had a quick conversation with the client said hey this is what we're seeing we want to make sure those jobs with with with your expectations of the protocol and basically what God is it kind of sounds right but it's all proprietary we're not going to acknowledge or or disconfirm what you are telling us some kind of stuff but anyway as you can see didn't really make a difference so next we wanted to move on to replace packets so we think we understand the general structure for making requests from the
client to the server now I want to see if we can forge those requests for a couple different reasons not the least of which is if I can take a high privileged user sniff that traffic again all the session keys are the same so I can decrypt it and replay that to the server as a less privileged user will they get backed-up sensitive privileged data and so we had to we did a lot of research to identify an existing tool that would work to do this and we found the only one that looked like it was there kind of - and we threw header capped out because that was a mess the last time I tried to use it years and
years ago I just never was great about manipulating packets in real time and so there was one burp no extension no HTTP proxy extension something like that which looked really promising we've got burnt Pro licenses so we threw it in but no go was like a kind of a headache we spent like a day Johnny get to work and it's just just not doing what we needed to do and there was a professional something that was built like kind of to look like Wireshark but it was it was a a they had a free trial version which didn't really seem to work and it was just a hassle to do so he said screw it let's just try to write
write our own thing and so the first thing we did was we utilized the program I wrote in C to just implement the right functionalities that we could read in packets that we captured from a peak app and just replay them and so this was an awesome learning experience I used to teach years and years ago and we get deep into know TCP connections and all that and so it was crazy to revisit all that information and put it to practical use and so there are things that you know you know completely new to me and and that I had to relearn to implement something like this so the first was dealing with the sequence numbers and
the acknowledgement numbers to get them to Jah because if we captured those those requests from the valid client those specific TCP sequence numbers and acknowledgement numbers would no longer work so we had to set up a live TCP connection and edit those to match where they should be so using the Linux I think we use the hex editor command and which I think was pretty again hopefully there will be a white paper after this but we utilized that to just mark a couple of specific bytes change those manually typed it into our program replay the packet and Yurika we can get we can replay any packet that we capture to the server and it will respond with
that legitimate data back to us so that was pretty awesome so so again it's similar to what you guys were doing with the alarm from a network perspective is that we can just you know wait snip this stuff and and replay it across any TCP set session it we're good so the problem is is that that was way to owners you know we can't go through and manually hex edit all these packets to get the type of attack scenario that we want you know basically what we're trying to do now is change the privilege response from the server instructing the client hey you have access to this type of functionality within the interface interface because some of the some of
the menu options are grayed out for the lower privileged users so we want to see it is there an easy way to spoof that response from the server and vice-versa to make both parties think that we have more privileges than we do and so we can't do that manually and so we did a ton of research and the best option look likes copy and I was I never learned Python before this engagement always makes me feel like an old fogey but I use seed pearl that generally accomplishes everything I wanted to and it was really reluctant to learn Python until I learned Python and it is freaking awesome the thing that like was the the big eye-opener was when
I needed to search an array for a specific value which in Python is a single line of code and in C it would have been like probably 10 or 15 depending what I need to do it more I was like literally I'm like looking around the keyboard like oh I feel so dirty like this is so if you don't know Python learn Python it's freaking phenomenal so this specific module and a few which was also new to me is a way to instruct iptables to pause specific packets and only Ford them or drop them based on your manipulation of that queue so again I don't have a perfect understanding of mnq that's kind of like
dumbed down version of it it's new to me we're still working on it but we did now that we had that capability we can edit packets in real time using pythons copy so we I will at least post you know a very generic version of these programs and scripts so that hopefully other people can find good use from them for them but we were able to use all the basic functions within escapee to flip the bits around that we need to to attempt to do specific things and the best part about that is that by doing it that way on live packets we don't need to mop with sequence and acknowledgment numbers because we're just changing valid
packets so again we're sniffing a packet from the client that says hey I'm on Tyler I'm trying to login server is gonna respond and say ok Tyler you're good to go but you're a low privileged user we're trying to change that say you're a high privileged user and see what happens so anyway we tried that we're in the beginning stages of that what we see we've seen success mocking with the data requesting legitimate data we get it back to support because on time so we think that we are right on the cusp of being able to basically access any data within this application with without using so that was unique for a bajillion reasons both
of which I just covered but again hopefully I'll have a white paper out soon yeah sulla than that that's all I got if you guys have any specific questions no still not use my grandma no no close close one time for that but it's not enough to break my ankles so yeah good question did you have a question the demon sermon gracias oh cool no one else awesome
[Music]