SAP Security Flaws: Default Credentials Exposed! #shorts
Show transcript [en]
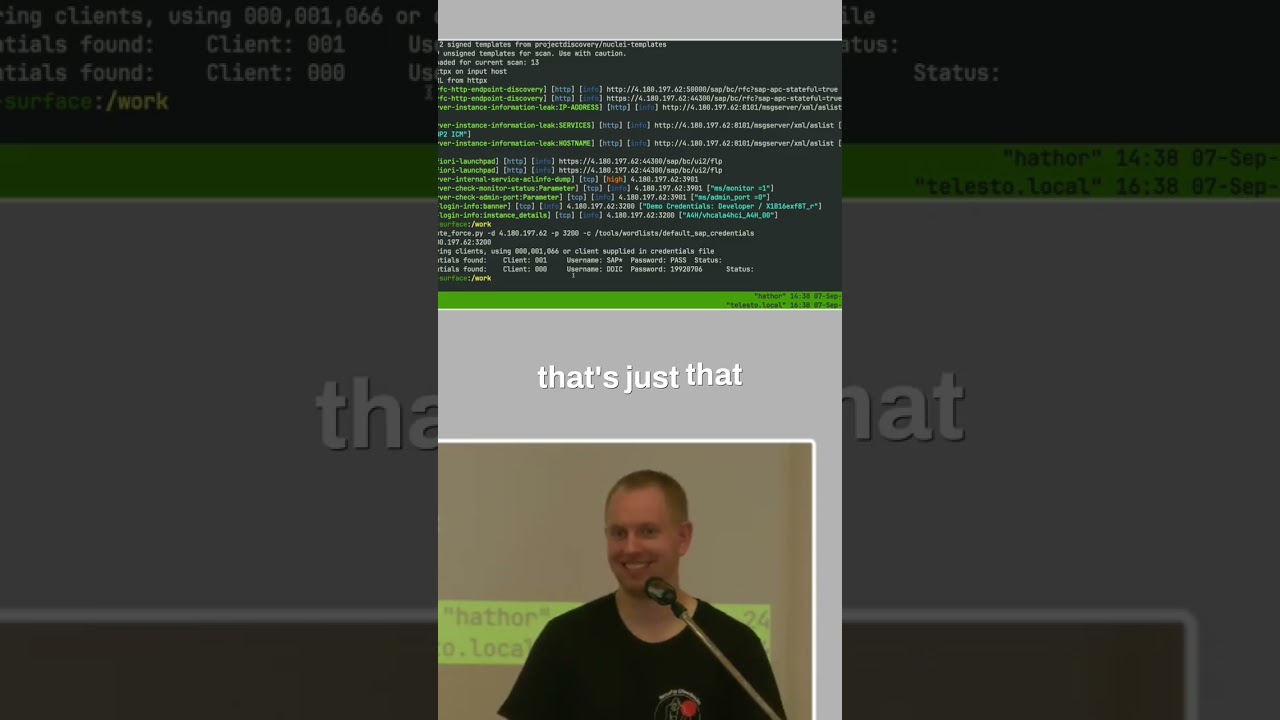
Go into that pie sap. So, there is a dialogue and brute force. And I told you there are some SAP default creds. Google there are they are publicly if not you can also get them in the repo. And what it does it simulates like a client connection and can enumerate all those different clients. If not it uses the default password spray, throws them against because there is defined pairs and say, "Hey, that's the default creds." And you can see we can log in with those. So, they're available like that SAP star and pass. That's by the way the hardcoded password. So, if you flip the parameter and that user doesn't exist, it's hardcoded in the kernel.
So, you cannot delete that or whatever. Either you disable it or it's there. And guess why did it has that password? What happened at that date?
R3 That's just that date. And by the way the other default password for the SAP star is just the same date reverse. >> [laughter] >> 06071992 Um and those are all known. So, that's SAP how it is. And for example that hardcoded sub star um you would think about like an insurance company, they have their security and maturity and they know about that. I did an audit about 4 and 1/2 years ago for a quite a big Swiss Swiss uh insurance company. Was like, "Hey, why is that enabled?" As a fallback. Just saying. So, many people enable that stuff because it could be just a fallback if something goes wrong.





