Your Key is My Key - Breaking Key Controls
Show transcript [en]
This afternoon, uh, we have a evil demon and he's going to go through your key is my key. So, thank you.
>> Hello. Hello. Oh, perfect. Hi. Uh, yep. I'm able. Uh, quick to save a lot of headache. This is going to be 63 slides. This is the entire slide deck. If you want to take a copy of that, just in case I go too fast for you, feel free to. Uh quick run through and what we're discussing is just a basic primer on locks and keys. Uh your keys are my keys and math manufacturing starts again aka industrial society and its consequences. They crossed what with my keys abusing master keys. Is this actually practical? Does this happen? And kind of debunking what I keep hearing from clients. So quick run through. Uh that's me. Uh I
day job as a pen tester. I do internals, physicals uh externals and yeah, I do a bunch of stuff. You'll usually see me running around doing like physex stuff at cons uh, and most of the time you'll see me outside of places taking photos of locks really carefully. Um, and unlicensed tools every once in a while on like doing access control stuff, so anyone can do it. Anyway, quick primer. Keys are physical objects. Yes, I know. Amazing. Um anyway, the basics of it work like this. Key fits in lock. If it's the correct one works, it unlocks. If it isn't, it doesn't work. And the thing that you need to remember is just it's a physical
element that's doing this. It's designed to be repeatable. Once you figure out those two, life comes a lot easier. So, quick terminology. This is called warding. It's the physical shape of the keyway as it goes in. The idea of this is that different keyways have different warding. This also the difference between restricted keyways and non-restricted. The next one is profile. This is what your keys are cut with. This is the this is the most common one. LW4 LW5 in Australia. Really popular. You'll find it everywhere. And it's just the shape of the other side. Inside lock. You've got key pins. These are the things that actually decide the pinning. If you ever wonder what the chart is on the right
here, that's the actual sizes of all the key pins. And this will make more sense why I'm talking about it now. And the next side is bidding. This is the actual cuts in your key that map out to your key. So the pins match the bidding. The bidding opens the lock. So if you take an incorrect key, put it in your lock, you'll find that it won't open. It will just be set like this. And you'll see how if you look closely along the pins here, they don't line up. The correct key gets a nice straight line all the way across. And that means you can actually turn the lock and open it. So, some of you might be thinking,
hey, if that has the key material, can I just open it up and figure out the key? >> Yes, >> this is correct. Uh, and there's methods to opening locks without keys. Uh, my personal favorite being Joss. He loves to show off impressioning. Uh, this was 1 minute and 43 seconds from a blank key to opening a lock with the key. Now, for the fun stuff that people actually came here for, probably common keying. This is where my key is probably your key. Basically, industrial society sucks. We all know this. And what happens is mass manufacturing means that a lot of keys are going to be non-unique. And sometimes that's on purpose, sometimes it's not. If you want to go
back to previous talks, I talked about elevator keys and all that. And this here is what sits on my uh my shelf. This is what I carry around on me. If you ever wonder why my bag is so heavy, that's why. So, quick quiz. Who can tell me what this key is? >> C7. >> Yes. Oh, C751. >> This here is the most common key used in US manufacturing, etc. At one point, I was just dealing with a friend's trailer and opened with the CH751. He's never even known that. This is a great image from the CH751 subreddit. Yes, that's a thing. This cabinet opened with the CH751. It had three CH751s inside of it.
>> So, let's talk about less notable ways that you can notice common keying. These are two different locks at two different buildings. And I love these ones. Some of you who do physicals a lot might already know what these are, but these are mostly filing cabinet mini side panel doors, places where you might leave your servers in a building. Who's to say? And they got these nice little markings on here saying like one and all these numbers here. I'm a bit of a nerd and I spend a lot of time doing advanced hacking techniques like searching eBay. You can just buy the lock and the key. It's not that hard. Uh, and they even have really nice guides on how to which
ones are mastered to which. And you know, you can get the key for that specific lock. Or you can buy the master. You want to spend a buck and get into pretty much every random server room in modern buildings. There you go. So, you know, it might be nice to get into a server room or something, but I want to get inside the actual building. So, little bit of a story. That's a spoiler for later. I was on a client site for a physical and you know, I was walking around looking and I saw one lock that had a stamp on it that says KA5. And I've never heard of the stamp. Made no sense
to me. No idea what it was. And it was weird. I looked it up. This is what I found. It was a company called Bravo. Very popular to get a lot of these locks and it had a really interesting line in there. Key to like. Turns out a lot of buildings in Australia when they get a cylinder installed, when they don't want to get a master key built for all of the building, they'll just go, "Yeah, whack whatever locket you want in there." And if you see this little brava stamp on the front of that lock, this is the first five of them. There's another five after that. It will just open. The answer is yes. This has worked
multiple times. >> Too many. >> So let's talk about a little bit more about where common key is practically done on purpose. This is one of my favorites. This is a utility box. And you'll notice it had a little stamp on it. Says W. Usually this is used to denounce different things in different places. This is called the Western Australian Standard Key. Now the idea of it is that if you have a company and you go, "Hey, I need to get into this meter box or this water area. I want the utility company to get in." They'll put this block on their stuff and say, "Yeah, you can open it." And you know it's supposed to be
restricted. It's supposed to be like oh you know utility company is the only one who has it. So you look on places like Reddit and you see that people are asking where can I buy this.
>> I'm going to save you all some time. We don't sell that anymore is the word I got. Called a locksmith and they said 150 bucks. uh locks in a supplier is like 40. And some of you might have figured out, yeah, you can just derive the key by opening it up once and figuring out the lock. And depending on where you are, that might be your initial access into the building. This is pretty common just to see boxes like this where you can just open it up and you've got a way into there. So, talked about common keying. Let's take this to the next step. And this brings us to a story of another
physical. This is not the actual lock. I have to say that very clearly. And I was walking around, found some kind of private areas, back of the house. No one was looking. I saw a utility closet stamped with the company identified keyway that I saw everywhere else and a utility key I already had. Now, this is what's referred to as cross keying. The idea of this is you take one key and you take another key and you make them work on the same lock. This works very easily. The idea of it is basically that you put little things referred to as master wafers inside of the lock. Now, you can see it from here that there's these little pins floating
at the top. These are the master wafers. If you ever wonder what they equal out to, those are the numbers. High level, instead of having a key pin that has a seven cut in it, you split it into two pins. So, a three cut will work and then a four cut will work. So, when you put a key in, you have a little row like this. It won't work. And you'll see how you can actually physically see they don't line up. And then once you add the wafers, they all line up perfectly fine and they're all flush. So, in example lock, we might have something like this. We've taken it apart and we've got these
key pins down here that we know line up perfectly. These ones over here which we don't know the value of and the master wafers up here. So from that we know key A has a three cut, a one cut and a one cut in those positions and key B also has those cuts as well. Some of you might be thinking okay so what if we derive it a little bit more? I took the key A. You can figure out the rest from there because you already have the key and break it down like this. Six minus what equals question mark. Do the same across and you can figure out those master wafers and the bidding
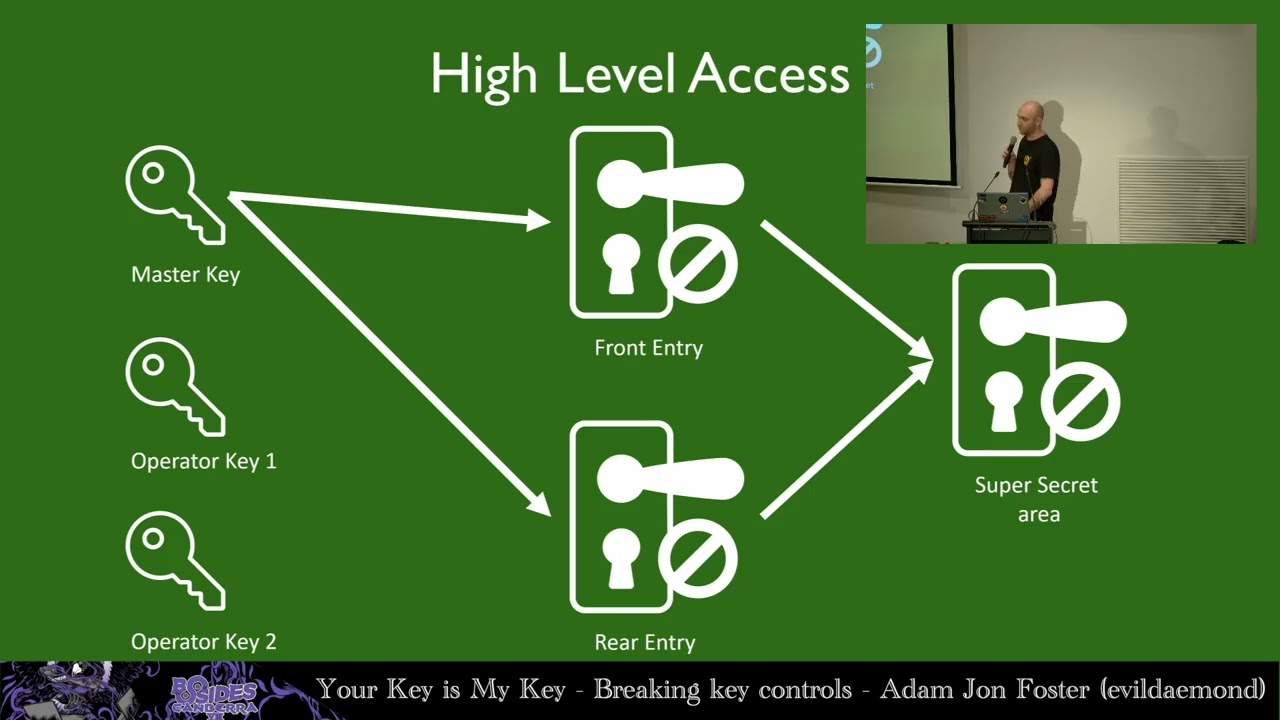
and that gives us your key B. And this is crossing and abusing crossing. It's very straightforward. Crossking is fun but we're going to talk a little bit more about master keying. That's the fun stuff. Let's say you go and you get a building mate. You decide, I want to get all my locks keyed so that I can open them up. They'll do what's referred to as tiering and mastering. So you'll have the first tier, which is your GMK, grandmaster key. This also goes up to great, great, and great. And they just add great to the front of it every time. Then you go down, you have master keys for individual areas, and then you have
your actual operator keys. And the simple idea is that when you have a building, you're going to have something like that. And as you go through, you're just going to go, "This key works here in the rear entrance. This key here works in the front entrance. And the master key works in all the doors." So, think about something. These all have the same key material inside of them. So if you can open one of these just like cross keying unlock the door lock remove the core disassemble the core question mark question mark question mark profit. Now that question mark question mark question mark profit used to be a lot of nerd stuff that you know figuring out
the maximum adjacent cut for each individual key and going deep into it. Um people have done a lot of good work in this. So this is a tool from a guy called Braden. uh he did a really nice talk on exploiting key space vulnerabilities and you can just go on to the website and put in your cuts and where everything is and you'll get something out like this. And this is from before and you'll notice both of our keys from all of those cuts are in there. So now you get an idea of you could take this core, dump it, figure out the master keys relatively easily. But this where we get to the part of the
slides that I always love. Do people actually do this? Um there's some interesting articles you'll find every once in a while pop up. This one here. So, does anyone want to guess why maybe some act, you know, padlocks with some cores inside of a maybe having a key for something might be stolen? I'm sure there's no particular reason for that. Also, if you know exactly where I've taken this screenshot, you and I should have a chat later on. So, let's talk about actual mitigations as well and what people think are mitigations. This here is the most common things I've heard from clients usually that you know this is advanced attack. Attackers have to be you know
really motivated to do this. You know blanks can only be bought by locksmiths and we use high security keys. Only the MLA the master lockmith association of Australia are the ones who can get those. So I'm going to start with the first part. Are these advanced tools that you can do? So, would you like to cut a key? The answer is probably yes. You can spend $15 to $20 on this. This is just a key nibber. It cuts down a key pretty straightforward and you can 3D print some guides. If you have about 30 minutes on 3D printer, it will cut through all of the keys that you want. Do I recommend rekeying your entire
house doing this? God, no. But it works and in the field it's really nice. Now for the rest of it. Pins can be measured with calipers. Economies of scale. They cost like4 to $25 or you can buy a decoder card which just lets you figure out the bidding from there. Just measures it already matched. Tweezers are cheap. Cardboard works as a pinning tray. And in a pinch you can use a rolled up plastic milk jug body as a plug follower to make sure the core doesn't come with all the springs flying at you. Now key blanks. I'm sure some of you might be going, I've tried buying key blanks from Bunnings. I walk in and they
say, get out of here. Well, you're looking in the wrong spots. Just go on eBay. eBay is great. Love eBay. I mean, you could go to eBay or if you have an ABN, you can just go locksmith supplier and say, "I'm an information security consultant." There's no legal definition for information security consultant. There is one for security consultant, so be very careful. But these are like your common blanks, you know, these aren't high security ones. So, this leads to a really funny story. Uh, this is my AliExpress store that I buy all of my high security blanks from. Uh, there's a weird story of finding out how this kind of appears. Apparently, a lot of people will buy locks from
different countries, bring them over, and try to reverse engineer and sell them to a Chinese domestic market. If that doesn't work out, what will end up happening is they'll just fogg it on AliExpress and wait till someone buys it. So, I don't know how long these blanks are going to be on here for. Uh, if you need a restricted key blank, they're on there. Uh, the hardest part is trying to figure out the phrasing they use for it. For some reason, they refer to as uh different warded keys as embryo keys. I'm not sure what the translation is, but these sorts of mistransations and weird terms of phrases appear all the time. And honestly, you're going to pay a lot
more for this than what a locksmith will a locksmith's going to pay a dollar for these blanks. You're going to pay like five bucks each. Now, if all of this is said and done, you might be going, "Okay." Would you practically do this? Would you actually go into a building and do this as a test? The answer is yes. On average, you can field strip a lock with practice in about 5 to 10 minutes. So, if you want to, you can just take the lock, disassemble it, put it back. Calculating the permutations to the lock can be done outside. You can take a photo of the core, leave, measure it all up, come back, go to your office, put it
all in, have a nice coffee, cut the key, and be done. You can also just do it in the field. It takes like 20 minutes. Uh, all of this is relatively straightforward. It's not something that's super advanced anymore. It used to be harder because locksmith tools were a lot harder to buy. Now, it's relatively straightforward. People are making it more accessible. 3D printing has made lockpicking very popular. Lockpicking lawyer has made everyone's Tik Tok feeds look like hell. And honestly, you got to consider the potential threat model. People are doing this for different reasons. There's everything from people want to figure out how to get into their building and figure out what the master key is. You
got dummy uni students who go, I want to climb on the roof. You've got CTF players who try, I'm going to climb on the roof. And yeah, sometimes you have actual physical threats who are like trying to break into buildings. Uh sometimes those are herbexes even. And these are all different threat models that just need to be considered when you go, okay, why do I care if someone steals a padlock from my office? Why do I care if some guy keeps walking in with a blank key, turning in my lock, and then walking away? They're rare. They're not around as much as you would see for an remote attacker, but physical threats do exist. And
that's the whole point here. I'm trying to encourage you to think about how these systems work, understand what these systems do, and think about how do you mitigate that and deal with that problem over time. So, uh, I'm glad everyone enjoyed that. Here's the slide deck if you want to see more of this again. And uh yeah, I'd like to open up to questions.
>> Thank you. Probably what's on everyone's mind. What about house keys? How uh how common are they? Um, in terms of like front door, like we've talked about buildings and stuff like that. Um, yeah. Are they common? Are they crap? Um, in Australia, most house keys fit into LW4, LW5 key blanks or the TE variety if you're using Gainesro. Um, it heavily varies. Um, part of what I target is mostly commercial because, well, residential doesn't pop up that often. From my experience, most of them aren't commonly keyed. But if you're buying $20 locks from Bunnings, consider your threat model.
>> What key would you recommend?
The one that fits your threat model is the best key. >> It depends on how much you actually want to spend. Um, for a lot of people, Ablo Procheek is a great option. There's some really interesting stuff coming out of uh different organizations. Uh, if you want to look at a commercial option, that's really interesting. Cyberlock has some interesting stuff where it provisions keys with certificates. uh that mixes between the physical and the uh and the internet. There might be other problems there. Who's to say? But there's different options. There's a lot of varying things, but it's just understanding that there's there's a threat model for you. It might not fit, you know, having the most cheap
lock available from Buddings as your front door or your building access. Um, have you delved into um the world of smart locks and and yeah um smart locks depending some RFID ones specifically but not a huge amount. A lot of them have already been researched by other people especially IoT researchers. So it isn't a field that I'm delving into too much but most of the RFID ones are interesting to me.
H just wondering if there's been any work with people trying to 3D print keys just as a experiment. >> So 3D printing keys, there's been some interesting stuff in that field, especially with high security blanks. Uh there's a very nice talk by um by beer grad as well who's discussed about 3D printing high security upload protect keys including the interactive elements used for the higher security varieties in most experience it just converts a printed key into a one pin pick for the interactive element anyway. So it yes it has happened. Do I recommend 3D printing your house key? No.
uh is this kind of attack present for like dimple locks, boil locks. Can you still achieve the same kind of thing for different standards? >> The simple answer is you need the blank. Block is heavily restricted. There's not a lot of people who are producing blanks. Uh they, as far as I know, Australian Lock Company produces their blanks inhouse through a stamping process. If you find a way to physically make your own Block key, I'm sure you can do something very similar. >> What about uh the Dimple standard? Dimple lock standard. >> Dimple is the exact same. Um it depend. It's all about finding the blank and finding a way to cut the key at the end
of the day.
Great talk, Adam. Uh, when you're out on the field and you've got the nippers, do you do you find the need that you do you find that you need to have a set of files with you at all or are the nippers enough? >> Um, usually I just use nippers and what I'll do is I'll just wipe it on jeans or canvas pants because that's just deburring it. Uh most of the time I don't need a file. If I was doing impressioning I would. But most my impressioning I just sit at a bench and do that. Excellent. Well, thank you very much for that.