Just Apply the Patch
Show transcript [en]
um first thanks for sticking around um I know I'm the last person and they just gave away the raffle prizes too and you guys are still here so sincerely thank you um just to start I I sort of a a quick quick background on on why um even doing this uh this is sort of internal you know sort of like Wiki notes that we have banging around our company um that we sort of saw when we started looking at this stuff we sort of saw it all over the place and the more we started looking for the more we were finding it to the point where we decided you know what we better just sort of like just
get this out here because if we're finding this all over the place on our pentest it's got to be in more places than people don't know about um and we're able to find some really fun ways to bypass just about every single vendor's uh IPS and WAFF that we came up against and we've notified them and I think the signatures are now out there but um towards the end you'll see some of the stuff that we're were doing that was just kind of silly and fun um to to get past some of the IPS waffs and and hopefully you guys think it's as silly and fun as we do um so first off I work for virtual
security research uh vssr based out of Boston um but I'm local here I'm from the Charleston well I'm not from the Charleston area I'm from Boston um but I Live Now in the Charleston area I just happen to work here um because it's sunny and there's beaches and that's nice and so this is not about you know zero days in in struts or anything like that this isn't any new exploits that that nobody knows about or that sort of thing um the closest thing we get to that is just some WAFF and IPS stuff and bypasses on on common vendors uh W and IPS signatures to still exploit this stuff if you haven't just patched it
which is the name of the talk um so a couple things that by the end of the the talk hopefully you kind of take away from this uh is that third party libraries are everywhere and they're in places that you don't necessarily expect them um they're in products that you don't necessarily expect them um so you have to expect the unexpected uh CVSs scores are what kind of turned me on to struts in the first place because we started seeing some really low CVSs scores that were resulting in full compromise of the box so like remote code execution from a CVSs score that was like a five and we're like isn't CVSs supposed to be like you
know that's like a 10 right that's like that's like up here if you can just hit one you know send one get request to a server and I own the server like that's that just didn't jive with us so that's what we started looking at it or that's where I started looking at it we sort of got into this whole thing um and so the the takeaway there is the third one is that you're we and your IPS and your IDs they're great things I'm not saying get rid of them I'm not in the whole you know they're useless technology type crowd but they're signature-based and signatures can be bypassed and so you know put them in place if you know that
your systems have vulnerabilities and and stop that immediate exploitation but get the patch there as soon as you can um and then keep it there as a long-term alerting so you know you know when people are starting to hit your boxes with certain types of things and and it's definitely helpful in that way um but what we're seeing clients come to us is where they were using that W or IPS as a long-term fix for the problem they said well it's going to take too much it's going to cost too much for us to actually fix the issue so this WAP takes care of everything we don't have to worry about this anymore and we can take
that you know CVSs score and we'll we'll mitigate it down by three or four points and now we're looking at you know an adjusted score internal adjusted score of next to nothing but that's still resulting in remote code execution on the box so it's not helping you any so why struts um why struts I just talked about a little bit you know we're sort of seeing it all over the place um it's it it's all over place and nobody seems to know it is sort of the the trend that we were seeing um like I was saying before officiation techniques for the for a couple of existing vulnerabilities um that are 18-month old vulnerabilities in
this case are some of the the most useful ones but you can still just blow right through them which is awesome from a pen testing perspective you know not so good from the defensive perspective um and it's from the Apache uh Foundation it's a a Java 2 Enterprise uh NBC framework it's model view controller I'll get into that in a second um and the URL for where you guys can go check out some stuff on it uh it's sort of a combination of a couple of different web Frameworks that merged around like 2006 2007 there was web work and there was uh Symphony open Symphony something else and they sort of stuck together and came
up with uh struts 2 which is the current version of the library and there's also struts one where if I have time we can talk about struts one I think I'll probably run out before we get there but there's some interesting stuff around that where there's a 9-year-old vulnerability in struts one that is out there and exists today and struts one is in all sorts of different products um if you check out HP fortifi blog they have some great information on that so this is what I was talking about before so this is this is why I started looking at struts here um this is from 2014 uh it's early say like late February somewhere around there from
2014 it's a cbss five do have anyone who does like the defensive side at all if you saw CVSs 5 would that be like patch now would that be like patch next week would that be like well we'll roll it into this month's patches and you know if we have something important going on we'll get to it this quarter you know right so five is like yeah whatever okay we'll get there and so people would look at this strut stuff and say okay fine I have a CSS score five it's struts but I don't use struts right I mean I don't I don't have a product that some vendor sold me that says struts on it I don't have you
know I talk to my developers and they're like I we don't use struts no we wouldn't do anything like that but every single one of these companies has products that incorporate struts as a core piece of certain product lines not all of them you know not every product line has it but certain ones do like Oracle for example anyone had a Fusion middleware install or dealt with Hyperion Enterprise reporting software that stuff no okay well it's the type of software where there's like two camps in the room right now there's the people who don't know about it you are the happy people there's the people who have dealt with it and when it needs to be upgraded or it needs to be
repaired or you need to add some new feature you call in the Oracle Consultants at you know $4 $500 an hour and they give you a six-month project plan and then when that six months is up they're not done with the work yet so it extends out another three months and another $250,000 and that's pretty much how that product goes so when somebody says I need to upgrade Hyperion everybody in the accounting office goes can we find a way not to do that and that's sort of where that whole WAFF and IDs stuff comes in right you say okay well I can put this box here box cost me 20 grand it cost me $1,000 a
year in signature updates whatever it happens to be and that's going to cover me because now I don't have to spend a million dollars to upgrade this piece of Oracle middleware that nobody wants to T and nobody wants to support um and just bouncing through the other ones real quick people soft that's another one of those for anyone who's had to deal with a people soft install you have my sympathy I've been there done that um and it pops up in weird places you know like an IBM San runs a Java Enterprise Pete Library as part of the web interface like who would have thought that so with one one series of vulnerabilities you can you can pop Erp
software you can pop Sands you can pop red height satellite and anyone know what red hat satellite does patches it oh it issues patches oh for all your other Red Hat boxes oh that's kind of important you know that's probably not good um Fujitsu some some middleware that it was one of those names I saw the name of the middleware and I'm just like this is straight out of like office space or something it was like you know the Fujitsu like like business analytics Cloud platform middleware I'm like okay whatever sure um I've never seen that one myself uh VMware Ops management and orchestrator products and then Huawei they have it in a ton of their stuff and
it's you know just their cloud and VM management platform that's all nothing big no problem here um but as I was looking through for all these different vendors who had struts included in them um one kind of stuck out and most of you probably saying okay fine but I don't need to worry about struts if all these vendors you know they issue patches I get the patch I imply the patch boom I'm done there's no problem I'm I'm covered with struts right oops so this one I came across was 2010 was a cve and if you if you look at the struts vulnerabilities they're not like it it affects one version if you get the
one from 2014 it it affects version from 2014 like all the way back to 2008 or 2006 so they were looking at at this and in their own advisory you know that's the advisory you can go look it up it says hey we're applying the patch for cve 2010 blah blah blah for the struts framework and I'm just looking at it going oh my God like this this sat out there for four years there was a remote code execution vulnerability on a couple of Cisco products and eventually they decided to patch it well that was nice of them um to to their credit I mean this isn't like the Cisco like Catalyst software or something like that this was
some like sip you know if you're running a uh VoIP stuff this was some sip interface something like that and and some media product and then an integrated service router or something like that so you know not their core core products but big enough that you kind of scratch your head and go you know how did that slip through and there's more custom applications right and that's that's a pink elephant in the [Music] room so this is where we most commonly um have sort of our clients this is where we interact the most and this is where we kept finding struts over and over and over again and and it we'll go into a little bit about struts and and
why we sort of saw it over and over and over again it actually has a really powerful framework and I started off looking at it thinking oh my God this thing's awful you know like there's all these vulnerabilities it it's remote code execution like 75% of the vulnerabilities out there remote code execution like what's going on here but once you look at what it does and how it does it you kind of appreciate and go oh well I was a developer I would probably look at this too because it makes your life easy in a whole bunch of ways
so seriously um I'm not a developer I can code I can script but I recognize that there's a big difference between somebody who can read some code write a little code and script and a developer who can create some magnificent castle of a a web application um so I'm going to give you a quick quick you know sort of tutorial on this hopefully you get something out of it um but yeah so it's an NBC framework a model view controller this is a concept that's been around since like 1970s or something like that and it's basically an object-oriented design pattern for uh designing stuff in a in a a sane manner oh that looks awful on the screen
sorry um it's all bleeding together but anyway the you kind of separate the your aspects of your application so that you have a a user it's a user focused framework you interact with controller have certain classes in your your uh code that act on a data model which is up at the top that data model sort of independent you keep your classes separated which then updates a view and the view is what's presented back to the user so by using something like this you can keep your your concerns and your codes separated from each other so if you need to update your data model you can update your data model classes and you don't have to worry about all the
other pieces and it's just a nice clean way to do things which is pretty much what I just said there um and internally uh what it does is uses this other Apache project ogl or object graph navigation language which is this other little intermediary language which sits in the strutz framework um as sort of the the way that it takes a request it takes a whole bunch of variables puts them in an ogl context and ogl can do expressions and it's this it's just kind of this cool little intermediary language that allows you to do simple operations on on object object very similar to Java but it's it's not this great big thing so you can
pass the ogl context between your different classes between what uh strut calls interceptors and and action models and other things so you can take them this this context object pass it through these different classes and it stays consistent it's just a nice pretty kind of neat way to do things but we're going to see later on this actually gets you in a lot of trouble um if you expose this stuff so the basic idea with struts is you get a Java class you get Getters and Setters in your Java class nice and simple sprinkle on some XML configuration files and strutz kind of takes care of everything else within its jars so you don't have to worry about
all the other stuff that goes on um just to give you an example this is a web application fully functioning web application that serves up a page that's all it is you add in a little bit of XML in your struts XML file nice and simple right a web XML file again nice and simple you know you can find 10 12 20 different tutorials online that'll walk you through doing this and you can be up and running with you know a fully fledged Java Enterprise app in couple of hours tops and that's coming from from zero from not knowing anything so what I was saying before it's that's why your developers like it you know allows them to separate their
code from their data model it prevent presents a clean way for them to do it and it gives them this nice easy way for them to configure and update and maintain the app I mean that sounds great right even from a security guy standpoint who's not a full-time developer I'm like I love it you know you have you have a way that you can keep your stuff updated you have a way that you can maintain it going forward and it's this nice lightweight configuration for you I'm like this this sounds fantastic um and on top of that it's Java right there's no problems with Java I not on the server side right I mean client side okay fine but you know
on the server side you know it's safe it's it's it's managed garbage collection you know no buffer overflows you got all these nice features about the language itself which makes it a lot safer to use on the server side and so the other question that was coming up okay um is if this library is all over the place why aren't people finding it you know why why is it that now that we know to look for it that we're running into this all over the place and it's still out of date like this just seems like the type of thing that this should be found a lot more frequently um and and one of the things
that we sort of took out of that is a lot of the reasons we think it isn't being found is because people aren't testing for it the right way so when you're doing pen testing on web apps you know you look at certain pieces of the application you look at the way that that each request interacts with the server and what response you get back and typically you're looking at you know I'm going to take the cookie value and I'm going to put some crazy injection string in there and I'm going to try to see whether I can get some you know SQL injection maybe I get cross- site scripting maybe I'll have some uh command injection or
something like that that'll come out of injecting into the the value of the cookie or injecting into the value of a parameter that you're passing but what you have to do with struts and and I think this is true for other Frameworks as well but particularly with struts is you fuzz and inject your your o NL we're going to get to that in a sec into the paths into the parameter names and into the cookie names because strutz takes those names and in some cases directly executes them as code awesome right or in other cases allows them to influence what code is actually run on the server side so oh good it did fit I had to
tweak this slide earlier I was afraid it wasn't going to so the traditional sort of web app testing model you'd start with something like what's up at the top you know here's a a get request to some server got a parameter one value one and I'm going to take that parameter one and I'm going to set it to something that you know the programmer never expected or that the server doesn't expect I'm going to watch what Behavior happens I'm going to see if I can trigger an error message I'm going to see if I can trigger something out of the ordinary and then I'm going to build my exploit from there with strutz testing and and
like I said I believe with other Frameworks as well this is probably just as true you don't want to do it at the value you want to do the actual names so every single place you see you know madness madness madness madness that's where you want to put your injection strings that's where you want to try to cause the errors to occur in the application and when you start testing this way you start seeing struts errors and struts you know exception reports all over the place and it's it's kind of crazy okay so I said we were going to go back to ogl gnl is that intermediary language remember this is sort of it keeps the the serers side context as as
the the client is interacting with the server and ogl uses or or uses pieces of these to build uh an execution stack essentially of things that it's going to do internally and it can evaluate expressions on that stack as well so anywhere you see this is where you want to try to be targeting uh your injections and when you're injecting into OG now sometimes it's as easy as doing something like this and this is that same CVSs 5 from from earlier this year so what's occurring here is you've got a strutz application you've got a a some parameter you know question mark and then the blue is the parameter that's the parameter name you know for anyone
who's who's done web app stuff or done web app testing you're looking at this and going yeah but that's not a real request you know it's just sort of like this blob of stuff after the question mark and that's not really you need an equal sign sign you need a value you need an Amper sand you need some other stuff with struts it takes that blue stuff up there and turns it directly into this Java code and then executes it on the server side and it's taking class putting class there it's taking class loader putting class loader there and as long as in this particular example in this particular vulnerability as long as the the method that you're calling is a
public method and takes no arguments it's going to append get and it's going to run that so I mean anyone familiar with Java security and know that when you pretty much get to the class loader it's kind of bad news I mean right I mean there's there's you know tons of stuff that if you look back over the years and and you take a look at Java issues getting to the class loader getting to the security manager if you can get to one of those it's you know bad things are going to happen so a a quick ogl reference when you're crafting ogl statements and and and little execution you know scriptlets that you want to put in there um you can
assign variables that's what the Ampersand is for or hashtag I hate hashtag it's an ampersand then you have an octo Thorp not an ampersand right yeah that's the other one right Octor is this one not a hashtag yeah got it I don't have Twitter either so comma separate statements you can have multiple statements within an ogl uh sort of expression and then you've got this idea of like an array or list of collection so you can you know use your brackets and and either index it by number you can index it by key um and then finally you can have these statement chains so you can do something like this that you know kind of looks
like Java not really but it sort of looks like Java and what's going to happen is it's just going to execute from left to right straight through and you can't see at the end and it's just a couple couple parns here at the end um and it's all going to be done within within ogl that's all valid ogl oops wrong way so the the end result of this this exploit here or this particular vulnerability here is that everything you see in Orange up there and this is on Tomcat by the way so on Tomcat you'd see something like this and what this was doing is using ogl to call this what you see in orange
up there is in Orange down here we you see in blue up there is what's blue down there and it's setting the document base of basically the serlet context to the attacker source so if you have any sort of file upload vulnerability in your web app and you're on a Linux machine you know they could probably Point their you know your serlet is now not running your code anymore it's not running your jar files anymore it's running the attacker's jar files if you have a Windows machine and you're not doing EG filtering the UNCC paths are a great thing and and there were actually cases where people were just pointing Windows servers running tomcat and running
struts and just changing the directory where it's getting all the jar files off to somebody else's server across the internet so here your server is pulling the jar files that it's running from you know Asia from Russia from the US from Kansas City if you remember the last talk um and then somebody else figured out you could take you know uh Tomcat 8 and there were some ways you can manipulate the the local files uh the error log files and you can get the error log files to actually get in the same position as well and so you could run jsps that you had injected into the error log files by purposely calling things that had JSP code in them and
would error out get stored in the log and then you'd move the doc base over to where the log was rename the log to a JSP and now you're running a JSP from the error logs of your own server it was a really cool like fun way to I'm looking through the whole thing I'm going man like whoever figured this out that's so awesome so just a few more vulnerabilities of this style with struts over the past few years um for those of you who are observant you'll probably notice a pattern like oh by the way these are my notes these are not you know official cbss notes or anything like that this is just my internal notes
of this is what you can do with this stuff if you find it um and you see patterns right so I mean you've got a whole bunch of them that just execute arbitrary genl code via Pam or you know class loer manipulation code exec or the top two uh modify service side context objects but it results in code execution and a lot of what strutz does in order to fix these issues is it takes a regular expression within the strutz framework and says okay that that one from 2008 we found out that you know if if put people put that hash sign in then they might be manipulating ogl context or variables on the server side that's
bad so we're just not going to allow the hash sign anymore and that'll take care of it okay well you know except for unic code and except for URL you know encoding of those same values and that's why in 2010 the exact same vulnerability comes up because the Reax just didn't cover all the corner cases if you look through a bunch of these other ones again you see the same theme that um they're applying re rexes Black List rexes and saying this is bad we're not going to let it we're not going to let it through and then somebody finds another way around it um and this one down here is the same thing 2014 there
were four different vulnerabilities that's one vulnerability it's just four failures of the regular expressions and it's four failures of where they were looking because there was no unified you know security manager with inst strust just sort of if it's a cookie it gets this Rex applied if it's a parameter it gets this Rex applied and so we fixed the parameter one and we forgot the cookie one you know and that's the type of stuff that that you see these same things so a lot of these it's it's really the same vulnerabilities just over and over and over again okay to bounce back just to give you a quick refresher before we move on to this so you know how bad can it be
it's just this ogl thing right so what's ogl it's allows you to do Expressions you have some commas you have multiple statements you have you know the the percent 23 you've got some some hash signs in there so they're ass signings and variables uh this is something that's pulled out of you know existing exploit code there's a whole bunch of Chinese blogs and sites and I don't know why it's all Chinese it just happens to be all Chinese for most of the struts resources that I found um where you know they're just building pointand click win32 apps that do this so and this is like the tame version this is the the lightweight version of what they do and
all this is doing if you sort of can read through it a little bit is calling a a Java process Builder feeding at the host name command and then if you look to other long line that's towards the middle of the slide there it's grabbing the the serlet response and just shoving the output of the host name command into the serlet response and feeding it back to you so the channel That the attacker gets the information back on it isn't a reverse shell or something like that it's the actual web page it's it's your server responding to their request and that's really hard from a defensive standpoint to catch because your server is doing exactly what it's told to do
which is it gets a request it looks at it serves up a page and gives it back to the user except that page contains an arbitrary command that the attacker wanted not you know your web page not what you wanted so if you look at metpo modules there there's met SPO modules out there for this stuff and it just does a simple test like this um this particular one uh is yeah 2013 2251 is uh it relies on this redirect or redirect action or action um what they call a parameter prefix which is a way that you can instruct struts make your parameters do special things in certain cases and if you get a modern version of
struts all of these parameter prefixes have now been removed by default every single one of them was found hey I can do some crazy stuff with that if I just mess around with it a bunch so if you find a site and it responds to that redirect prefix parameter you automatically know I either have a developer who really thinks they know what they're doing and has reversed all the defaults and is doing their own thing and they're going to you know they're going to protect it and it's going to be okay or you have an old version of struts and you definitely have remote code execution you just have to figure out how to get
there and the thing to know with ogl is if Java can do it and these are some of the main sort of you know Java class libraries soak in the attacker so they can run commands make requests read write files even load new classes and loading new class classes brings in some fun possibilities right so you know metlo again came up with a module that says all right fine well I'm going to load a Java interpreter over the internet I'm just going to pull in the Raw class files I'm going to load them up in the class loader and now suddenly your Java application is running essentially meterpreter class files instead of your own application or
actually alongside your own application um so internally we've been working on some stuff to do sort of like an encrypted class loader and do some fun things we wanted to have it ready for this it just it it wasn't happening we ran into more hurdles than we thought we would all right too many cooks everyone's seen that right please say yes okay good I you know I was thinking about it I'm like if I have 11 minutes [Laughter] like so smarf is later in the slides just wait um so payload evasion right so this is what I'm talking about if you've got some of these older versions of struts you know you've got remote code
execution here's some tricks here are some ways that we're found that we could get around like I said at the time we started doing this we we were getting through every single W and IDs that we encountered we've notified most of them now they have fixed it and so if you have the most current versions from snort and Cisco and and all those guys then you're probably okay with this but you know if you didn't apply the the right sign from them or you didn't apply signatures at all you know a lot of these will still work and and I've really wanted to work too many cooks into this one way or another but it does kind of actually
make sense here so um what we're doing in the evasion strategies is using the different layers that this your Crest has to go through in order to sort of you know security is at the seams right one side makes an assumption it's not a correct assumption or one side implements something the other side doesn't expect and when you have these transitions between these different layers of the technology it opens up opportunities for something to look one way over here but when it's actually run on the other side of that interface it means something different um and so that's what we sort of take advantage of so when I started you know simple just do a get request and and client had a w
IPI I can't remember exactly what product it was doesn't matter um and this gets and this gets blocked right so immediately the the connections just gets dropped on the floor nothing's happening right so I'm like okay well I'll just change over to a post I'm like holy crap that worked you know just just by changing from a get to a post I just went bu your W that's
bad and so we said okay fine you know they fix the post or we have a different product and and we couldn't get by with just a simple post so we'll change the encoding on it right so normally we just do URL encoded post no problem that gets blocked so we switch over and go okay fine so now it's a multiart you know like I'm uploading a file or something I'm sending you a whole bunch more data so I'm just going to change the encoding on that and then that worked so again we're like okay well that's really not good for the state of like the the WAFF and I IPS industry here if that's what
it takes but we're like well that's still not all that complicated you know it's it'll be a simple fix they just put a couple things adjust the signatures we're good to go again right so I said all right now we're going to start taking advant some of the the differences in the different layers that we're going through and ogl and Java support unic code awesome um you know you can URL incode things percent en code things that's that's just sort of standard web stuff at this point so if you look in the Java docs you can put Unicode escapes into Java code did anybody know that I didn't know that before I started looking at this no so
if you want you know and it's for people want to do it in other languages or or if you have some cool code conver verion stuff that you're doing and you want to be able to make sure it doesn't get corrupted or something you can just take a character and code it as an escape you know SLU four hex characters and Java is like cool I'll compile that no problem so these three lines the red the orange and the green they're exactly equivalent and this is where the waffs and this is where the ipss start to have problems because you know new Java iio and that second line you know you can sort of see okay fine it's kind of there
if you if you know Unicode if you dream this stuff in your sleep this is no problem you see right through it and you get down okay we're going to URL encode a whole bunch of that stuff and okay you know maybe again if you're really hardcore into this like like web filtering stuff you can see right through that again um and the funny thing is if you look back at stress vulnerabilities back to to 2008 2010 this stuff was hinted at like the guy he now works for Google and I'm not even going to try to pronounce his name because I'll butcher it um and he he basically said back when he found these vulnerabilities back then
he's like you know this Unicode thing probably isn't good there's probably a whole lot here that I'm just missing at this time so somebody should probably take a look at this and you know four years later nobody had still but again there's more so we don't stop at just Unicode and a little URL because again that's that's sort of common that's been around for for years and years ws and IPS is are protecting against that so it also turns out you can do different whites space characters and Java and ogl will will happily compile them you know you can have new space tab tab tab tab tab tab tab new line new line new line tab tab form
feed Java class and the Java compiler is like cool I got that no problem here's the the URLs if anyone wants to look at them it's really dry and this is straight out of the spec I mean this is this is if you read through the Java spec this is what you get to eventually and cool so we take that and again we roll it back into our whole strategy of how we're doing this and if you guys haven't looked at this particular blog or site or or
website.com to look through the stuff that they've figured out that you can do um and to get by uh SQL injection filters so a lot of what we were doing here and looking up we're like well if you can do that for SQL ey why can't we do it for ogl too right and so what you end up with something like this so new Java iio file is exactly equivalent to what you've got right there those two when it hits and gets evaluated they are the same but to the WAFF and on the network they look drastically different so the next couple of examples that I'm going to go through and oh well coming up on time um the next couple
examples that I'm going to go through are all going to be this same string right here and I chose this on purpose and I chose this vulnerability on purpose because it's a little more flexible than some of the other ones that are out there but it allows you to take a look create a a new Java object IO file look at the C drive this is Windows machine and then list files and then that little bracket in the one is basically saying give me the second element that's returned in the list in the directory listing that I get and what you'll see is the because of this this redirect prefix parameter the result of that
is actually going to be spit back in the location header of a 302 redirect that comes back from the server so this is a really sneaky way to sort of I'm going to send a request and you don't even know you're leaking info but you're leaking whatever I want back here and by adjusting the two that you see an orange up there you can cycle through the entire you can do a directory listing of the entire machine granted that the account that Tomcat or Joss or whatever you're attacking has access to you can access it as well and once you find something cool like that right I mean awesome and that's what we look for when
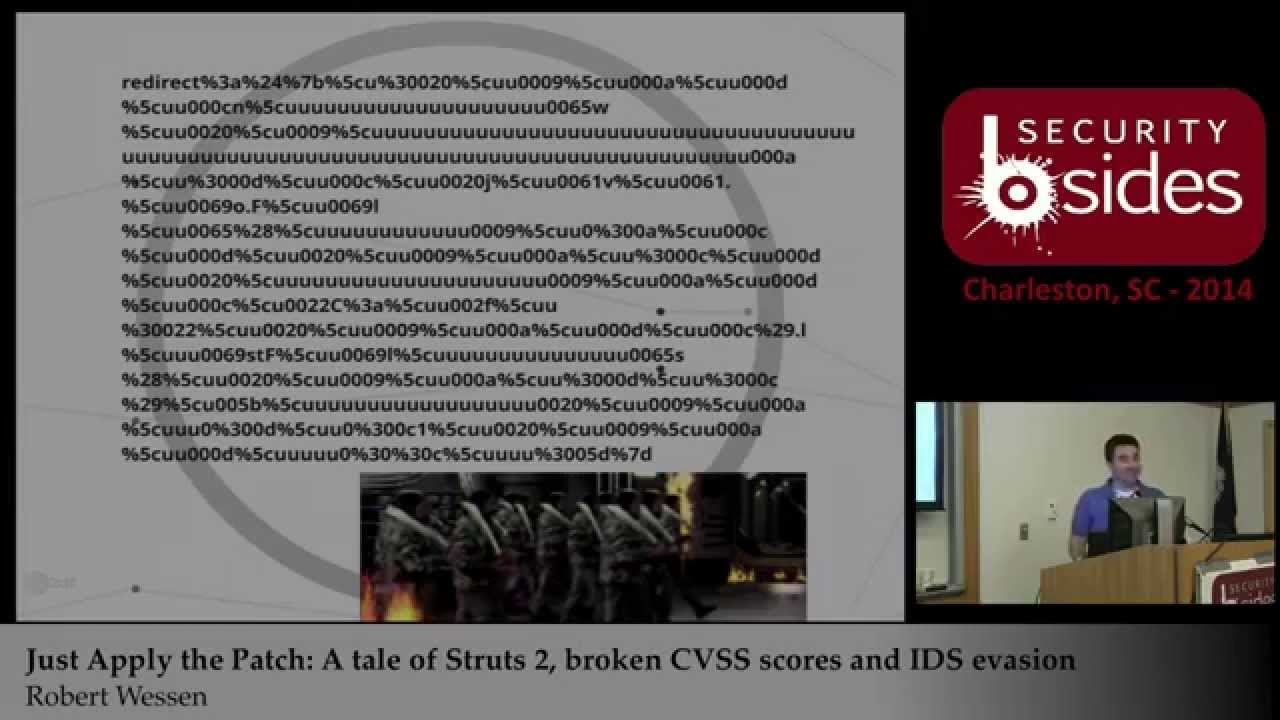
we're doing testing okay so this is the same string up top and this is just simple URL encoding again nothing special we should be able to see that W should be able to see that no problem now we're going to add a little little Unicode again same exact string the top and the bottom are exactly equivalent to each other when they get executed again getting a little crazier little more Ural en coding a little more unit code en coding and now we're getting a little crazier because we're adding white space we're adding Terminators and again the top line is exactly equivalent to the bottom line those two are the same when they get executed and then finally this is this
is my favorite finding when we're going through trying to get by off trying to Opus skate this um Java has this great feature where if you do an escape you know U four hex digits for a Unicode Escape it'll actually take any number of 's like the actual regular expression that's in the parser is like you star so it you can just sort of just keep on going like You' add 1024 U's in in Javas like yep that's a single Unicode character we got you I I haven't tried an upper limit on that I just thought it was kind of funny and finally I mean if if you take a look at this I mean there's there's no
way from a human perspective that you could look at that and say that's the same you know that's the same code that we're just looking at right here like that Top Line and what you end up with here is just so massively different and I'm sure there are those of you in the audience who are saying like Okay but if I see a request like that like I'm dropping it on the floor I mean come on that is no way that's legitimate and then you have to remember that you can send this bya get request you can send this by a post request you can send this via a a multi-part form post request so you can include a you
know 10 Meg file in the first part of your multi-part upload and then right at the very end just tack that on you know at what point is does your W look at a request coming in you know read a certain amount and just say okay fine just let it go you know it's a PDF who cares so there's so many different things you can do there and then again what I was saying with this particular vulnerability I chose this one as a as a specific example to give because you can use different prefixes at the front so that redirect you think oh well if I see redirect then I'm just going to block that okay fine well there's redirect
action there's action there's method there's you know you've got all these different options that you can use um and eventually your Waf and your IPS rules just start looking like total spaghetti you don't know why you put them in there in the first place and and that sort of takes us back to the the beginning of you know just patch it don't don't bother with this don't go there because the amount of effort you will have to go through in order to make your WAFF or your IPS consistently pick this up and not run out of you know processing power you know if I decide to send a thousand of these requests at you and it has to sit there and try to tear
apart all these requests and figure out what's going on like how many people have business rules where if you get you know your WAFF starts to die they're like no we want it to fail closed like we want to deny all traffic like no if it fails open so that we can keep doing business right I mean that's I mean maybe that's not everywhere but in most cases wh I've run across that's that's how the business wants it that's how you have to do it if your security equipment starts shutting down the business your security equipment goes away you know I told you there were smarf okay so what can you do um like I
said a minute ago you can just patch it I I mean that's really your best bet but the problem is not often patching it it's finding it I and and that takes us back to the beginning of what I was saying you know we see this stuff all over the place but it's like people don't know it's there um I ordered these in in a rank of Effectiveness from top to bottom so hope your volum scanner catches it probably not you know you can look for Action do in in the URLs that are passing through you know if you got some logging going on say okay cool well I see action stuff I see do stuff like I
know strutz does that maybe I have struts here kind of lame you know it might help you get there take a look at the the parameters that you're passing back and forth so they have a structure that looks like object. method because that's a very common thing to see in strutz applications okay that could be another clue maybe I have some strut stuff going on here um you can interrogate your vendors good luck with that I'm sure they'll be very cooperative and give you their pen test results and say yes we have it tested quarterly and here they are and I'm sure that happens um you waterboard your de did I put that on there oh I thought I
took that off is it too soon um and then finally it use some automation um I don't know Jeremy I I've read some of his stuff since actually doing this because what I was going to do for this particular presentation is give you guys you know a little script that would run out there and take a look and and hash some files and compare them and say cool you know you guys have struts in your network here's a little script that you can run to tell and what I actually ended up finding when I went to look to see if anybody else had done something similar was that this guy has done something similar and far beyond as
well so that what he's got out there um will actually give you a nice little report if you want it to give you report um but what's even more effective is he has like plugins for like ant and Maven and these other build processes that your developers if you're doing code inous probably are using so what you can do is not be the security guy who says Nope stop we got to freeze until I can scan everything and make sure it's secure you can say hey guys include this in your build and when you do a build it's going to tell you whether you're using not just struts but anything that it has like an over es scap signature for it's
going to tell them so if you've got this crazy old XML library that you know somebody threw in there because they just needed something right now it's going to say and before the their build even finishes you know and if you can build that into your process to say hey guys if you have a security critical warning that comes up during your build process your build process is not done you need to go back and figure out what's wrong with that and and make it one of the goals of your build process is that you come clean on on a security scanning for autodate you know thirdparty libraries um and in with struts it's it's important to note that I think I
alluded to it earlier they've changed a lot of defaults so if you go from like a six-year-old struts install and you go ahead and just go up to the latest version you're going to break a whole lot of stuff um things aren't going to work the regular Expressions that they put in place in some cases blocked totally legitimate applications so if you use the word class in one of your objects that you legitimately put into your application I mean a lot of Developers do that right it just sort of makes sense to them you know the name of the object is the something class well okay we have a regular expression says you can't use the word class in a
parameter all right well your whole app is broken if you just upgraded to the the secure version so and those other parameter prefixes things like that are gone as well so there it's not as simple as just dropping in a new jar file and going um but it's definitely worth doing and so what I would do personally if I were on the defensive side is build this into um you know your your overall process say Hey look guys we have struts here but this is indicative of a larger problem um and if you guys have seen the oasp uh you know the top 10 number A9 from 2013 is using out ofate components so use something like
this as an opportunity to say we're going to build in an OAS A9 plan into our build process um and you'll be better off for now and you'll be better off for later you know go ahead and find Spring rails. net XML you know visual C++ libraries that are out of date that are you're including into your your or your developers are including into their software and it takes us back to the beginning um which is the takeaways you know third party libraries are everywhere struts is just one example it's a particularly bad example it's a particularly fun example from a pentesting standpoint um your CVSs scores are only as good as you know your
understanding of your own environment and and you have to look at them carefully you have to look at them critically and say okay is a five really a five for us um and that's not an easy job and it's not a simple thing to do and then again um your apps your your WS your IPS your IDs they're they're great to have um but don't rely on them to permanently fix a problem that's all I got
questions





