Making Consistent STRIDEs With Threat Modeling Templates
Show transcript [en]
right hello everyone um this is my first big bsides talk uh my first ever one was on the inaugural bsides Newcastle standing in a skate park half pipe so uh it's a little bit different here being a bit more civilized um but yeah I'm going to talk to you um about possibility of um improving the threat modeling process um using a a free tool um is something that we started using in our organization and uh as I played with it I thought yeah there's quite a lot of potential here so I'm not going to give you something that's finished and Polished but hopefully just put some ideas of something you might want to take and uh and work with if you haven't
got the resources for something else so um I'm Andrea Jones um I'm a lead information security uh product Assurance analyst um and uh I work for big super Market that's our color as well as the bsides uh Bristol color um so Sams bris um I've been in information security for about 10 years um fell into it from sitting in an IT department and head of it com and say you've got an i with detail I'll give you our ISO 27,000 And1 to do um but having had a kind of history of building computers and playing with databases and websites and all that sort of thing um and starting in the days of Doss I used to teach word
processing on dos you might think that's not even possible I run a database in Doss as well um so yeah that kind of background and the knowledge of some of those nuts and bolts I think has helped and I would say it's a kind of a mile wide and an inch deep knowledge but it helps you in infoset because you get so many different things and aspects to look at um so I'm on Twitter if you want to find me and and we do have some vacancies at the moment we'll probably have a few more coming up if you're looking for an entry level position in particular keep your eye on our site for the next few
months you might find a good opportunity coming up so what's the problem that we're trying to address here um I don't know if many of you are building in the cloud nowadays I expect most of you are moving that way if you're not there already um but how many of you look into your Cloud security hubs and see this mass of alert of various issues or you you look at the security score and perhaps it's around 60% or something and it's just because people go ahead and build things and they don't really know what they should be doing in the configuration to get that top score and they don't bother do they I don't know if that's some a few
nods of heads I'm glad someone else is thinking this is a problem as well um so what I'm going to talk about today is really how you can use this tool to hopefully uh improve that posture and that is all part of improving the security posture isn't it because that's where these things come from um so developers they don't follow the best practice they don't read the company policy to the letter um often things get past the people who could tell them what the policy says um so it's often too late and it's very expensive to sort these things out once you've built the final product isn't it um and maturity is hard isn't it we know that looking at
our kids growing up I always use laundry bins and putting your clothes in them as an example of a maturity model um I think it's a very good likeness so what's threat modeling um how many of you do threat modeling it's have a show hands yeah we're around I don't know maybe the 40% Mark something like that so I'm glad there's quite a lot of you who don't do it and perhaps don't know what it is um it's a very good thing to do and can be very very helpful so it's performed at the design stage or should be performed at the design stage of the um security development life cycle security development life cycle is
something Microsoft have developed um but there's also a design stage on the systems design development life cycle as well so you start off with your requirements um and specification and then you go through to your design and so on and obviously if you get to production and you then find out about all these problems that's where expense comes in um a few helpful resources for you the Bible of threat modeling Adam show Stack's book threat modeling designing for security that's got some particularly helpful appendices in it as well very worthwhile investment um there's the oasp pages on threat modeling they also do some paid training courses if you really want to get into the subject then you can go on
one of their courses and get a really in-depth um instruction on how to do it and um the Toran threat modeling Playbook can also be quite helpful some resources there that you can use so we start off in threet modeling with a diagram um show what there is that we're building uh the process then goes on to identifying threats mitigating the threats and validation and uh often this is rep represented as a circle and some threat models Frameworks throw in a fifth element as well but um uh the whole idea is that you don't stop at the validation because you go back again so the whole thing is what do we building what could go wrong
in it what can we do about the going wrong it's no good working out what can go wrong if you don't then work out what you're going to do to solve the problem is it um and then did we do a good enough job so if you didn't do a good enough job if you're not happy with the finished result you go back to the beginning and you work through again and you work a little bit deeper next time so looking at the maturity side of things um this is the oasp security security assessment maturity model think actually software assessment maturity model but it's called Sam um I think someone else mentioned this earlier and
you can see here that threat modeling comes in under the sort of design pillar of this as well but again o has a lot of resources on threat modeling and maturity as well so maturity levels you've uh probably heard of this sort of thing before um but they're generally graded around you your sort of the thing doesn't exist at all um or you've defined a process it's there at least uh but then it's got to get a little bit more mature and you've got to get it implemented and then to get that really polished to be a real ninja in this thing then it needs to be um consistent stantly applied across the organization and properly integrated with your
processes so that you can't get through those Loops now often it's easier to do that by implementing some expensive tool and yes there are expensive tools out there that can help you with that uh but not everyone has the resources for that um or it takes time to implement them fully throughout the organization and you may not be able to implement them in some aspects and so threat modeling you can apply it to any systems and you can apply it to multiple systems from multiple Technologies joined together to look at that and there's the descriptor for level three of where you need to get to to be in that real sort of ninja state with your threat modeling and um I think
the thing you know the very last paragraph there about automating parts of the process using threat modeling tools so you know trying to do it all manually with pen and paper yes it's possible but it's not easy to get that ninja consistency um doing it that way because people forget things or they don't realize that this is a different technology and there could be other issues at play here um and all that integration that learning from mistakes um and then building things back in uh someone was saying earlier on an AI talk about taking stuff from the sock and how they dealt with tickets and building it into an engine well you can do the same
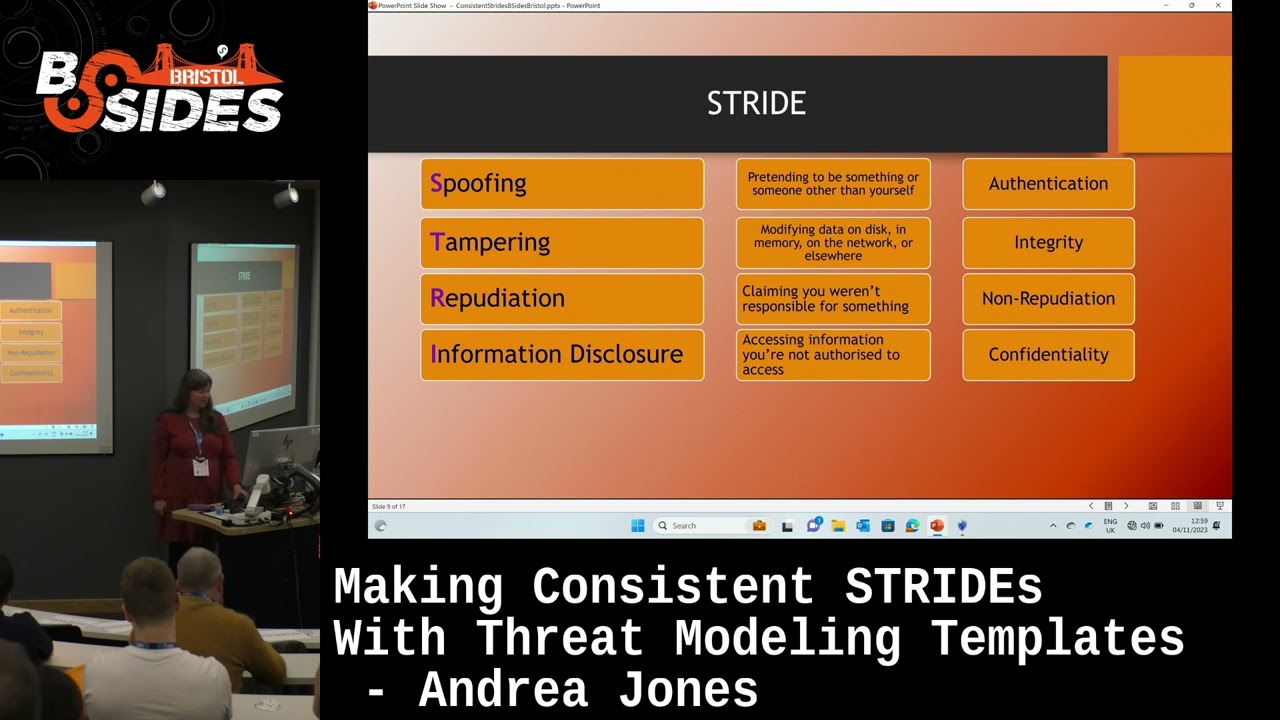
sort of thing with threat modeling you know what problems have we had in our organization with these Technologies and how did we remediate those issues build into your threat modeling so you can tell people look this is how you need to build this so Frameworks there's quite a number around and you may have come across various ones uh but stride the one is the one I'm looking at today it's probably the most mature threat modeling framework um but it does take a a fair bit of effort to apply it um there's another one called pasta the process for attack simulation and threat analysis obviously very attack driven um attack trees they can be useful in more um sort
of situations where you don't have quite so much infrastructure or maybe you're looking with L lots of third- party platforms that you're not responsible for um but you can still look at those various issues around authentication and the like and again show Stacks books got some very good appendices with information about that um in there um something has been around a long time security cards the elevation of privileged card game um some of you may have looked at that uh in the past um it's best you know you need to apply these things in the context of an actual system it's no good just getting the cards out and playing a game you need to
actually analyze your system and again thinking of the what could go wrong is a bit that is sometimes a hard thing of having to do that research and find out the the possible issues so looking at Stride um the the six letters stand for different elements of the threat modeling of of what we're looking at so when an attacker is attacking one thing they can try is spoofing and so that's pretending to be someone or something other than yourself and so you counteract spoofing by very good Authentication and that's where we've got to the point of having to implement MFA and things obviously we still get attackers find ways around that and uh but the whole
thing is that if you're going to mitigate spoofing you need to look at strong authentication and how you do that tampering so that's uh modifying data in some place so could be static or in transit um and so we get around that with Integrity that what is there is what we expect so taking hashes and things so that we know that what's there is what was there before and having backups so that you can restore your integrity is obviously another important mitigation repudiation not me mate um attackers they'll often come in and mess with your logs and try and make it look like they weren't there they'll take over someone else's account and so it looks like this
person was doing it and sometimes even just having shared accounts that gives you repudiation because you don't know who did it who was using that shared account and so the property we want there is non repudiation we can absolutely nail this down and we've got all the solid evidence of who was doing what and nobody can mess with that evidence information disclosure and so uh that's obviously a lot of what we see um grabbing stuff Lisa was talking earlier ransomware groups steal your data and Ransom you for it um but yeah all sorts of places where information can get leaked out and so we prevent that happening with confidentiality encryption uh but again a bit of advice on what encryption
standard to use uh could be very useful in your threat modeling process so your developers put the right sort of encryption in there and don't get nasty things in their pentest reports of uh you got some weak C cyber block training protocol in use or something denial of service well it's not just Bots attacking websites uh it's anything that denies access to a resource and so even deleting a file can be a denial of service because it's no longer available um but obviously you can also get to things around there about uh any sort of resource exhaustion one of the nice things in the cloud is having Auto scaling available um so looking at the possibility
that this element might come under extreme pressure can you scale it in some way or you know with um uh using message cues and things so that um systems don't get overloaded with a flood of traffic and then finally the E stands for elevation of privilege doing something you're not allowed to do and so there authorization is something that we can put in place so by thinking about those different elements of Str you can probably see that you can go through and threat model something and think about each of those components and how could that sort of thing happen in this system and that's the whole idea of stride so when we diagram threat models
um these are the standard symbols that we use uh rectangles for things external to the system any sort of process so executable and uh any other components is shown in the circle uh data store store is two parallel lines and then a data flow with a bendy arrow and uh if you want to draw some of these diagrams oas's free threat Dragon tool is quite nice for drawing the diagrams and you can use it to manually document your threat modeling process um if you like but it doesn't give you the actual things of what could go wrong any prompts or anything else um I think this group Matrix here is quite useful of how the stride elements are likely to apply
to these sorts of components um because you know when it comes to data Stores um spoofing is not the kind of thing that generally happens you you authenticate on your way to the data store but it's not the data store itself that that applies to and as for repudiation well if the data store is is logs yes repudiation will come into it but often it's not very relevant so here's a sample um threat modeling diagram done with those um standard symbols for the type of thing I'm going to demonstrate in a moment so I've got something here where a person uploads an image file to an S3 bucket um that goes to an SNS topic into an S
sqsq um onto a Lambda function which basically runs some python which then might reduce the size of that image to make it suitable for storage onward processing and then it goes perhaps off to some other system so that's just a very simple diagram of the kind of system someone might set up and that you might threat model and the dotted lines you see there are what we call Trust boundaries so there are the points at which there's a significant change in trust in the systems and where a threat actor might interact with that system but obviously if someone's inside your system then they may interact at a lower level and I think it's still worth
considering protecting everything that's inside that trust boundary so the tool that I'm going to show you and some of you may come across it but you might have got frustrated because you found everything was a your and didn't apply to what you wanted to do um it's Microsoft threat modeling tool um and so the template it provides there's some one for Azure there's one for Microsoft's own um software development life cycle and um there's also one for medical devices and all the templates are are basic XML files so although they have a tb7 extension you can quite easily open them in a text editor and uh you can put your own uh customizations into them um although you
don't need to do that to create the template but I find that's useful for kind of naming it and um you know saying what it is and putting some notes about it so when building your template um you need a few components and I'm going to particularly major this talk on the AWS side of things because it's a very big cloud platform that's in use a lot everywhere um and unfortunately there's no template for it in this tool um so AWS provide um some a PowerPoint presentation with all their icons in so that's a wonderful Resort and it's free for anyone who's an AWS customer or partner to use um when it comes to looking at the
what should you do the mitigations uh rather than trying to work it out yourself it's always best to go to these best practice guides and to look at the um the pages about certain components and how you should operate them for best practice and get all the mitigations They list there the sorts of configurations you should put in place so the AWS um security found foundational best practice is a a good list of some of the things and these are things that turn up in aws's security Hub um to give you alerts so if you can address them you'll cut down your alerts for a start um there's also a set of uh benchmarks in there for the um CIS
benchmarks uh but just note with those that there is a license issue around use of the cyst benchmarks um for commercial use uh miter attack framework again that can be a useful source of mitigation advice and also about um kind of defense and monitoring advice um so not everything can always be mitigated very easily um and so you may need to in your threat modeling look at well have we got suitable detection in place so that if our threat did happen we can pick it up even if we can't prevent it your organizational policies and any um security standards and guidelines that you've got very useful um build that into a tool like this and then hopefully
you can shift leftand this to your developers they can build their architecture and it can bring out all those components for them so that they know what's applicable in this situation um and very important to put in that information about mitigations as I said earlier what's the point of finding all the possible things that could go wrong if you're not going to do anything about it that's the the Nu of all this so here's some example um threats from the foundational security best practice um s3.1 and S 3.8 so that relates to S3 buckets um so these are related to blocking Public Access how many stories do we hear of exposed S3 buckets and the
big data breaches that they lead to um so one is relating to blocking it at the account level and the other one is at the Bucket Level and and there's four um properties there of the bucket that need to be set to true for this to be fully mitigated and what you can do in this tool is you can actually uh give options for these uh properties and allow people to select how is yours set and if they do that then you can write your threat analysis so that you can work out yeah the way they've got that set if they haven't got all four set to True they're at risk of of a threat like this
and so here's an example of um some threat details entered for that particular threat um so just got a name for the threat at the top and you see there all the brackets and all statements around those various properties um that have been set there to do the test um and then here is the mitigation and uh the threat modeling tool does encode apostrophes and things for you so um you have to live with that it comes out beautifully in the end um but I like to put in some URLs where people can look up further information um and get that advice you can also put a severity I use the um f the foundational security best
practice ratings um to put the severity there um and uh you can also uh enter this the stage of the sdlc where that should be implemented so hopefully I'll be able to show you something of this tool now not sure what time we are we' got plenty of time wow I I wasn't sure how rushed I'd have to be on my demo um right so here is the tool um so I'm going to start off by opening a template just so that I can show you um some of the nuts and bolts of how this is made so I've got one that I've made for
today and so here on the left you see all the kind of standard components that Microsoft has put in and it does have some generic elements um but it's not always easy to get the full benefit of threet modeling just from a generic element it will give you some information but you know not as detailed as it could be as looking at our S3 bucket for example um and then we go down and we've got various aure components as I was telling you earlier here are our trust boundaries now you can have a trust boundary either as a rectangle around a whole section or you can put a generic trust line boundary in if you just want
to Mark a certain point as a trust boundary and what you do when you set your threats up is that you include that trust B boundary so flow crosses a trust boundary is the condition you use and that's where that generates look at this particular threat um so here is um the stencil that's been set up so what the the putting the icons in is under this add stencil section so I've put in an application integration stencil uh for a section um you do have to set these behavior and shape dropdowns when you're adding a new one otherwise it won't work and you'll get messages down here telling you if the template doesn't like something it'll tell you if there's
threats that don't have something in the stencil um or if a stencil isn't set up properly and then um under that I've got the simple notification service and so here's a property so when users use this they will be able to choose how is your SNS topic encrypted at rest not at all I'm using AWS managed KMS or I'm using customer managed KMS okay and so you then build that into your threats for how good that is because if they're not using customer managed KMS there's still some risk that someone else could pretend to be um not someone who they're not um so those are the stencils and the that's the sort of way setting up so
here's the um uh S3 one and this is what I was talking to you earlier about the um public access settings so here are all the various properties of set up so that someone can choose how have I got my uh access settings set and then we go to the threats and so they're categorized um under the main headings of spoofing tampering repudiation Etc and to add a new threat you click on the category and then click the new threat type button and that will put a new threat under that heading so if I look down to um here we go uh Lambda permission uh so this is under the E the very last category
elevation of privilege so I've got a threat there make sure the Lambda permission doesn't contain a wild card action now I'm not going to analyze all the resource policies and I am policies relating to an element when I do the threat modeling so all I'm doing is making a kind of Aid Memoir for the developer of well when you've done your Lambda function have a look through your policies and just make sure there's no Wild Card actions in there um so that's the general way that we set up the threats it takes a bit of effort obviously to get those things in there and to think about how you should set up your source and your target um so here
we've got the include sources Lambda function um another thing you can use is Curly bracket target. name to pick on a particular component that's being looked at and that can help then reference that individual component um in the thread so enough about uh that template here so let's make a new model so using the diagram I had earlier so I've got a human user over
here I've got the wrong
stencil right there we go here we are that's the thing you see this was using the sdl stencil that's why I couldn't see all my elements so always make sure you've chosen the right stencil so let's try again here we
go oh there we go right so I've got user here
go down to my S3 bucket then on to SNS then on to sqs back to S3 bucket and I'll I mean I would have another user at the end I'm not going to um do this just for the moment um but then we join these together you can do requests and response but I'm just going to join these together with a simple request at the moment and using this pane down the bottom you can actually name your elements more intelligently so that um I could actually click on that S3 bucket there and I could give it a more meaningful name image upload bucket or something like that which will help it me more when I look at the final diagram
showing me the uh final
output I hope these all joining together properly there we are um so now I can do a report from this and if I create a full report and I haven't gone through and set all the fiddly little options because I want to leave enough time uh for questions and things um but if I create a report
we are you get this nice HTML file which can also be quite easily chopped up and distributed to different people for different components if you needed to um but it shows you the different sections of the diagram and the various threats that could apply um so you can see there all the things I fed into the tool are coming out another thing you can do is you can change into analysis View and here you can actually see the various threats that have been found and uh we've got a state box here as well so down the very bottom botom you've got a pane there where you can set the status of this and where it's at so if
developers want to come back to their diagram once they've uh their model once they've created it they can mark off the things they've done and easily see the things that are outstanding another nice thing you can do is you can export it to CSV and uh sometimes you can get some duplication in there so often what I'll do is I'll export it to CSV um do some D duplication on it and then use that spreadsheet to record my discussions with developers of well what are you going to do about this are we going to mitigate it or are we going to deal with it some other way or is the risk so low um that we're accepting it um so that's
really the threat modeling tool and how you can make your own templates um it's meant to be a very basic tool so I wasn't hoping to blow anyone's minds but I hope for those of you who not come across it before it might be a good place to get started and uh for those of you who haven't got the money to pay for fancy um Cloud security posture tours and things um it might be something that you can use uh another nice thing with the the diagramming is that you can actually put in other components outside of the that main platform you're using and so you could include your data warehouse you know a thirdparty SAS marketing platform a
thirdparty SAS analytics platform uh and put in all the relevant controls that you have around those um you're not restricted to just one vendor's view of security so anyone H that's it so any questions questions
questions one is are there sharable
awsw um yeah I did look for this there is one guy I think on bit GitHub who has made a template but I found it was very basic and unfortunately even some of the other threat uh platforms like there's a platform called threat modeler which you can get a free account on but you want a threat related to an S3 bucket you've got to pay um the second question sorry is around um things that are non things that might be non digital in your threat model how can can that Co I'm thinking of things like getting some attack in last few weeks it Service Test where privileg access social engineering that's why it's in my how I show that on that di
yeah well you you could show the the service desk as an external entity um with some of the systems it links to couldn't you um and then yes so you could say you know source is IT service desk um and this could go wrong and this is how we mitigate it um sorry I didn't repeat the question but hopefully you heard on the microphone um but uh yeah you could you could put anything you like in there it's just obviously um takes time adding elements and it's probably good to just put your effort into the resources that are going to be used the most by the people using the tool but you could put absolutely
anything in there any more
questions in terms of the modeling um what would be a good scenario for uh this so it be eff for a specific process or service or would it be useful for the whole business you know with firewalls engaged da basis um you what would be the best scenario best J for that yeah I think for this it was asking about what's the scenario you know whether you use a a big broad um thing of the whole business or um a smaller section of it um now I think it's uh it is better with threat modeling to break things down enough that you can get get to the point where you would Implement your mitigations you know looking at the big
organization you've got to go to a finer detail to get to that point where that mitigation actually is implemented and so I think that's the the best way for prep modeling so you can actually tie that mitigation to that particular component any more questions [Music] yeah maybe this the isop um unfortunately for the Microsoft to I don't think so um um yeah as I say uh most the other things tend to that I'm aware of tend to be paid for and so yeah you're paying for someone else um to do that work um but certainly as around threat modeling itself then the oasp has a a good commun um where people discuss that and you
know lots of blog posts and things you can look out for threat modeling itself but I I think the best source of information about mitigating things is go back to the actual provider's website and what information they give you about how these things should be configured because after all they're the ones who end up helping their customers when they've had a a zero day attack on some component um so they're going to update their guidance on configuration and provide the tools that you can actually put some settings in to stop that happening any links to analysis tools settings back to um say I think probably with um your things like your Cloud posture Security Management things you would get that
kind of uh information and you know I think it's something that the cloud providers are probably maturing in um again not everybody gets all their um accounts fully integrated into the cloud platform's own Security Management System um there's all sorts of things there in like AWS config and inspector and everything else but you know have you got that set up and finally tuned but that will only deal with AWS and so by using the threat modeling tool you can build in all those other components that you use around it as well ftic any other questions got a little bit time for questions [Music]
there no I will say it's a very simple tool um it's not even easy in this tool to see what threats you you've made for a particular stencil um I end up exporting the XML and then analyzing it probably a spreadsheet um so yeah it's it's a very basic tool but that's why it's
free there any that you can rep sorry I didn't quite catch the question there is there any way you can um run the report generation depend you can build secur sorry to S I'm not I'm not I'm not investigated really and you'd obviously have to look at the terms of the software as to how much you can tamper with it um but uh no um I I don't know maybe you could take the HTML though and if you can decipher what's within it I but I don't know I I'm not even sure if what's output is available as XML in a way that you could do that there may be possibility just time for one last
question [Music] so interested on how Drive
[Music] bus do people Proactiv come to you and and ask you how you yeah well you know um the the squads I've been using this with now when they're building things they're you know they're fully aware threat modeling needs to be in the process and they've found it helpful um and you know one one Squad um they were very heavy on building terraform um to make things and obviously the beauty of if you threat model your terraform beforehand then all the things that are built from that terraform are going to be good um and in in two different situations one where I was noticing the previous iteration of this particular tool that was made before I joined um had loads of S3
problems I mean it was all internal stuff so they weren't exposed but they were still not good um and uh so the threat modeling exposed that and now the new version of the tool everything comes out of it nice and shiny and there's loads and loads of buckets made from the tool but another Squad um they used it and they realized oh the version of terraform we're using can't cope with that setting and so that then prompted them for uh an upgrade on their terraform which improved them in other ways you know um so you know I've um I've only been in the organization two years and so I haven't been using this with developers very long uh but it's
something we're talking to them more and more we had our cyber awareness week this week and one of my colleagues was talking Dev SEC Ops um and he was uh speaking the virtues of threat modeling and using this tool and directing people towards me um so yeah people as they start to use it they they start to see how it helps them um and although we're not maturing it yet but we're hoping that eventually you get to the point you get a good template that you can then give it to developers and let them use it on their own but at the moment I use it with them thank all right thank you okay fantastic thank you so first
things first we give a round of applause





