Battle-Tested Incident Recovery: Lessons From The Front Lines
Show transcript [en]
And today we're going to actually take a step outside of my normal world of incident response. My normal world is actually helping organizations respond to and then hopefully recover from an incident. When we talk about incidents in my world, I'm talking about ransomware. I'm talking about business email compromise, advanced persistent threats, and insider threats. All of those types of incidents that you might experience where actually you're out of technical expertise. It might not be an incident you've responded to yourself. With ransomware, we tend to get to that point at the weekend where actually it's been we've been working on an incident all the way through the week. It gets to 5:00 p.m. on a Friday. Everybody's
exhausted and your organization might take that point to actually go we need to get some backup help. So, what I'm going to do today is walk you through actually unit 42 very very quickly touch on where I come from, what I do, and what uh we were actually put in the place of the organization to do. I'm going to take you through a couple of highle threat insights to be able to say what we're observing on a day-to-day basis. Walk you through an incident, how that then corresponds and how we look at them ransomware as a whole before I'm then going to take you through the battle tested incident response or incident recovery methodology and I'm
going to share that with you so you can take that back into your organizations and if you are ever the unfortunate victim of something like a ransomware attack, you can utilize that as a framework to start helping your organization recover. But before we get started, I am going to ask, has anybody actually dealt with a ransomware attack? There might be one or two in the room. Brilliant. Good stuff. That's actually a real step change cuz normally audiences I'm talking to on this topic, they go, "Nobody's responded to it. No one's ever touched ransomware." Which means none of them understand the stress and emotion that Adrian was talking about earlier of actually ransomware recovery. We will
focus on ransomware a little bit in this talk, but this isn't only applicable to ransomware. It could be applicable to other incident types. So myself, I'm Jack Hughes and I'm director of digital forensics and instant response at unit 42. So doing all those great things of helping organizations both understand how a threat actor got into an organization, help them understand exactly what it what it was that they did whilst they were there and then help them onto that next stage of um improving security maturity and removing them from the organization as a whole. So unit 42 was put into uh the PA Palato networks to give them threat intelligence. We have this amazingly powerful technology. I'm
not going to touch on that very much, but we utilize that uh technology to give us insights of threat intelligence. We get to look at network telemetry on firewalls, endpoints, and the data we get from EDR agents and then also looking at cloud surface technologies. And that's great because what we do then is we take all of that telemetry of the billions of events we're looking at every day and look at the threat intelligence that we actually have available to us from a telemetry point of view. threat intelligence team do their wizardry, pull all that together and enable us then be able to go and take some insights from that I'm going to talk you through in a second but
selfishly from the instant response side and I got a few members of the team here as well we get to utilize that threat intelligence to help us really on that uh right hand side there to speed up our services from an instant response perspective so when we go and help organizations it isn't that we're just going in a fresh that we've never seen this incident type before we've never seen this threat actor type before we get to go in knowing who the threat actor is knowing what is likely that they do within those organizations and then we get to utilize that to speed up our response. So what we seeing um and these stats you
can all go and have a read of in the global incident response report and I absolutely advocate going and taking a read of it because it's really really well detailed and well put together. But what we're seeing is that there's a larger number of incidents that are affecting the operations of a a business which is why I want to focus on the recovery today rather than actually the response as a whole. And when we think about business impact, there's lots of different ways that we can address and assess impact or quantify it. But what we're looking at is financial and operational impact. So that being an incident happens and that's either preventing the organization on from
operating as a whole and we'd focus on ransomware particularly when we see that an encryption level events, but we also see the financial operations of organizations being impacted. We've seen some statistics today that talk around the total cost of an incident. There's a huge variety of costs, but they do come down to actually the operations of the organization as a whole. What we're also seeing is attacks happening faster. This one's particularly scary as a statistic because when we think about attacks happening faster, what we're talking about there is threat actor, bad guy, hacker, call them what you want, scanning the internet, looking for opportunities, dropping fishing emails into an uh into a organization, and then
being successful of getting that initial foothold. They then take that foothold and push it forwards into being able to get within the organization, understand it, and then take action on their objectives. And we're getting into a matter of hours now to take action on objectives. Imagine as a new starter in an organization. I know we've got some extremely technical people in the room. Imagine as a new starter in your organization being able to get in and within hours have the privilege to be able to get to the central data stores and excfiltrate it from the environment after having actually worked your way through and understood each step to do that. Well, you as an employee would may
take days or weeks to understand all the SharePoint sites and Confluence sites and HR data repositories of an organization. Somehow they're doing it within hours when they get into these organizations. So speed is absolutely something that we're seeing and they are happening much much faster. We're also starting to see AI or LLMs or artificial intelligence or augmented intelligence as I prefer to call it actually being used as a way of being able to speed up attacks. And what that means and where we're really seeing this is helping organization or threat actors target um and actually take action on their objectives more quickly. So crafting PowerShell scripts, actually crafting those command line interface uh parameters that they're passing and
being able to use that as a way of scripting more quickly and that's where we're really seeing it. On the other side, we're also seeing it being used to create more sophisticated and convincing fishing emails. And that's something unfortunately we're going to continue to see. Advice there is continue to do the great work you're doing on fishing education or spear fishing education in your organizations and continue to use technology to identify and block it where possible. Lastly, and this one's really quite fun, is they are extremely good at using cloud technologies. They're able to get into cloud environments, understand everything that they have access to and take action on their objectives very, very quickly. We see them having more
sophistication in cloud expertise than sometimes the actual cloud providers themselves. is when you have an incident that they experience and you ask the cloud provider and be it one of those large data centers or large global cloud providers and you talk to them well how did they do this and they stand there scratching their head well we don't really know well threat actors do because they're doing it on a day-to-day basis so these are the things that we're really starting to observe threat actors and the way they're operating so why are they being successful well there's far too much complexity in organizations too many individual operating units too many different technologies being utilized Technology is the real focus here. There
was an IBM survey that recently found there was 80 is it 83 solutions from 29 vendors in organizations of on average. How does a security operations team actually stand a chance of monitoring all those technologies at one point in time making sense of the data making sense of the alerts that are being generated and then hopefully taking action upon those alerts that are being generated. They don't stand a chance. We're also seeing that we don't have enough visibility. So great that we might have a comprehensive um uh roll out of an EDR technology and a comprehensive would be a nice place for us to be. Um we don't tend to see that. But we also know from an external facing
perspective, how many of you this would be a great fun question. How many of you would actually put your hands up and confidently say you know exactly is what internet is facing from your organizations today? I I've got hands up. That's amazing. It's really really difficult thing to do. understanding shadow IT actually the way in which cloud cloud technologies are being modified on a day-to-day basis remote access solutions are being put in place or even worse threat actors exposing new assets onto the internet these are all things that we're seeing so attack surface uh visibility is a real challenge and let's last one on cloud because cloud is still a new technology and it's crazy that we're
standing here in 2025 and saying cloud is a new technology and people are still learning how to utilize it learning how cloud technologies work. This means that the identity and access management solutions or identity access management as a whole for those cloud environments, we're going give it everything because we don't really know which permission set it needs to be able to do what we need it to do and unfortunately we then give accounts far too much trust as part of it. So if we were to have a think about that, how can we reduce complexity? Absolutely something to focus on because that will reduce the impact of an incident. If we're able to get more visibility, we've got more
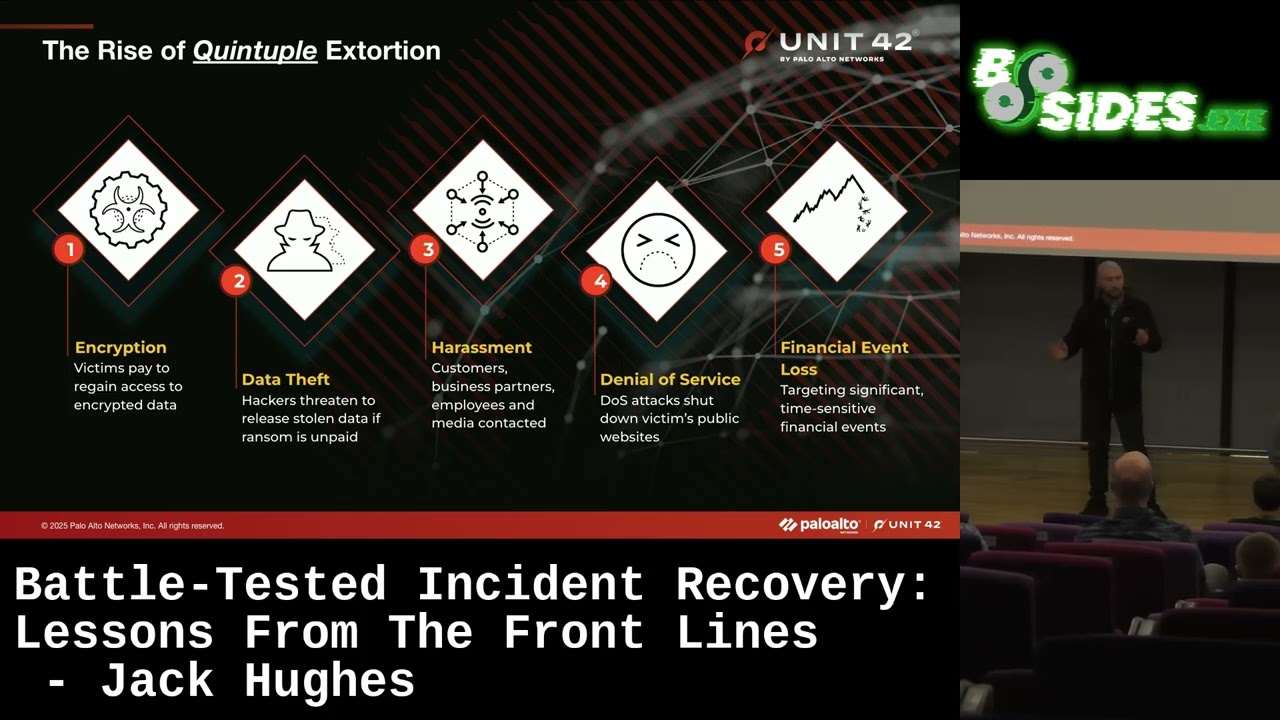
chance of responding to an incident. But when I say increasing visibility, that doesn't mean adding more tools to a situation because adding more tools to the situation increases more complexity. And also, if we can, let's reduce the amount of uh trust that we're giving to any account within the environment because we responded to an incident very recently that had 200 domain administrators within the environment. I would suggest that's few too many. So, we talked about extortion and we're going to talk about ransomware. Um and this is quite good fun because we get to add a new one to this every year. I think last two years we started the three when we gone to four and this year
for some reason we've gone 2025 and it's quintupal ex extortion now ex encryption level events. So when we think about ransomware there's two things that we tend to be focused on. They are confidentiality and availability bringing it right back to the simplicity of the CIA triad and information security. When we think about encryption level events we're thinking about availability. How can an incident reduce the availability of a system? That means that going back to that point, can we pay people at the end of the month? Are we able to manufacture the parts in our organization? Are we able to service our clients? We're seeing a lot of encryption. We're seeing more data theft. As I mentioned, very quickly
threat actor gets into the environment is then able to very quickly understand what they have access to and excfiltrate terabytes of data from organizations at a time. We're seeing that data theft is a huge problem and becoming more of a problem than encryption. The threat actors are then utilizing that as a way of extorting and placing pressure on an organization. And they're doing that by placing harassment in place. So sending flowers to the CEO of an organization, reaching out to your own customers, telling them that they have uh the ransomware has affected the organization or actually releasing this to the media or the best example releasing it to the regulator that you've been affected by
ransomware. things that we're seeing in part harassment claims. We also see and especially where we don't then where you don't engage with a threat actor and I don't suggest that any of you take that upon yourself to go and do if you do have a ransomware attack but if you do decide to engage with threat actor make sure you do it in a professional manner cuz if you don't it's very likely they'll come back and try and um issue with a denial of service attack of some sort against probably one of your applications because they're using as a way of being able to extort you later down the line. And this latest one that we're seeing quite frequently is where
they're taking information or getting access to information that can be used actively on the financial market as a way of being able to extort you because if they are able to identify and utilize that information in a manner that would reduce your financial pricing on the market, they will look to do that to extort funds from you. Think of a fun situation here where actually data theft occurs and they run it through an LLM and then can start querying that data. What's the most important piece of information in this data set? How could I potentially use this information against the organization? These are all implications of LLMs and how they could be utilized against us. So, this will
make a couple of my team laugh because we're talking about Goot Loader. But when we think about incidents and the simplicity of how these occur, we'll actually use a fishing email as an an example here. And all in this case is search engine poisoning. In this case, someone was trying to be really useful trying to find a way of actually conducting a new contracting element. So they were on Google typing in a very very specific contracting term and in doing so they clicked on the website downloaded this really useful document that was actually a hidden JavaScript file when they executed it turned out to be bootloadader. Now in doing so trying to be really useful they
were trying to find this contracting for their organization. They enabled the whole rest of this attack chain. And it comes back to this emotions and the blame. Not trying to blame anyone in this case because there was a lot of technical controls that could have prevented this from happening in the first place. But then this enabled the threat actor to very quickly and I just wanted to step through as quickly get that reconnaissance in the environment being able to look at the cobalt strike actually getting onto the domain controller be able to use mimikats on the domain controller to get use of all those credentials that they had access to. But also look at the timeline here.
We go from June and I apologize it's cut off ever slight on this screen but it's fine there. It goes from the left hand side saying June all the way through to September. Now this is actually a really long time especially for these type of actors to have access to an environment. It's very likely this was an initial access brokerage. Uh so somebody actually got access to the environment and sold that access at a later date before the rest of the attack then continues. For the techies among you, one of the cool things that we did as part of this investigation was to identify the files that had been excfiltrated from the actor. There was a
whole lack of logging in this environment. But what was cool is we got hold of the memory and we're able to look at the application execution artifacts in memory and list out all the files that have been touched by free file sync. Thus giving a really good indication of the files that had been excfiltrated for that later regular piece. But unfortunately they then continue actually after exfiltrating information and move to ransomware. Now ransomware is a particularly scary place to be because imagine coming into an organization in the morning and suddenly this is what you see across the the banks and benches of your organization. Nobody wants to see this and it's really difficult to be able to move forwards
from a ransomware incident. You will very likely not have access to anything in your environment and so you have to then very quickly identify how you're going to move forwards with the incident. So how do you respond? When we think about incident response and what we want to do, we want to very quickly identify what has happened. What we're looking to identify in that initial piece is firstly the technical facets. What can we not do today as part of our business operation? What are the systems that have been impacted? How many systems have been impacted before we then look at the business impact as well? If we're not able to pay our employees, because this has happened on
Friday, could be today, just before payroll is being executed across organizations, and you're not able to pay your employees, are they able to go and pay their mortgages next month? Are they able to make their car payments? These are all very real threats of ransomware incidents. Once we've identified that and we can actually start to think of an approach to move forwards, we then move into the investigate phase, which is really understanding how a threat actor got access to the environment and what they were able to do whilst they were there. Now we think about four pillars of information when we're conducting these investigations around network identity, cloud and application and endpoint because that enables us to give a really
good visibility of exactly the timeline of the incident as it flowed its way through. Once you've got access to that information, you can then move into this secure or contain and eradicate phase where you use all of the indicators of compromise, everything you've understood about the incident to really get rid of that threat actor and ensure they can't get back in. We then might want to move to the restore phase depending on the incident. That's where we're really going to focus today is on restore um and how we get back to operation. But we're going to use um all of the information we've gathered there to securely bring ourselves forward into that last phase of lessons learned. And I heard someone
mention post incident review earlier. And I actually really wanted to ask this question. How many of you have ever actually done a post incident review? That's actually more than I thought I was going to get. I was expecting that to be um hands down to be honest actually effectively performing post incident reviews is absolutely one of the most important things we can do to take those lessons learned and ensure the incident can't happen again. So, question for you. If you had ransomware in your business tomorrow, what's the first thing that you would do? >> My notice. >> Hand in your notice. Fair. Yeah. Could be. It could be something you do. >> Comms. Okay. >> Brilliant.
>> Sorry. >> Call me. >> Call me. Anything else? >> Panic. >> Panic. Yeah, the reality I expect a lot of people now is disconnect everything from the internet. But >> I'm I'm not going to say that's right or wrong actually because it depend it depends. That's one of my favorite sayings here. But nobody's going to use the instant response plan. >> No, because that's buried at the bottom of the drawer. No one's touched it. No one's updated it. And actually, do you even have one in the first place that's comprehensive enough to us for us to move forwards? And I say this in justest, but we talk about instant response plans a lot. When we've
responded to incidents, in all the incidents I've responded to in my time in instant response, I've never come across an organization that actually has and uses an instant response plan. And this either says one of two things. This either says that those organizations that have the instant response plan don't ever call us because they are got it all in hand organizations really aren't taking instant response preparedness very seriously. So, as I mentioned, what we're going to focus on is this restoration phase. So, we can talk about incidents, how they happen, the kind of technical response to them all day long, but we don't very often get the opportunity to focus on business restoration or actually how we respond
to and recover from an incident. So, the first thing we're going to focus on if we deep dive really into the restoration piece is what backups do we have? Now, if I come as an incident responder into your organization and you tell me you have tapes, I'm a very happy person because I know I've got something to work from. I know that even if it's in the bottom of your drawer and you've not touched it for a year, you've got a backup of at least some of your systems to work from. They may be out of date. They might not have the latest stock information on them, but they have something. Because if you don't have any
backups, it's a much more painful place for us to actually work from and move ourselves forwards. So when we think about backups, we might have on premise backups, we might have uh tape servers, we might have backup servers as a whole. Recommendation, if you have backup servers, make sure they're not domain joined because if they do get access to your network, they will go and delete anything that's on those backup servers. You might have cloud solutions that are being used for backups, and that's great. I'd suggest if you have them, you use them in a hybrid manner. So you've got something on premise, something in the cloud, and hopefully you're using a tape backup solution at the same time.
How frequently you should do this depends on the criticality and actually um threat profiling is a great way to think about the risk and how we think about backup solutions as a whole because how frequently we back up. If we've got a stock system, it might be that we want to keep a duplicated data storage system so we know exactly the financial records and where they're occurring. It might be it's not quite as important and a daily backup may suffice. All of these things to consider when we're considering backups and how we utilize them. But backups are not always safe. And I'll give you an example. I had an organization that uh contacted us just before Christmas that
wanted assistance in a ransomware incident. Great. We can definitely help them. One reason or another, they decided that they didn't need our assistance. Absolutely fine. But what they did is they took their backups cuz they had them. Fantastic. Very happy for them. And they restored them directly back into the environment. And we're happy. two weeks of normal business operations, they'd responded successfully to the incident. But what they'd done is they had actually taken ransomware environment and restored the threat actor directly back in there. So all of a sudden the beacon starts going back out to say this this environment is live again. And guess what happened? Well, the threat actor got back into the environment using exactly the same
access they had previously. They then went in and found the backups that they utilized to restore from and deleted them and then ransomware the environment again. So again, an unfortunate place to be, but absolutely something to focus on. This is where I really want to start focusing. Now, if there are no backups, I will say it's not the end of the world. We have had some really really good success in being able to go in to an organization that has been affected by ransomware and we're seeing very frequently and especially in virtualized environments at the moment that actually the data isn't all gone. Ransomware tends to be very quick and dirty in its operation. And what we mean by that is
it goes in, it executes, but instead of it going and encrypting the entire piece of data, and for those of you who haven't experienced ransomware or in this type of world, if you go try and encrypt an an entire zip file, as an example, takes a long time. Even if you've got some real good compute behind it, it takes a long time. So what they do with ransomware is they tend to just focus on the very very first few headers or very few um first pieces of the information in those file stores because it enables them to say that the information is encrypted. Unfortunately the way that file systems work it means that it looks at it and goes n can't use
that. We don't really understand what type of file it is and as such the ransomware is effective to a means. However and we'll go a little bit technical for a second. If this happens in a virtualized file system and happens because it encrypts the first part of that virtual disc rather than the entirety of that disc, what it does is it goes and when we think about NTFS and we really go technical for a second and then we go into a master file table and it only encrypts the very first part of the master file table. Well, the great news is there's a backup MFT at the back of the disc, which means that we can
utilize the backup MFT or the MFT mirror, more specifically if I think about terminology, to then look at the MFT mirror that then tells us where each of the files are located in the virtual ser in the virtual disc storage system. Meaning, we have fantastic success of identifying a way of being able to recover information even when it looks all as lost. I will say don't rely on that as where being able to restore information because firstly might not work and B it's not a very quick process. Tapes are still slightly quicker than taking that um process even though tapes are quite slow. So do have a think about that. So when we're considering incident response and
thinking about how we respond to these incidents incident response is a team sport. It's going to require a businesswide approach. We all think of ourselves as the heroes. We all think of ourselves as way of being able to get into organization and help them move forwards with pace and you can but you can't do it by yourself because you have to be able to identify what the function is of the business as a whole especially in the incident. If your business is producing man or manufacturing car parts that is the primary objective to get that part of the business back online. all the superfluous and other pieces of the business that are maybe not be so
necessary such as and other parts of the organization will hate us for saying this. There may be IT systems that may not be quite as important. There might be some HR systems, a learning and training platforms a very nice thing to have might not be actually the right point to actually focus on getting back online. So think about the primary objective of the business. What is it that they need to get back online to actually come and continue the operation of the business as a success? And that enables us to then think about the minimal viable solution from an operational perspective to reduce the impact to the business and then come forward with this goto green plan. And
our go to green plan is something that is a little bit of a technical um approach. But it means that we then have to start thinking about all these different technologies and what is it that's most important at that point in time. Now it be I put these all these words on there cuz they're all things that people think about. Some organizations will go active directory got to get our identity sources back online. If we come even a step further back from there actually if they're using virtual firewalls are they even able to utilize them? Have they been encrypted? If we come a step back for even further from there and they're using NTP locally, do they have a time
source that they're able to utilize? So really think of the technical constructs of go to green planning and then you start to go all the way and continue about what the planning might be as part of the incident. All of those different systems and what's the order we need to bring them back online. Cyber recovery planning is something that is really difficult to get right. It takes a long time. But as long as you sit with the organization and you start to think about the business who are thinking about the objectives of the business, you're going to have to work with the IT team as an incident responder because they are going to be the ones that are
going to be telling you which are the systems that are most important. What have they got available to them? Do they have backups available? Do they have networking available to them at the moment to bring those systems back online? From a HR perspective, we're also then going to be thinking around are there HR implications of this incident? Actually, are we able to employ our T teams at the moment? Are we able to pay them? Are we able to are there litigation uh that might be needed to take it by the legal team as we move our way through from a finance perspective? Are we able to receive money and actually keep ourselves afloat? But are we able to pay our
suppliers and continue the supply chain of an organization? And this is why we talk about incident response being a team sport and not just a technical facet because all of these organizations and all of these parts of the business have to come together for this to be a success. So I promised you a methodology. So we have a battle tested incident response methodology that we're going to talk about now that enables us to really move forward from an incident and and ensures that even if we have backups and even if we don't have backups that we can bring an organization back safely and securely and that comes from a bit of a heritage of agriculture and when we think about
that I love some of the shaking heads that are going on in the crowd right now but when we think about this this is called sheep dipping now from an agricultural perspective what sheep dipping is used for is that sheep out in a field, they tend to get really muddy feet and over a period of time they become degraded. They become worn away and they get mud stuck in there and they become infected. And so what farmers do is they take field of sheep, they run them through a sheep dip very much like this that contains chemicals that looks at the feet and it really attacks them quite nasty. You wouldn't want to dip your own feet in there, that's for sure.
And at the other end, they come out very clean. And we apply the same principle as a methodology into incident recovery. And what that enables us to do is take an environment that's postbach. So a threat actor has had access to the environment and they've been in there, they've performed an attack of be it a um ransomware attack, be it an insider threat, whatever it may be, that enables us to take this really dirty dirty field sheet field as we're talking about it in this sense and we talk about in the agricultural means, but we're then able to run it through our sheep dip. Now in our sheep dipping environment, what we're doing is we create a clean
environment or at least a semi-clean environment that enables us to take these systems through our virtual sheep dipping this means and we apply security controls, we apply different technologies to this environment to ensure that we take the findings of the investigation and we're able to remove the risk from the environment and that enables us to move forwards and actually get to a point of a restored environment of pastures new these bright green fields of actually we know exactly what we've got in the environment and how we're going to utilize it. So when we think of this as a methodology, the first thing we're going to do is we're going to create a clean environment. From a create a clean environment, this
might be that we create a segregated VLAN. It might be that we create a hypervisor that's very focused on just being used as a sheet dipping process. It may be that we're unplugging physical devices from switches to create that clean environment. And that means that we're also going to remove any interconnectivity between systems bar it being able to reach out to and bar not being used in the agricultural sense there um but actually being able to reduce the essence of it being able to connect to any of those other systems and touching them. But we do need to connect to some security technology solutions to enable us to do that. We're then going to restore any of those
systems or backups into that environment. And we're going to do that, as I mentioned, into that environment, but without any connectivity to any of those other systems. We're then going to install security technology or tooling onto those. And that will be EDR technologies, enable us to collect forensic packages from them. We'll go and potentially take log sources from them. But what we're going to do is we're going to put that safety bubble and wrapper around those systems to perform uh go way back when to an AV scan on those systems or a malware scan. We're going to go and look for any of the indicators of compromise of the incident as a whole. And then we're
going to place it into the next step of taking the opportunity of never wasting a crisis and installing those patches that they've been waiting for for the last 5 years. From a operating system perspective, from an application perspective, from a security perspective, take this crisis and utilize it to enhance the operation as a whole. So that enables us to go from this really dirty field of we don't really know what we've got through the sheep dip of applying all of these security controls looking for how they've been impacted ensuring that they are all clean because if we do identify anything dirty in there it gets removed it gets obliterated and we get to move a
fresh and then we get to move the devices of the pasture new and of a clean network. They all have up-to-date technologies. they all have actually been now in a state where we can monitor them and we can move forwards with a matured improved environment. So thing I will note just moving outside of that environment and I've added a added a farmer on here. There's a difference here is we've now got this beautiful clean environment but the really important thing once I've now got all that technology monitor it and watch it because even though we've brought that environment back we still have to make sure the threat actor doesn't come back and target us again. So the idea of SPS
piece being that we're both going to monitor, we're going to continue to look at the environment in this stage, but we're also going to use it as a you never waste that crisis and improve the security operation moving forwards. So to recap, backups are really, really important. They're not always the only solution. There are other technical means that we might be able to take to restore or recover an operation. Make sure you are using tapes. And I should have asked the question, but it'd be lovely to know how many of you are using tapes. I know that a lot of organizations are trying to move away from that as a an expensive potentially storage mechanism, but it works and I
really would ask you to take that back to your organizations. It works. It enables us to recover organizations. Make sure we're using that 3 to one to one 3 to one backup rule of being able to have three different backups in two different locations and one offsite. Absolutely. A great way of being able to think about backups. Sheep dipping will provide confidence to an organization because you can literally take a list of systems and have a little rag status. So red red amber green status next to it and go I know exactly at which stage of the sheep dipping process I'm at and whether they're actually prior to the sheep dip within the sheep dip or post sheep sheep
dip and now in operations and how they're being utilized take time. Things will go wrong not can go wrong they will go wrong as part of incident recovery. that comes of experience and unfortunately we have quite a lot of that um in the sense of responding to incidents not making mistakes that's not what I'm admitting to here but it does take time it will go wrong but don't waste that crisis and lastly please create and test rehearse and utilize an incident response plan because if you have the plan in place you're effectively rehearsing it and there was a really good comment earlier about law enforcement and the way in which they utilize plans and the way in which they
respond to incidents think of the Coast Guard We're actually very fortunate to be down in Devon and we got the Coast Guard and lifeboats. They go out very frequently to rehearse operations to be able to go and help people and recover from incidents. We need to be doing the same thing in our industry because if we don't we don't have that muscle memory of responding to incidents. We're very fortunate as an instant response team. We do it every day. A lot of organizations don't do it at all. It may be the first time you've ever responded to an incident. And if you don't have that muscle memory, how can you possibly hope to succeed? because I goes back to
the old memory of uh fail to prepare, prepare to fail. And I will leave you with that and happy to take any questions. Thank you very much.
>> Yeah, fine. >> Any questions? >> How many deep mind credits did you use? >> It was um Imagin on uh Google uh Gemini. I was using for the images. Um certainly recommend giving that a play. It's good fun. >> Um as an industry and I think quite a lot failing in response planning and we're certainly failing exercising it. I've seen a number of organizations every time badly. Um I guess a lot of push back you get organizations is you have to introduce disruption to effectively test an instant response plan. How can we kind of I know it's very open but how can we fix that problem that really >> that's a a great question. Um I would
challenge whether we need to introduce disruption and the reason I'd say that is that a wellplanned uh exercise should encompass a a threat informed approach which says these are the threats that are very likely to occur to our business. It comes back to the threat modeling uh that we were talking about earlier as a business. What is it that we're most likely to see? Who are the attackers that are most likely to be targeting us on a day-to-day basis? So that we can then work with actually across the business to understand if you're doing this as an external perspective understanding across the business who are the likely stakeholders to be in involved in that to understand
what the weaknesses are. So then in an exercise there's two objectives. One is to be able to utilize the instant response plan effectively and find where it's failing but also to identify and constructively identify those areas for opportunity uh of improvement across the business more widely as it may not just be the instant response plan. is very very likely a whole raft of technical things that need to be worked on at the same time. So I wouldn't necessarily say it has to be disruptive disruptive as a black um black swan event as a tabletop exercise or a rehearsal. They can be good fun to be participate in from a consulting side, but they are also good
fun to respond to as a as a business as well. Um but planning and and that preparation phase around actually the planning itself is really really key. If you take the time to actually put together a well rehearsed and a well um a well doumented and a threat informed rehearsal that enables you to then be able to move forwards rather than just being a a cookie cutter here's a ransomware attack. How would you respond to this in business in your business? If they actually take the time to prepare for that and go these are the systems that are most likely to be impacted because they're internet facing and they're running really old technologies. If that went offline today what would we
do? And that's what a lot of their plans don't do is they take this cookie cut cookie cutter cutter cutter approach and they bring up slides like I've just brought up to say this is your business today. This is what a ransomware attack looks like. What would you do? It's all very theoretical and it doesn't really work. It's that practical application of what it would look like in your business that I'd look to focus on. Um, I'm not saying my organization is perfect, but I was quite surprised by your reaction to maybe something I would have thought.
Um, so so to me that's that's common sense. I'm quite surprised by your reaction really. And I am honestly I was surprised that I saw hands because not only is it thinking about the the external assets that you might have exposed and you go right we've got some firewalls we're exposing technologies or services or or actual boxes through the firewall at this point but are you aware of all of the um pieces of application what software they're running at a single point in time and actually are they vulnerable and it's an attack service management program as a whole that we consider. Um, so I am very surprised and I I looked to I've got a couple of the
team that are here to or a few of the team here today actually this is where we spend a lot of our time. Last year from the global incident response report um we I think it was 36% of incidents were caused by software vulnerabilities on the secure software edge um and be that firewall vulnerabilities VPN vulnerabilities webf facing applications that's where we tend to see the vast majority of those instance happening and when you ask the organization well were you aware that this was internetf facing or were you aware that it was running a vulnerable piece of software the answer is um more than 50% of the time no we weren't aware of that and we didn't know
it was even internet facing Any
other questions? If not, we're around for the rest of the day. Please grab me if you've got any questions and thank you very much for your time.





