To the docs and beyond!
Speakers
Tags
About this talk
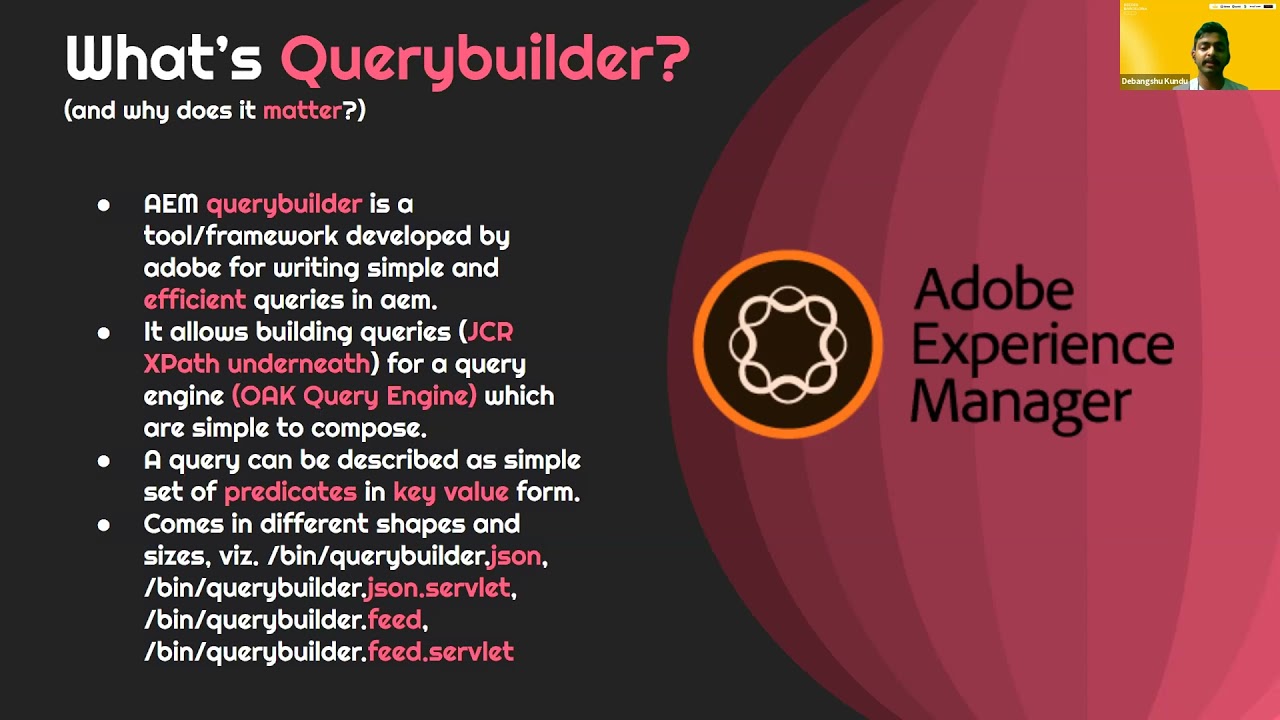
BSidesBCN21 - Day 2 - Sagrada Familia Track To the docs and beyond! (Debangshu Kundu) On the journey to explore some non-traditional attack vectors, I picked up developer documentation as a possible attack vector. Why Developer Docs? It provides a holistic reference of the platform/feature to the end-user, be it a developer, hobbyist, or a hacker like me! Also, almost every IT company out there has a documentation of some form or the other, making this a juicy and widespread attack surface. Well No! Just the presence of documentation itself doesn't guarantee any vulnerabilities, but instead, gaining a deep understanding of the feature or product through a thorough read of the docs followed by hand-picking possible issues is the art here. The main idea behind this talk is to leverage documentation to aid exploitation of security vulnerabilities. It goes through four individual security issues that I've discovered through the said approach. The first issue deals with the improper usage of blacklists(i.e: a list of all non-permissible entities) to prevent Cross-Site-Scripting (XSS) and how I bypassed it with the help of developer documentation. The next issue talks about two security misconfigurations, (i.e: incorrect system configurations) in the Slack instance of a company. Slack, which is already known for its granular security controls, leaves ample space for humane errors and hence generates security flaws. The Third Part of my talk is about the AEM (Adobe Experience Manager) Querybuilder Framework and how to leverage data exfiltration just via Adobe's developer documentation of the same. Rather than relying upon automated tooling, learn how docs help us in building handcrafted payloads and even how to combine them to gain maximum leverage out of AEM Querybuilder and score a critical bug! The Fourth issue brings about the possible risks of incorrectly exposing a staging API without authentication. The finding presents an exposed Swagger UI, which is an open-source GUI representation for documenting underlying REST APIs. Upon exploration of the same, three critical security issues were uncovered, The first being a Local File Read,The Second, a Local File Write, The Third, a Local File Delete, all without the need for any user authentication or credentials. Last but not the least, a bonus finding briefing about missing CORS policies, possibly usable to steal user specific information via XML HTTP Requests (XHR). Finally wrapping it up with some key takeaways, helpful to keep in mind while building and breaking web applications. About Debangshu Kundu I am a bug-bounty hunter, boring documentation reader and 2x MVP on Bugcrowd. Love finding flaws and misconfigurations in CMSes, AEM being my favourite.





